I can ping PFSense but PFSense can't ping back
-
Hello,
I have tried googling and searching these forums, but I have not been able to find an issue that seems similar to mine. My apologies if this has already been answered, but i'm honestly at a loss here.
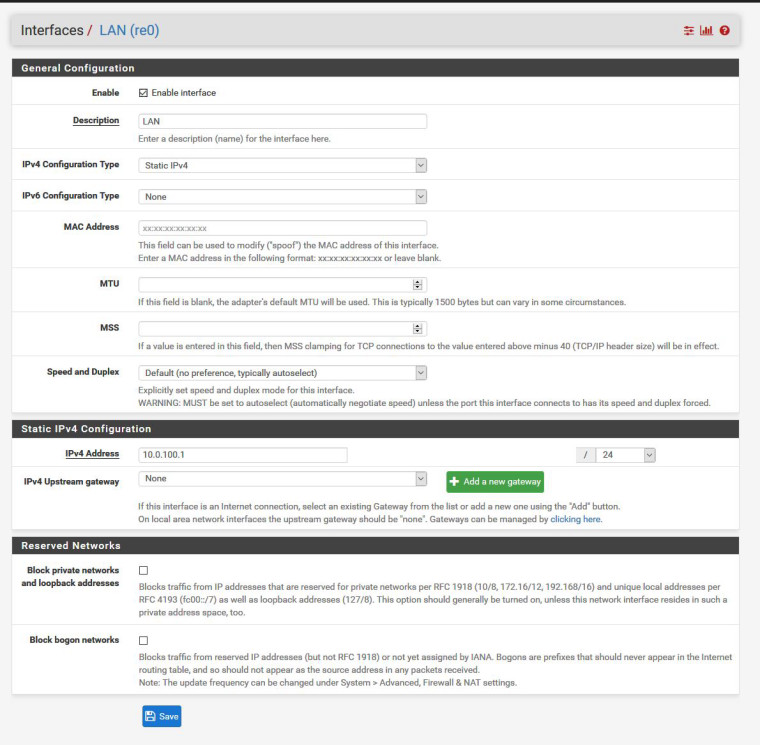
My PFSense LAN IP is 10.0.100.1
I have numerous devices on my LAN with static IP's in the 10.0.100.2 - 10.0.100.99 range and dynamic IP's in the 10.0.100.100-10.0.100.200 range.
All of my LAN devices can access the internet without issue. All of my LAN devices can ping each other and the LAN IP of the PFSense box. However, my PFSense box cannot ping any of my LAN devices. I noticed the other day that my port forward was no longer working properly so I started investigating. I haven't changed anything with my PFSense box since the last time that this port forward worked. I think the port forward not working is related to the fact that PFSense can't ping my LAN devices, but I have no idea why that would be.
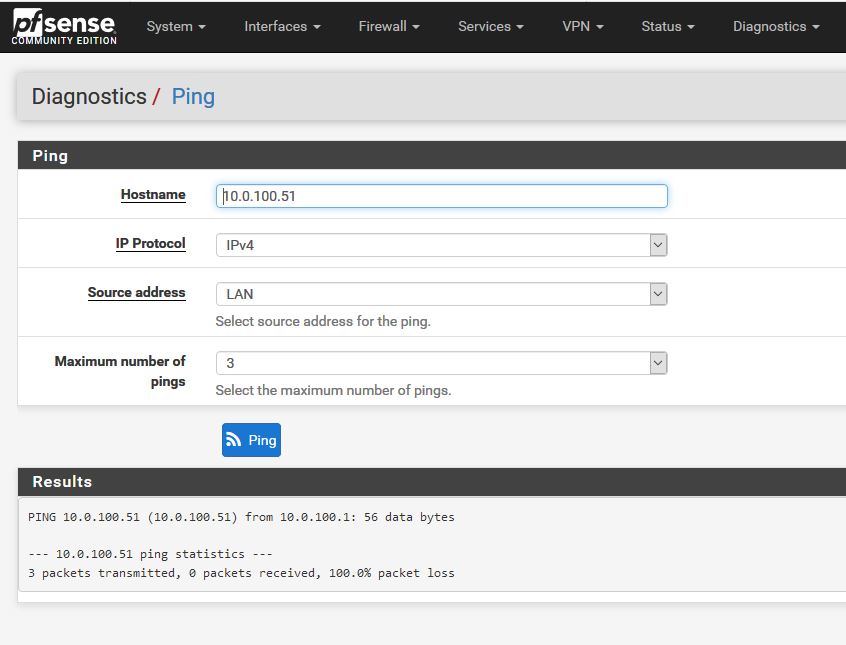
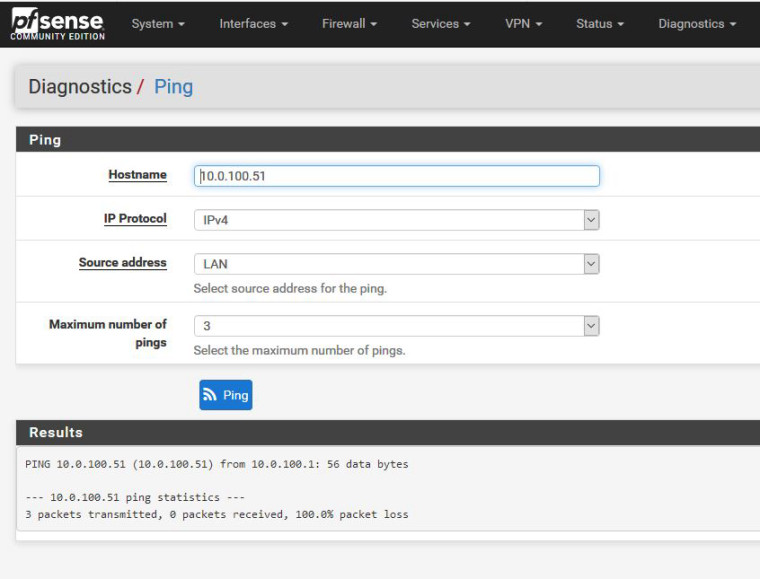
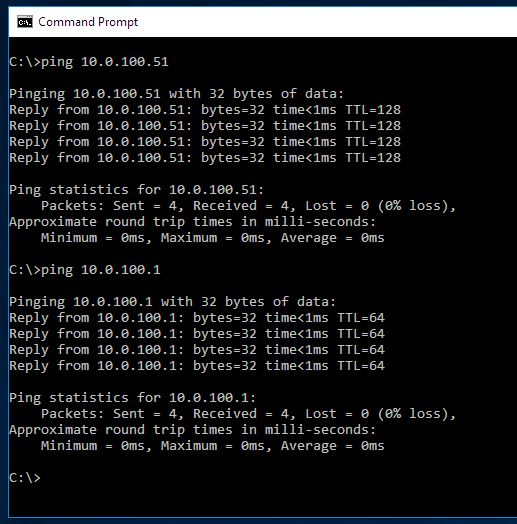
I have included screenshots showing that PFSense cannot ping on its LAN to 10.0.100.51 yet from a workstation on my network I can ping both 10.0.100.51 and 10.0.100.1.
Can anyone offer any insight or possible troubleshooting options that I could try?
Thanks!
-
Hi,
LAN interface settings and firewall rules ?
-
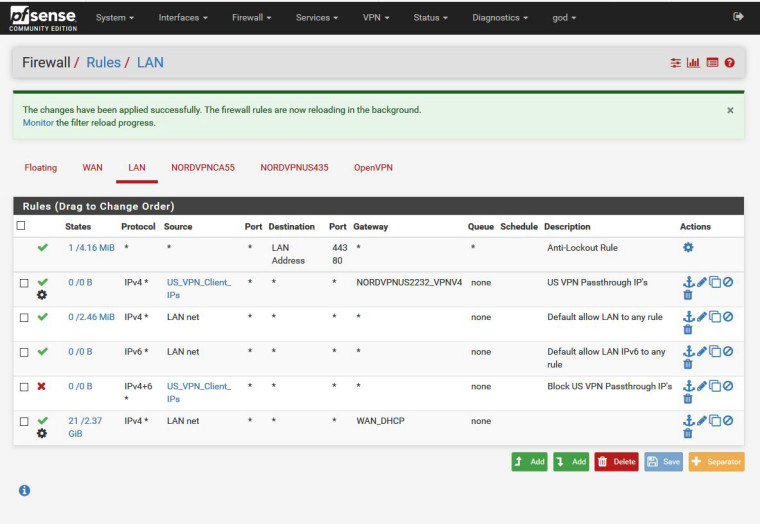
Nothing terribly special in either of those as far as I can tell. Screenshots are below. The "US_VPN_Client_IP's" is an alias for IP addresses ranged through 10.0.100.90 - 10.0.100.94. The blocking firewall rule only applies to those IP's to prevent them from accessing the WAN as I only want them to exit PFSense via the VPN tunnel established for them.
-
well do a sniff on your lan when you do your ping test from pfsense.. Does it send the ping? And is the ping going to the correct mac address?
Do you have any floating rules?
-
I do not have any floating rules defined.
The MAC address for 10.0.100.51 is: 00:22:15:9f:4b:51 which I see in the sniff results below as the destination of the ping, so the ping is being sent, but it is not reaching the destination or it is not being replied to.
As I can ping 10.0.100.51 from other machines on the network and receive a response, it seems like the ping is being blocked from leaving PFSense, but i'm not sure how or why that would occur.
Results from the sniff show:
09:50:01.664068 00:11:09:d7:2b:fa > 00:22:15:9f:4b:51, ethertype IPv4 (0x0800), length 98: (tos 0x0, ttl 64, id 7165, offset 0, flags [none], proto ICMP (1), length 84, bad cksum 0 (->f178)!)
255.255.255.0 > 10.0.100.51: ICMP echo request, id 16367, seq 0, length 64
09:50:02.671776 00:11:09:d7:2b:fa > 00:22:15:9f:4b:51, ethertype IPv4 (0x0800), length 98: (tos 0x0, ttl 64, id 1980, offset 0, flags [none], proto ICMP (1), length 84, bad cksum 0 (->5ba)!)
255.255.255.0 > 10.0.100.51: ICMP echo request, id 16367, seq 1, length 64
09:50:03.673660 00:11:09:d7:2b:fa > 00:22:15:9f:4b:51, ethertype IPv4 (0x0800), length 98: (tos 0x0, ttl 64, id 39043, offset 0, flags [none], proto ICMP (1), length 84, bad cksum 0 (->74f2)!)
255.255.255.0 > 10.0.100.51: ICMP echo request, id 16367, seq 2, length 64 -
Well pfsense put it on the wire to the correct mac.. So the problem has nothing to do with pfsense.
Wrong network masks on the client? What is between pfsense and the client? Switch I assume - any vlans setup on the switch, is the switch dumb?
-
@striker-0 said in I can ping PFSense but PFSense can't ping back:
00:11:09:d7:2b:fa
Hey
Try so
System/Advanced/Networking
-
The client is assigned its IP through a static DHCP mapping from pfsense so I don't think it is a wrong network mask. Additionally, pfsense cannot ping any LAN client, i'm just focusing on this one as this is the one I care about pfsense being able to port forward to.
There are two dumb switches between pfsense and the client in question. They have both been rebooted several times to clear anything they might be retaining internally.
There are no vlans setup in my environment.
-
@striker-0
try check " Disable hardware checksum offloading" in System/Advanced/Networking -
@konstanti I gave that a try, Thank You for the suggest! Rebooted pfsense to ensure it was applied. Same results on a ping test.
-
@striker-0
Show the output of the command
ifconfig -m
and arp -a -
@konstanti The forums are being weird and telling me that the content is flagged as spam. I've attached the requested results as a text file.0_1548526770045_Results.txt
-
@striker-0
So in a whole, all looks decently
What you can try- Change the LAN - re0 interface speed (e.g. media 100baseTX mediaopt full-duplex)
- Check the lan re0 - switch cable
- Connect any device directly to PFSense and try to ping .
- check the subnet mask in dhcp server settings and devices that have permanent ip addresses (255.255.255.0)
-
Client firewalls? If you changed anything such as your LAN subnet your desktops will change to "public" and block everything.
Even changing an interface on your router could trigger that.
https://www.netgate.com/docs/pfsense/nat/port-forward-troubleshooting.html
As you eluded to in your first post- once you figure out why your port forward does not work you will most likely also fix the ping.
-
If you can ping one way and not the other it is almost certainly a firewall on the device you cannot ping blocking it. One way ping success proves two-way traffic, routing (for the most part in most cases), and layer 2 are correct.
-
-
I would prefer not to change my link speed. It is currently running at 1000. If I switch it down to 10 or 100, I would be limiting my access to my internet as my internet connection is currently rated for 300. Additionally, this was working previously under the current link state, so I would be surprised if this would resolve anything. What is your rationale for checking this?
-
Tried a different cable, no change in results.
-
Tried connecting a device directly to pfsense. No change in results.
-
Subnet Mask is set to 255.255.255.0 in DHCP and aligns with the client.
-
-
@chpalmer I thought it could be client side firewall too. I normally leave those disabled on my internal LAN as they just cause unnecessary trouble. I have confirmed and they are still off.
-
Then you'll have to packet capture to see the pings going out and nothing coming back, look at the MAC addresses, etc.
-
@striker-0
Reducing the connection speed is just a test
I am very confused by the line in ping test
255.255.255.0 > 10.0.100.51: ICMP echo request, id 16367, seq 0, length 64
( I don't know what's the subnet mask )Should be so
length 98: 192.168.1.1 > 192.168.1.230: ICMP echo request, id 30542, seq 0, length 64
length 98: 192.168.1.230 > 192.168.1.1: ICMP echo reply, id 30542, seq 0, length 64
length 98: 192.168.1.1 > 192.168.1.230: ICMP echo request, id 30542, seq 1, length 64
length 98: 192.168.1.230 > 192.168.1.1: ICMP echo reply, id 30542, seq 1, length 64Can you put the packet capture file here ?
-
@derelict I have confirmed the firewall is off. This issue occurs across all devices on my network, the only constant is pfsense. Additionally, within my network other devices can ping each other and I can connect to the port I am trying to forward. Something is going on with pfsense or the hardware it resides on.