Outgoing traffic being blocked to strange dns servers
-
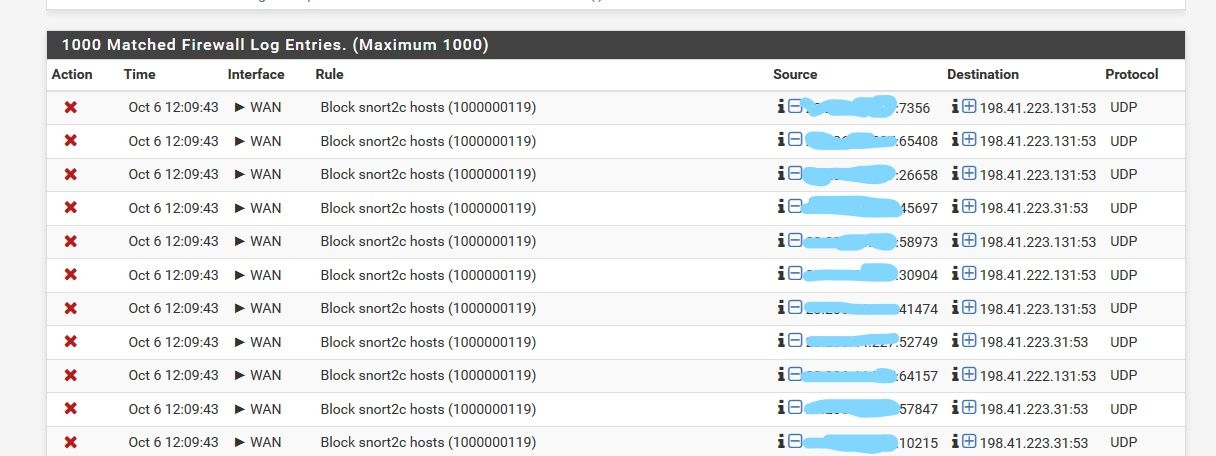
Getting thousands of firewall logs with the rule "Block snort2c hosts (1000000119)" which seem to be blocking traffic from the firewall to strange remote hosts on port 53. We have another identical pfsense firewall, and we don't see any alerts like these. How can this happen?
-
Presumably one of your internal clients is trying to access public DNS.
-
I don't think so. All the clients on that firewall use the firewall itself as their dns nameserver.
-
I see, so possibly it's the digi-ghost who is requesting the servers found in the log.

So add a firewall rule to your internal networks, maybe a floating rule for multiple interfaces at once, and block TCP/UDP port 53 except to the firewall, enable logging and you will get the culprit on a silver table in the log.
-
@stepariley said in Outgoing traffic being blocked to strange dns servers:
strange remote hosts on port 53
There is another recent thread (right here - this part of the forum) that states that pfSense itself doesn't care about the forwarding to 8.8.8.8 etc and keeps resolves the old fashioned way : that is : goto a root for a tld, goto a tld for the domain and then the final real domain name server of a domain for the A, TXT, MX, AAAA or whatever.
A bug report was opened recently. -
that IP is a cloudflare IP
cf-198-41-223-131.cloudflare.com
I don't think pfsense would do would be talking to that for its own stuff, but it could be some package using loopback (unbound) directly that is resolving.
Out of the box pfsense would just check if there is an update, and pull listing of packages, etc.
But if you have say pfblocker trying to download lists of IPs and such, then it could be asking unbound directly, which would resolve where ever that domain is..
Why is snort blocking it? What does the snort log say? Snort likes to block specific tlds that it feels are not legit.. or used for bad stuff.
-
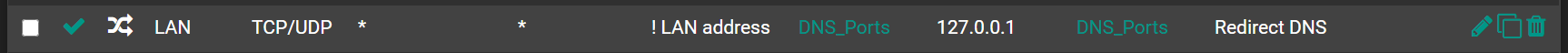
Try a NAT rule. Will force all LAN DNS to pfSense.
-
So, I tried blocking requests on lan for port 53 that weren't going to the firewall directly, and all of a sudden my zimbra server started complaining. Not sure what it's doing, since it's resolv.conf file is the same as every other client, i.e. use the firewall for dns. It starts to fail to respond to smtp requests of all things.
-
Also, I suspected pfBlocker and such, but like I said, I have the same configuration on a different firewall and I don't see it. I only have zimbra on the firewall that's giving me a problem.
-
@stepariley said in Outgoing traffic being blocked to strange dns servers:
So, I tried blocking requests on lan for port 53 that weren't going to the firewall directly, and all of a sudden my zimbra server started complaining. Not sure what it's doing, since it's resolv.conf file is the same as every other client, i.e. use the firewall for dns. It starts to fail to respond to smtp requests of all things.
If you cannot change the DNS settings on the host, however, by adding the NAT suggested by @provels you can direct its request to pfSense without taking a notice.
-
I just added the NAT rule suggested. Checking the log, I still see the same snort messages. So, I'm not sure what this means.
-
Also, putting some filtering in place, I don't see any logs showing requests coming from LAN that don't go to the LAN address of the firewall or the 8.8.8.8 server.
-
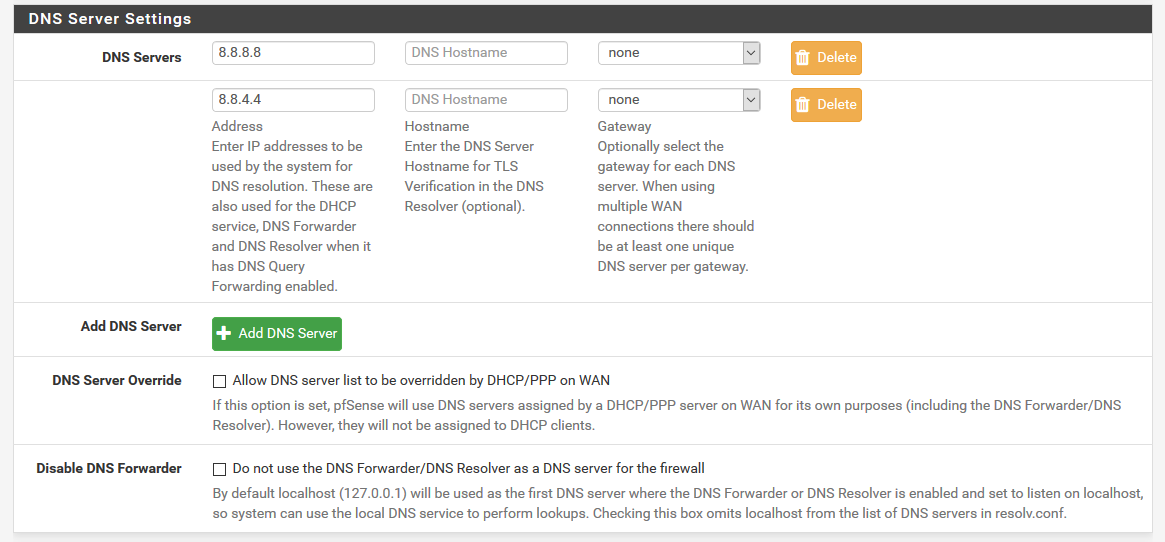
You make not mention of actually setting up forwarding in unbound or using dnsmasq.
You do understand that out of the box unbound is a resolver right? Doesn't matter what you put in the dns settings under general.. Unless you told unbound to forward.
-
Where do you configure that? I don't know anything about unbound.
-
unbound is the default dns for pfsense, out of the box. It resolves, it doesn't forward by default.. So you have no need to put anything in dns for general, or even get dns from isp.
Its under services menu, dns resolver.
-
Ok, so I looked in the resolver, and I saw that my Enable Forwarding was turned off. I turned it on, and I haven't seen any snort warnings in the last 10 minutes since then. So, maybe this is snort being overly aggressive on outgoing dns queries? My other firewall was the same, and I never got any snort errors.
-
So you would have to look in the snort log for why something was specific blocked. But I do know it can be very aggressive for specific tlds, like biz as example.. and some of the other ones that are cheap and not really used for normal major business..
I do see with that specific IP a wuai.biz related to it - atleast at one point in time, as well as ns4.cloudflare.net etc.
-
Yeah, I will look at the snort logs for that, but I think for now, I'm happy with the firewall not going out to the root dns servers. Just makes me nervous to see queries like that, especially when they are going outside the country.
-
And where do you think they go when you forward to 8.8.8.8 ;)
That is an anycast IP, you have no idea where the actual server that answers you might be..
-
Yeah, I realize that, but at that point, I feel it's someone else's problem.
