Time is not syncing
-
NTP is 100% UDP and with UDP your application (in this case the NTP service) is responsible for both sending out the queries and listening for replies. This is completely unlike compared to TCP where TCP does all the heavy lifting for you with setting up the connection and dealing with the return traffic. The consquence of this is that any application using a UDP based protocol has to listen on a socket to do anything, even if it's just a client querying other servers.
-
This post is deleted! -
@kpa said in Time is not syncing:
NTP is 100% UDP and with UDP your application (in this case the NTP service) is responsible for both sending out the queries and listening for replies. This is completely unlike compared to TCP where TCP does all the heavy lifting for you with setting up the connection and dealing with the return traffic. The consquence of this is that any application using a UDP based protocol has to listen on a socket to do anything, even if it's just a client querying other servers.
Okay. That doesn't answer my question though. My questions are:
- Why does it sync on WAN but not on any of the internal interfaces
- What does it mean by it is "listening" on those interfaces. I need to know from a routing perspective. I've done a ping sourcing those interfaces and pings from LAN, GUEST, etc come back with 0% packet loss. So if what you are telling me is true IF NTP is listening on though interfaces then UDP should not have a problem IF ICMP is fine.
-
-
Post your outbound NAT configuration, if WAN is deselected from the interfaces the NTP service might be trying to bind to another interface but the outgoing connections fail because of faulty outbound NAT settings.
-
It means literally what it says, listening for incoming data packets on the said interface. UDP is connectionless and stateless, an application that uses the UDP socket sends out a data packet (or multiples depending on the protocol) and then stops in listening mode to wait for the replies to the sent packets. Once those are received the data is processed and the loop starts again by either sending out more data or staying in listening mode for more incoming packets.
-
-
@brunovic said in Time is not syncing:
@johnpoz so it looks like my outbound NAT is manually configured. How will this prevent NTP from syncing?
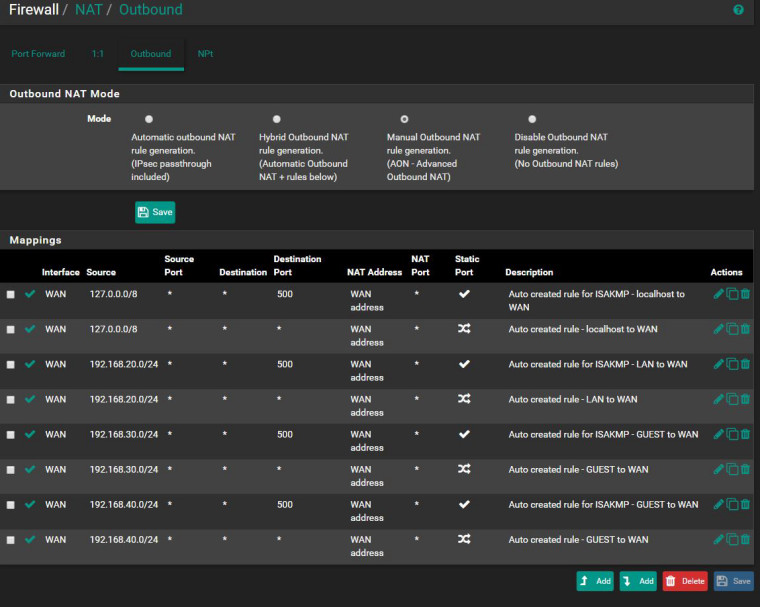
This is what you are looking for right?
-
@kpa if that is the case then why would it be listening to NTP packets on the LAN and not the WAN? That server is not on my internal network.
-
Your router can provide ntp to clients on your lan, that’s why it listens on the lan interface.
Have a look at the dhcp settings for your lan subnet.
-
Why do you have it in manual mode if all you doing is what automatic would be doing?
Where is your nat for vpn connections, your tunnel network would need to be natted? Try changing it to automatic.. You sure and the hell should not have to listen on wan to query a time server.
-
@johnpoz said in Time is not syncing:
Why do you have it in manual mode if all you doing is what automatic would be doing?
Where is your nat for vpn connections, your tunnel network would need to be natted? Try changing it to automatic.. You sure and the hell should not have to listen on wan to query a time server.
There is a reason to it. I can't remember but something was not working correctly in automatic mode.
-
Like what? Put it back.. And delete all your manual rules. You can always put it back to manual if this whatever it is comes back.. But if there is something that is not working in automatic mode that should be brought up so we can fix it, so other users using automatic don't have whatever this is issue is you think you were having.
-
@brunovic said in Time is not syncing:
There is a reason to it. I can't remember but something was not working correctly in automatic mode.
This makes me think you have some other misconfiguration as the root cause here. If your WAN is static, make sure you have a gateway set on Interfaces > WAN. And also check Interfaces > LAN and make sure you do not have a gateway set there. Same for your other local interface(s) like Guest.
-
@jimp said in Time is not syncing:
@brunovic said in Time is not syncing:
There is a reason to it. I can't remember but something was not working correctly in automatic mode.
This makes me think you have some other misconfiguration as the root cause here. If your WAN is static, make sure you have a gateway set on Interfaces > WAN. And also check Interfaces > LAN and make sure you do not have a gateway set there. Same for your other local interface(s) like Guest.
If you see my route print screen above the only quad zeros out are on the WAN interface.
-
@johnpoz said in Time is not syncing:
Like what? Put it back.. And delete all your manual rules. You can always put it back to manual if this whatever it is comes back.. But if there is something that is not working in automatic mode that should be brought up so we can fix it, so other users using automatic don't have whatever this is issue is you think you were having.
I'll keep it at manual. I am VPN into my network. If these manual routes were for that the last thing I want to to hose my own connection. All I need to know is what outbound NAT rule should I be seeing in order for NTP to work without having to select the WAN interface.
-
@brunovic said in Time is not syncing:
If you see my route print screen above the only quad zeros out are on the WAN interface.
That has nothing at all to do with what I said or why I asked. :-)
Read my message again and check the settings I mentioned.
-
@jimp said in Time is not syncing:
@brunovic said in Time is not syncing:
If you see my route print screen above the only quad zeros out are on the WAN interface.
That has nothing at all to do with what I said or why I asked. :-)
Read my message again and check the settings I mentioned.
What does the gateway setting do?
-
@brunovic said in Time is not syncing:
What does the gateway setting do?
It controls whether or not pfSense treats an interface like a "WAN" for NAT and other purposes. If you have no gateway on WAN, or a gateway set on LAN or other internal interfaces, it will confuse the code that tries to setup automatic NAT and other functions.
WANs must have a gateway selected in their interface settings (statics anyhow, dynamics will get this automatically), LANs must not have a gateway set on the interface settings.
-
Also if it helps one of the things I had to do was create rules that seperated VLAN traffic from one another. This is a bit reverse from Cisco where you have to assign VTI and create route statements before any VLAN can start talking with one another. However for pfsense the moment you create a VLAN everything is automatically routed between VLANs. I do not like that at all. All I want are the VLANs to be independant from each other and for them to get out to the internet on their own. If I want to route traffic between VLANs I should be able to opt-in not opt-out. As a result I ended making some janky solution where I created alias with all other VLAN networks but it's own and told it to go anywhere but those networks.
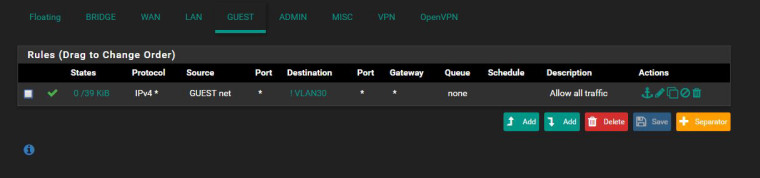
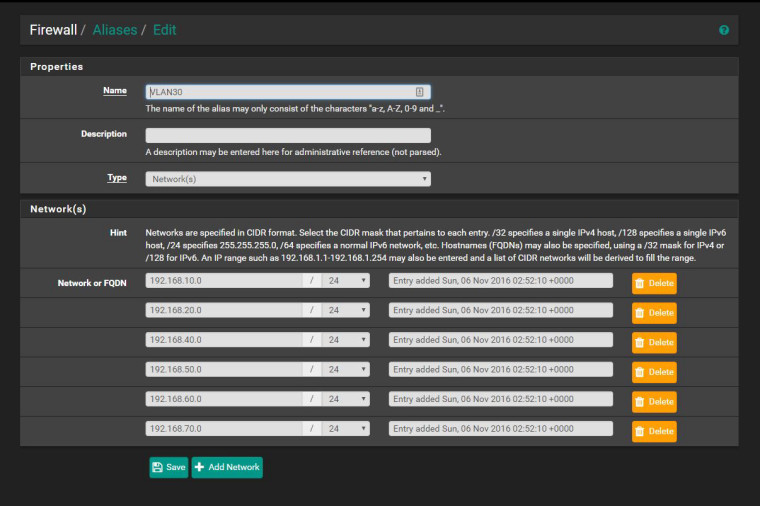
-
@brunovic said in Time is not syncing:
Also if it helps one of the things I had to do was create rules that seperated VLAN traffic from one another. This is a bit reverse from Cisco where you have to assign VTI and create route statements before any VLAN can start talking with one another. However for pfsense the moment you create a VLAN everything is automatically routed between VLANs. I do not like that at all. All I want are the VLANs to be independant from each other and for them to get out to the internet on their own. If I want to route traffic between VLANs I should be able to opt-in not opt-out. As a result I ended making some janky solution where I created alias with all other VLAN networks but it's own and told it to go anywhere but those networks.
Routing happens automatically, rules do not. They were allowed to do that because your rules allowed it. If you setup your rules properly, that won't happen. That's not related to this thread, however.
-
@jimp said in Time is not syncing:
@brunovic said in Time is not syncing:
What does the gateway setting do?
It controls whether or not pfSense treats an interface like a "WAN" for NAT and other purposes. If you have no gateway on WAN, or a gateway set on LAN or other internal interfaces, it will confuse the code that tries to setup automatic NAT and other functions.
WANs must have a gateway selected in their interface settings (statics anyhow, dynamics will get this automatically), LANs must not have a gateway set on the interface settings.
Anyways to answer your question there is no setting under the WAN interface to designate it as the gateway. And all other interface are not designated the gateway.
-
I feel like no one is talking to me like a network engineer. I never had this much difficulty trying to configure a Cisco router, firewall or switch. I may have screwed something up and I think the problem here is you guys are trying to troubleshoot my problem. I am pretty proficient enough to troubleshoot it myself. But the one answer I have not been getting it HOW exactly is the NTP communication routing? Is the NTP server sourcing the LAN interface going out the WAN or is it sending the NTP out the LAN interface. That is what is confusing me about the "interface section" under NTP Server Settings. If it is the latter then no wonder it isn't syncing because there are no NTP servers on my LAN network however IF it is the former. I have already done a ping test to the NTP server SOURCING the LAN interfaces and I got 100% replies. IF this is a NAT issued then pings would fail.