Blocking DNS over HTTPS. Seems the only way is to fire a shotgun at it
-
I realise Cloudflare cannot be using their entire IP space to serve up DNS, but they're clearly using a lot of IPs embedded in many, many subnets, either as a part of their design, or deliberately to obfuscate the target server for network admins.
-
Hi-
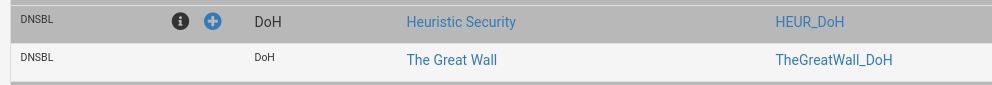
How do you feel about using this list in PF Blocker https://heuristicsecurity.com/dohservers.txt.I know not everyone uses PF blocker, but how does a list of the DNS ip work for blocking when the query is sent out FQDN?
-
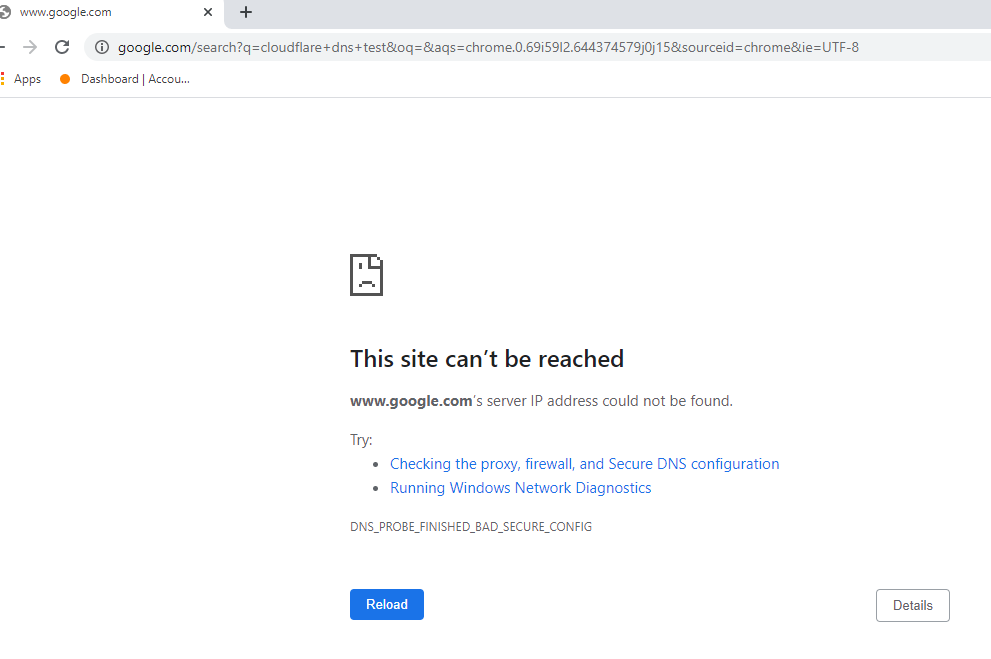
I'm now playing with a host override in my DNS resolver, pointing cloudflare-dns.com at local IPs to monitor, as you suggest above. However, I am seeing completely different IPs being queried from Chrome, also with DNS leak test websites. If I do a DNS lookup from the gateway itself, on those Cloudflare FQDNs, the IPs returned are in the blocklist. IPs queried from Chrome are not in the blocklist. Chrome must be using a different, unknown FQDN
-
What exactly are you settings in chrome? So you have it on purpose set to try and use doh, and your trying to block it?
You have it set like this
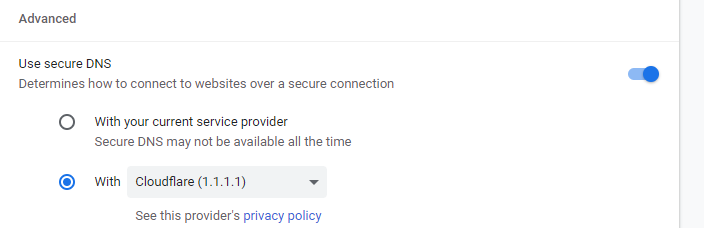
If so, I can do that and look to see what its doing.. Logging all traffic coming from the machine.. with a sniff.
And see if dns works.
-
@johnpoz Yes, Chrome DoH set to use system DNS, host machine set to use 1.0.0.1 and 1.1.1.1
This particular machine in Bangkok keeps using IP 162.158.161.161 when using DNS leak test website
-
Show me the setting you have set, like I have above - you have the other setting set..
And how your seeing that IP is from a leaktest.. I think your not understanding how those tests work.. Then.. Just because you see an IP there doesn't mean your client talked to that IP..
-
@johnpoz I have experimented with all the setting variants i.e. like in your screenshot above, and the other "current provider" setting. It appears to have the same result. If I choose Google, or CleanBrowsing, my countermeasures work. However, with Cloudflare, it is extremely difficult to block as far as I can see, without blocking all of their IPs.
-
@johnpoz said in Blocking DNS over HTTPS. Seems the only way is to fire a shotgun at it:
I think your not understanding how those tests work.. Then.. Just because you see an IP there doesn't mean your client talked to that IP..
Perhaps so. I am merely using that leak test site as an easy reference to see if that endpoint is using the DNS provider I specify in the gateway, or Cloudflare. It's ALWAYS Cloudflare without the blanket ban on Cloudflare IPs in place. You are correct in that I'm not understanding why this is so. I am trying to understand so I can remedy it.
-
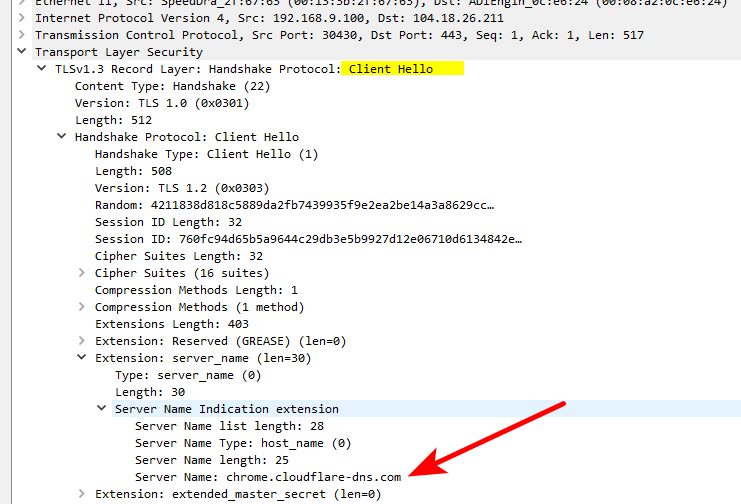
chrome is using this
chrome.cloudflare-dns.com
With the setting I had above..
added that to my block list, and no more chrome working for anything with that setting.
If you want to know what its doing, and what IPs it talking to - vs those stupid leak tests.. Just sniff.. See right away where its going
Those leak tests don't show you what IP the client talked to, they show you what IP ended up resolving the test fqdn they used... So it could be some IP upstream of where you asked that actually resolved it... Those tests are pointless scare tactics to get users to be scared -- OMG its "leak" without clue one to what actually is going on..
It never shows you 1.1.1.1 or 9.9.9.9 in those stupid tests.. It might show you your lame ISP dns if your using that - which NS uses the same IP to resolve with as it listens for queries on.. Small setups not enterprise or CDN setups..
The real problem here is users don't actually even understand what dns is or how it works - and if someone says hey your "leaking" they jump!!! OMG.... the man knows what I did a dns query for... The black helicopters are coming.. Without clue one to the basics of how any of it works in the first place... They can not tell you the difference between a forwarder or resolver, etc..
Sorry for the rant... Those dns leak tests don't do anything other than scare users to be honest.
-
@johnpoz Kudos!!! So it was indeed a previously unknown FQDN. That's sure going to make things easier for me.
-
Oh you got me started - sorry... The above example where I show how easy it is to see where you went in a simple sniff..
Should show these users.. They are so worried omg my ISP knows what websites I am going to... Hiding your dns doesn't stop them from knowing that.. Even encrypting it and sending it all to whereever..
They still see the IPs you go to, and right there in the freaking hello is what fqdn you were trying to hit.. Exact same info dns gives them..
So what are you doing other than handing all your dns to someone else, along with your ISP still having the info, and making your dns slower to boot.. But OMG a freaking leak<rolleyes>
-
https://redmine.pfsense.org/issues/10969 - feature request for adding https://github.com/Sekhan/TheGreatWall feeds to pfBlockerNG
-
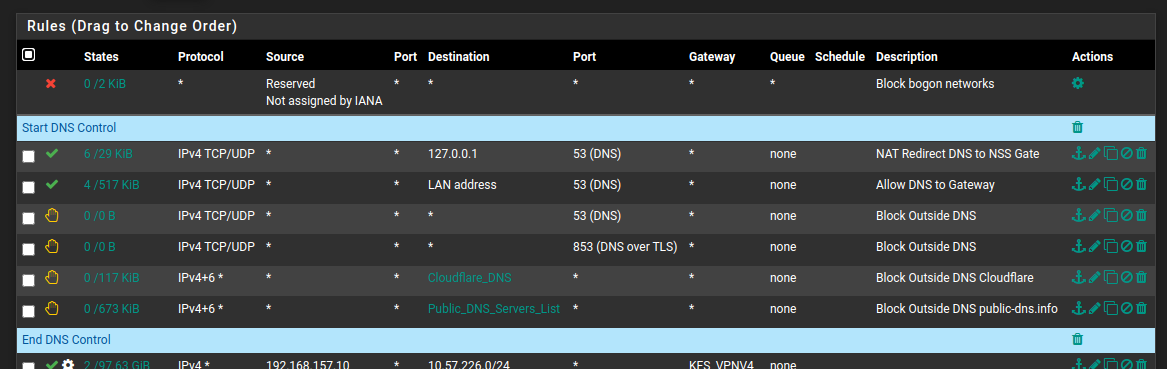
Just to update this topic, setting the following in my resolver's custom options. . .
server: local-zone: "use-application-dns.net" always_nxdomain local-zone: "cloudflare-dns.com" static. . . and adding the following IP lists to the firewall as blocked aliases. . .
https://public-dns.info/nameservers.txt
https://raw.githubusercontent.com/Sekhan/TheGreatWall/master/TheGreatWall_ipv4. . . completely hamstrings Firefox and Chrome's attempts to use DoH. I'm sure they will find new ways to screw with network admins, but for the time being, this appears to be highly effective, while keeping things pretty neat and tidy. This is what I am deploying on my production network.
NOTE: Anyone reading this, don't just throw this into your config and forget. You MUST also have the DNS redirects to your local resolver/forwarder in place first.
-
@Lanna said in Blocking DNS over HTTPS. Seems the only way is to fire a shotgun at it:
local-zone: "cloudflare-dns.com" static
That is a great solution.. Since you set it static, unbound will not try to resolve any subdomains of that be it the Mozilla or the chrome one..
-
@Raffi_
Yea, that "managed environment..." seems to work for domain aware devices. I imported their Active Directory settings into my home domain (Windows Server 2016), and it comes up as disabled by default on domain members. I did turn off the Chrome DNS function via their policy additions anyway (and disabled DOT in Firefox too using their extensions). I then turned my attention to the non-domain stuff so added a NAT redirect for 53 on my IOT VLAN to catch all the 53 to 8.8.8.8 and redirect to my DNS, and don't allow 853 to the internet. DOH from the non-domain-joined IOT was still an issue, so I just setup Lanna's suggestion of the two block lists and the local-zone setting.This seems like a lot of work to stop software from doing something against my wishes. I was using DOT for a bit but decided I was still handing over my my browsing history to some company so I am just letting the router do the resolving to root servers now.
Feels like a cat and mouse game, or wack a mole...
-
@Tzvia said in Blocking DNS over HTTPS. Seems the only way is to fire a shotgun at it:
Feels like a cat and mouse game, or wack a mole...
Concur - its really no better than the spammer changing their tactics to find a way to get their spam to users through corp filtering.. Now its the likes of google and cloudflare.. We will get your users data someway, no matter what you say corp IT..
They really want to send us their data, honest they do because we told them you were spying on their dns.. You know on the network you own and run, and them using the device you gave them to work with.. They clearly need to be able to resolve shop.tld
Oh you don't really want that to happen corp IT.. Here

JUMP!
-
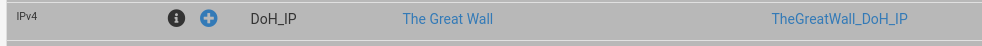
Anyway, TheGreatWall feeds are added to the latest version of pfBlockerNG-devel:

-
@Lanna said in Blocking DNS over HTTPS. Seems the only way is to fire a shotgun at it:
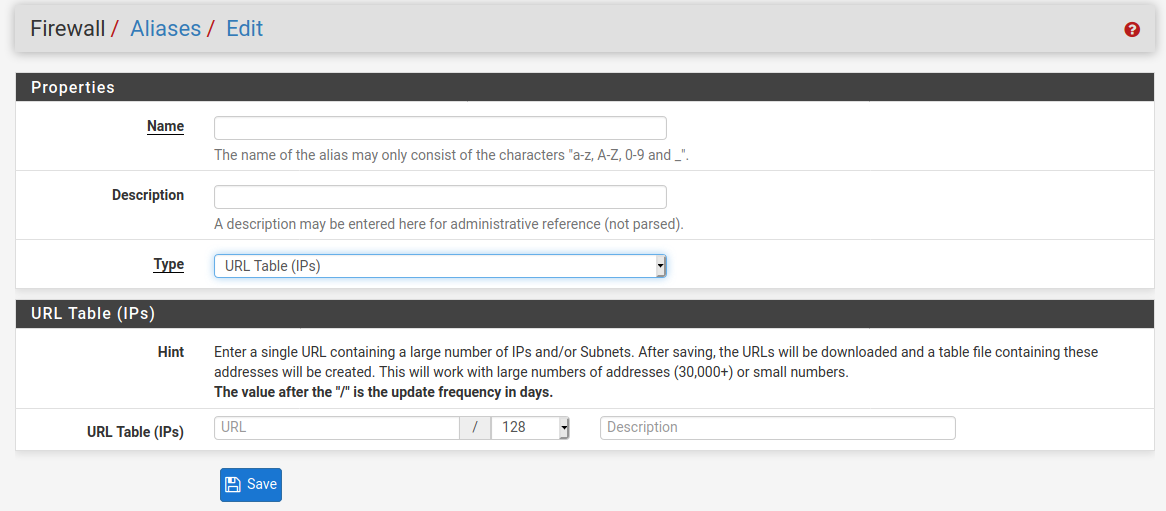
. . . and adding the following IP lists to the firewall as blocked aliases. . .
Trying to wrap my head around this one ...
Are you blocking everything to these IP's , or just 443 ??Are you pointing the alias to the listfiles via this one ??
Thanx for doing this
I have setup my pfSense (unbound) to use (forward) all queries to use two Linux Bind9 servers i have locally (vlan100) , doing all the resolving.
They have to have "access to the root servers" UDP 53 , if i enable (dns) portforwarding on vlan 100 , can i make an exception for these two so they're not redirected ?
I'm already handing out pfSense IF as DNS via dhcp to clients , and blocking
53/853 to other(s). No UDP 53 portredirect yet.I'm not that intertested in pfblocker-ng , i use Pihole (also vlan 100) for "scrubbing" my mobile devices.
So i suppose i have 4 local ip's i'd like to prevent from being redirected.
local DNS1 - A root server access
local DNS2 - A root server accesspihole - Allow dns from Phone vlan + Mmedia Vlan
Express-VPN ATV DNS - Allow dns to this one from my ATV's on Mmedia vlan
/Bingo
-
@bingo600 said in Blocking DNS over HTTPS. Seems the only way is to fire a shotgun at it:
@Lanna said in Blocking DNS over HTTPS. Seems the only way is to fire a shotgun at it:
Are you blocking everything to these IP's , or just 443 ??
I am blocking all ports to those IPs, but adjust to your liking
Are you pointing the alias to the listfiles via this one ??
That's right, I am using the URL Table option
-
@Lanna said in Blocking DNS over HTTPS. Seems the only way is to fire a shotgun at it:
Just to update this topic, setting the following in my resolver's custom options. . .
server: local-zone: "use-application-dns.net" always_nxdomain local-zone: "cloudflare-dns.com" static. . . and adding the following IP lists to the firewall as blocked aliases. . .
https://public-dns.info/nameservers.txt
https://raw.githubusercontent.com/Sekhan/TheGreatWall/master/TheGreatWall_ipv4. . . completely hamstrings Firefox and Chrome's attempts to use DoH. I'm sure they will find new ways to screw with network admins, but for the time being, this appears to be highly effective, while keeping things pretty neat and tidy. This is what I am deploying on my production network.
NOTE: Anyone reading this, don't just throw this into your config and forget. You MUST also have the DNS redirects to your local resolver/forwarder in place first.
Just as an addition to the above, I've spent the last 24 hours playing around with DNSBL and I realised that with the BETA of 'Enable TLD' you can in fact just add those domains in a custom blacklist and every subdomain will be blocked there too. Probably neater for some setups.