VLAN's not working with pfSense and HP1810-24G Switch.
-
Good day Everybody,
It’s been some time I was on the forum. Still I am in love with the pfSense firewall. Great product!
Lately I am figuring out VLANs. I think it is time to segregate my home network as well with VLANs. Read really a lot about it and it makes sense.Now since I have played around with VLAN’s on my home network I still not get it to work. Therefore I am hoping that you guys can help me in the right direction.

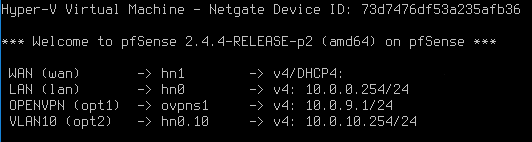
Let me explain what I have setup so far. My default LAN has the network 10.0.0.0/24. Now I have setup a new VLAN in pfSense called "VLAN10". The network ID VLAN10 owns is 10.0.10.0/24. The pfSense box, running on a server 2012R2 as a Hyper-V virtual machine, has 2 network interfaces onboard (LAN and WAN). The LAN of the pfSense box has IP address 10.0.0.254. Next I have configured a new VLAN under “Interfaces – VLANs” named VLAN10. As Parent Interface I have chosen the LAN interface “hn0 – lan”. The new VLAN10 I have assigned as a new interface under “Interface Assignments”. So now there is a new interface called “VLAN 10 on hn0 – lan (VLAN10). VLAN10 has a static 10.0.10.254/24 IPv4 address. So far so good. The next thing I have configured is under “Firewall/Rules/VLAN10” a “default allow VLAN10 to any” rule.
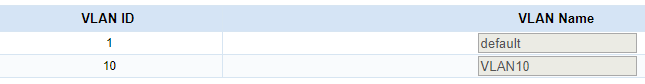
Then the switch configuration. The switch is a 24port HP 1810-24G (J9803A) manageable gigabit switch. On this device I have configured under “VLAN’s – VLAN Configuration” a new VLAN called VLAN10 with VLAN ID 10. The default VLAN has VLAN ID 1 (did not touch that). Under “Participation/Tagging” I selected VLAN 10 and changed port 12 to “Untagged”. On port 12 I have connected another workstation for testing purposes. Port 12 on VLAN 1 automatically changed to “Excluded”.
I thought this was it. So on the workstation connected to switch port 12 I’ve changed the IP address to 10.0.10.50 with gateway 10.0.10.254. Unfortunately I am not able to ping 10.0.10.50 or 10.0.10.254 from my other workstation in the Default VLAN 1 (10.0.0.50).

I hope you guys can help and teach me where I go wrong. I just don’t find the problem…
Kind regards in advance,
Herman. -
Hi Herman,
For what its worth I have a HP 1810-24G and have a baremetal pfsense box configures with three VLANS configured on the one LAN interface, with a BT Infinity connection on the WAN interface.
Unfortunately I'm not able to check my configuration to provide more information at the moment, but I'll try tomorrow.
In the mean time, is it possible the virtualisation of your pfsense box is part of the problem? How many NICs does the Windows 2012 hosts have? If you've two vNICs in the pfsense VM, how are they configured? (I'm more a VMWare guy, but the terminology over there is either NAT'd or Bridged). I'm going to guess you only have one NIC in the WIn2k12 host, but have two vNICS? I think the port the Win2k12 host is connected to will need to be a tagged member of VLAN10 as well as an untagged member of VLAN1, and you'd need to do something in the HyperV configuration to assign VLAN10 to one of the vNICs.
TD;DR - pfsense and HP1810-24Gs do work together nicely.
Cheers
Steve
-
Herman,
did you configure VLAN10 on any other port of the 1810G switch apart from port 12?
The VLAN10 traffic has to enter the switch somehow. Usually you configure a trunk-port in the switch and in pfSense and interconnect those two.May I suggest you read about VLANs and Trunking a bit
https://docs.netgate.com/pfsense/en/latest/book/vlan/index.html
https://docs.netgate.com/pfsense/en/latest/interfaces/vlan-trunking.htmlI have no idea how VLANs are handled in Hyper-V.
-
Hi jahonix,
Port 1 of the HP switch is connected to the Virtual Hyper-V LAN port of the pfSense. I've configured port 1 as a static trunk port on the switch. Makes no difference. I read also a lot about trunking ports. Thank you for providing even more info. will be appreciated.
I have a strong feeling that I have to look in the Hyper-V switch corner, like Steve Scotter mentioned. But I am not sure. So I have to play around with that some more.
Regards,
Herman -
Hi Steve-scotter,
Thanks for your reply. I was thinking in that direction as well. The pfSense LAN and WAN port are Hyper-V switches connected to a physical NIC on the Hyper-V (Server 2016) host. De server has two physical nic's on board en a 4 port Intel server NIC interface card. So in total the server has 6 physical nic's on board. In another post I've read some info about some power shell command regarding the Hyper-V nics.
Kind regards,
Herman -
Hello,
This is the thread I found regarding some powershell commands were @bobtheninja talks about. Does this make sense?
https://forum.netgate.com/topic/81161/pfsense-hyper-v-vlans/3
Any help appreciated
Herman -
Hi Folks,
I tried the following command. Somehow something went wrong.
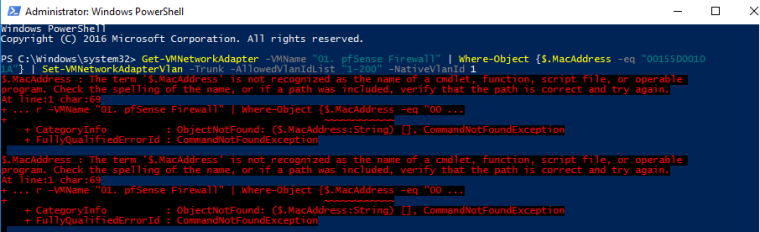
This is the solution @bobtheninja provides. Any ideas?
Regards Herman
-
I just went over this recently... Let me dig up the thread..
But yes you have to set trunk mode with powershell - not sure why messing with mac addresses? That thread is 2 years old..
BRB
edit: here you go
https://forum.netgate.com/topic/139891/solve-hyperv-2012-vlans-support-hn0/8I walked through how to do tagged vlans, with pictures ;)
-
Hi @johnpoz,
Wow. That is a lot of information. I have to dig in there. You were right. I messed up things. Messing around with the mac address was indeed no good idea!!! Now I have to wait till I am home because my whole config isn't accessible anymore :-(
I have to figure out the exact power shell command to do your trick. I have 2 nic's in de pfsense vm. A LAN and WAN. So I presume that I only have to alter the LAN vlan settings right?
For now I am not able to connect to the network anymore! :-( I hope I can reverse the settings i've made...
Cheerz Herman
-
Hello Johnpoz,
I am back in business again. Was able to reverse my mes sup with the MAC address.
Let me show you what i Have done. That is after the restore :-)
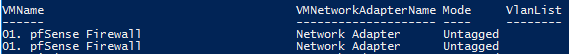
Above you see the 2 virtual network adapters connected to my pfSense. one of them is the LAN and the other would be the WAN. cannot see that here. I think that is the reason why @bobtheninja was using the MAC address part???
Next I executed the following command.

After that evrything stops working. When setting the mode back to Untagged everything is working again.
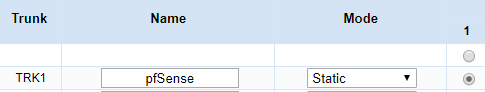
My HP 1810 switch is configured this way;
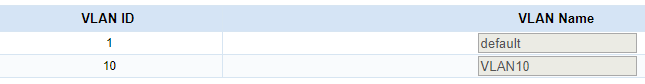
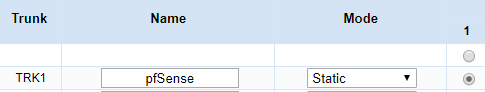
Port 1 on the switch that is connected to the pfSense LAN interface is configured as a Trunk port
Any suggestions?
Kind regards Herman
-
@herman said in VLAN's not working with pfSense and HP1810-24G Switch.:
Hello Johnpoz,
I am back in business again. Was able to reverse my mes sup with the MAC address.
Let me show you what i Have done. That is after the restore :-)
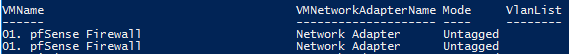
Above you see the 2 virtual network adapters connected to my pfSense. one of them is the LAN and the other would be the WAN. cannot see that here. I think that is the reason why @bobtheninja was using the MAC address part???
Next I executed the following command.

After that evrything stops working. When setting the mode back to Untagged everything is working again.
My HP 1810 switch is configured this way;
Port 1 on the switch that is connected to the pfSense LAN interface is configured as a Trunk port
Any suggestions?
Kind regards Herman
Another screenshot how the interfaces are shown in pfSense;
-
You sure hp uses trunk in the same same with as cisco? WTF is static mode? Where are you tagging specific vlans?
-
Yes, there is a difference between HP and Cisco:
https://networkingnerd.net/2011/02/02/when-is-a-trunk-not-a-trunk/ -
^ exactly!!! I thought they were different!
-
On the old forum I posted a question few years ago and ran into this terminology problem myself, you where part of it too johnpoz
 , misunderstanding all around as same here, but cannot find the post...
, misunderstanding all around as same here, but cannot find the post... -
I have not had to touch an HP switch for years and years - and to be honest have no desire to any time soon... But yeah I recall terminology is different that cisco ;)
-
@johnpoz said in VLAN's not working with pfSense and HP1810-24G Switch.:
You sure hp uses trunk in the same same with as cisco? WTF is static mode? Where are you tagging specific vlans?
When I read the document Pipin provided HP uses tagged ports to carry multiple vlans.
Under mode there are the multiple option;
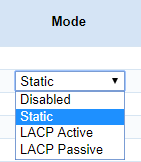
Gr. Herman
-
@pippin said in VLAN's not working with pfSense and HP1810-24G Switch.:
On the old forum I posted a question few years ago and ran into this terminology problem myself, you where part of it too johnpoz
 , misunderstanding all around as same here, but cannot find the post...
, misunderstanding all around as same here, but cannot find the post...Hi Pipin, I really hoping you will ... :-)
It seems that my HP 1810-24G is the pain in the ass here.
Gr. Herman
-
@johnpoz said in VLAN's not working with pfSense and HP1810-24G Switch.:
I have not had to touch an HP switch for years and years - and to be honest have no desire to any time soon... But yeah I recall terminology is different that cisco ;)
I have the feeling you are not a really big fan of HP switches

You are tending more to Cisco? Is Unify also a good product?
gr. Herman
-
Not that not a fan of them... Just much more experience with Cisco, and the few times I have had to deal with HP.. Not impressed with them compared to the cisco use to working with.
For the price of unifi - you could get a pretty much full featured L3 switch from cisco small business line. The sg300 or sg350 line.. I just saw a sg350-28 on amazon for $179.. Its feature set far exceeds the same sort of price point from unifi.