Transparently Intercept and Redirect DNS Traffic to an Internal DNS
-
Hey your the man, you've got 24k posts here and know more than probably anybody. I would ask that before you get your panties in a twist you read what people are asking. That sentence was specific to listing the DNS in the DHCP server section. In my limited understanding and testing of how DHCP works, when I put a DNS address in the DHCP it gets passed directly to the client.
Both of my latest posts highlight that your method is probably best... but I still need a DNS solution for the VLAN / subnet that the pi-hole DNS solution is put on. I'm not putting it on my DMZ as you suggested but on a management vlan and need the other servers / services to have access to that vlan without hardcoding it into them.
-
You can redirect traffic from pfsense on same segment, you just have to source nat it.. And now your pihole will not know that client X asked or client Y asked... Since it will all look like it came from pfsense.
Is there a way to override the DNS Forward DNS address and let the pfSense itself continue to use the System/General settings?
Yea set the forwarding in the custom option box vs using the checkbox.. Now you can point pfsense to whatever you want for dns
@cyrus104 said in Transparently Intercept and Redirect DNS Traffic to an Internal DNS:
eed the other servers / services to have access to that vlan without hardcoding it into them.
Already went over how to do this..
Here is what I would suggest, and why adding to OLD threads is problematic... Your ask or question really has ZERO to do with this thread.
You should start your OWN thread, laying out your exact questions and what your trying to accomplish..
-
@johnpoz said in Transparently Intercept and Redirect DNS Traffic to an Internal DNS:
You can do it when the dns server is on a different network.. Here I create a redirect on my lan network 192.168.9/24 to redirect to my pihole which is on my dmz or 192.168.3/24 network..
So you can see I did a query to 8.8.8.8 and was redirect to pihole, which logged it as my PC I did the query from I5-win box..
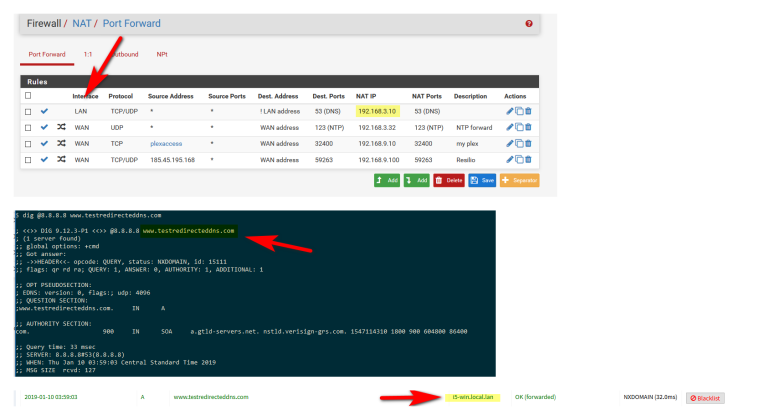
Where your going to have problems is trying to redirect traffic in and out the same interface with a port forward.
Move your pihole to its own segment and you will be fine.
As to unifi, not sure how they do it? Haven't look into it - but if you think they are out doing pfsense... Have at it ;) I had to run their USG for a while.. Their dns features are WAY behind... Well all their feature to be honest.. Creating a simple firewall rule was a PITA... Running multiple vlans, again PITA, etc..
I have the USG sitting on my self... Let you have it at pfsense forum users discount if you want it ;)
How can your PiHole see the Name of the Client? Mine only shows the IP :/
-
Because pfsense knows the name, and it does a PTR for it..
How pihole assigns name to an IP is via a PTR query for the IP..
-
@johnpoz I tried this setup and it works, as in I do get the right host name at the pihole end, but I get the following error as well:
❯ dig @8.8.8.8 dns-redirect-test.com ;; reply from unexpected source: 192.168.8.2#53, expected 8.8.8.8#53 ;; reply from unexpected source: 192.168.8.2#53, expected 8.8.8.8#53 ;; reply from unexpected source: 192.168.8.2#53, expected 8.8.8.8#53 ; <<>> DiG 9.10.6 <<>> @8.8.8.8 dns-redirect-test.com ; (1 server found) ;; global options: +cmd ;; connection timed out; no servers could be reached192.168.8.2is the IP of the pihole.
LAN1 (on which all devices sit) is192.168.7.x
LAN2 (on which pihole sits) is192.168.8.xProbably something to do with properly setting up an outbound NAT rule but I've tried diff configs, none seem to resolve the issue.
Any pointers are welcome.
-
@ibbetsion
The NAT Rule is only valid for the .7. net? -
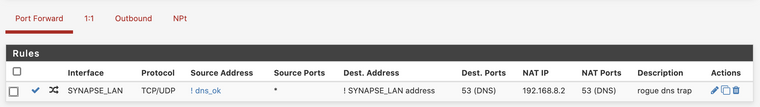
@Marv21 the redirect NAT rule is set up for the .7. net.
In the image below,SYNAPSE_LAN = .7.net.
-
@ibbetsion
dns_ok is 192.168.8.2 then - right? -
@ibbetsion
Where are you running this Dig command from?
A client from the 7 or the 8 Net? -
@Marv21 Sorry for omitting that,
dns_okis an alias that I use for those hosts that are allowed to make queries to external DNS servers. Any local host not in this alias/group should be re-routed to the local DNS server at192.168.8.2 -
@Marv21 the dig command is running from a host on the 7 Net.
-
@ibbetsion said in Transparently Intercept and Redirect DNS Traffic to an Internal DNS:
; reply from unexpected source: 192.168.8.2#53, expected 8.8.8.8#53
No shit what do you think was going to happen... This is why you put your NS your going to redirect to on a different vlan.. Or you have to forward it to loopback.. So pfsense does the query, and then sends the answer..
-
@johnpoz the NS is on a different subnet...
-
@ibbetsion
could you try this just 4 fun?
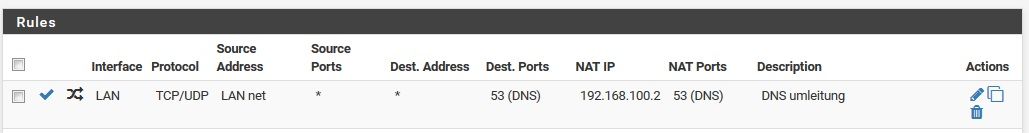
Thats mine. So everything will be redirectet from LAN to the SYNAPSELAN (any - directed to to that net or not) -
@Marv21 said in Transparently Intercept and Redirect DNS Traffic to an Internal DNS:
@ibbetsion
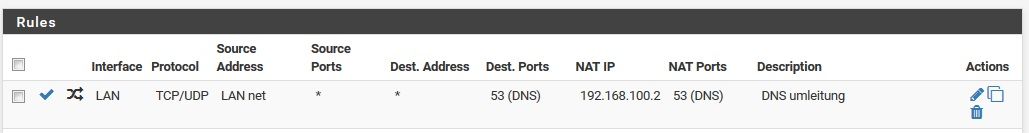
could you try this just 4 fun?
Thats mine. So everything will be redirectet from LAN to the SYNAPSELAN (any - directed to to that net or not)That caused all DNS resolution to stop working. I think the issue is somewhere else. I am also now finding out that I cannot ping (or ssh) from the 8 Net to anywhere on the 7 Net or anywhere else. But I can go from 7->8 Net. Need to solve that first :)
-
@ibbetsion
Have you a allow Rule on the 8 net?
YOu need to allow traffic to 7. -
@Marv21 said in Transparently Intercept and Redirect DNS Traffic to an Internal DNS:
@ibbetsion
Have you a allow Rule on the 8 net?
YOu need to allow traffic to 7.Yes, there is an allow rule on 8.

-
@ibbetsion said in Transparently Intercept and Redirect DNS Traffic to an Internal DNS:
the NS is on a different subnet...
You can not run multiple layer 3 on the same layer 2 and call it a different network..
For what your seeing to happen, the NS you redirected to had direct access to answer the client..
. I am also now finding out that I cannot ping (or ssh) from the 8 Net to anywhere on the 7 Net or anywhere else.
Seems you have bigger issues in your network than just trying to redirect dns..
-
@johnpoz I was able to resolve the other issues. Everything is on track except for the
unexpected sourceissue.A bit more on the network setup.
- ISP modem connected to pfsense on WAN port
- pfsense's LAN1 port connected to an unmanaged switch which in turn has all other local devices on it
- pfsense's OPT1 port connected directly to host running DNS/pihole
LAN1=192.168.7.x network
OPT1=192.168.8.x network -
Then what your seeing makes zero sense...
So I can for sure duplicate your problem when the NS is on the same network..
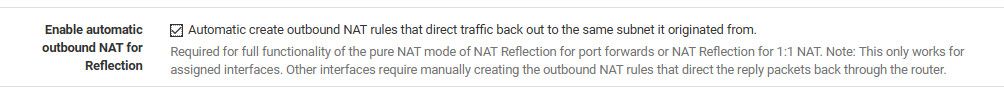
root@ntp:/home/pi# dig @8.8.8.8 www.google.com ;; reply from unexpected source: 192.168.3.10#53, expected 8.8.8.8#53 ;; reply from unexpected source: 192.168.3.10#53, expected 8.8.8.8#53But if I put it on a different subnet works fine, or if forward to loopback, or if setup nat reflect auto outbound nat rules so it
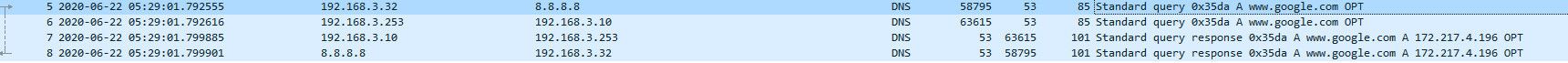
You can see from this sniff, pfsense saw traffic to 8.8.8.8, sent it on from its own interface 3.253 to 3.10, got answer and then sent answer back to 3.32 looking like it came from 8.8.8.8
But yes if client thinks it sending to A, and gets back answer from B - its going to complain.