Port Forward in Active CP
-
Dear All,
I have an active CP and I want to allow only a port for specific IP. the only option I found that I allowed I can bypass an IP or hostname.
The problem that I made a port forward to the Remote Desktop to a PC in my LAN network but I can't access it because of CP is active.
PLease Advise! -
@mohkhalifa said in Port Forward in Active CP:
I have an active CP and I want to allow only a port for specific IP. the only option I found that I allowed I can bypass an IP or hostname.
Specific IP like a specific site (on the Internet ?) ?
Make a first pass rule on your Captive portal firewall tab that allows this port and IP.
The second rule will be a block all rule.
Done.But I guess that's not what you're asking so the question isn't clear at all.
@mohkhalifa said in Port Forward in Active CP:
The problem that I made a port forward to the Remote Desktop to a PC in my LAN network but I can't access it because of CP is active.
That's messy.
A captive portal should be on a dedicated network / dedicated NIC - on which you accept the "non trusted" devices - and probably some AP's if you want also Wifi facilities.
Not your own desktops and servers.
These should be on some other, trusted LAN.
Of course, you can activate your captive on the LAN interface, but that's messy and hard to administer. As you figured out.Example :
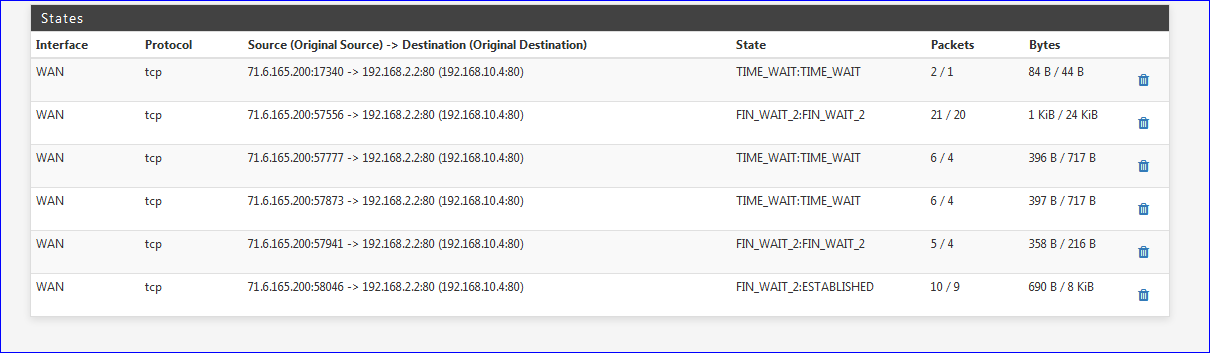
I have a captive portal on an interface 192.168.2.1/24 with some AP's on 192.168.2.2 - 192.192.168.2.3 etc.These Ap's have a GUI web interface - they always have such an interface. I can access their web interface s when I NAT to this (a ) device :

I'll keep this NAT rule open for a day or so :
http://br---------------.fr:80 (edit : removed the URL - see below)You'll be seeing the web interface of one of my AP's ( 192168.2.2) on my captive portal's network.
This access is not initiated from the captive portal so all captive portal 'ipfw' rules and captive portal GUI rules are complely bypassed here.
-
This was you ?
Yeeh, I opened up a device with a NAT on one of my LAN's and posted the URL (see above).
Had dozens of hits (different IP's) in less then an hour

-
@Gertjan this IP belongs to shodan.
-
Who's that ?
-
@Gertjan shodan.io is a service that scans the internet for known exposure and for vulnerabilities
i remember you are french, so I link you here a video in French on the subject https://youtu.be/SxjmOFBtsvk