Pfsense WireGuard Client Working ( With Catch 22 )
-
Dear Community,
This tutorial guide details dead simple GUARANTEED process to get WIREGUARD Client up and running on pfSense Firewall. Some of you may remember my work with GETDNS and STUBBY. This installation is for commercial WireGuard Clients ONLY ! - where creation of keys and how to exchange them is not needed. The keys are generated and managed by your WireGuard VPN service provider - in my case - TorGuard.1 - This is what I did and it worked out great. First go to https://pkg.freebsd.org/FreeBSD:11:amd64/latest/All/ as pfSense is based on FreeBSD 11 - the current WireGuard release is version - July 2019 wireguard 0.0.20190702 . To get started install bash # pkg install bash ( as it is need by WireGuard-GO ). Scroll down page on FreeBSD package website ( find wireguard and wireguard-go ) Then issue these commands: # pkg add -f https://pkg.freebsd.org/FreeBSD:11:amd64/latest/All/wireguard-go-0.0.20190517.txz and # pkg add -f https://pkg.freebsd.org/FreeBSD:11:amd64/latest/All/wireguard-0.0.20190702.txz - As I said, this will install latest versions of these packages. W are now ready to get this going and up and running. Just follow these steps below:2 - To begin you need to get your WIREGUARD configuration files from the TORGUARD website. To do so login your TORGUARD account then go to Tools ( along the top of Login Page ) from drop Down Menu click on Enable WIREGUARD Access. You will then be in your TorGuard Account Area. You will see this message along the top : Below is a list of WireGuard VPN Servers, Please click enable in front of the servers you like to connect to, and use the returned keys shown to connect. Currently, TORGUARD offers WIREGUARD Servers in USA - New York ( quite actually situated in Clifton, New Jersey ), Asia - Singapore and Europe - UK. Click on your preferred Server - Enable WIREGUARD. This will result in a green box below the now grayed out box - which states now Disable WIREGUARD- naturally leave your server enabled as you want to connect to the now enabled server. Next, Download Config file as the box allows you to do now that you have enabled your WIREGUARD Server. You will also see in the adjoining box the following :
Location VPN Server Keys Manage
USA - New York 1 159.xx.xxx.xx:xxx Server Public key: 62lKu9HsDVbyiPenApnc4sfmSYTHOVfFgL3pyB+cBL4=
Your Private Key: cE2ecALeE5B+urJhDrJlVFmf38cJLAvqekONvjvpqUA=
Your Address: 10.xx.x.xxx/24
3 - Now I used this guide as the template for my manual installation of WIREGUARD on OPNsense see here : https://genneko.github.io/playing-with-bsd/networking/freebsd-wireguard-quicklook/ I will make this simple for you step by step. You may sing and / or hum along as we proceed.
A- First - configure WireGuard Client. TorGuard, AzireVPN, VPN.ac, Mullvad, IVPN, are commercial VPN providers which offer LIVE ! WireGuard Services now. I use TorGuard here is a sample file. Keys are dummies - only used for illustrative purposes in this tutorial- Use your real WireGuard configuration file here: Create file by command line - # nano /usr/local/etc/wireguard/wg0.conf - and enter the configuration file below ( copy and paste ) - substitute your real one. Save and Close. Done with this file.# TorGuard WireGuard Config [Interface] PrivateKey = foxZRnIh9gZpWnl+zEiKa0EJ2rdCGroMWm02gaxSc9Q= ListenPort = 51820 DNS = 104.223.91.210 Address = 10.xx.x.xxx/24 [Peer] PublicKey = 62lKu9HsDVbyiPenApnc4sfmSYTHOVfFgL3pyB+cBL4= AllowedIPs = 0.0.0.0/0 Endpoint = 159.xx.xx.xxx:xxx PersistentKeepalive = 25B - Secondly, run command via SSH # wg-quick up wg0 ( wireguard-go is in package and this action creates wireguard interface ) You may also run # wireguard-go wg0 to create wg0 - however, I prefer to use the first method mentioned here.
4 - Configure WireGuard Service with rc.d - for automatic startup/shutdown of the tunnel. In order to achieve this there’s already an rc.d script /usr/local/etc/rc.d/wireguard which came with the wireguard package. You need to issue this command : # mv /usr/local/etc/rc.d/wireguard /usr/local/etc/rc.d/wireguard.sh then enter the file - # nano /usr/local/etc/rc.d/wireguard.sh Then go to bottom of file - lines 46 and 47 - change : ${wireguard_enable="NO"} to : ${wireguard_enable="YES"} and then add wg0 on line 47 : ${wireguard_interfaces=""} to : ${wireguard_interfaces="wg0"} ( wgZero ) - Save and Close - Make it executable, I run two commands - it works for me: # chmod a+x /usr/local/etc/rc.d/wireguard.sh # chmod 744 /usr/local/etc/rc.d/wireguard.sh - Done with this file.5 - Now head to pfSense WEBGUI in order to configure Wireguard Interface ( created earlier ) and FireWall Rule. First, go to Interfaces > Assignments -you will see wg0 interface - click (+) add button /symbol. Once the wg0 interface is listed as OPT ( 1 - 2 depending on your setup ) - Click underneath it - - enter check in " Enable interface " - and enter description - I call mine " WIRE " - DO NOTHING ELSE HERE ! Save and Apply - Done with this phase.
Second - Firewall Rule - go to Firewall > NAT > Outbound > Once on this Landing Page put a Dot in radio button Hybrid outbound NAT rule generation - Click on Save - Do Not - Repeat Do Not Click Save and Apply At This Time - Instead Click on Add Square with Up Arrow (underneath Mappings ) on the page which opens change Interface from WAN in drop down menu to your Wireguard ( wg0 ) Interface which you created and labeled previously - in this example
" WIRE " . Next - Change Source Address to " LAN NET " . You must manually enter your LAN NET . For example if your LAN Address is 192.168.11.10 - then enter 192.168.11.0/ 24 . Finally, set ( leave ) Translation/target to Interface address. Enter " Description -e.g. " Made For Wire " now Click " Save " at bottom of page. You will be taken back to Firewall:Nat:Outbound Landing Page - Click on " Apply Changes " in right upper hand corner - Done with Firewall Rule for LAN. Repeat this Firewall Rule Operation for all of your other LAN Interface Subnets if you choose to do so.
6 - Your WireGuard Client is now installed and ready - you must enter command # /usr/local/etc/rc.d/wireguard.sh restart in order to start it up. Lastly, issue command # wg show which prints out your WireGuard Connection statistics and configuration. Sample output for wg show below:interface: wg0
public key: cE2ecALeE5B+urJhDrJlVFmf38cJLAvqekONvjvpqUA=
private key: (hidden)
listening port: 51820peer: 62lKu9HsDVbyiPenApnc4sfmSYTHOVfFgL3pyB+cBL4=
endpoint: 159.x.xxx.xxx:xxx
allowed ips: 0.0.0.0/0
latest handshake: 1 minute, 46 seconds ago
transfer: 3.35 MiB received, 859.23 KiB sent
persistent keepalive: every 25 seconds7 - The Catch 22: Good and Bad News. When you reboot your pfSense FireWall, the WireGuard interface will be removed. Further you will be asked and required to " Assign Interfaces " again. You will see this message : Network interface mismatch - Running interface assignment option - In order to get your WireGuard VPN up and running again simply follow these steps after reassigning your vlans ( if you have any ), WAN, and LAN interfaces. All your network configurations will have been preserved including your firewall rules, addresses and so on.
A - Remember your WireGuard interface ( wg 0 ) was removed on reboot. so, simply repeat this step to add it again: In the pfSense WEBGUI go to Interfaces > Assignments -you will see wg0 interface - click (+) add button /symbol. Once the wg0 interface is listed as OPT ( 1 - 2 depending on your setup ) - Click underneath it - - enter check in " Enable interface " - and enter description - I call mine " WIRE " - DO NOTHING ELSE HERE ! Save and Apply - Done with this phase.
B - In order to get WireGuard up and running again - simply issue this command once again - # /usr/local/etc/rc.d/wireguard.sh restart
You do not have to recreate any of your Firewall Rules as they are all still there. Your WireGuard VPN connection is now reestablished.
Last Notes and Thoughts: I realize that this implementation is not perfect albeit it works. I run OpenVPN on pfSense as well. You must disable OpenVPN client before and when running WireGuard. I will write up a tutorial to switch between OpenVPN and WireGuard on pfSense. Currently, I am running WireGuard on pfSense 2.5.0 Development SnapShot VmWare Machine. pfSense 2.5.0 is based on FreeBSD 12 - so you must modify url's thusly and get the packages from : https://pkg.freebsd.org/FreeBSD:12:amd64/latest/All/ If anyone can provide me with a solution that will allow WireGuard interface ( wg0 ) the ability to survive a reboot; I will be most appreciative and edit this tutorial to include that solution.Peace and Grace Be Unto All God's Creation
-
@ubernupe said in Pfsense WireGuard Client Working ( With Catch 22 ):
Some of you may remember my work with GETDNS and STUBBY.
Yup sure do - complete and utter waste of time and effort.. Guessing this in the same line?
If someone wants to run wireguard, wouldn't it just be easier to run it on another box/vm?
If your actually worried about security, etc.. dicking with the stuff the makes up your "firewall" is not something I would suggest anyone do to be honest..
In my opinion, take it how you will.. Wireguard will be added to pfsense when the developers deem it ready to be added, or someone creates a package that adds it that the developers sign off on and include in the package system..
And such off the reservation sort of "hacks" your firewall system is not something I would recommend anyone play around with.. But maybe that is just me ;)
-
@johnpoz
Dear johnpoz,
Hello and I hope that you are well. First, let me begin by stating that I do understand and accept the validity of your comments and criticisms of " hacking " pfSense FireWall. Just to let you know my thinking, I love pfSense and I think that you guys do a great job overall. However, as I am retired ( English Teacher ) with time on my hands - I do love to " dick " around with network applications - especially those in the realm of security. There are other BSD based firewall distros that already offer both getdns plus stubby as well as wireguard packages in their repositories. pfSense seems to lag behind often; moreover, as I search for answers that I have about these solutions - I find that many other pfSense devotees also are seeking how to implement these emerging protocols - e.g. - DNS PRIVACY and WIREGUARD. My tutorials are more " proof of concept " than anything and yes - I realize that I am " pushing the envelope ". However, the fact that you call DNS PRIVACY Project work : https://dnsprivacy.org/wiki/display/DP/DNS+Privacy+Project+Homepage ( getdns and stubby ) " a complete and utter waste of time and effort " and that " Wireguard will be added to pfsense when the developers deem it ready to be added, or someone creates a package that adds it that the developers sign off on and include in the package system. " proves the point that pfSense is unresponsive to many of the interests of pfSense users . I run a different edge router than pfSense currently, and I can assure you that I will not post any additional " hacking " solutions on the pfSense Forum.
However, I am left wondering why pfSense is such a top down distro in its' decision making and does not more readily respect the input or feedback from its' user base. I dare say that some of your replies to me smack of disdain, dismissal and outright mockery. I respectfully submit to you that the work I have done here is reflective of the work being done across a wide spectrum of Linux and BSD distributions - and I suggest that you do read what work the DNS Privacy Project is actually doing. Again Peace and God Bless
ubernupe -
you should not take it personally, johnpoz is like that, you can teach english, he can teach networking and security, people will read your tutorial and try to mimic it, if they do something wrong it may be dangerous for a firewall or it could interfere with future updates, alot of thing can go wrong. it's the duty of a moderator to advise against stuff like this, if you want something to be officially added to pfsense you should go to redmine.pfsense.org and ask for a new feature. that said if someone is interested in your work no one will prevent him from following it. provided they understand that they do so at their own risk.
The protocol called DNS over TLS run on port 853, network operators that dislike DoT can easily block it. Most corporate networks will in fact do this by default, then we have all the other stuff like doh doc
It is generally possible to tell where a TLS connection is going even without looking at DNS since the name still travels in plaintext.. there is little/no privacy differential when using DNS over HTTPS
if it's your concern. the request will be in any case decrypted by the dns you query. so moving your personal information from your ISP to google IMHO it's bullshit, an excess of privacy. the other reason to have DNS over HTTPS / TOR it's to break the censorship in your country so you are free to search for all that illegal stuff / censored pornography that your country impose. i really don't think any of this have anything to do with a product of a certain seriousness that points to security.
this is only my 2cents -
@kiokoman
Dear kiokoman,
I opened my reply to johnpoz by stating that I do understand and accept the validity of your comments and criticisms of " hacking " pfSense FireWall. Further I ended with I can assure you that I will not post any additional " hacking " solutions on the pfSense Forum. On the topic of DNS OVER TLS - you can also run that protocol on Port 443 as many of the providers here from The DNS PRIVACY Project : https://dnsprivacy.org/jenkins/job/dnsprivacy-monitoring/ - offer DNS TLS on port 443. Also, DNS OVER TLS is suggested to be run in conjunction with a secure VPN service. Again, thank you and johnpoz and I will be a good team player
Peace
ubernupe -
-
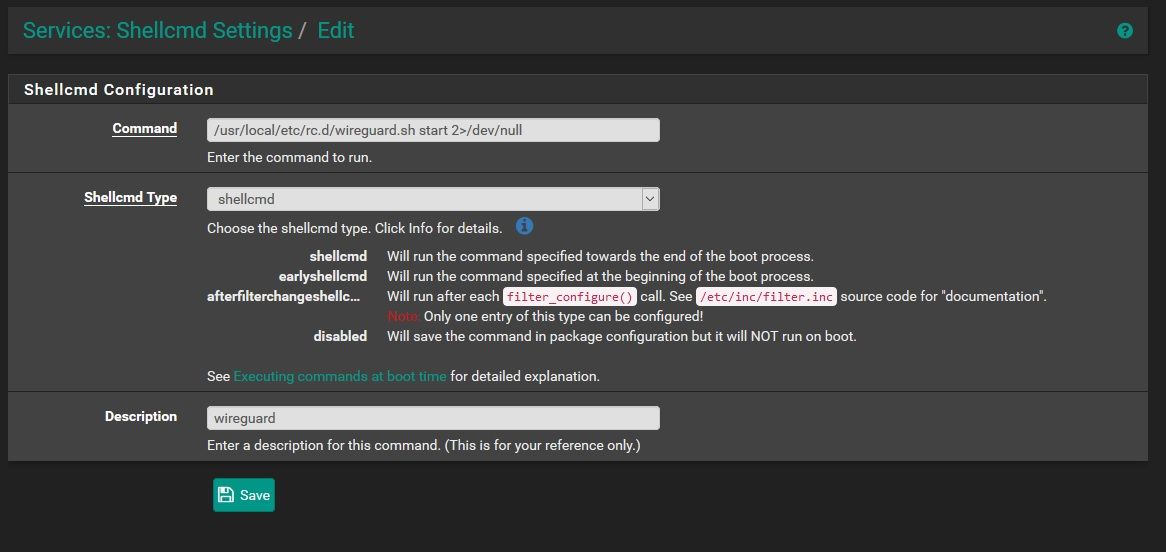
The shellcmd utility is used to manage commands on system startup.
i suggest to take a look to this package, you can put that script inside shellcmd, this way it will survive even after an upgrade of pfsense -
@kiokoman
Dear @kiokoman,
Hello and I hope that you are safe and well in these times. I am writing to ask you if you would be so kind as to provide the correct manner to enter this solution listed above :vi /etc/pfSense-rc
/usr/local/etc/rc.d/wireguard.sh start 2>/dev/null
to shellcmd utility - so that WG0 survives ( will survive even after an upgrade of pfsense )
To be clear - I am asking for the exact entry and type - thanks
Peace
-
Hi, I got it working fine until I wanted to change config in: /usr/local/etc/wireguard/wg0.conf to other server details.. when I have updated the config and use command: wg-quick down wg0 and then wg-quick up wg0, the internet just stops working... do I need to change some other places or restart something else in order to load new wireguard server config ? And seems like battle.net games aint working, need to use another wireguard vpn on windows in order get it working so seems like the NAT is not working right ?
-
@ubernupe i don't have wireguard installed but i suppose that something like this should work
-
Dear @kiokoman,
Hello and thanks for the advice.I tried your suggestion - and that does not work ( at least on a test VMWare Machine ) - maybe it will work on real hardware. I am going to try earlyshellcmd and see how that works. Adding the line /usr/local/etc/rc.d/wireguard.sh start 2>/dev/null
works fine. However I am running 2.5.0 Development Snapshot - so I really hope that someone here can help me out when it comes to using proper shellcmd utility entry. anyway, thanks - and I do appreciate your assitance andreply. Stay Safe -God Bless You and Yours Always In Peace and Grace,
-
Hey all,
Having had a bit more time at home to play with my configs, I figured I'd kick in some observations:
-
The most important thing here is that one should acknowledge that this is definitely a hackjob at present. None of the netgate people are in the slightest responsible if your setup catches fire, nor should they be. But, if you want to play with something that's the "new hotness" before it (hopefully) becomes a kernel addition for BSD and integrated into pfsense some day (sounds like this may be in progress), go for it! Hacking up your home router is a rite of passage for some. Maybe don't do this to your production pfsense box, though.
-
My pfsense box is in a closet and is headless. Having a "missing interface" prompt is not something I would want (having had it happen before). Nobody wants to have to go over with a serial cable or monitor to kick their router over to get internet. Having said that, the trick to fixing this involves renaming your wireguard interface to one of the interfaces that pfsense skips on boot. For example, if you rename your interface to, say, ovpns2 (with ovpns2.conf), it'll skip looking for it on boot and allow you to manually start. Again, very hacky and not intended, but it works.
-
As much as I love the shellcmd utility and recommend it over manual edits, there's a slight issue with when it fires in the boot order. I can't remember as I set it aside a while ago, but I think the issue is that you'll have to make it count to 10 (or more likely 300) before it tries bringing up wireguard as otherwise it hangs when nothing is ready on boot yet. Might be worth trying it with the interface renaming scheme above.
-
Calling a user's contributions "an utter waste of time" is disappointing to see from anyone, let alone a position of authority. Being critical and being dismissive are two different things. Just my .02 as a person.
-
-
@ravenium
Dear ravenium,
My man - I hope that you are well and safe in these days and times. Thanks for your thoughtful and measured contribution and observations regarding the specific issue here and your philosophy about " hacking " pfSense in general. I am the OP ( in case you don't know ) - and you are obviously an erudite thinker - and once again - I for one greatly appreciated your .02 as a person
Later my brother - Peace and God Bless You and Yours Always in God's GracePS - I will try your proposed solution as stated here in # 1 of your reply ( just for sh*t and giggles ) - and thanks for that one more again