pfSense on Hyper-V Home Setup questions.
-
Hi there!
I want to install pfSense on my home lab and I have some questions/. Here are the data :
I have :
- an Asus DSL AC-68U router
- a Hyper-V host (Windows 2012 R2 with 8GB of RAM and two (2) NICs.
- a physical workstation PC
- One Laptop
- Smartphones
- One Tablet
- A Netgear Managable Switch (8 ports)
and I want to be able to use pfSense only as a Firewall for my network.
I have a Windows 2012 R2 VM installed on Hyper-V as a DC for my Active Directory and also, yesterday, I installed pfSense as a VM on Hyper-V (I followed the online manual of Netgear Support pages).
I want my physical workstation but also the wireless clients, to be able to be protected behind the pfSense firewall VM and I have an "understanding" problem of how I'm gonna be able to accomplish that.
Can you please help me understand the network diagram that I will have to design\deploy to make it work?
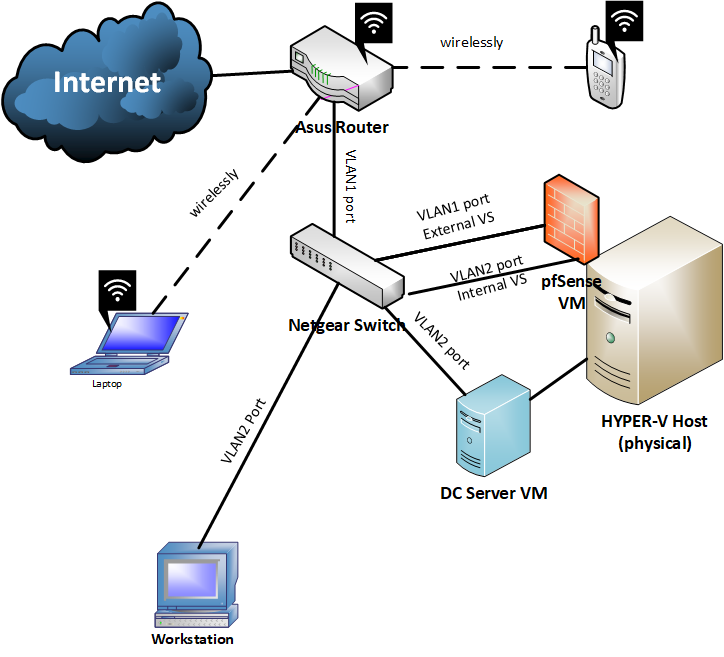
As I am guessing I have to design this kind of network diagram :
But, the wireless clients? How are they gonna passthrough the pfSense first?
As you guessed it, I am a little bit confused. :/
-
disable the wireless on the asus, buy an AP and put it in a vlan
-
@kiokoman There is no other way right?
-
Use your wifi router as just AP and put it behind pfsense.. You can do that with pfsense as VM.. Does your VM host have more than 1 nic?
If not then you would need a vlan switch between your isp modem and the rest of your network..
-
@johnpoz My Asus AC68U is a modem/router. So I use it as my ISP modem and then as a router. I dont know if I can use it as AP only (and not losing the routing operations of this device). I dont have a separate ISP modem. Also, my hyper-v host has 2 nics.
-
Then you have the wrong model number posted, a RT-AC68U is not a gateway device. The ac68u is a very common "router" only device.. Good reason to make sure post exact modem number ;) heheheh
You have a DSL-AC68U?
if your device is a gateway, then no you can not.. You would need to get a different modem or AP.. So you can separate the functionality of your modem and your AP.
Once you can sep the functions - then yeah its very easy to put everything behind pfsense - even your wifi... What I would suggest is get a real AP, vs modem and using your current device as just AP... Say a unifi AP that supports vlans - this will allow you to create multiple segments for wifi, as long as you have a vlan capable switch - which I assume you do since you call out vlans in your drawing - what is the exact model of this netgear?
-
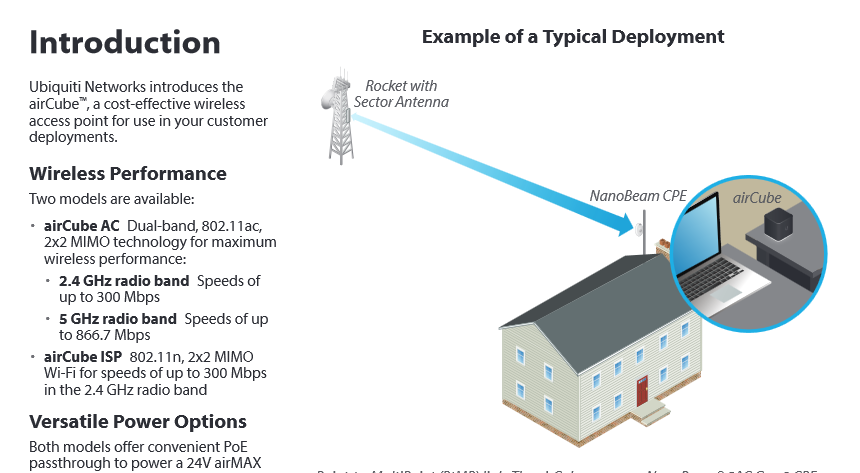
@johnpoz oh man! sorry. :) Yes, I have a DSL-AC68U. My netgear switch is a GS108T. So I think I might keep Asus as a modem and the buy a Unifi AP (Im watching videos right now, for the AirCube ACB-AC) and separate my wifi and put it behind pfSense right?
-
yup, exactly as i said, it 's the best solution, this way you can place the access point in a better position
-
@uxm said in pfSense on Hyper-V Home Setup questions.:
AirCube ACB-AC
No that is not what you would want... That is airmax... If you want something you just set on a table or something you prob want the https://store.ui.com/collections/wireless/products/unifi-flexhd
Why can you not just get a normal AP that is mounted?
This is more what you would setup in a home as your AP
https://www.ui.com/unifi/unifi-ac/ -
@uxm said in pfSense on Hyper-V Home Setup questions.:
AirCube ACB-AC
did pay attention to this, yeah, listen to johnpoz
-
Yeah not sure what video's he is watching... But that is not wifi AP you would use in a home setup..
-
@johnpoz sorry I didnt know that Aircube is for costumers deoloyment. I think I will go for the Unifi AP-AC as you said.
Can I ask one more question? Should the virtual switches on my pfSense be internal and external? How will I be able to manage it? From the host itself or a VM? I thing my physical workstation will not be able to access it, right?
-
You would manage esxi host via the vmkern, which would be on your lan network..
-
@johnpoz I dont have VMware esxi installed
-
Sorry hyper-V just admin it from the lan side
-
@johnpoz that was my question/statement. That I cant admin it from lan side by a physical pc if the pfsense vm connects to an internal (hyperv) virtual switch. :(
-
You do understand pfsense can have multiple lan side interfaces right, and VM switches can be tied to physical network a well.. Maybe your issue is you don't actually get how VM Hosts work?
Your drawing is tied to both physical and virtual networks - so not sure why your confused?
-
I know how Hyper-V works..The actual reason that I am confused, is that I can't ping pfsense from my physical PC nor I can admin it.
Physical PC : 192.168.2.108
Pfsense Internal side : 192.168.2.10both on the same LAN/VLAN.
-
Well then you have something setup wrong. Or not connected how you think its connected, etc.
-
@johnpoz Yeah I guess so. I will try to find the reason. There is no reason to bother you with that kind of questions but I will come back if I cant make it work.
Thank you ALL for your precious help! This community seems to be totally ALIVE!