Port forwarding IP cams, is it that bad?
-
I have Blue Iris server set up, it is a IP camera recording software. The server can be accessed only through IPsec. I also have 36 cameras in over 25+ locations. 24 of them passing RTSP traffic through IPsec but the rest I have no options for IPsec "yet". I know port forwarding cams is a bad practice for many reasons.
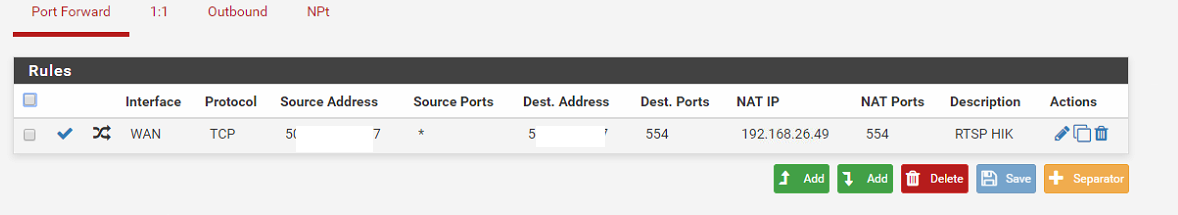
What if I make this port forwarding rule? Can the traffic still be intercepted?
-
RTSP is not crypted so generally you don't want to send it plain over the Internet.
-Rico
-
@Rico said in Port forwarding IP cams, is it that bad?:
RTSP is not crypted so generally you don't want to send it plain over the Internet.
-Rico
So, its either through VPN or as it is?
-
Yes VPN would be the best solution.
If not possible for any reason maybe you can use SRTP which is AES encrypted.-Rico
-
Depending on the sensitivity of the video feed, I wouldn't have a problem with a NAT'd cam locked down to a specific source address.
-
@KOM said in Port forwarding IP cams, is it that bad?:
Depending on the sensitivity of the video feed, I wouldn't have a problem with a NAT'd cam locked down to a specific source address.
Its a camera that records audio/video of patients interacting at the front desk when they register to be patient, discharge their treatment and etc. Company sometimes reviews certain episodes if patient and employee information doesn't match. We have a disclaimer for all patients entering our offices that there is live video recording of audio and video. According to MD laws as company's lawyer said is enough to have a permission.
And of course its for any theft that might happen, like few days ago a patient stole purse with credit cards and cash.
-
I don't know if there would be any specific HIPAA regulations involved with that.
-
@KOM said in Port forwarding IP cams, is it that bad?:
I don't know if there would be any specific HIPAA regulations involved with that.
Yea, i will have to research on my own, I just wanted to see what are my options in terms of secure networking.
-
@KOM said in Port forwarding IP cams, is it that bad?:
I don't know if there would be any specific HIPAA regulations involved with that.
I was thinking may be VPN small offices to a branch office pfSense <>Sonicwall, and then all Sonicwalls to HQ Sonicwall where Blue Iris server resides because our Sonicwalls support only 20 VPNs.
-
@pfrickroll said in Port forwarding IP cams, is it that bad?:
our Sonicwalls support only 20 VPNs
Boo!!!!
-
@KOM said in Port forwarding IP cams, is it that bad?:
@pfrickroll said in Port forwarding IP cams, is it that bad?:
our Sonicwalls support only 20 VPNs
Boo!!!!
Yea, the company doesn't plan their future very well and I had to take over from previous guy with my helpdesk experience.
-
In the EU this kind of traffic uncrypted via Internet is not be possible without the risk of serious penalties.

-Rico
-
IIRC anything into/out of medical facilities like that needs encrypted. There could be potential privacy violations if that video stream were intercepted and faces/names/etc were visible. I haven't read through HIPAA in years though so that may not be specifically called out, but I wouldn't take my chances on that.
Even if it weren't medical, though, I don't trust cameras unencrypted over the Internet. Even if the source is locked down/password protected. It's not worth the risk.
-
Rule of thumb: You want any traffic leaving your building encrypted.

-Rico
-
@pfrickroll said in Port forwarding IP cams, is it that bad?:
Its a camera that records audio/video of patients interacting at the front desk
Your going to send patients video streams across the public internet unencrypted? Yeah I would get ready for your lawsuit as soon as someone that had a buddy that is a lawyer or someone that has too much time on their hands finds out about it and thinks they can make a buck..
There is is one thing if you don't care about video of watching your cat walk around the house being in the clear or anyone else can view that... But when your in your building, and have video of "customers" giving out info like their names and place of residence and any other personal info that might come up in a conversation with checking in, etc.
You better hope such stream or recording is in accordance with all and any appropriate regulations and or laws in your area.
-
This has me a bit curious......
The only time this video would become "vulnerable" to prying eyes is whenever it is viewed over the Internet or through the air via WiFi.
Don't most (if not all) applications used to view video remotely already encrypt the connection using SSL (https) ?
Couldn't the video be assumed "safe" from prying eyes as long as in the case of accessing the video stream via the Internet the connection was via SSL?
I find it hard to believe all these DVR manufacturers would not address this security (and perhaps legal) issue right from the design boards.
If not, there are millions and millions of cameras in private and public locations recording what could be construed as sensitive information that is being sent elsewhere via the Internet every second of every day.
Don't most modern DVR's and video cameras have encryption capabilities?
-
@HansSolo said in Port forwarding IP cams, is it that bad?:
Don't most (if not all) applications used to view video remotely already encrypt the connection using SSL (https) ?
I wouldn't make that assumption. Unless they advertise it as such, I would bet they're aren't using any encryption at all.
And yes, there are tons of live video sources that have no idea they're streaming to the world on an unsecured camera.
-
@HansSolo said in Port forwarding IP cams, is it that bad?:
If not, there are millions and millions of cameras in private and public locations recording what could be construed as sensitive information that is being sent elsewhere via the Internet every second of every day.
Yup exactly!!
There are also millions and millions of that that firmware is utter crap and exploits out the ying yang, etc..
If your camera doesn't clearly state its being encrypted - then most likely its NOT... And even if was - you believe that is up to specs for whatever HIPPA laws or other regulations there might be for sending patient info across the public net.
-
HTTPS or not, if the port is exposed and the stack is weak, it can be accessed remotely by attackers.
Doesn't matter if you think you are not worth finding, scanners will find you.
https://www.shodan.io/explore/tag/webcam