Routing between WAN and LAN
-
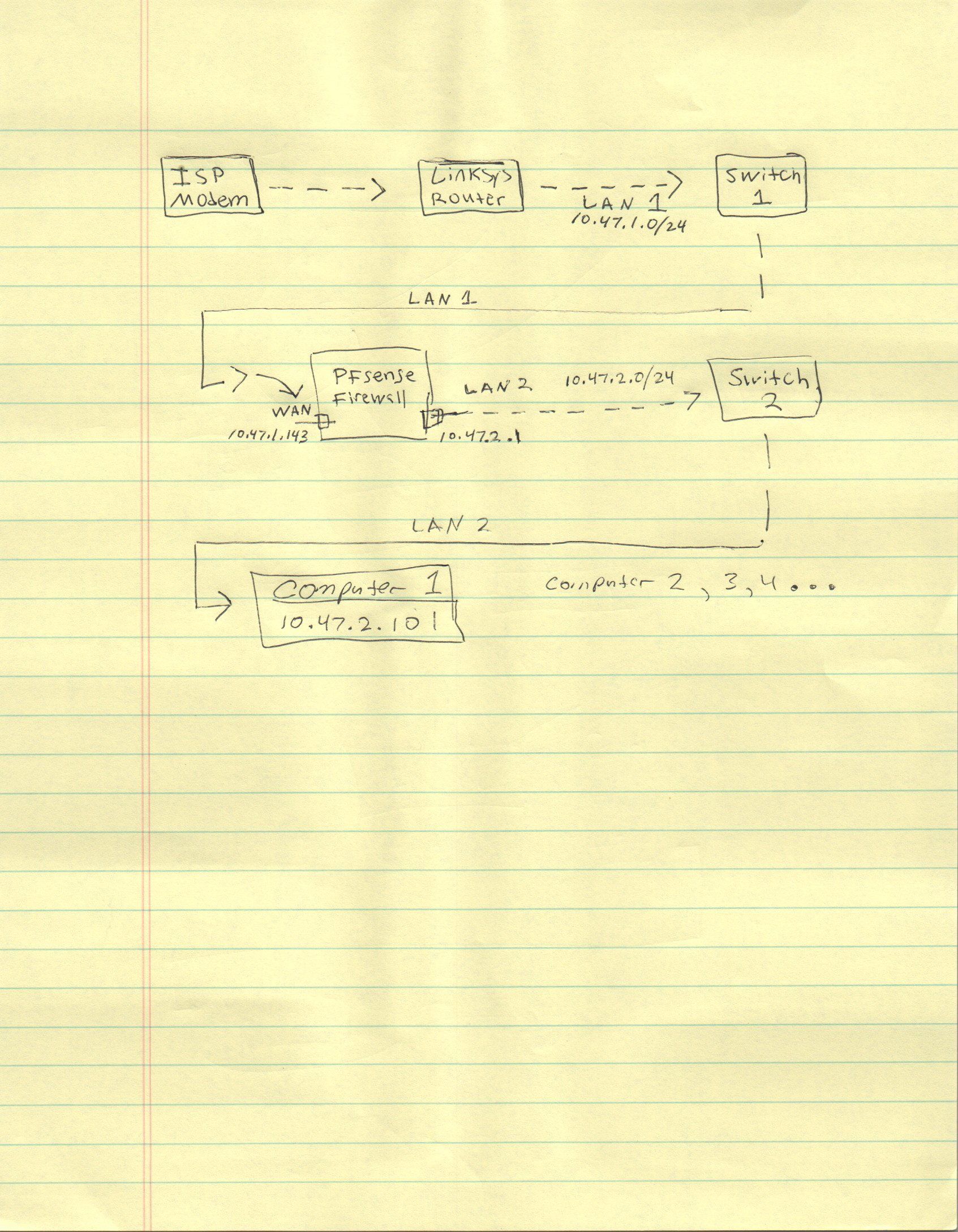
He called it out here
something I need to change in my linksys router on lan 1
But yeah a drawing is always good! What I took from his statements is he has this.
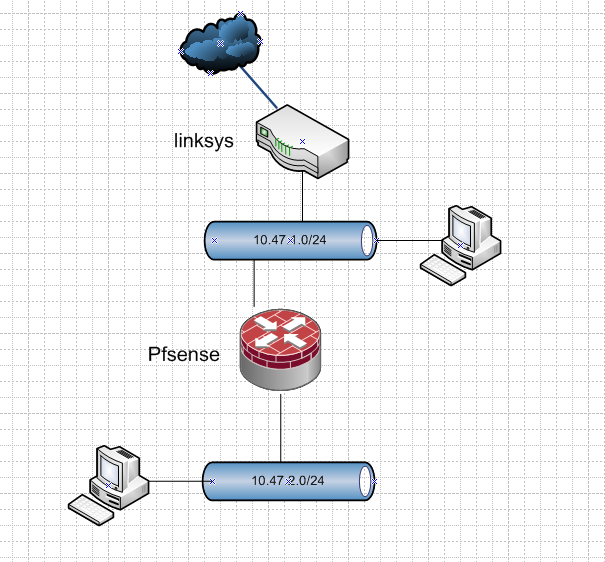
That is going to be asymmetrical unless you host route on every device in what he calls his lan1, or nat at pfsense.
-
@johnpoz
Ahh, yeah, didn't see it this way before, but absolutely agree. -
-
I'm not too familiar with nat and forwarding/routing stuff. I've been reading up on it, but it confuses me.
Are you saying it's not possible to access the computer at 10.47.2.101 from LAN 1?
-
I'm sure @johnpoz will suggest this soon.
What pfSense device do you have ?
Does it have possibility 3 netcards ??Here is a suggestion , that "keeps your" 10.47.1.x devices, no need to change ip addresses on the devices on that network (well except the linksys).
And introduces a "Pure Transit network" (No user devices on it) behind the Linksys.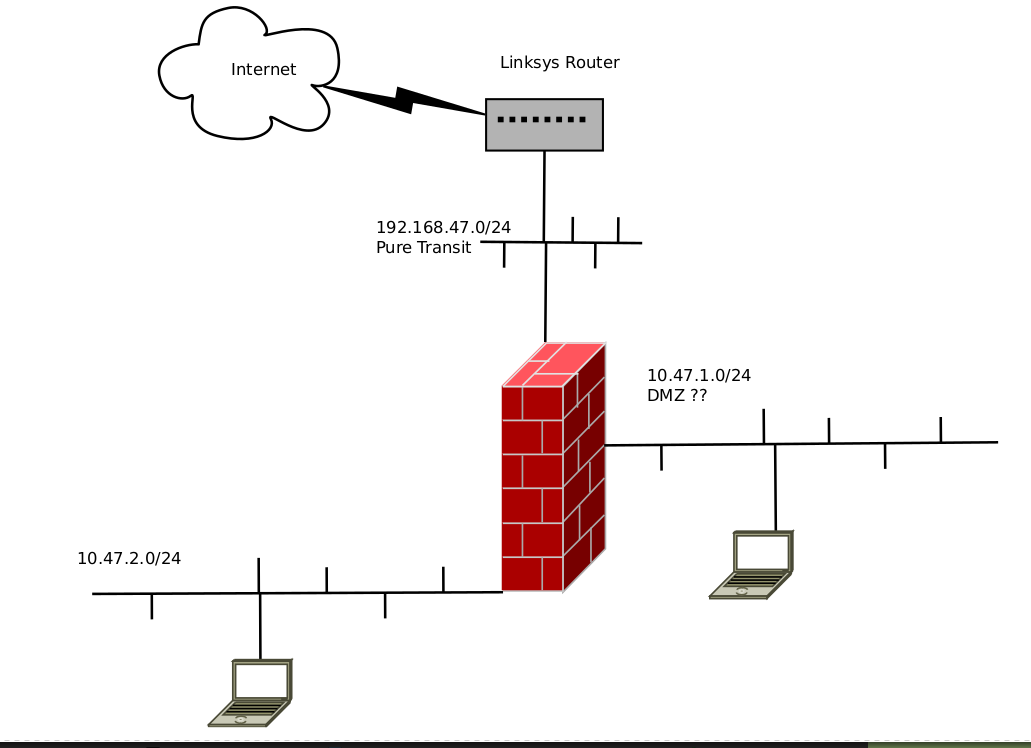
/Bingo
-
@brandon-lizard
@johnpoz already mentioned all options you have here.Best practice would be to set up a transit network between the Linksys and pfSense. So your LAN 1 devices simply send their packets to the Linksys and they get forwarded to pfSense.
But I assume, that router isn't capable of handling multiple subnets.The other options are NAT or adding a static route for LAN 2 to each LAN 1 device you want to enable to communicate with that network.
When doing NAT you have add virtual IPs to pfSense for each device behind you want to access and forwarded the packets to the destination devices.
Both not optimal, I think. Maybe you can exchange the Linksys and pfSense, then you could set up a transit network.
-
I do have 3 netcards available, yes. My pfsense is actually running in proxmox. I also have a nas and pbx. I'd like those to all be on the 10.47.2.0 network.
-
@brandon-lizard said in Routing between WAN and LAN:
My pfsense is actually running in proxmox
Yeah another complexity..
Which you left off your drawing.
I suggest you just do the double nat setup.. Which will work just fine, and would be default out of the box setup for pfsense.
Only thing you have to do is as mentioned turn off the block rfc1918 rule, and setup your port forwards for stuff you want lan1 to access on lan2.
https://docs.netgate.com/pfsense/en/latest/nat/port-forwards.html
-
Then i suggest you move the 10.47.1.x network "behind/into" the pfSense.
Tip: Keep all 10.47.x.x networks behind the pfSense (makes life easier).And make a 192.168.47.0/14 network as Transit.
Now you can still restrict the 10.47.1.x devices via pfSense rules , if 10.47.2.x devices needs to be "protected". And you don't have to bother with portforwarding , as 10.47.1.x is now "behind/inside pfSense".
-
Sorry ... for making another suggestion

-
Yeah removing devices off the network being used between linksys and pfsense, would be a better solution yes. And would remove the need to port forward for his networks behind pfsense.
But I have a sneaky suspicion he also has wireless devices connecting to his linksys router that would not be able to access anything behind pfsense without port forwards.
If was me, I would ditch the linksys as a router and just use it as an AP. And use pfsense for all his routing needs. Pfsense would get his public IP on its wan.. And all his networks would be behind pfsense.
-
If you want to access the NAS or other "inside" devices from the internet.
Then just do the portforwards as @johnpoz says , you'll have to do them anyway.I'd still suggest using a 192.168.47.0 as the "linksys (transit) net".
To keep the 10.47.x.x/16 net "inside" the firewall.
-
@bingo600 said in Routing between WAN and LAN:
Then i suggest you move the 10.47.1.x network "behind/into" the pfSense.
@brandon-lizard Yeah, I would put all behind pfSense and kick the Linksys.
Don't scruple due to virtualization. My home main router (pfSense) runs on KVM as well since more than 3 years and does its job very well. -
@johnpoz said in Routing between WAN and LAN:
But I have a sneaky suspicion he also has wireless devices connecting to his linksys router that would not be able to access anything behind pfsense without port forwards.
Ah I didn't see that one comming

If was me, I would ditch the linksys as a router and just use it as an AP. And use pfsense for all his routing needs. Pfsense would get his public IP on its wan.. And all his networks would be behind pfsense.
That would be an "elegant" solution , if you "trust" Proxmox to be "Wan".
-
Sorry for not putting in the details. didn't think it mattered.
Yes, that's the easiest solution to put everything behind pfsense.
But, my hubby will get mad if anything goes down. I was trying not to have the whole network depend on pfsense.
-
If the pfSense goes down , then you won't be able to access the devices on 10.47.2.0/24 from the linksys 10.47.1.0/24 anyways.
Then why bother accessing them at all from the "linksys" net.
Keep what you have.
And if pfSense goes down ,"teach the hubby" to move the cable from switch2 to switch1.Or do you have wireless on the linksys , and that's what the hubby is using ?
Edit: Sounds like @johnpoz portforwarding is a winner anyway.
I'd still suggest the "All behind pfSense" way.Maybe even get another wireless device to put "behind" the pfSense.
Then Hubby can connect to SSID "Inside" when wanting to use the NAS etc ... And SSID "Outside (Linksys wifi)" if pfSense goes down./Bingo
-
@bingo600 Yes, the linksys router is a wireless router that he uses. that router runs our main network (10.47.1.0/24) .
-
@johnpoz
Can i get the brand & model of your "Crystall ball"
I want one@brandon-lizard
If you can get/buy another wireless device , you could have 2 SSID's.
Existing Linksys (for emergency) when pfSense is down.
New device for "Normal use" connected to the NAS Lan/Bingo
-
OK. Here is what I’m going to do. Thanks everyone for your input, I really appreciate it.
With T-Mobile, I just realized I have an internet gateway modem, in addition to my cable modem from Comcast. T-mobile gateway isn’t being used at all right now.
I will use the internet coming from t-mobile as the WAN, and then plug in my two lans. LAN1 and LAN2. I will use three nics.
This should make things easier routing between LAN1 and 2 now right?
-
Never-mind. That gateway doesn’t work like a cable modem does. So I ran into a pickle.
All I am wanting to do is separate my two networks, having the ability to route between them, and sharing internet.
Why does this have to be so hard?