change local networks for all openvpn servers
-
I am having a bunch of openvpn servers for my remote shops. And is there a way to do it with some script or something, or i must mannualy change it all?
-
You have server at each location? You connect to them individually?
Why are you changing the local subnets? There is a conflict?
If each location was a client and connected to a central server you could potentially push new details to the clients. NAT to each location maybe.
Steve
-
@stephenw10 said in change local networks for all openvpn servers:
You have server at each location? You connect to them individually?
Why are you changing the local subnets? There is a conflict?
If each location was a client and connected to a central server you could potentially push new details to the clients. NAT to each location maybe.
Steve
i am having routers on remote location and all those location are seperate openvpn instance.
So one pfsense hold those instances, and all of them are seperate openvpn servers in pfsense.
I have add new subnet and want to add to all of them to can reach it. -
So pfSense is configured as a client for each of those remote servers?
And you need to the remote servers to access a new subnet at the pfSense end?
There is no way to do that remotely, you will need to add the new subnet as a remote network on each server if that's how they are configured.
If they were SSL/TLS clients to pfSense as the server you could have just pushed out new values to them.
Steve
-
@stephenw10
thanks, and just one questin though.
Is there an option to restart openvpn services all at once, or also i must in status one by one? -
There is no GUI button to do that directly.
If they're all on the same WAN you could resave that interface and it will restart all the services on it.So they really are clients at the pfSense end?
If so those will restart when you make changes to the server end anyway.Steve
-
@stephenw10 said in change local networks for all openvpn servers:
There is no GUI button to do that directly.
If they're all on the same WAN you could resave that interface and it will restart all the services on it.So they really are clients at the pfSense end?
If so those will restart when you make changes to the server end anyway.Steve
I dont search for gui button, it can be from shell also. Yeah, they use all same WAN IP(VRRP interface).
There is a couple 100s more.
And if i want to restart openvpn service..What you propose to do? I wait a half day forsome to check if router will realize that it is disconnect, bit it doesnt. Maybe some timer for that? -
If the remote routers are the server end they won't do anything if the client disconnects.
Is pfSense the client end of the tunnels?
-
@stephenw10 On the router end we put client cert, if thats your question?
-
EDIT: The below would only work if you are using SSL/TLS with /30 network topology
If the server(s) is on the "Central pfSense" , and the remote shops are "Clients". You might be able to do some "scripted" changes to the servers in the central end.
I suppose you have added a new subnet , that is available on/via the central end ?
And want to as another ipv4 remote network to the central server, for the specific shop: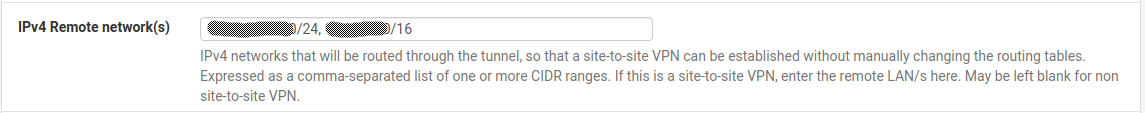
But messing with your pfsense config file , especially on the pfsense it self. Could be a "heartbeat raising event".
If i had several hundreds i might try to download the config as xml (make a work copy), and give a search/replace a go.
But you would need to upload it as a "new" config , and the pfSense would reboot (downtime).
If the change had to be done on anything but the central pfSense .. I'd say manual work.
/Bingo
-
@bingo600 said in change local networks for all openvpn servers:
If the server(s) is on the "Central pfSense" , and the remote shops are "Clients". You might be able to do some "scripted" changes to the servers in the central end.
I suppose you have added a new subnet , that is available on/via the central end ?
And want to as another ipv4 remote network to the central server, for the specific shop: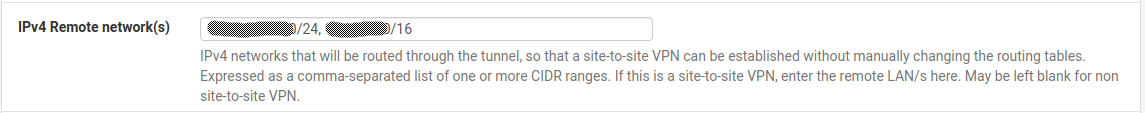
But messing with your pfsense config file , especially on the pfsense it self. Could be a "heartbeat raising event".
If i had several hundreds i might try to download the config as xml (make a work copy), and give a search/replace a go.
But you would need to upload it as a "new" config , and the pfSense would reboot (downtime).
If the change had to be done on anything but the central pfSense .. I'd say manual work.
/Bingo
I want to add into IPv4 Local network(s), Remote network is subnet of the shop (all shop has their subnet)
-
Yes if pfSense is the server end of these tunnels you might be able to push new routes IF the tunnels are SSL/TLS. Which is sounds like they are if you used certs.
I would certainly not have used individual tunnels to each router though.
Steve
-
@stephenw10 I am not using ipsec. Router have openvpn with pfsense server from which i reach any subnet i want via routes from switch. So remote shop via openvpn instance have access to subnets.
-
@mercy_angel said in change local networks for all openvpn servers:
I want to add into IPv4 Local network(s), Remote network is subnet of the shop (all shop has their subnet)
EDIT: The below would only work if you are using SSL/TLS with /30 network topology
What i showed was my Central Server OpenVPN definition.
And the "remote networks" announced to the Client OpenVPN.This would often be the same announced networks to all clients.
As it is the ip nets of the Central/Main site.If you had to do it manually , would you have to do the change on the openvpn defined on the pfsense in all the shops ?
Or would you have to do the changes on the same pfSense box , and change it in every instance of the OpenVPN servers defined for the shops ?
All changes on the same box , or changes on all remote boxes ?
This is the xml tag you would search for tn the config file.
<remote_network>192.168.1.0/24, 10.1.0.0/16</remote_network>But as mentioned earlier , it would only make sense if you have to change everything on the same box (config file)
-
@bingo600 said in change local networks for all openvpn servers:
@mercy_angel said in change local networks for all openvpn servers:
I want to add into IPv4 Local network(s), Remote network is subnet of the shop (all shop has their subnet)
What i showed was my Central Server OpenVPN definition.
And the "remote networks" announced to the Client OpenVPN.This would often be the same announced networks to all clients.
As it is the ip nets of the Central/Main site.If you had to do it manually , would you have to do the change on the openvpn defined on the pfsense in all the shops ?
Or would you have to do the changes on the same pfSense box , and change it in every instance of the OpenVPN servers defined for the shops ?
All changes on the same box , or changes on all remote boxes ?
This is the xml tag you would search for tn the config file.
<remote_network>192.168.1.0/24, 10.1.0.0/16</remote_network>But as mentioned earlier , it would only make sense if you have to change everything on the same box (config file)
i will enter each server in OPENVPN and one by one add that subnet.
-
@mercy_angel said in change local networks for all openvpn servers:
i will enter each server in OPENVPN and one by one add that subnet.
And where would you do that ?
On the same pfSense box , or on each "shop box" ?
-
@mercy_angel said in change local networks for all openvpn servers:
I am not using ipsec.
I never suggested you were.
OpenVPN can operate using pre-shared key or SSL/TLS with certificates.
If you are using SSL/TLS and you have a subnet style topology (>/30) then the client will pull the routing and tunnel details from the server each time it connects. That means you can add new values at the server end without having to make changes at the remote client end.
You could have all your clients connecting to a single server, or a just a few servers, which would make this much easier.
Steve
-
@stephenw10 said in change local networks for all openvpn servers:
If you are using SSL/TLS and you have a subnet style topology (>/30) then the client will pull the routing and tunnel details from the server each time it connects.
Whoopzz
I'm using SSL/TLS w. Certs & /30I thought all the setups pulled routes from the server end

I could easily have lead the OP on a wild goose chase.
Once again . Assumptions are the ..... all FSCK'upsSorry
-
Yup I have fallen into that trap more than once!

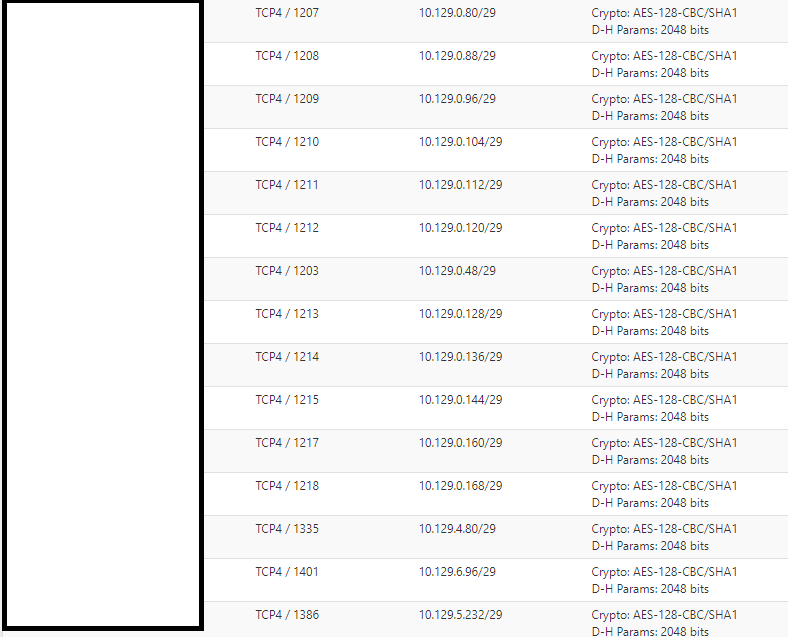
The OP here looks to be using /29 though so it should be pulling details. It might have been setup specifically to do this since using /29 is just a waste of IP space.
Makes things more complex though as you need iroutes etc.
https://docs.netgate.com/pfsense/en/latest/vpn/openvpn/configure.html#ipv4-ipv6-tunnel-network
Steve
-
@stephenw10 Mikrotik have some issue with /30 mask, cant remember why.
if someone know, this is how we connect when apply certificate/interface ovpn-client add add-default-route=no auth=sha1 certificate=remoteSHOP_cert.crt_0 cipher=aes128 connect-to=PFSENSE_IP disabled=no max-mtu=1500 mode=ip name=ovpn-out1 password="" port=1671 profile=default user=anySo its client based on mikrotik, and one remote shop have their own pfsense ovpn server and client certification.