Trying to configure IPsec for IOS 13.3.1, fails with "Negotiation with the VPN server failed"
-
If you can tell me how to post pfSense setting screens to this forum, I'll be happy to copy my exact configuration.
Take a screenshot and drag it into the message window.
-
Hi @NogBadTheBad Thanks for the suggestion!
I'll include all of my configuration screens (let me know if I missed anything), in case this helps to diagnose my issue":
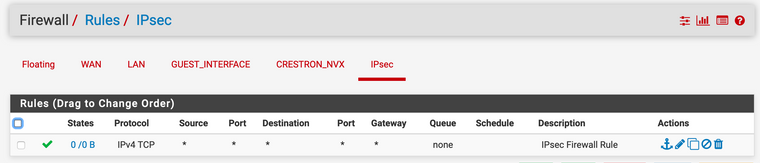
- Firewall screen:
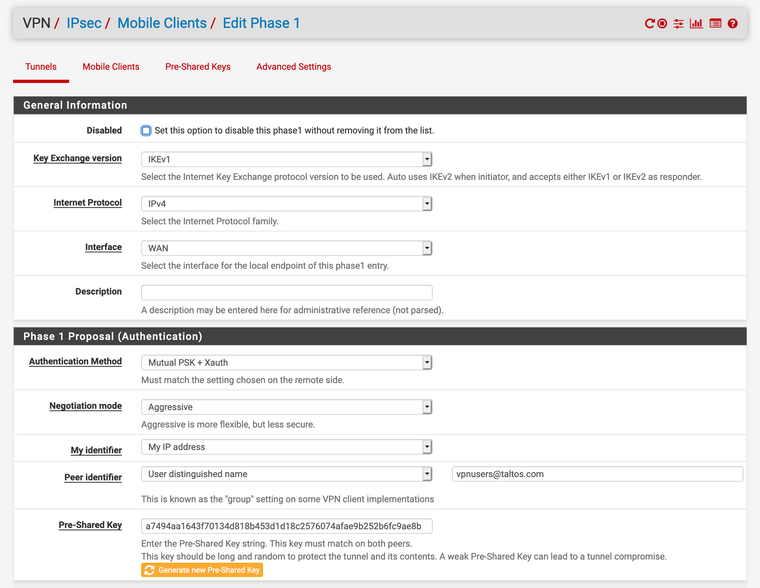
- IPsec Settings, Phase 1: (Note that I did change the pre-shared key)
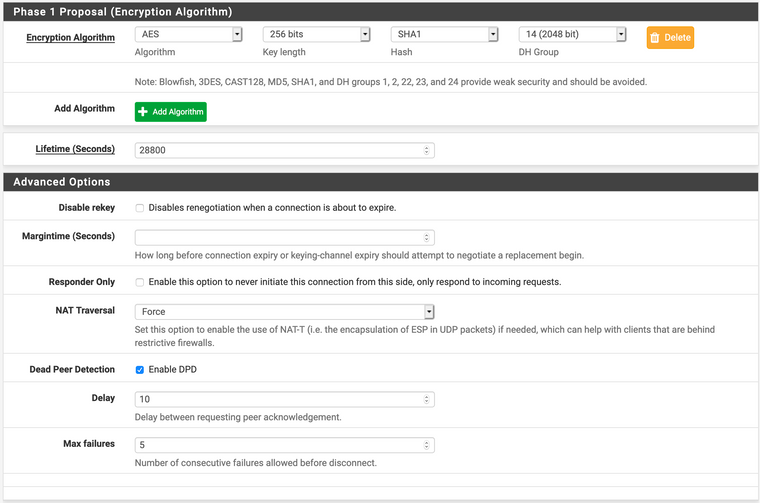
- IPsec Settings, Phase 2:
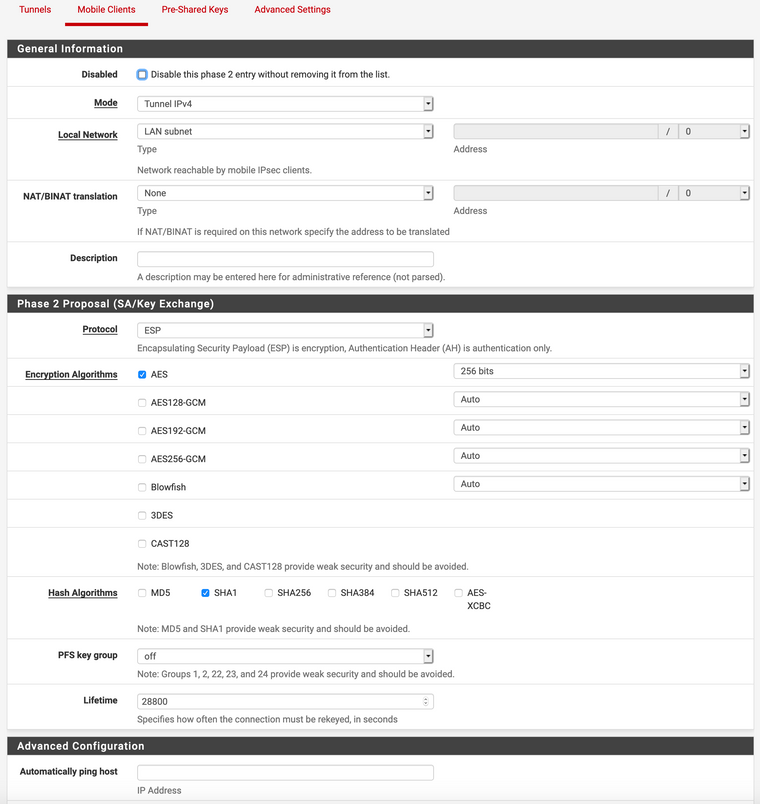
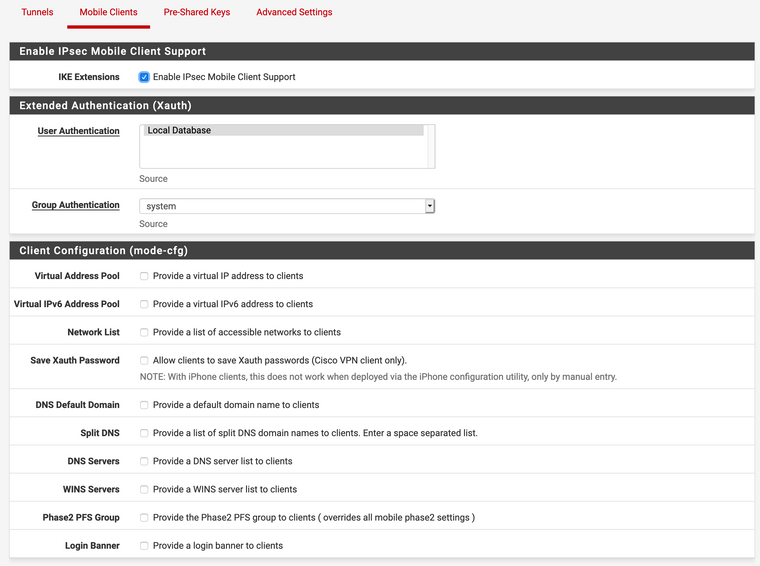
- IPsec Settings, Mobile Clients:
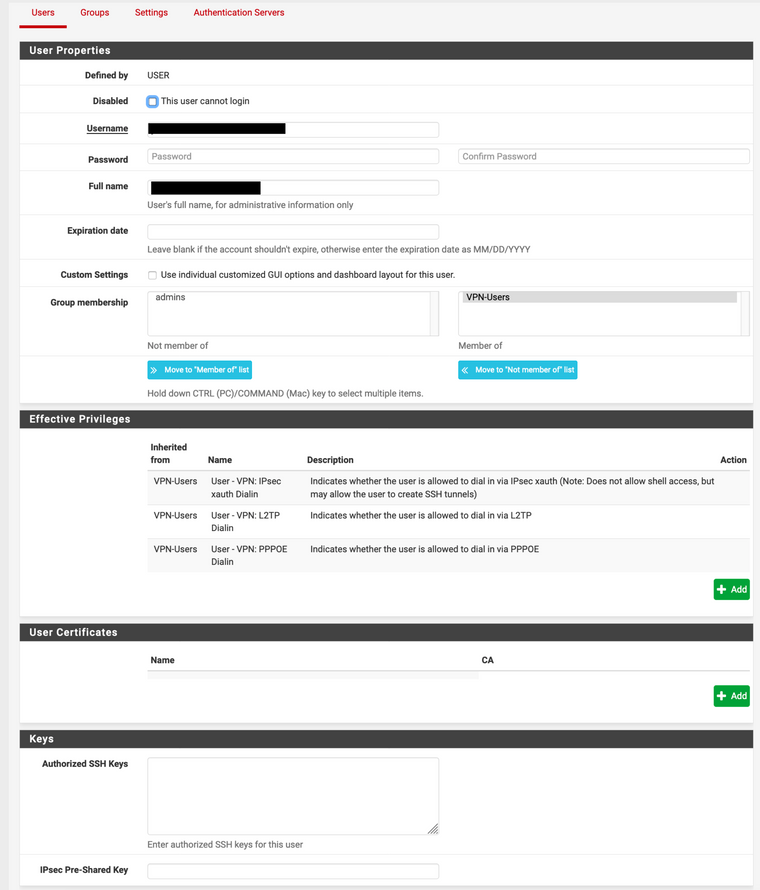
- User Settings:
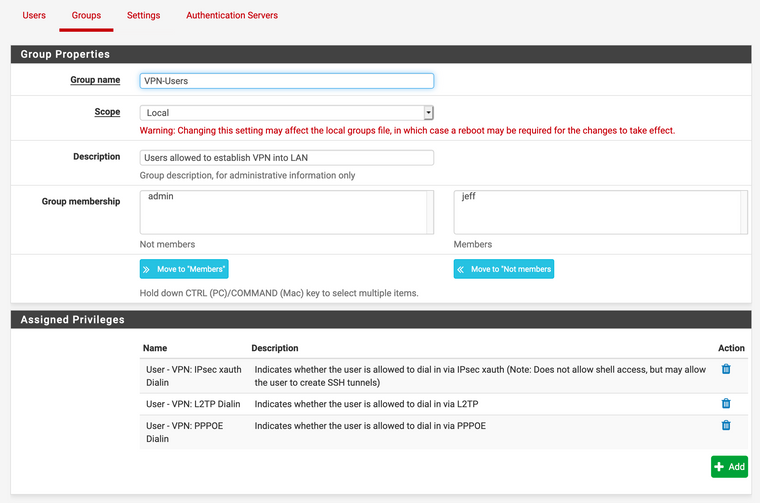
- And finally, Group Settings:
Thanks in advance for help in diagnosing my issue! If you need the current log, the one I posted before this would still be relevant.
-
Can you try DH Group 2 (1024 bit) in Phase 1.
-
Sorry for the delay. I did try changing the DH group to 2 (1024 bit) in phase 1, and that has no obvious affect. I still get
Negotiation with the VPN server failed.Any other suggestions? Thanks again for your willingness to help me with this, I really appreciate it!
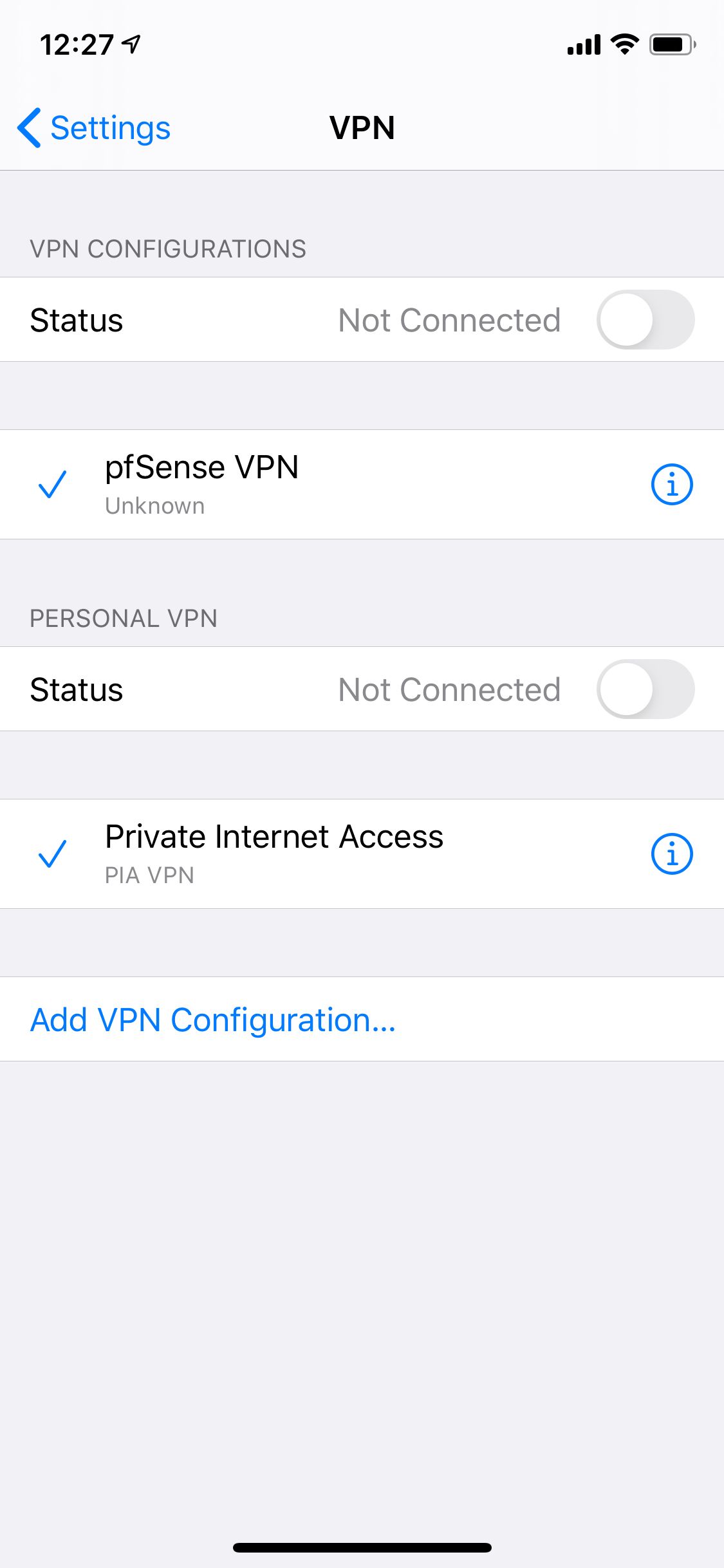
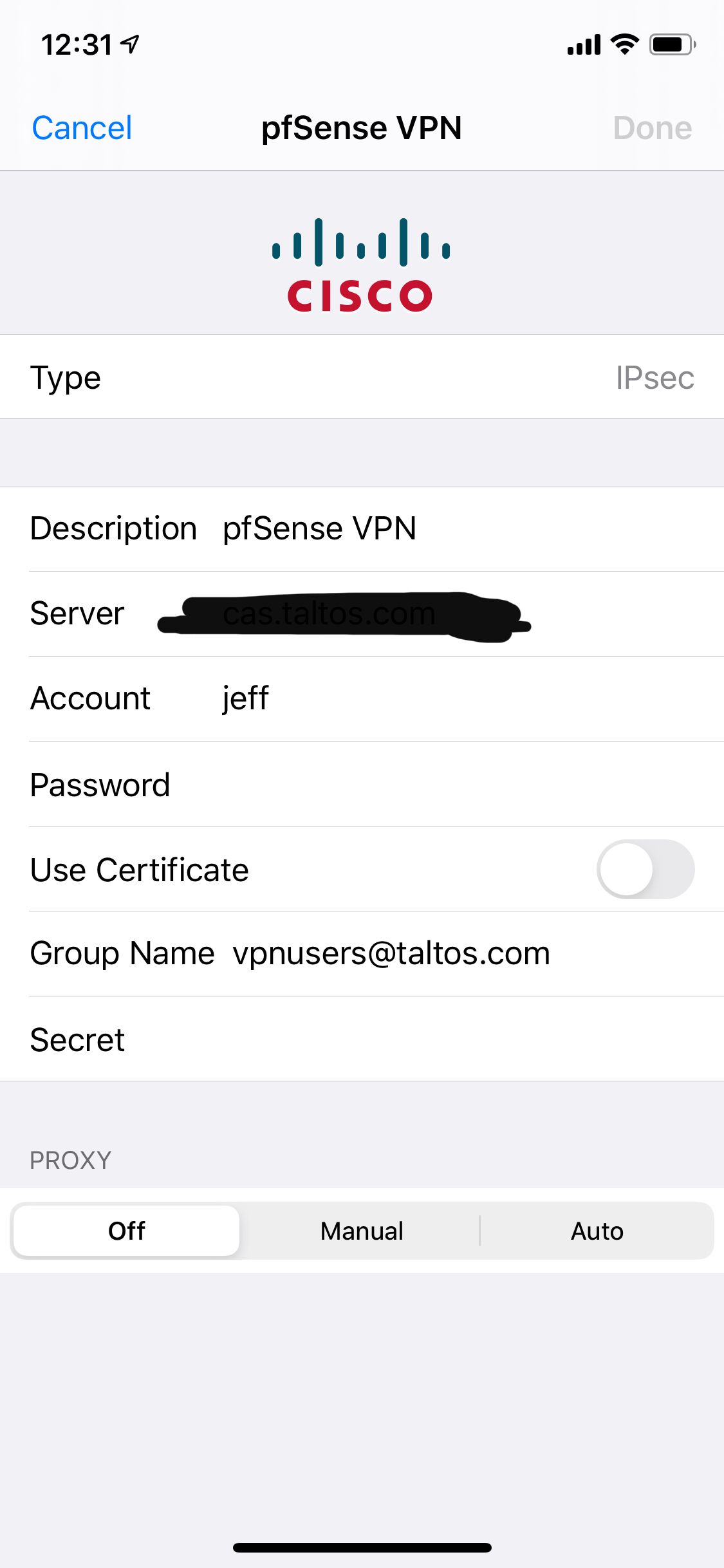
In case it helps, here's my settings screen on the iPhone:
If I drill down into the pfSense VPN configuration:
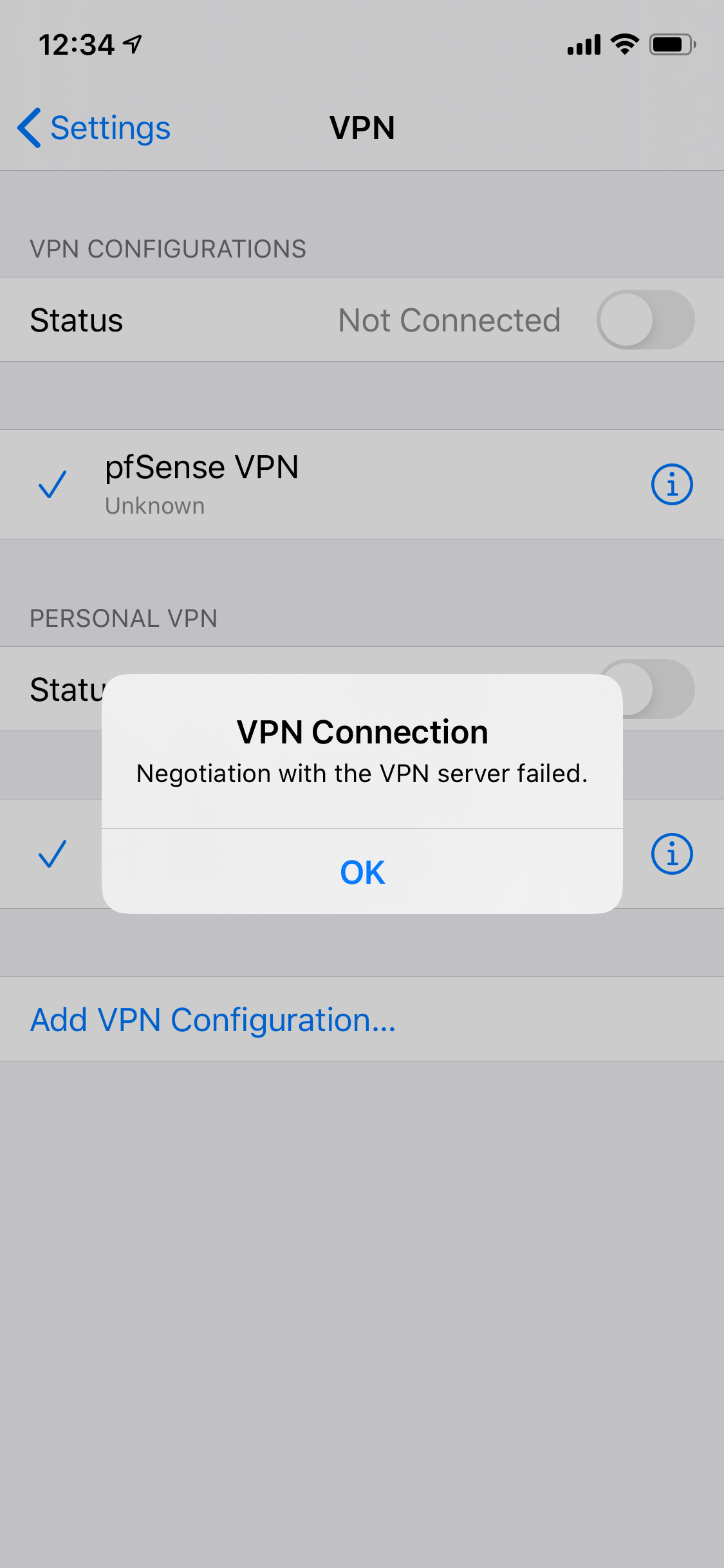
And, finally, when I try and launch the VPN:
-
@jeffc any reason your using IKEv1 ?
I followed https://docs.netgate.com/pfsense/en/latest/vpn/ipsec/configuring-an-ipsec-remote-access-mobile-vpn-using-ikev2-with-eap-mschapv2.html but I'm using Freeradius.
-
@NogBadTheBad I'm using IKEv1 for two reasons:
- A doc that I found specified using that for mobile iPhone access,
- That was also recommended in @egoisst posts, so I didn't change that.
Given that it's not working, I'm happy to try something else. This requires certs, though? I guess I'm okay with that, but it's an extra step I haven't currently done. Is that mandatory for EAP-MSChapv2?
I'll give this a try in a bit and see if it helps ... thanks!
-
I just wanted to follow up on this (really old) topic.
I did finally get IPsec configured with the iPhone, and it works great. In the end, I found that the pfSense documentation had everything I needed, including:
- How to configure the router, and
- How to configure the iPhone with the VPN properly.
See pfSense IPsec documentation for full details. Hope this helps someone!
-
Please uses IKEv2.
With IPsec Export: Apple Profile you can easy setup your iOS Device.
But if you want to use PFS, you have to insert 2 lines in the Profile output from pfsense.<key>EnablePFS</key> <true/>My Setup:
P1:
EAP-MSChapv2
AES 256
SHA 256
DH 14
Responder only
NAT Auto
Mobike enableP2:
Tunnel IPv4
ESP
AES 256
SHA 256
PFS key group 14Rekey works well if you inser the 2 lines in the ios Profile file.
-
@NOCling Thanks for your feedback. After I got the IPsec VPN working (and posting to this topic), I did look more closely at negotiated protocols. The default protocols in the pfSense documentation does get you up and running, but the encryption is not nearly as strong as desired.
After looking at what was actually negotiated between pfSense and the iPhone, I picked identical settings to you in terms of encryption.
In Phase 1, I didn't change the defaults for "Responder Only", "NAT Auto", or "Mobike enable". So, for me, "Responder Only" is disabled and "Mobike" is disabled. The rest is identical.
Why did you specifically change "Responder Only" or "Mobike enable", since it doesn't affect the iPhone? Or did you enable those for other reasons?
Also, why do "Rekey", since that's not needed either (at least for the iPhone)?
Thanks!
-
I want a Tunnel that use PFS:
https://en.wikipedia.org/wiki/Forward_secrecyClient VPN is incomming, nerver use for outgoing connections, to i set responder only.
For Outgoing i use Side 2 Side IKEv2.Mobike is a nice feature, so I turned on this crazy shit.
At my point of view, Microsoft support it 7 and Apple up iOS 9 or newer this feature.
https://tools.ietf.org/html/rfc4555