Bypassing DNSBL for specific IPs
-
Hey @horse2370 , thanks for the reply!
Okay I took some more screenshots of my setup. As they say "The plot thickens".
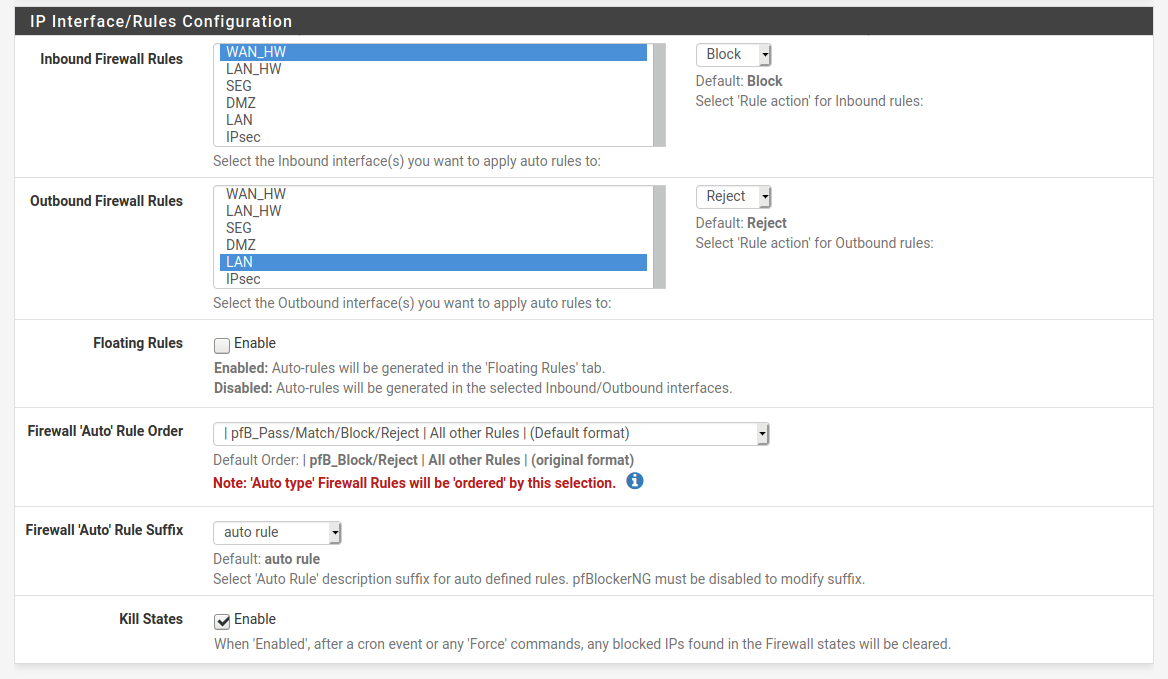
Before all of that, I had taken the precaution to make sure pfblocker was disabled on DMZ, here's a screenshot of the IP configuration page. As you can see, pfblocker is selected only on LAN (my main home network). DMZ is not selected :
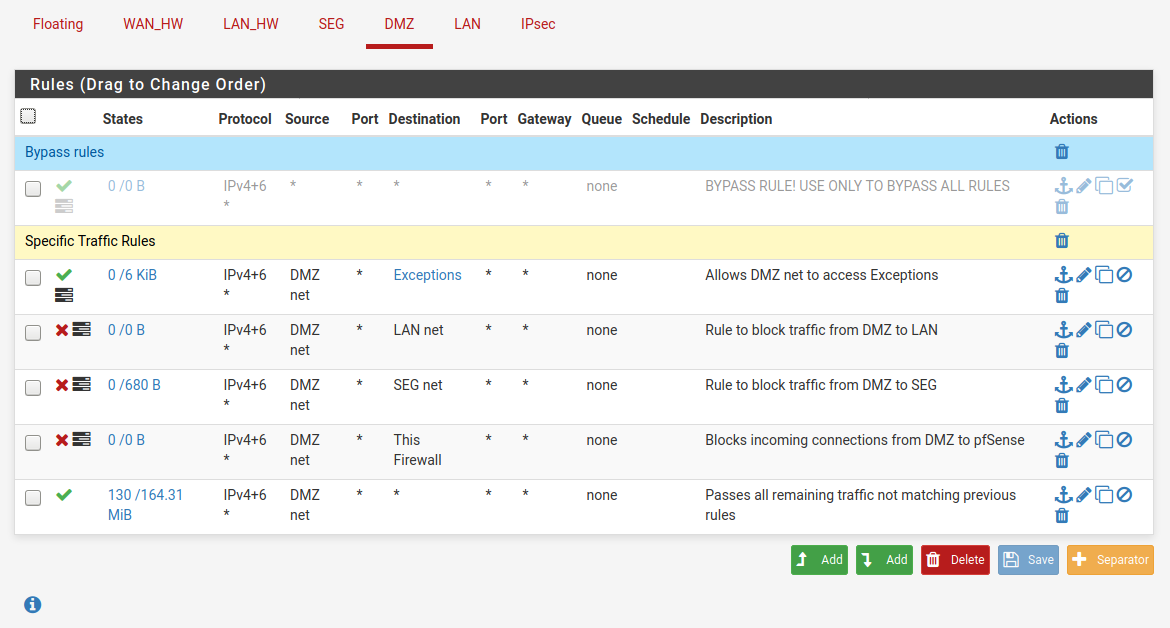
Also under Rules > DMZ I do not see any pfblocker rules (as expected!):
But still, this morning, the FW logs are filled with blocked connections on DMZ. Today, however, there's all kind of destination IP's in there (WAN, Amazon servers, Zscaler, etc...):
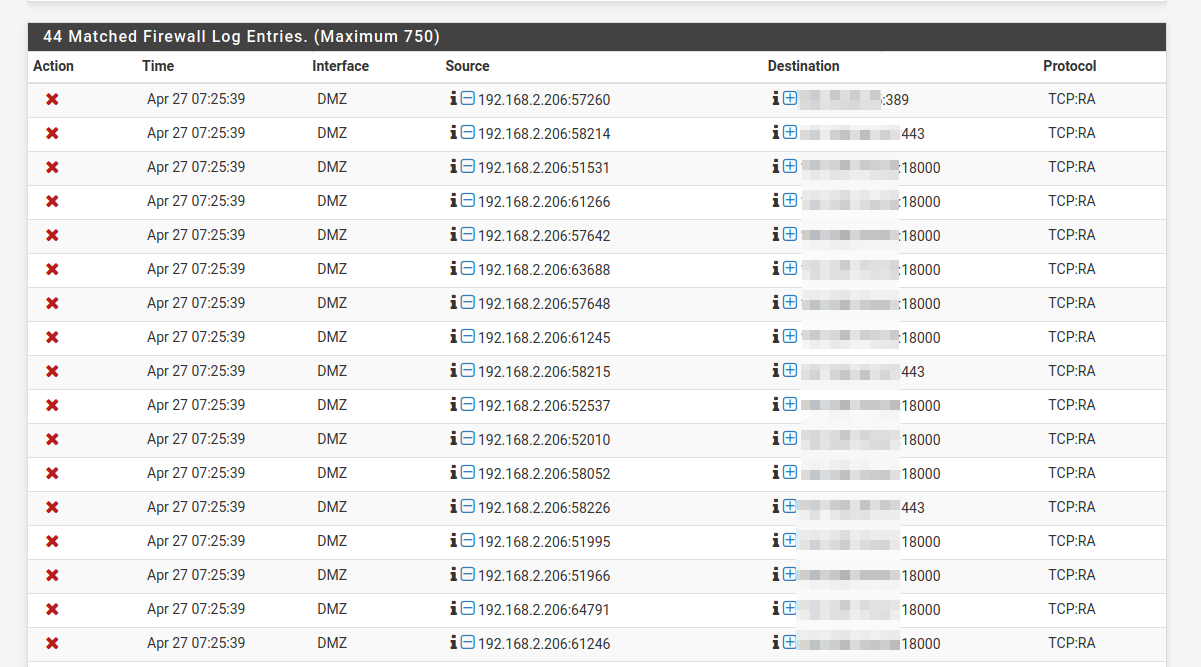
All (literally ALL) of these blocked connections have the following reason:
The rule that triggered this action is: @9(1000000103) block drop in log inet all label "Default deny rule IPv4"Until I sort this mess out, I will have to either commute to my office or physically bypass pfsense completely and connect the laptop directly to the cable modem.
Any idea of what's going on? I know these "TCP:RA" or "TCP:PA" could be asymetrical packets.... I am 99.9% sure I never had this before. Could my ISP be doing some sort of f*ckery with my connection?
-
@pftdm007 said in Bypassing DNSBL for specific IPs:
The rule that triggered this action is:
@9(1000000103) block drop in log inet all label "Default deny rule IPv4"Most easy solution : stop login the hits on the default block rules. (see Log > Settings )
Your 192.168.2.206 is a device that lives on DMZ, a VLAN.
Take it out of the VLAN to bypass "smart switch issues".
On the device, find why these "TCP:RA" or "TCP:PA" are send .... Is it a Wifi connected device ?Probably not a pfBlockerNG-devel issue. Disable pfBlockerNG-devel and these hits continue ?
-
@Gertjan said in Bypassing DNSBL for specific IPs:
Your 192.168.2.206 is a device that lives on DMZ, a VLAN.
Correct. So is my work cell phone. Same issue with my cell phone.
@Gertjan said in Bypassing DNSBL for specific IPs:
Take it out of the VLAN to bypass "smart switch issues".
OK will try to connect the laptop to a non-VLAN subnet, but in the meantime, all of my other computers/servers/networked printers, are all on LAN which is also a VLAN, and I have absolutely zero issues with any of them. Side note: everything is a lot more severe on LAN (more pfB/DNSBL lists, Snort, etc...)
@Gertjan said in Bypassing DNSBL for specific IPs:
On the device, find why these "TCP:RA" or "TCP:PA" are send .... Is it a Wifi connected device ?
My employer's IT are investigating on the device to see if everything is properly setup & running.... In the meantime, yes the laptop & cell are wifi connected to DMZ, but I already tried connecting the laptop via wired connection, same issues. That kinda eliminates possibilities of issues with my WIfi access point.
@Gertjan said in Bypassing DNSBL for specific IPs:
Disable pfBlockerNG-devel and these hits continue ?
When they release the laptop, I will reconnect to DMZ, and try. I am pretty sure I already tried, but I've done so many things in the last few days I am getting a bit confused so I will retry to make sure.
-
guys what is wrong in my custom config since all LAN subnet 192.168.1.0/24 is being filtered by DNSBL ? I want some computers (192.168.0.1 and 192.168.0.2) to be excluded from DNSBL filtering.
server:
access-control-view: 192.168.0.1/32 bypass
access-control-view: 192.168.0.2/32 bypass
access-control-view: 192.168.0.0/24 dnsbl
view:
name: "bypass"
view-first: yes
view:
name: "dnsbl"
view-first: yes
server: include: /var/unbound/pfb_dnsbl.*conf -
These are 'clauses' in the (unbound) config file :
server: .... view: ...They are recognised by the terminating ':'.
"view:" clause can exists multiple times.
"server:" clause can't (there is only one server)Or, you have two of them.
This one is thrown in by the pfBlockerNG-devel package :
server: include: /var/unbound/pfb_dnsbl.*confThat is, you edited it. pfBlockerNG-devel package added this :
# Unbound custom options server:include: /var/unbound/pfb_dnsbl.*confThis is the same thing :
# Unbound custom options server: include: /var/unbound/pfb_dnsbl.*confSo, I guess this would work for you :
server: include: /var/unbound/pfb_dnsbl.*conf access-control-view: 192.168.0.1/32 bypass access-control-view: 192.168.0.2/32 bypass access-control-view: 192.168.0.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yesBtw : Use this when you start to add unbound specific manual settings. It's part of the RTFM concept ;)
Be careful : if
server: include: /var/unbound/pfb_dnsbl.*confcan't be found by pfBlockerNG-devel when it start, it will automatically add such a clause again into the unbound config file.
Remember, pfBlockerNG-devel parses as a program, not as a human ^^
Adding a seconds "server:" clause probably breaks the unbound config .... -
@Gertjan thanks. removing server: clause solved problem. I hope pfBlockerNG-deve won't add it again
-
Hi, been reading through this post but confused. I want to allow my IP 192.168.1.16 to bypass the blocker, is this correct?
Go to Services/DNS resolver/General Settings then in Custom options write:
server:include: /var/unbound/pfb_dnsbl.*conf access-control-view: 192.168.1.16/24 bypass access-control-view: 192.168.1.16/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes -
server: access-control-view: 192.168.1.16/32 bypass access-control-view: 192.168.1.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes include: /var/unbound/pfb_dnsbl.*confThe changes are: -
access-control-view: 192.168.1.16/32 bypassMatches the host you want to bypass with a /32 to make it ONLY match the single address.
access-control-view: 192.168.1.0/24 dnsblMatches the rest of the subnet, assuming a 255.255.255.0 mask.
Moved the include: to the "dnsbl" view
-
Thanks very much! Is it possible to something more fine grained. Like allow 192.168.1.16 to www.blockedwebsite.com?
-
I have tried the following file and it appears to work, by adding a
local-dataentry in the view, and not allowing it to fall back to the globallocal-dataentries . It has the benefit of keeping the pfblockerng-generated entry# Allow these hosts to bypass pfblockerng server:access-control-view: 192.168.0.2/32 bypass view: name: bypass view-first: no local-data: "dummy.entry 60 IN A 10.10.10.1" server:include: /var/unbound/pfb_dnsbl.*conf -
Hi All,
I see this thread has been ongoing for a few years. How is that? Is there a systematic way to make suggestions so this gets added to pfBlockerNG-Devel? It seems like a reasonable request. If we can't get this added to the GUI is there something else the customer can do? i.e. whitelist the host for 15-60 minutes so they can get the info they need without getting blocked?
having end users manually point to a different DNS server just makes it a pain in the ass. Asking end users to run Opera in VPN mode is also extra steps and eventually I would want to block that as well except for a few users/ip addresses. Having a separate machine or VM on a different network is something our users would call us out on.
Do all the edits to these text files migrate during version upgrades or do we have to remember to re-do all the custom stuff we tinker with?
Thanks,
Joe -
@Gertjan I had this working 4 months back:
server: access-control-view: 192.168.0.20/32 bypass access-control-view: 192.168.0.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes include: /var/unbound/pfb_dnsbl.*confbut later HDD of my custom firewall crashed, and Covid-19 lockdown began.
Meanwhile, I took firewall home, replaced HDD, upgraded pfSense to 2.4.5, upgraded pfblockerng-devel to 2.2.5_33. Now my bypass doesnt work. Everytime Firewall restarts or Enable/Disable pfblockerng, it changes unbound custom option to:
server: access-control-view: 192.168.0.20/32 bypass access-control-view: 192.168.0.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes server:include: /var/unbound/pfb_dnsbl.*confi.e. it adds another server: clause in the last line. You mentioned that there can't be multiple server: clause.
bypass still doesnt work. Can you please help? -
Try this :
server: access-control-view: 192.168.0.20/32 bypass access-control-view: 192.168.0.0/24 dnsbl include: /var/unbound/pfb_dnsbl.*conf view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes -
Thanks @Gertjan for responding quickly.
I tried what you suggested, but bypass still not working.
Additionally, when i tried to enable/disable pfBlockerNG(with above custom option), it moved the include: to the last line, with additional server: clause.
server: access-control-view: 192.168.0.16/30 bypass access-control-view: 192.168.0.26/32 bypass access-control-view: 192.168.0.0/24 dnsbl view: name: "bypass" view-first: yes view: name: "dnsbl" view-first: yes server:include: /var/unbound/pfb_dnsbl.*confAnymore ideas worth trying?
-
@Gertjan said in Bypassing DNSBL for specific IPs:
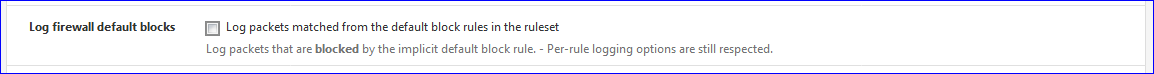
Most easy solution : stop login the hits on the default block rules. (see Log > Settings )
Sorry Gertjan, I am not following your suggestion here. Do you mean "the Settings tab under Status > System Logs"
-
@SmokinMoJoe said in Bypassing DNSBL for specific IPs:
Do you mean "the Settings tab under Status > System Logs"
Yep, this one:
@HiteshJain said in Bypassing DNSBL for specific IPs:
when i tried to enable/disable pfBlockerNG
pfBlockerNG is a program.
It's adds "server:include: /var/unbound/pfb_dnsbl.*conf" without taken in account if you have anything else already in there.
Normally, this isn't a big issue, because, normally, you do not need to enable and disable pfBlockerNG all the time.
And if you do, you have to visit the Resolver config page afterwards to "correct" the custom config options somewhat - if you have other, your own config settings entered.
The syntax has to be correct for unbound, who parses the config file.Btw : My proposition about how to format is : how I should do it.
There is another forum thread that details how to do so already, use that one to compare it with yours. -
@HiteshJain I have evolved the config I posted last month. It still allows pfblockerng to regenerate the configuration correctly, without corrupting it, and adds in a few addtional files which were needed.
# Allow these hosts to bypass pfblockerng server:access-control-view: 192.168.0.2/32 bypass # A view to bypass pfblockerng view: name: bypass view-first: no # This is needed to prevent falling back to the # global 'local-data' settings local-data: "dummy.entry 60 IN A 10.10.10.1" # Static host entries include: /var/unbound/host_entries.conf # dhcp lease entries include: /var/unbound/dhcpleases_entries.conf # Domain overrides include: /var/unbound/domainoverrides.conf server:include: /var/unbound/pfb_dnsbl.*conf -
-
@HiteshJain said in Bypassing DNSBL for specific IPs:
2 server: clause which as per @Gertjan cant be multiple.
I actually said this :
@Gertjan said in Bypassing DNSBL for specific IPs:
"server:" clause can't (there is only one server)
I guess I dive back into the manual ....
But before that : I've seen thousands of these type of files : you've seen one, you've seen them all.
See :
server clause - not server clauses.
Maybe several server: "Attribute keywords" can exist .... you tell me ;)
In real world examples I see only one ...
-
@Gertjan I didnt mean to offend you by quoting you. I apologize :). Probably, I misunderstood your statement because I dont have any idea on how Unbound works or even configured.
I got to read about Unbound only because google results directed me to pages where people more experienced than me mentioned about using custom options of Unbound to bypass few IPs , and I wanted exactly same in my pfSense.@Gertjan The way you explained in one of the earlier replies of yours, gave an impression that you know a lot about Unbound(& related stuff) and that impression is still maintained. I'd like to Thank you that you take time out to respond to newbie like me.
I tried to look at Unbound manual, but I gave up just after scrolling the page down to bottom of earth.
BTW, I am still searching for the right configuration thread from which I could compare my config. Current thread is most appropriate thread i could find so far.
Do you mind sharing the link of thread you mentioned earlier?