pfSense and meraki z3
-
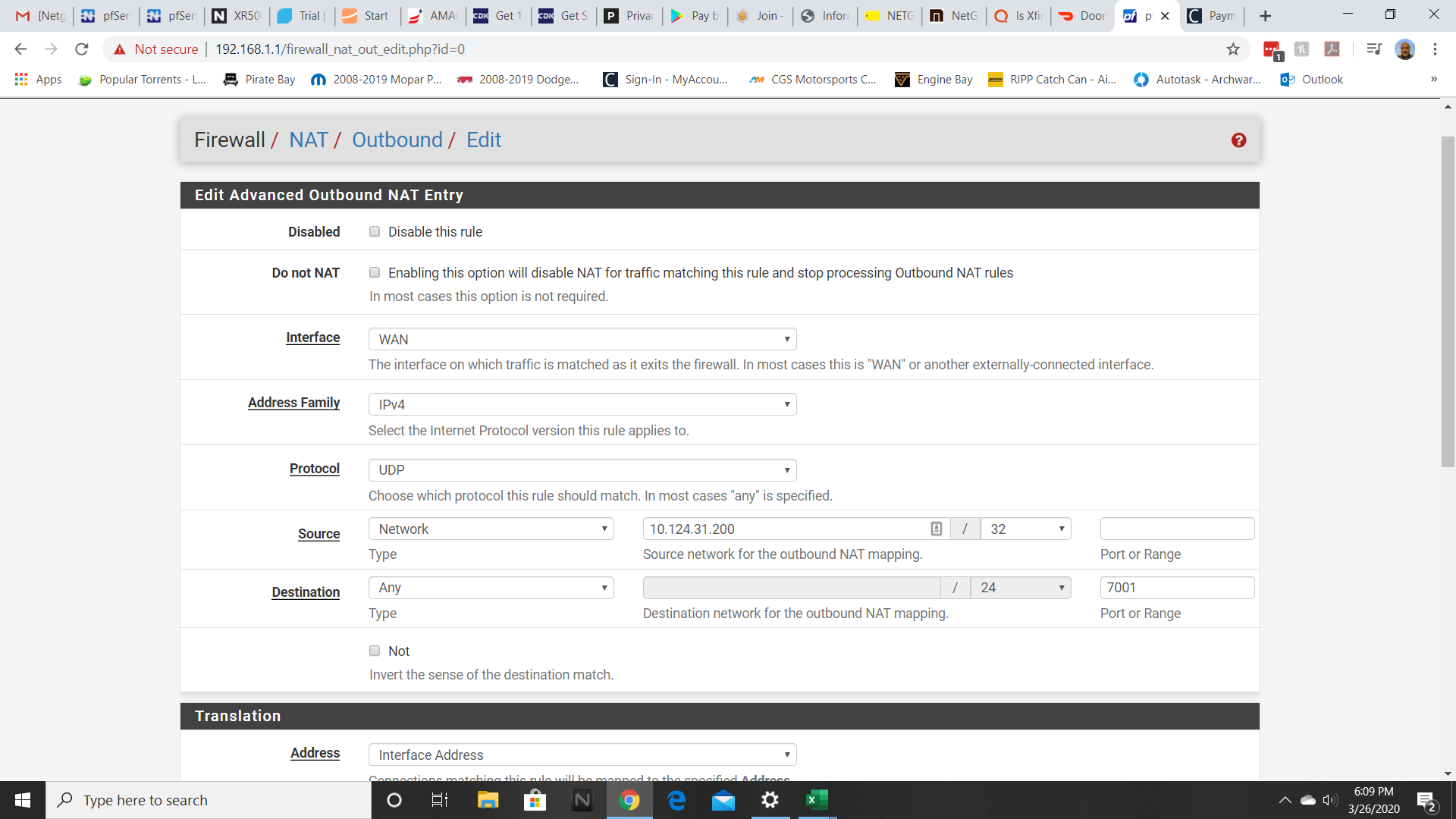
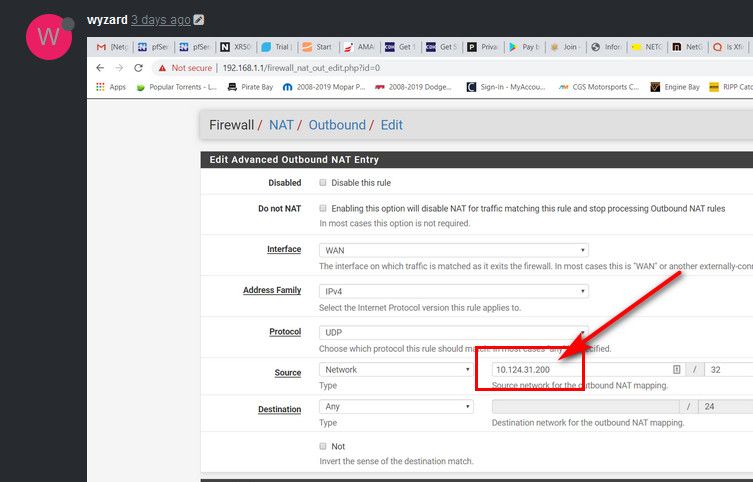
Both rules for 9350 and 7001 ports are the same.
Also, I'm 95% sure that is the ip address of the device.
Appreciate all the help.
-
That looks correct assuming that is the Z3 address.
Check Status > DHCP leases to be sure.You could just set the source as 10.124.31.0/24 to sure it's included. Assuming your internal subnet is a /24 that is.
We are also assuming they are using ports 7001 and 9350. Check the state table for states from 10.123.31.200 to be sure it is.
Steve
-
@stephenw10 said in pfSense and meraki z3:
...We are also assuming they are using ports 7001 and 9350. Check the state table for states from 10.123.31.200 to be sure it is.
@wyzard For reference, here's a sanitized version of what I'm seeing in my state table when filtered for WAN and ports 9350 and 7001. I see a couple of lines for both ports with different destination IP addresses. You can see that the source port is the same for the Z3 and WAN IPs. Before the NAT mapping was in place, those source ports were different.
2x
WAN udp WAN_IP:43830 (Z3_IP:43830) -> MERAKI_DEST_IP:9350
2x
WAN udp WAN_IP:43830 (Z3_IP:43830) -> BUSINESS_DEST_IP:7001 -
Ok, that looks correct. In terms of the ports at least. I would expect that to work as long as the Z3 is actually configured correctly. I assume it is not though?
Can you get any sort of connection status or logs from anywhere?
Steve
-
Still no luck. Verified the static IP of the Meraki. Also verified the ports. When I watch the activity it indicates that it's attempting to authenticate, the authentication failed. Still at a loss.
Again, I appreciate all the help.
-
So you actually validated this thing works when not behind your pfsense..
Authentication failed could just mean it can't auth with the creds its using.. Are these something you or your wifi put into some gui.. Is it suppose to be you plug it in sort of solution from work and anything behind it is on the vpn?
but before you actually blame whatever the problem is on something pfsense is or isn't doing - state port mapping for example.. Have you actually validated it works when you take pfsense out of the picture?
-
@johnpoz said in pfSense and meraki z3:
So you actually validated this thing works when not behind your pfsense..
Authentication failed could just mean it can't auth with the creds its using.. Are these something you or your wifi put into some gui.. Is it suppose to be you plug it in sort of solution from work and anything behind it is on the vpn?
but before you actually blame whatever the problem is on something pfsense is or isn't doing - state port mapping for example.. Have you actually validated it works when you take pfsense out of the picture?
Hi John. Thanks for the response.
Yes, I have taken pfSense out of the picture and it does authenticate and work.
It was provided to us from my wife's work and is suppose to be a plug it in sort of solution.
I'm almost positive it's something that I just don't have right in pfSense.
Thanks.
-
Well why don't you sniff on pfsense when you connect the thing to see what its trying to do.. Are you using IPS, or pfblocker that could be blocking stuff your not aware of?
Pfsense out of the box doesn't block anything.. So unless its something odd like its looking for a static port on your outbound nat or something... Which is odd for what say a soho wifi router would be doing..
Your not behind a double nat are you - pfsense gets a public IP on its wan?
-
Yes, it does get a public IP on its WAN.
Could the block private networks (RFC 1918 Networks) WAN firewall rule be preventing this from working?
The funny thing is that her work can "see" the box. But when it tries to get out to authenticate it can't. Not using IPS or pfblocker.
I pretty much left pfSense "stock", just added a rule to let plex outside my network.
-
'block private networks' on WAN will make no difference here.
Try looking at all the open states from the Z3 IP address. It might be trying some other port(s) as well.
Steve
-
This is extremely frustrating. Nothing that I've tried is letting me connect out using the Meraki.
I see nothing in open states about the Z3 IP address (although I will admit I am an extreme novice when it comes to pfSense).
Let's wipe the slate clean and if everyone that has helped so far (and again, thank you all so much for the assistance) can start from step one and what I would need to do (where to put rules, what they need to be, etc. etc.) I'll give this one more college try before throwing in the towel.
Again, thanks to everyone for their help
-
You shouldn't have to put any rules anywhere.. This should work out of the box!
So this box gets its "wan" IP from pfsense dhcp, connected to your pfsense lan... Then you put a box behind that..
Sniff on your pfsense lan for this IP of the Z3 IP, its gets... What do you see it doing.. Or just look in the state table of pfsense.. If your not seeing traffic and states - then its not doing anything!!! So no shit it wouldn't work...
-
Ok, so then why is it working when it's not behind the pfsense box? That is what is confusing.
As I said, I'm a novice when it comes to pfsense, so how do I "sniff" on my pfsense lan?
Thanks.
-
Via the diagnostic menu packet capture..
If your not seeing any states then pfsense didn't see any traffic that were allowed.. Which would make no sense unless whatever it was doing was blocked.. Which would make no sense because your default rules on lan are any any.. Unless you picked to block bogon or something and its trying to go to a bogon IP.. Which should be in the firewall log as blocked, etc. Unless you turned off logging of that..
Out of the box this should work - your going to have to get some info if you want to try and figure out why its not.. For all we know it never got an IP on its wan?? If your not seeing any states that would make sense, etc. etc.
Information is key to figuring out why its not working...
Here is a quick question... What network is your pfsense lan 192.168.X and what is the network this box uses for its lan? It has to be something other than 192.168.x - or yeah your going to have nothing but issues... It needs to be 192.168.Y for example - something different than what pfsense is using for its lan. Then can not overlap or your going to have a bad day - see your trying to do 10.124 for your outbound - are you using 10/8 for your lan? and its also using some 10.x network on its lan?
-
Hi John. Really appreciate your help.
My pfsense LAN is set to 192.168.x.x The box is set to something different then that. I do have bogon blocked on WAN but not on LAN.
Are you also saying that an outbound firewall NAT rule(s) should NOT be needed?
I keep working on it based on your input, so hopefully at some point.
-
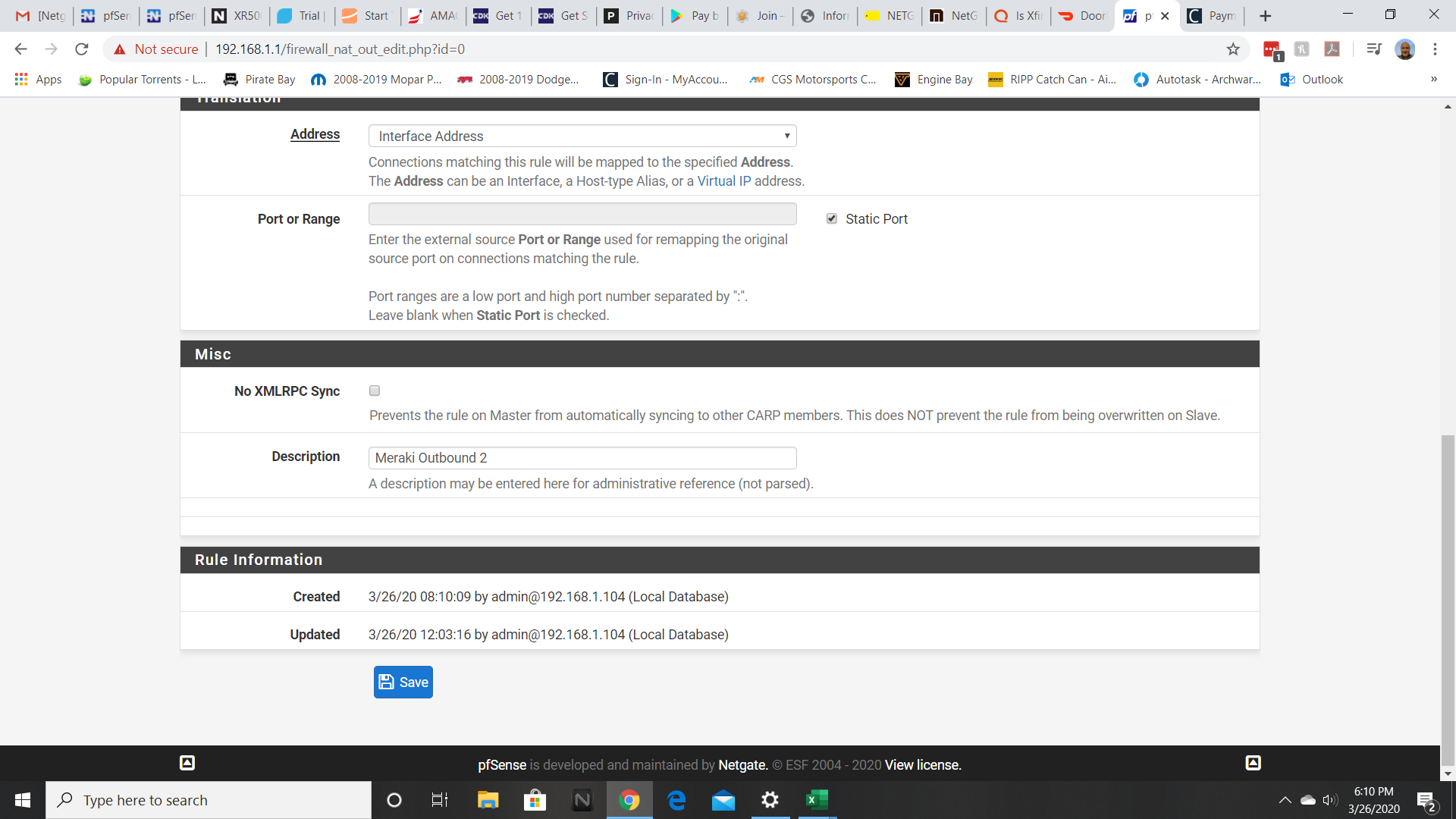
The reason it works behind some other firewall is that most SOHO style so not randomise the source port for NAT'd connections. pfSense does that to increase security and to prevent multiple outbound states all using the same port which could conflict. For some reason the remote Meraki device is unable to cope with more than one source port.

https://docs.netgate.com/pfsense/en/latest/nat/static-port.htmlIf you don't know what ports it needs then you can just set and outbound NAT rule with static source ports for all connections from the Z3 IP. At least as a test.
Steve
-
@stephenw10 said in pfSense and meraki z3:
NAT rule with static source ports for all connections from the Z3 IP. At least as a test.
Great test for sure!
But doesn't matter if the random ports on nat were were the problem or not - he still should see states or traffic.. Where you could see what it was doing from a sniff..
That they would setup some sort of vpn solution that required static port natting seems pretty unthoughtful on where this might or could get deployed.
But yeah just setting all outbound natting to static would be a simple test if you can not see which ports its actually using via states or a sniff..
My pfsense LAN is set to 192.168.x.x The box is set to something different then that
Than what was that 10.124 nonsense for an outbound nat? That would of never done anything. Where did you get the 10.124 address from?
-
It seemed to me that the 10.124.x.x was the static IP of the Meraki.
So here's what I know:
- The IT department at my wife's work can "see" the Meraki when it is behind the pfsense. For some reason the Meraki can't get "back" to them.
- The PC that is connected to the Meraki is not getting an IP address.
- The PC indicates "attempting to authenticate"
- It then says "authentication failed".
From what I can see in the logs on pfsense (states and packet capture) nothing seems out of the ordinary.
I agree with everyone that this should not be that hard. I my mind should be a simple plug and play. Really not sure what is going on?
About to call it a TKO
-
@wyzard said in pfSense and meraki z3:
I agree with everyone that this should not be that hard. I my mind should be a simple plug and play.
As I mentioned, this appears to be a device intended to replace a consumer router/firewall, not be used behind it. That it works without pfSense shows this. Another thing you could try is put a consumer grade router/firewall ahead of it. If that works, then some investigation may reveal what the problem is.
-
@wyzard said in pfSense and meraki z3:
It seemed to me that the 10.124.x.x was the static IP of the Meraki.
Where did you get that from? It wouldn't be able to do anything if that was its IP of its wan, and if that is is lan IP, your outbound nat wouldn't do shit..
The IT department at my wife's work can "see" the Meraki when it is behind the pfsense. For some reason the Meraki can't get "back" to them.
If they can see it, then it CAN get back to them..
The PC that is connected to the Meraki is not getting an IP address.
Then how would it be saying its attempting to authenticate...
Answer some basic questions.. from pfsense does it hand out an IP address to this device? If so what is it?
When you connect a PC to the lan side of it.. lets see the IPconfig /all from this device...