W10 / Ikev2 + radius on PFSENSE
-
Hello everyone !
I've set up a IkeV2 vpn with my windows 10 clients. The server is pfsense with local user database.
I followed this tutorial : https://docs.netgate.com/pfsense/en/latest/vpn/ipsec/configuring-an-ipsec-remote-access-mobile-vpn-using-ikev2-with-eap-mschapv2.html--> My clients connect correctly. (no cert issue, split tunneling ok, vpn to local lan ok, … )
I've then set up a FreeRadius server with google auth on pfsense.
--> I can, with success, auth with the Authentification diagnostic page (pfsense), so my radius server is ok.Now i try to switch from local database to my working radius, with those instructions : https://docs.netgate.com/pfsense/en/latest/vpn/ipsec/ikev2-with-eap-radius.html (following Ikev2-->radius) .
When i connect my client on windows 10, with a working combination of user / PIN + google pass, i have :
- a message on windows 10 rejecting the connection : unable to connect to XXX
- the following message on pfsense System Log : (2) Login incorrect (Failed retrieving values required to evaluate condition): [FirstName.Name/<via Auth-Type = eap>] (from client XXX port 4 cli XXXXX[4500]) FirstName.Name -
Additionnaly in ipsec log :
Dec 6 17:03:59 charon 07[IKE] <con-mobile|5> RADIUS authentication of 'FirstName.Name' failed
Dec 6 17:03:59 charon 07[IKE] <con-mobile|5> EAP method EAP_MSCHAPV2 failed for peer XXXXX
Dec 6 17:03:59 charon 07[ENC] <con-mobile|5> generating IKE_AUTH response 4 [ EAP/FAIL ]Do someone have a similar issue, or an idea where to look ?
Really appreciate your help, thanks !
-
@aniodon said in W10 / Ikev2 + radius on PFSENSE:
AP method EAP_MSCHAPV2 failed for peer XXXXX
Hello
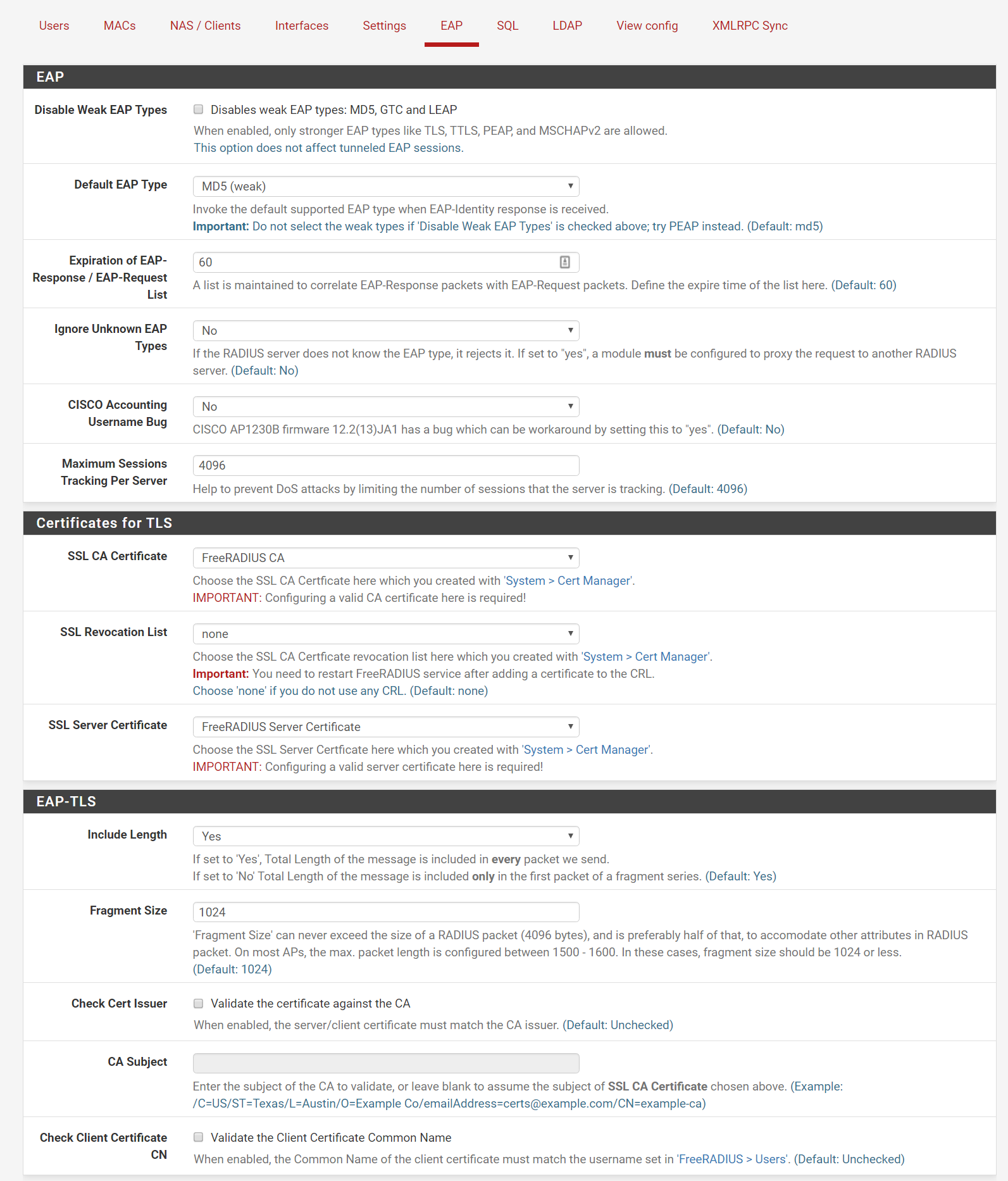
Show EAP settings for radius server . -
For information, after digging, it seems related to the password encryption of the user.
i created a user WITHOUT google auth, just login / pass. Then, in General Configuration of the user :
- password in clear text : No issue, i can connect !!!!
- MD5 encryption : Cannot connect (cf above issue)
-
@aniodon
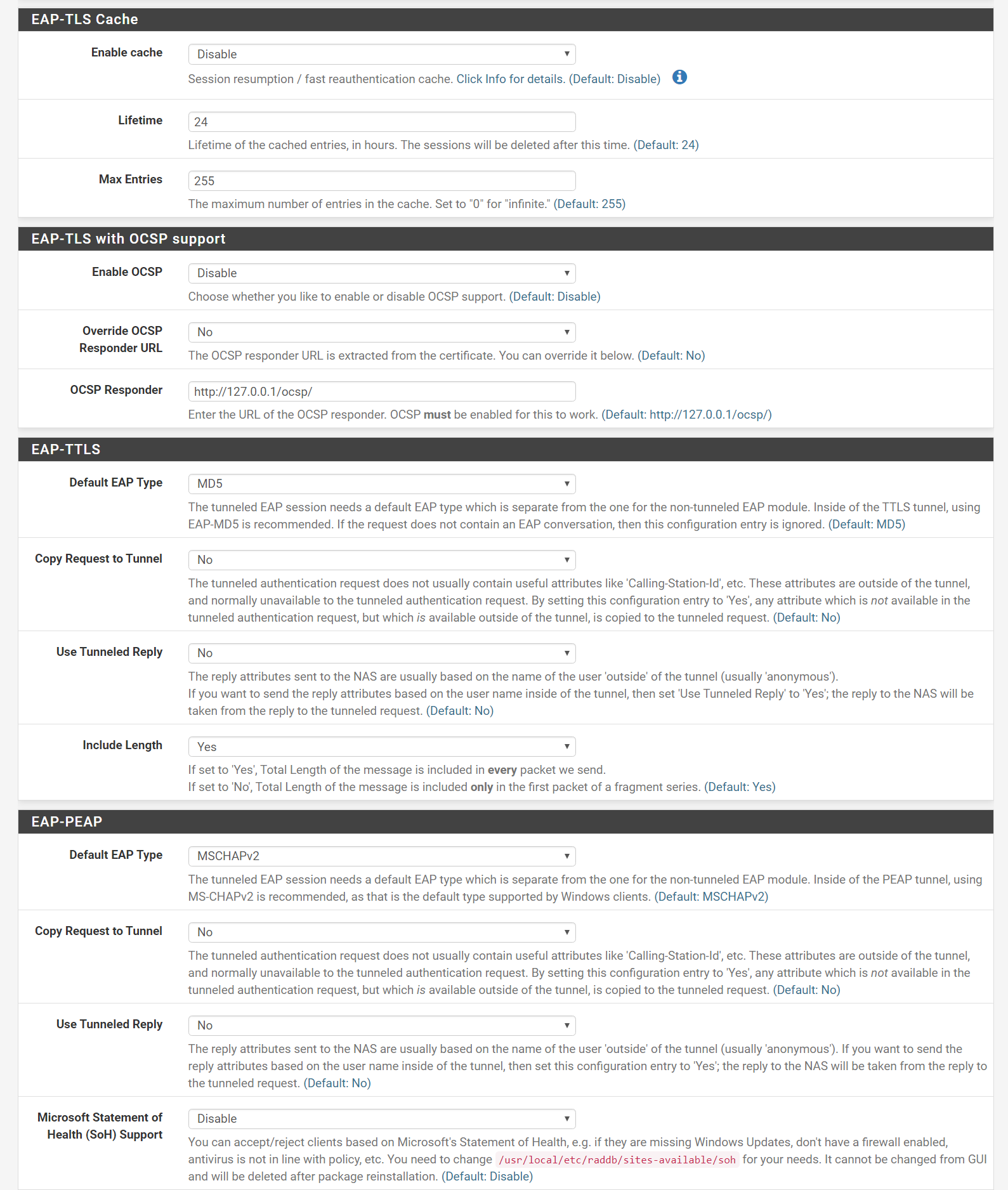
Try to change
Default EAP Type to
-
Thanks @Konstanti ,
This does not resolve the issue.
here are my test :
- User with Clear password, without google : OK
- User with MD5 password, without google : KO
- User with Clear password, with google : KO
- User with MD5 password, with google : KO
-
and make sure that the IPSEC client and freeradius use certificates signed by the same CA.
-
thanks,
they were indeed different. I corrected the CA and certificate in radius and restarted IPSEC.
i still get (1) Login incorrect (Failed retrieving values required to evaluate condition) , when i am not in a "No password encryption/no google" setup.
-
-
You need to stop the Freeradius service
/Status/services/ -
From the PF console run freeradius in debug mode
radiusd -X
Then you try to establish a connection and analyze the errors
-
-
Sorry for the delay, took me a while to connect, get logs and sanitize
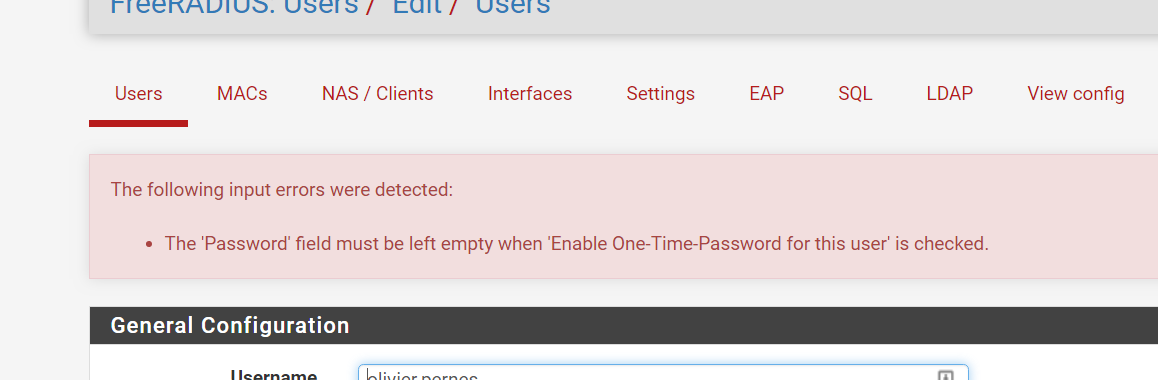
(0) Received Access-Request Id 63 from XXX:4608 to XXX:1812 length 167 (0) User-Name = "XXX" (0) NAS-Port-Type = Virtual (0) Service-Type = Framed-User (0) NAS-Port = 20 (0) NAS-Port-Id = "con-mobile" (0) NAS-IP-Address = XXX (0) Called-Station-Id = "XXX[4500]" (0) Calling-Station-Id = "XXX[4500]" (0) EAP-Message = 0x02000013016f6c69766965722e7065726e6573 (0) NAS-Identifier = "strongSwan" (0) Message-Authenticator = 0xf18266cb0a8226f4f224c8f18eb6cb9e (0) # Executing section authorize from file /usr/local/etc/raddb/sites-enabled/default (0) authorize { (0) [preprocess] = ok (0) [chap] = noop (0) [mschap] = noop (0) [digest] = noop (0) suffix: Checking for suffix after "@" (0) suffix: No '@' in User-Name = "XXX", skipping NULL due to config. (0) [suffix] = noop (0) ntdomain: Checking for prefix before "\" (0) ntdomain: No '\' in User-Name = "XXX", skipping NULL due to config. (0) [ntdomain] = noop (0) eap: Peer sent EAP Response (code 2) ID 0 length 19 (0) eap: EAP-Identity reply, returning 'ok' so we can short-circuit the rest of authorize (0) [eap] = ok (0) } # authorize = ok (0) Found Auth-Type = eap (0) # Executing group from file /usr/local/etc/raddb/sites-enabled/default (0) authenticate { (0) eap: Peer sent packet with method EAP Identity (1) (0) eap: Calling submodule eap_mschapv2 to process data (0) eap_mschapv2: Issuing Challenge (0) eap: Sending EAP Request (code 1) ID 1 length 43 (0) eap: EAP session adding &reply:State = 0xdfebf9ccdfeae3f1 (0) [eap] = handled (0) } # authenticate = handled (0) Using Post-Auth-Type Challenge (0) # Executing group from file /usr/local/etc/raddb/sites-enabled/default (0) Challenge { ... } # empty sub-section is ignored (0) Sent Access-Challenge Id 63 from XXX:1812 to XXXX:4608 length 0 (0) EAP-Message = 0x0101002b1a0101002610f38b08acd1311eefcb492fa37fff3cd8667265657261646975732d332e302e3137 (0) Message-Authenticator = 0x00000000000000000000000000000000 (0) State = 0xdfebf9ccdfeae3f19eb8b5707e5d7a79 (0) Finished request Waking up in 4.9 seconds. (1) Received Access-Request Id 64 from XXX:4608 to XXX:1812 length 239 (1) User-Name = "XXX" (1) NAS-Port-Type = Virtual (1) Service-Type = Framed-User (1) NAS-Port = 20 (1) NAS-Port-Id = "con-mobile" (1) NAS-IP-Address = XXX (1) Called-Station-Id = "XXX4500]" (1) Calling-Station-Id = "XXX[4500]" (1) EAP-Message = 0x020100491a02010044318d9f92f4ffafcd3cfea6f97ccd098ddc000000000000000008b552fb470b098eea40b7be084f902e5d471f37d0a1dcc0006f6c69766965722e7065726e6573 (1) NAS-Identifier = "strongSwan" (1) State = 0xdfebf9ccdfeae3f19eb8b5707e5d7a79 (1) Message-Authenticator = 0x5e084f4a691fe612767c92001f1015e8 (1) session-state: No cached attributes (1) # Executing section authorize from file /usr/local/etc/raddb/sites-enabled/default (1) authorize { (1) [preprocess] = ok (1) [chap] = noop (1) [mschap] = noop (1) [digest] = noop (1) suffix: Checking for suffix after "@" (1) suffix: No '@' in User-Name = "XXX", skipping NULL due to config. (1) [suffix] = noop (1) ntdomain: Checking for prefix before "\" (1) ntdomain: No '\' in User-Name = "XXX", skipping NULL due to config. (1) [ntdomain] = noop (1) eap: Peer sent EAP Response (code 2) ID 1 length 73 (1) eap: No EAP Start, assuming it's an on-going EAP conversation (1) [eap] = updated (1) files: users: Matched entry XXX at line 2 (1) [files] = ok rlm_counter: Entering module authorize code rlm_counter: Could not find Check item value pair (1) [daily] = noop rlm_counter: Entering module authorize code rlm_counter: Could not find Check item value pair (1) [weekly] = noop rlm_counter: Entering module authorize code rlm_counter: Could not find Check item value pair (1) [monthly] = noop rlm_counter: Entering module authorize code rlm_counter: Could not find Check item value pair (1) [forever] = noop (1) if (&request:Calling-Station-Id == &control:Calling-Station-Id) { (1) ERROR: Failed retrieving values required to evaluate condition (1) [expiration] = noop (1) [logintime] = noop (1) pap: WARNING: No "known good" password found for the user. Not setting Auth-Type (1) pap: WARNING: Authentication will fail unless a "known good" password is available (1) [pap] = noop (1) } # authorize = updated (1) Found Auth-Type = eap (1) # Executing group from file /usr/local/etc/raddb/sites-enabled/default (1) authenticate { (1) eap: Expiring EAP session with state 0xdfebf9ccdfeae3f1 (1) eap: Finished EAP session with state 0xdfebf9ccdfeae3f1 (1) eap: Previous EAP request found for state 0xdfebf9ccdfeae3f1, released from the list (1) eap: Peer sent packet with method EAP MSCHAPv2 (26) (1) eap: Calling submodule eap_mschapv2 to process data (1) eap_mschapv2: # Executing group from file /usr/local/etc/raddb/sites-enabled/default (1) eap_mschapv2: authenticate { (1) mschap: WARNING: No Cleartext-Password configured. Cannot create NT-Password (1) mschap: WARNING: No Cleartext-Password configured. Cannot create LM-Password (1) mschap: Creating challenge hash with username: XXX (1) mschap: Client is using MS-CHAPv2 (1) mschap: ERROR: FAILED: No NT/LM-Password. Cannot perform authentication (1) mschap: ERROR: MS-CHAP2-Response is incorrect (1) [mschap] = reject (1) } # authenticate = reject (1) eap: Sending EAP Failure (code 4) ID 1 length 4 (1) eap: Freeing handler (1) [eap] = reject (1) } # authenticate = reject (1) Failed to authenticate the user (1) Using Post-Auth-Type Reject (1) # Executing group from file /usr/local/etc/raddb/sites-enabled/default (1) Post-Auth-Type REJECT { (1) attr_filter.access_reject: EXPAND %{User-Name} (1) attr_filter.access_reject: --> XXX (1) attr_filter.access_reject: Matched entry DEFAULT at line 11 (1) [attr_filter.access_reject] = updated (1) [eap] = noop (1) policy remove_reply_message_if_eap { (1) if (&reply:EAP-Message && &reply:Reply-Message) { (1) if (&reply:EAP-Message && &reply:Reply-Message) -> FALSE (1) else { (1) [noop] = noop (1) } # else = noop (1) } # policy remove_reply_message_if_eap = noop (1) } # Post-Auth-Type REJECT = updated (1) EXPAND %{User-Name} - %{reply:Acct-Output-Octets} (1) --> XXX - (1) Login incorrect (Failed retrieving values required to evaluate condition): [XXX/<via Auth-Type = eap>] (from client Frigo port 20 cli XXX[4500]) XXX - (1) Delaying response for 1.000000 seconds Waking up in 0.3 seconds. Waking up in 0.6 seconds. (1) Sending delayed response (1) Sent Access-Reject Id 64 from XXX:1812 to XXX:4608 length 127 (1) MS-CHAP-Error = "\001E=691 R=1 C=bf32f65eb19092390d7f03336fad171a V=3 M=Authentication rejected" (1) EAP-Message = 0x04010004 (1) Message-Authenticator = 0x00000000000000000000000000000000 Waking up in 3.9 seconds. (0) Cleaning up request packet ID 63 with timestamp +35 (1) Cleaning up request packet ID 64 with timestamp +35 Ready to process requests -
(1) eap_mschapv2: # Executing group from file /usr/local/etc/raddb/sites-enabled/default (1) eap_mschapv2: authenticate { (1) mschap: WARNING: No Cleartext-Password configured. Cannot create NT-Password (1) mschap: WARNING: No Cleartext-Password configured. Cannot create LM-Password (1) mschap: Creating challenge hash with username: XXX (1) mschap: Client is using MS-CHAPv2 (1) mschap: ERROR: FAILED: No NT/LM-Password. Cannot perform authentication (1) mschap: ERROR: MS-CHAP2-Response is incorrect (1) [mschap] = reject (1) } # authenticate = reject -
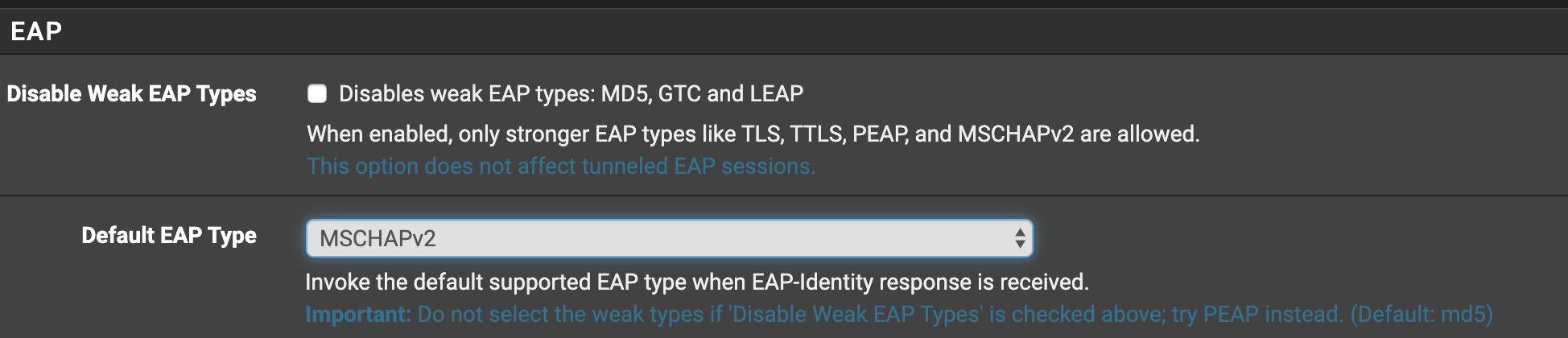
Thank you @Konstanti, but, you cannot set password when in google mode :
-
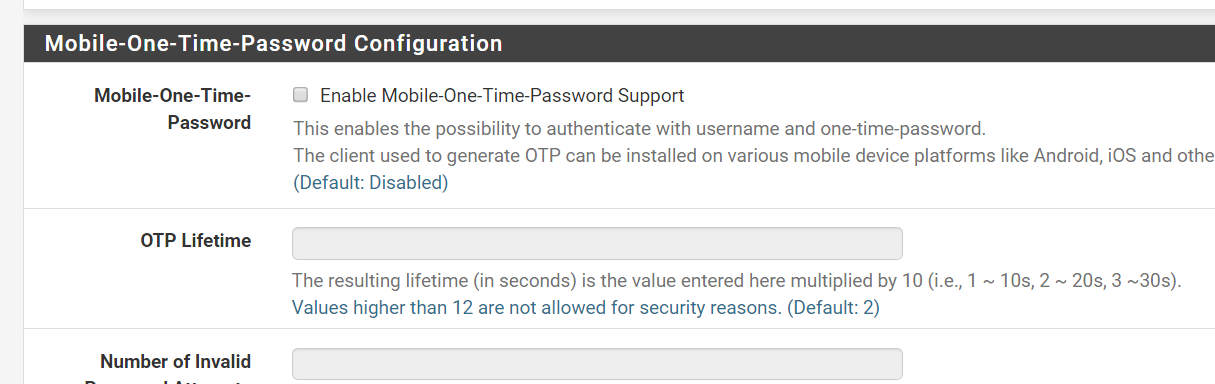
Miscellaneous configuration and hints:
The configuration for different mobile devices can be found here.
And here is the software for mobile devices.
Please read the limitations to make sure how secure this is.
mOTP will probably not work with EAP, CHAP, MSCHAP. If it does - tell me how :-)
-
@Konstanti : The quote is from the mOTP section. Are mOTP and the One-time-Password from users pannel the same ?
mOTP is disabled in my confDo you know if i have an alternative ?
i would not like to use credentials in clear text and i would like to use more elaborate ways of authenticatethank you
-
Hi @aniodon
Did you ever get this working? I am trying to achieve something similar and have run into the same problem.
-
@nippertje hello, sorry but no. I concluded this was not possible and Just gave up.
-
You can't use that kind of OTP with EAP because using mOTP/GA requires PAP which is unencrypted, while EAP will refuse to work with anything less than complete end-to-end encryption of the credentials.
You would need some other sort of MFA hooked into radius, likely from an external/third party radius server.
-
Thanks @jimp - I found that out with additional reading, so changed tack and now am using OpenVPN with ESET Secure Authentication, which works well and provides convenient push authentication.