offloading OpenVPN using external gateway
-
Activated packet capture on host 192.168.5.9 and opened a webpage with www.google.it:
16:58:57.410983 IP 192.168.5.1 > 192.168.5.9: ICMP echo request, id 43267, seq 8815, length 9
16:58:57.920985 IP 192.168.5.1 > 192.168.5.9: ICMP echo request, id 43267, seq 8816, length 9 -
@chrispazz said in offloading OpenVPN using external gateway:
Activated packet capture on host 192.168.5.9 and opened a webpage with www.google.it:
16:58:57.410983 IP 192.168.5.1 > 192.168.5.9: ICMP echo request, id 43267, seq 8815, length 9
16:58:57.920985 IP 192.168.5.1 > 192.168.5.9: ICMP echo request, id 43267, seq 8816, length 9Where did 192.168.5.9 come from ??
did you mean 5.99 -
@bingo600 yes is 5.99 :) don't hate me eheheh
-
So we have confirmed that the ICMP (ping) packages are actually being "policy routed" from 5.1 (pfSense) to 5.99 (RasPI)
We don't see any Echo reply ... The issue is probably on the RasPI
-
On the Raspi (as root)
What does a : sudo iptables -L show ?
And this one ?
-
This post is deleted! -
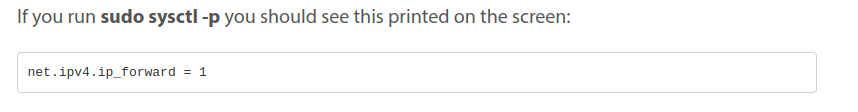
Did you reboot the RasPI after enabling forwarding ?
-
@bingo600 yes, forward is activated.
Chain INPUT (policy DROP)
target prot opt source destination
ACCEPT all -- anywhere anywhere
ACCEPT icmp -- anywhere anywhere
ACCEPT tcp -- anywhere anywhere tcp dpt:ssh
ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHEDChain FORWARD (policy DROP)
target prot opt source destination
ACCEPT all -- anywhere anywhere
ACCEPT all -- anywhere anywhere state RELATED,ESTABLISHEDChain OUTPUT (policy ACCEPT)
target prot opt source destinationand yes, I rebooted it a lot of times :)
-
Does this one give the expected result , should be your (OpenVPN public ip) ?
wget http://ipinfo.io/ip -qO -
Can you ping the google.it from the RasPI ?
/Bingo
-
@bingo600 said in offloading OpenVPN using external gateway:
wget http://ipinfo.io/ip -qO -
Both yes.
And if I test a traceroute from raspi I can confirm it is going outside using VPN connection.... -
Now : I would connect a PC directly to the RasPI , or directly to the ISP inside LAN , and set def-gw to the RasPI , and maybe DNS to 8.8.8.8
Then start debugging directly between the PC & The Raspi.
This can come in handy ... Disables all iptables stuff on the Raspi.
But only for this "boot sesion"iptables -F iptables -X iptables -t nat -F iptables -t nat -X iptables -t mangle -F iptables -t mangle -X iptables -P INPUT ACCEPT iptables -P FORWARD ACCEPT iptables -P OUTPUT ACCEPTI use these rules on my Deb10 machines , for OVPN to a VPN provider.
Remember to replace ens192 with the name of your ethernet interface on the Raspi.
# Default policy to drop all incoming packets iptables -P INPUT DROP iptables -P FORWARD DROP # Accept incoming packets from localhost and the LAN interface iptables -A INPUT -i lo -j ACCEPT iptables -A INPUT -i ens192 -j ACCEPT # Accept incoming packets from the WAN if the router initiated # the connection iptables -A INPUT -i tun0 -m conntrack \ --ctstate ESTABLISHED,RELATED -j ACCEPT # Forward LAN packets to the WAN iptables -A FORWARD -i ens192 -o tun0 -j ACCEPT # Forward WAN packets to the LAN if the LAN initiated the # connection iptables -A FORWARD -i tun0 -o ens192 -m conntrack \ --ctstate ESTABLISHED,RELATED -j ACCEPT # NAT traffic going out the WAN interface iptables -t nat -A POSTROUTING -o tun0 -j MASQUERADE #Remember to save new rules if you change them
sudo systemctl enable netfilter-persistent -
@bingo600 said in offloading OpenVPN using external gateway:
sudo systemctl enable netfilter-persistent
I made some other tests.
Raspberry is working good if I set a client to use it as network interface gateway and connection will go thru VPN (using my own iptables rules or yours).
So it seems that when I go thru pfsense, WAN main gateway (ISP router) is getting used instead of firewall rule gateway...
-
@chrispazz said in offloading OpenVPN using external gateway:
@bingo600 said in offloading OpenVPN using external gateway:
sudo systemctl enable netfilter-persistent
I made some other tests.
Raspberry is working good if I set a client to use it as network interface gateway and connection will go thru VPN (using my own iptables rules or yours).
So it seems that when I go thru pfsense, WAN main gateway (ISP router) is getting used instead of firewall rule gateway...
That doesn't make sense
The packet trace you made doesn't lie. -
Now is the time to use tcpdump on the RasPI
https://kalitut.com/record-network-traffic-with-raspberry/
To see what it actually receives & forwards
-
@bingo600
This is traceroute from the client with the firewall rule applies:traceroute to www.google.it (216.58.215.227), 64 hops max, 52 byte packets
1 192.168.5.254 (192.168.5.254) 2.370 ms 1.583 ms 1.516 msThe first hop go to ISP gateway....I can't see Raspi here...
-
@chrispazz
But that is not consistent with the packet trace you made on the pfSenseCan you do another trace , and then the traceroute ?
-
@bingo600 if I try a trace to www.google.it IP address as host I get this:
18:25:31.846958 IP 192.168.5.1.4704 > 172.217.168.35.443: UDP, length 1350
18:25:31.883433 IP 172.217.168.35.443 > 192.168.5.1.4704: UDP, length 1350so it is using 192.168.5.1 as gateway....
-
@chrispazz Perhaps I understand the problem.
My WAN interface is getting IP from ISP router (DHCP server on 192.168.5.0).
The ISP gateway is getting on top of the firewall rule gateway....This is WAN if on pfsense:
em1.90: flags=8843<UP,BROADCAST,RUNNING,SIMPLEX,MULTICAST> metric 0 mtu 1492
options=3<RXCSUM,TXCSUM>
ether 02:11:32:25:4e:f9
inet6 fe80::11:32ff:fe25:4ef9%em1.90 prefixlen 64 scopeid 0x8
inet 192.168.5.1 netmask 0xffffff00 broadcast 192.168.5.255
nd6 options=21<PERFORMNUD,AUTO_LINKLOCAL>
media: Ethernet autoselect (1000baseT <full-duplex>)
status: active
vlan: 90 vlanpcp: 0 parent interface: em1
groups: vlan -
No wrong.
192.168.5.1 is pfsense.... :(
-
@chrispazz said in offloading OpenVPN using external gateway:
@bingo600 if I try a trace to www.google.it IP address as host I get this:
18:25:31.846958 IP 192.168.5.1.4704 > 172.217.168.35.443: UDP, length 1350
18:25:31.883433 IP 172.217.168.35.443 > 192.168.5.1.4704: UDP, length 1350so it is using 192.168.5.1 as gateway....
Nope
It's using 5.1 as source IP (Consistent with your WAN NAT)If you enable logging on the Policy rule , do you see any log lines ?
Now you are not doing the traceroute on the pfSense box ... Are you ?
What PC ip address are you doing the traceroute from , and are you 100% sure you have that ip in the OPENVPN Alias , and a policy route rule on the pfSense interface that that PC is connected to ?