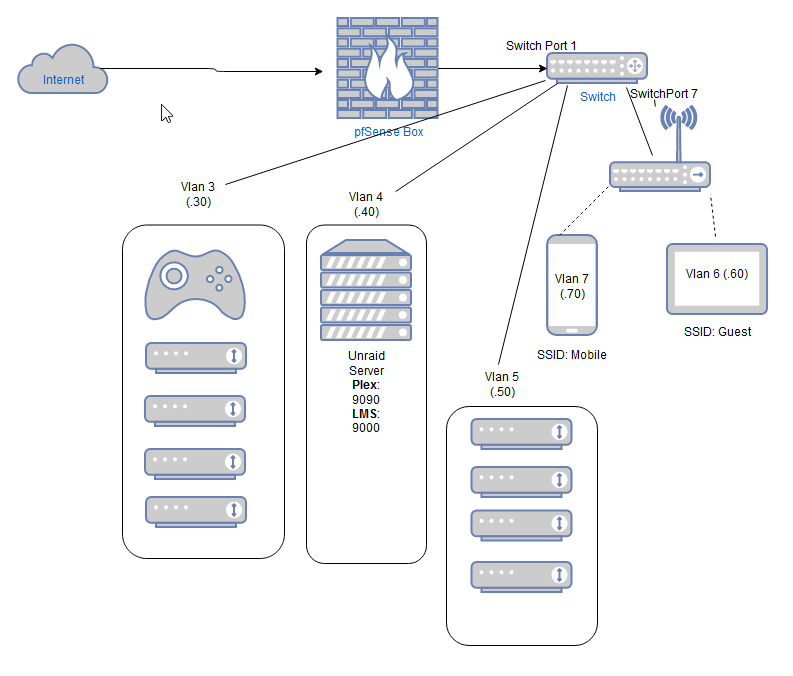
Vlans and firewall rules
-
@cburbs Yes, plexnassrv and plex are both aliases.
My NAS is not only a plex server, that is the reason that it is in a separate VLAN.plexnassrv is an alias with only one IP, but in your situation, you could add more for the unRaid server.
plex is an alias with port 32400 that is the plex default port. In your case, it would be 9090.
You can add more than one port to this alias.Regarding the first rule (Block to Firewall), that is needed, because without it, this VLAN would be able to access pfsense GUI trough it's WAN IP address.
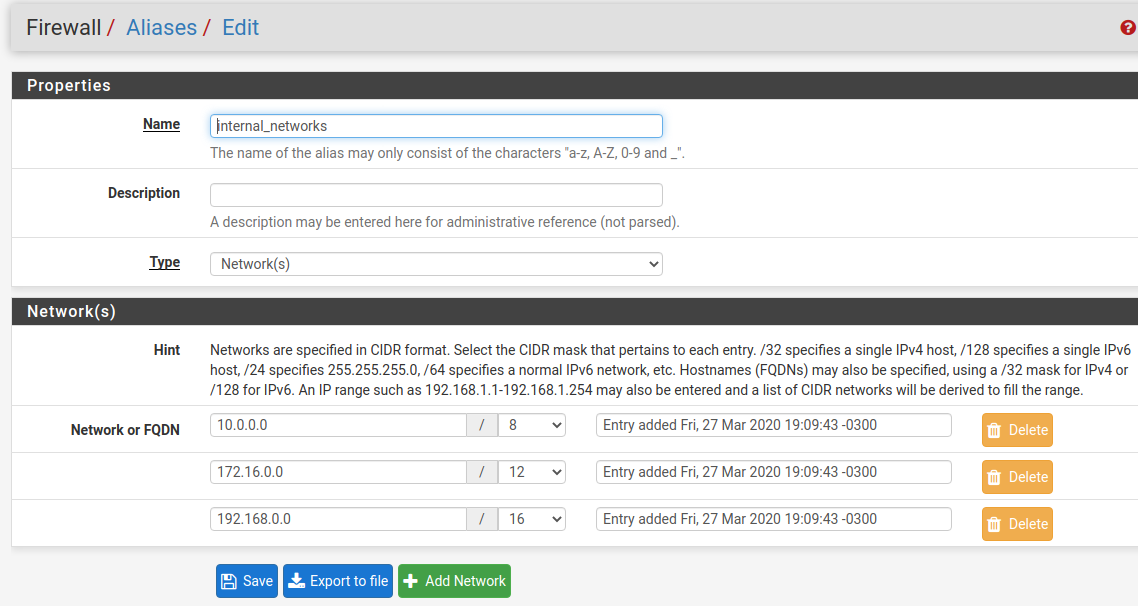
So, this rule blocks access to all pfsense interfaces.Edit: internal networks is also an alias, that contains the other VLANs.
-
How do you have your Alias "Internal Networks" set?
-
I set RFC1918 because I'm always adding and removing VLANs.
But you can add only your VLANs, it would work in the same way.Just remember, in case you add a guest VLAN for an example, you would need to edit this alias and add the guest vlan.
-
Yep - Seems alot of people go that route. Some even add IPv6 stuff to it.
-
@cburbs In my situation, only "VLAN3" has IPV6 connectivity.
So, it was easy for me.Edit: I don't like the idea of my servers using IPV6.
Also, my ISP only gives me a /64.. -
Also I noticed on my Vlan test I can still ping all my devices on my LAN even though I have a rule set for that.
So..
Laptop on Lan can ping test vlan. But only one of the devices not both which is odd. This is by IP.My other laptop on test vlan can ping my lan pfsense, switch, AP, etc
Also I have pfblockerng setup on my lan. What needs to be done to pass all Vlans on this as well?
-
@cburbs said in Vlans and firewall rules:
Also I noticed on my Vlan test I can still ping all my devices on my LAN even though I have a rule set for that.
So..
Laptop on Lan can ping test vlan. But only one of the devices not both which is odd. This is by IP.
My other laptop on test vlan can ping my lan pfsense, switch, AP, etcWhat switch do you have? Some cheap switches are known to leak VLAN1.
Also I have pfblockerng setup on my lan. What needs to be done to pass all Vlans on this as well?
You can tick the box inside pfblocker to create floating rules, or just select the interfaces you would like to pfblocker to create the firewall rules.
-
-
@cburbs I'm not sure if this switch has a problem with VLAN 1.
I know other TP-Link switches that this problem happens, like TL-SG105E or TL-SG108E, in hardware revisions 1, and 2.If I remember correctly, they fixed this in revision 3, 4 and 5..
And they were leaking multicast and broadcast, not sure if that was happening to ICMP ..
Do you have a firewall rule to block ICMP from vlan test to LAN?
-
It is Versionn 4..0
No on the ICMP rule.
-
@cburbs If you don't have a block rule, this ping from vlan test to LAN will work through the Internet Rule or (ipv4 allow all)
You have to explict block it, and put this rule above the internet rule.
-
@mcury Makes sense! Thanks.
-
Ok I have my Picore music Player working with my LMS server.
So vlan 60(test vlan) can talk to my LMS server.
I also have an Nvidia Shield on this Vlan 60. My Iphone is just on my lan network what needs to be done so I can cast something from my phone to the Shield?
-
@cburbs Chromecast works with mdns, which can be accomplished with the avahi package in pfsense.
Not sure if nvidia shield works with mdns, you would have to test and confirm.Then, after installing avahi, you would need to create firewall rules to allow your iphone to reach the nvidia shield.
Chromecast uses tcp 8008 and 8009, but not sure about nvidia shieldFor testing purposes, you can create a rule to allow everything from your iphone to the nvidia shield.
Or, just put the nvidia shield in the same VLAN as the wireless devices..
-
Do you think it makes sense to have Vlan3(video streamers) and vlan5(music streamers) or would you just put them into one Vlan?
Also if in Vlan5 I have one device that just needs Internal access and nothing else is that just a block rule?
-
@cburbs said in Vlans and firewall rules:
Do you think it makes sense to have Vlan3(video streamers) and vlan5(music streamers) or would you just put them into one Vlan?
I always choose to separate servers, like samba, nas with file storage, and plex, from other devices.
So, in my scenario, I have 4 vlans.
MGMT - To manage devices
LAN - Servers
WIFI - My family devices, TVs, chromecasts, printers and etc
GUEST - for friends that come hereIn your case, I would remove VLAN5, and put video streamers and music streamers in the same vlan, which would be VLAN3.
But that is my personal choice, of course other users could have a different approach.
Also if in Vlan5 I have one device that just needs Internal access and nothing else is that just a block rule?
If you have a device in VLAN5 that needs to access VLAN3, you would create a firewall rule allowing the device (IP address), to access VLAN3, then, you would create a second rule, below the first one, blocking the entire network to access other vlans.
In the last position, the internet rule, allowing any. -
Let me rephrase that....
In vlan3 I have one device(AVR) that doesn't need access to anything.My Iphone just needs access to it to control it from an App.
-
@cburbs The idea would be the same.
Firewall rules goes from top, to bottom.Just block the DVR to access all other things, this rule must be in the top.
Your phone, that I'm assuming that is in other VLAN, you create a firewall rule in this other VLAN allowing the iphone to access the DVR, then you block other devices to access the other vlans, and finally the internet rule allowing everything.
In case iphone and DVR are in the same VLAN, they wouldn't communicate through the firewall, it would go directly through the switch.
-
Drawing it out as it helps me sometimes
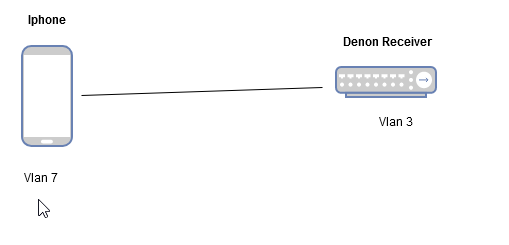
So my Iphone which is on Vlan7 needs to talk to my Denon Receiver on Vlan3.
You mention creating the rule in Vlan 7 to talk to the device in Vlan 3.
Could you also do it the other way around and create the rule on Vlan 3 to allow the Iphone in?
Is one way better than the other? and why?
-
@cburbs Creating the rule in VLAN3 wouldn't work.
The interface where the packet is coming from, needs to allow that flow in first place, otherwise the firewall would drop the packet.
pfsense is a stateful firewall, which means that if the packet is allowed to enter, the return of the packet would work, even without a rule.
So, for an example, you can create a rule blocking everything in VLAN3, so all VLAN3 ip addresses would be blocked to enter the firewall.
But, if you come from VLAN7, and if there is a rule allowing this flow, the return traffic from VLAN3 would work, even with a block everything rule.