StrongSwan user authentication failed on Android
-
do you have set dns sec on your android?
-
No, but to wich server?
-
okay, did you set the user identity under advance settings on the strongswan app?
-
@Alitai
Yes its the same username. -
okay, on the android part there is not much more to todo.
Normally this is the easy part.Now, I think it's time for pictures from your pfsense and android. but don't forget to deleted the sensitive Infos.
-
@Alitai
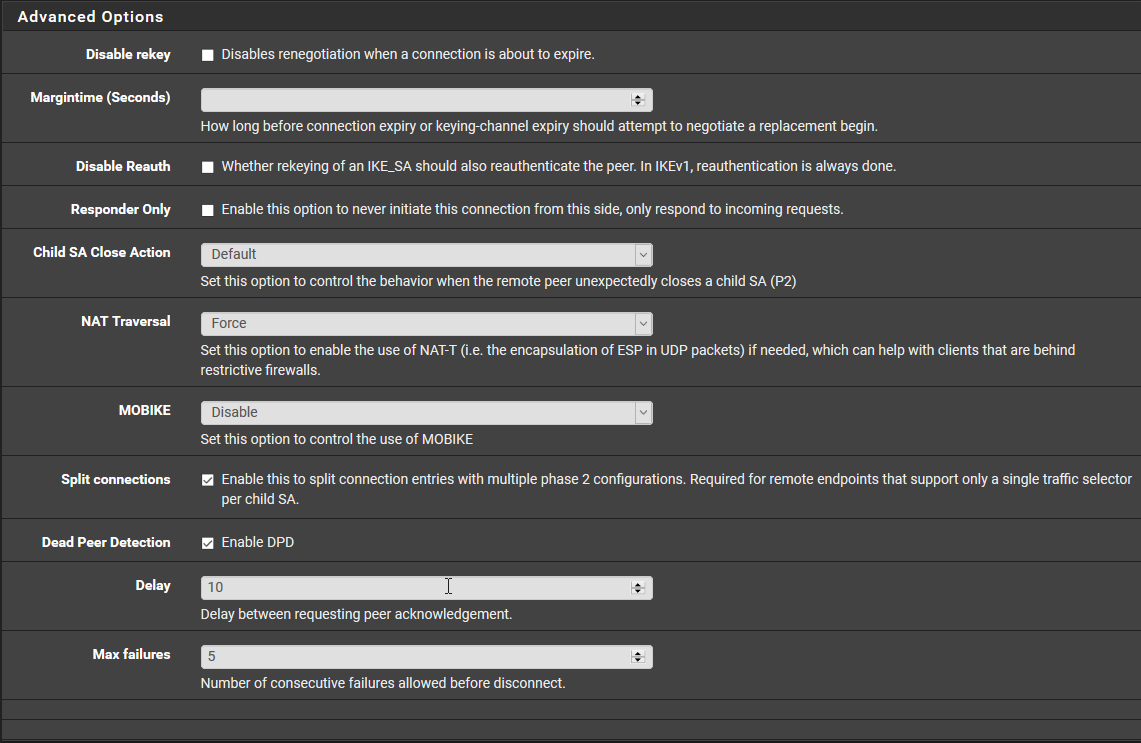
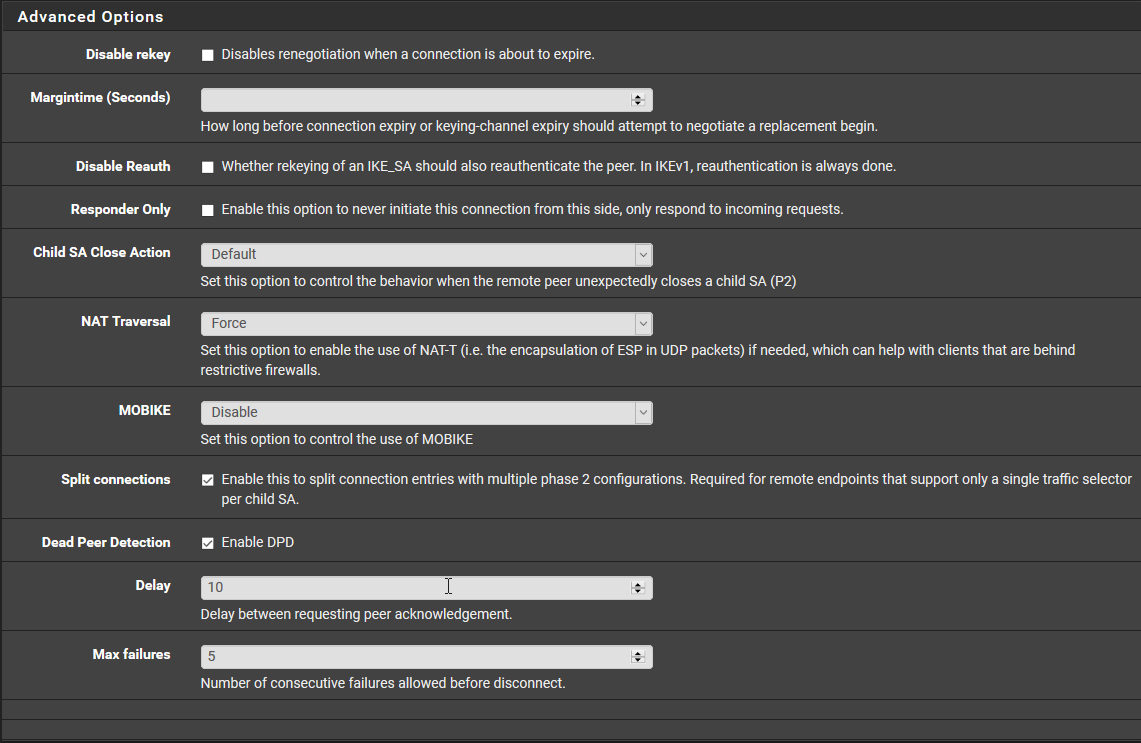
This the P1 on pfSense.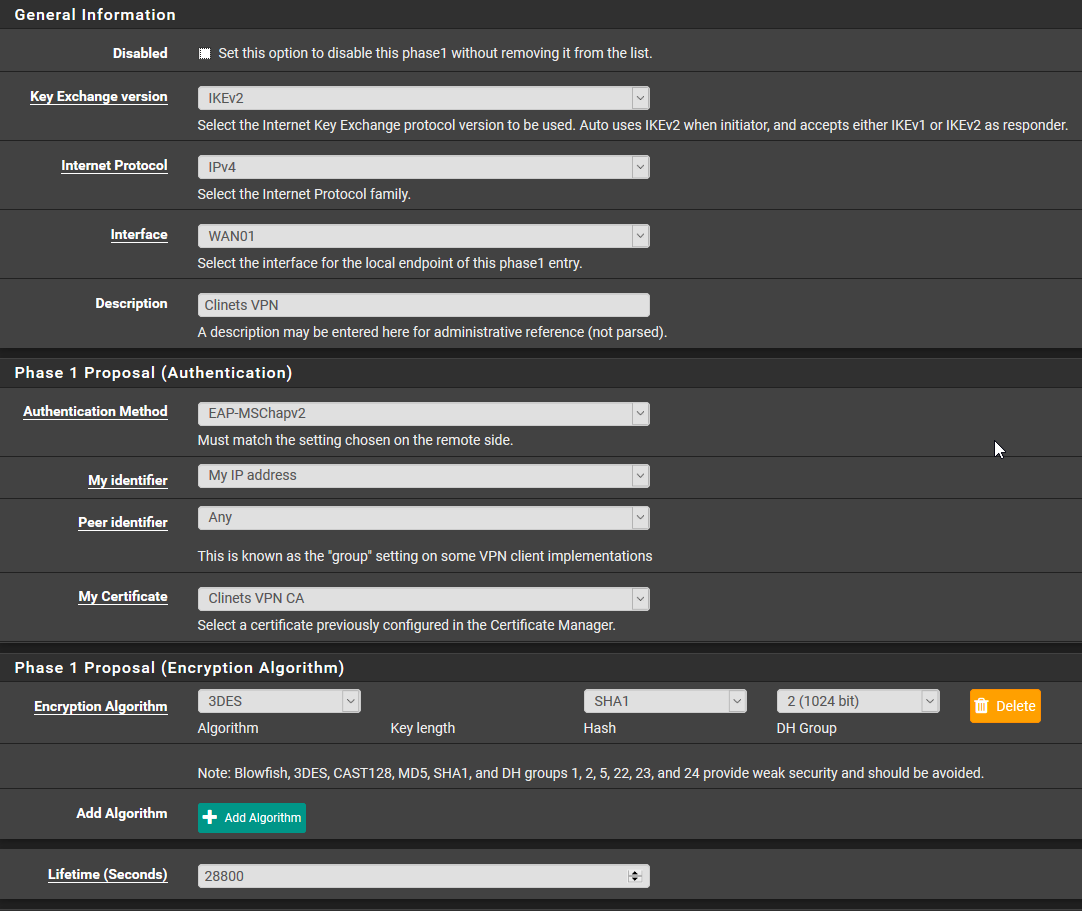
This Mobile Client
For the Pre-Shared Keys the secret type is EAP.
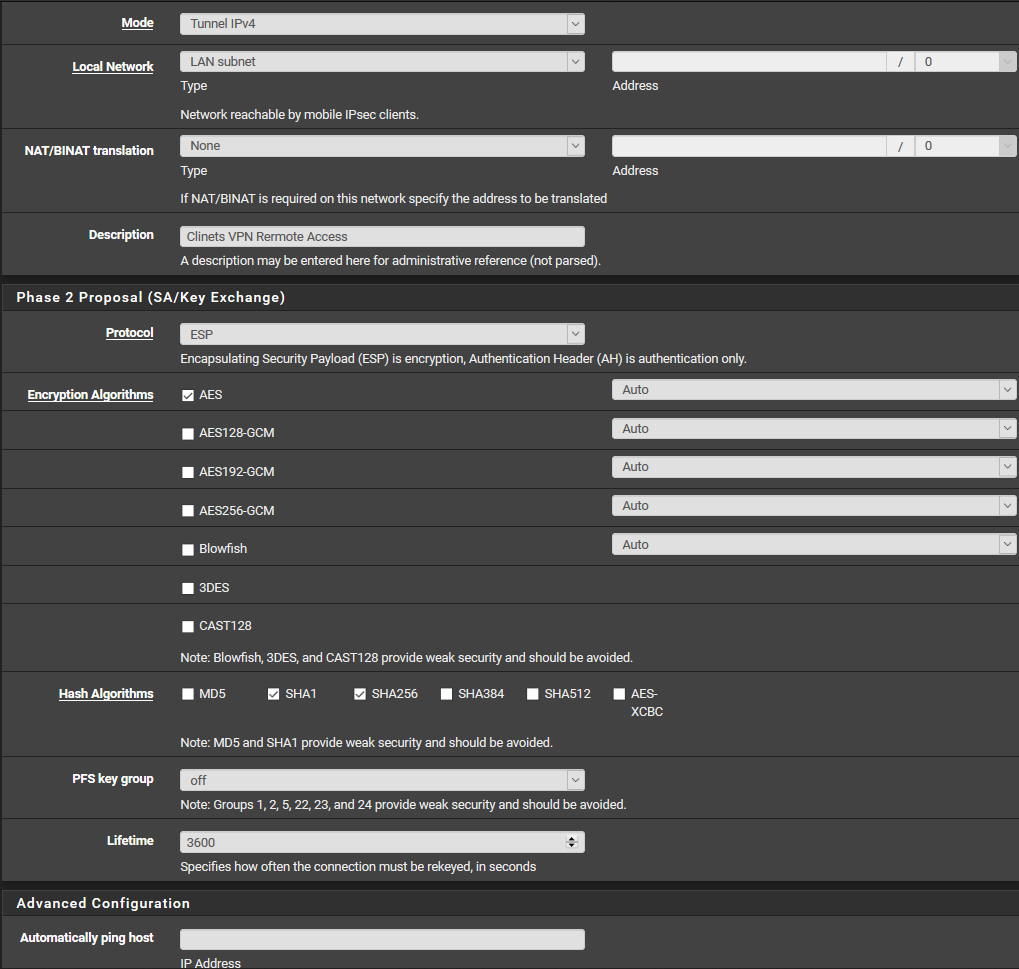
This P2
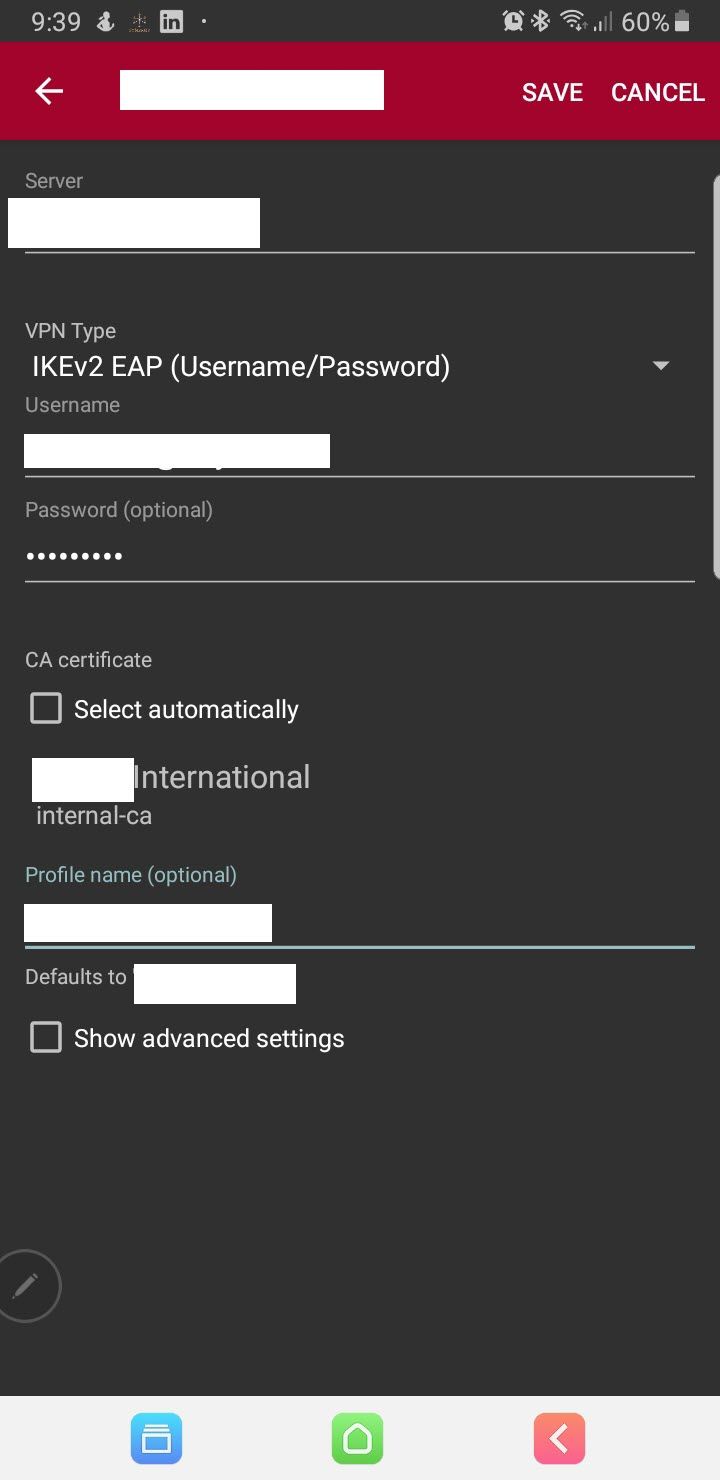
This on the Andriod
-
@Alanesi
Phase 1 - My identifier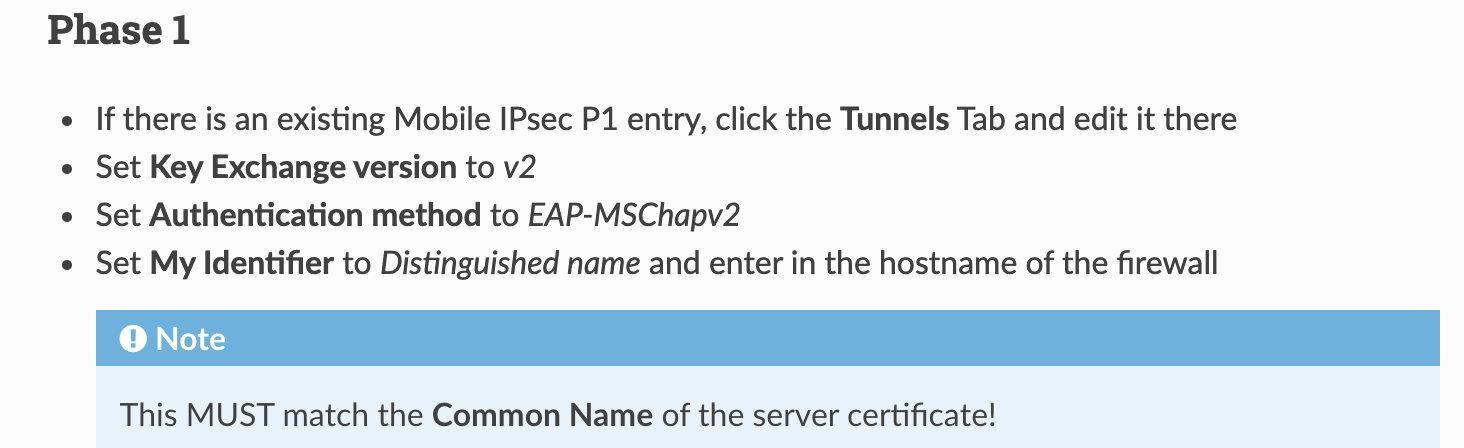
-
Thanks @Konstanti
I did that but it didnt make any diffreance still same error.
-
Phase 1:
Switch to:
AES / 256 bits / SHA256 / 14 (2048 bit)
and
Enable MOBIKEAndroid:
Don't forget the advanced settings (see above). -
Copyright 2025 Rubicon Communications LLC (Netgate). All rights reserved.
