Can't seem to force OpenDNS
-
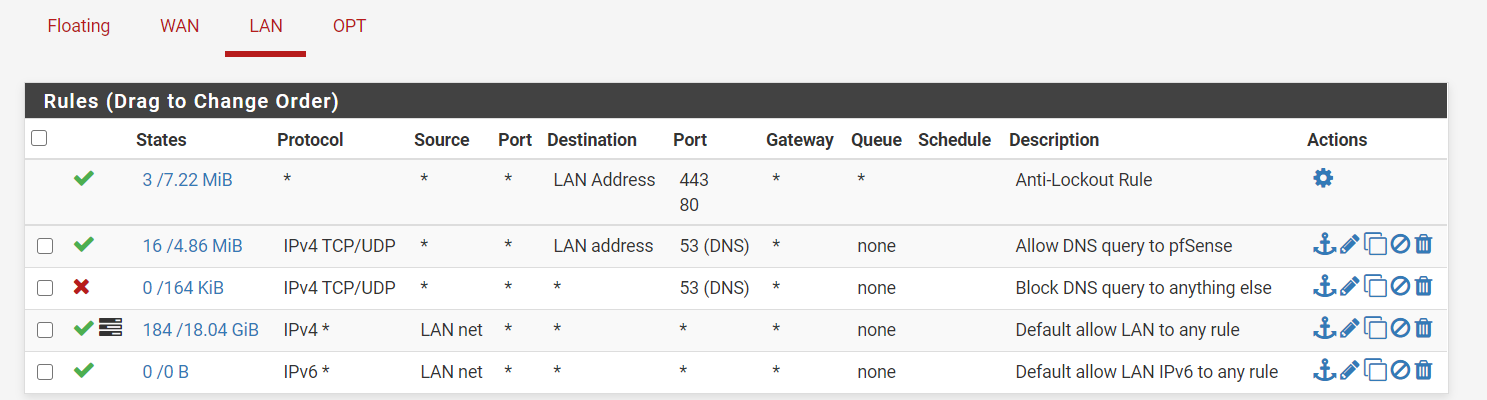
I have my firewall rules set to force all DNS queries to be resolved by pfSense.
And on my general setup page, I have the DNS settings like below:
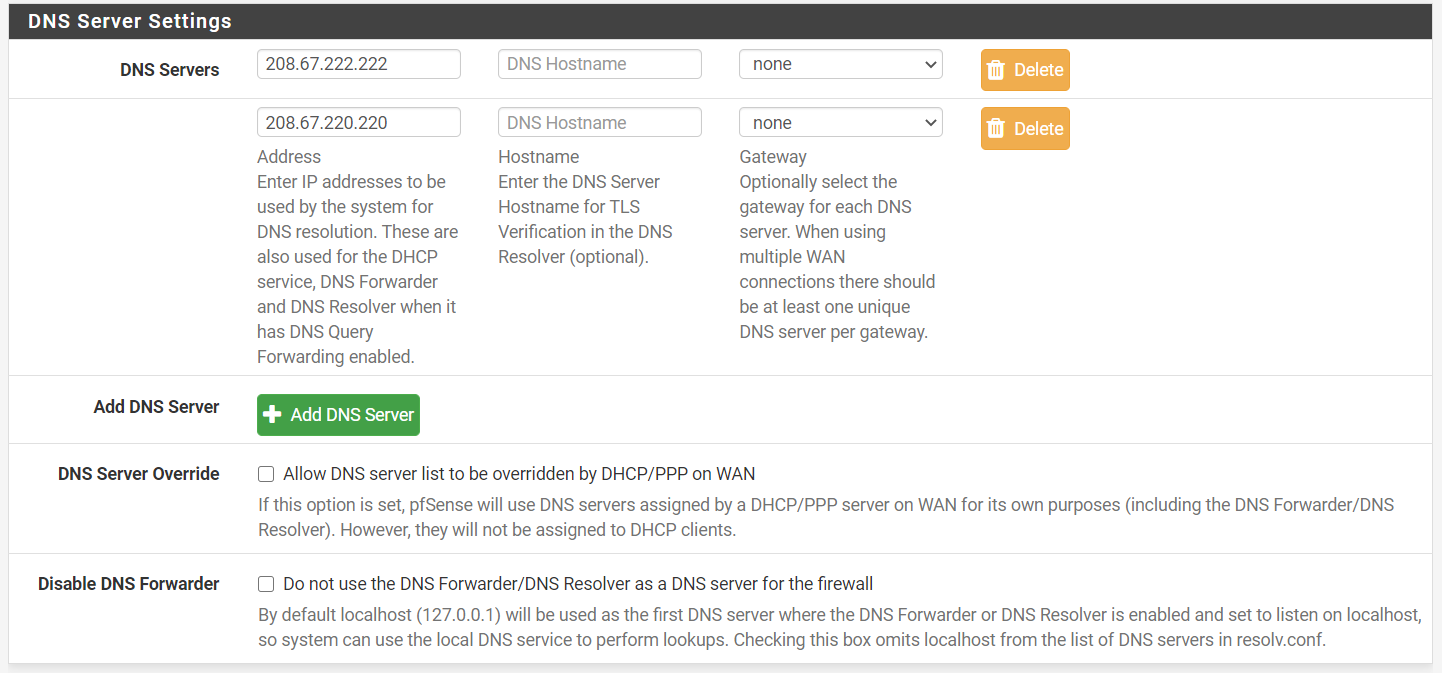
Given these two, I was expecting my clients to be forced to use OpenDNS. But that's not happening. They're still using the DNS supplied by my ISP. What am I doing wrong?
-
read DNS leak prevention -1
https://www.techhelpguides.com/2017/06/12/ultimate-pfsense-openvpn-guide/
-
@bcruze, is it possible that you misread my "OpenDNS" reference as "OpenVPN"?
-
Go to:
Services/DNS Resolver/General SettingsDown to:
DNS Query ForwardingMake sure its checked to be sent to those custom dns servers.
I would also add DNSSEC its important, read up on it. Check that too.
-
Thank you @Mr-Waste. That did it.
I read up on DNSSEC also. The good news is that the "Enable DNSSEC Support" box was already checked by default on my installation.
Bad news? Like most discussion topics about security, reading on DNSSEC makes me feel less secure about the world I live in. Anyway that's my problem. Thank you for the tip.
-
Reading up a little more (as discussed on this thread)
https://forum.netgate.com/topic/139771/setup-dns-over-tls-on-pfsense-2-4-4-p2-guide/11It seems like enabling DNSSEC when forwarding to known public DNS servers may be generally pointless.
I am still going to keep the option checked, because I don't know enough. But I'll change that if someone acts confident and tells me to :-)
-
@DrPhil said in Can't seem to force OpenDNS:
reading on DNSSEC makes me feel less secure about the world I live in.
How so ?
When a DNS request is answered with the DNSSEC== Ok anwer, you know that that answer is certified (and not spoofed).
That should/could give you a 'more secure' feeling.DNSSEC isn't about hiding DNS requests. It's about making sure the info retrieved is valid.
One that wants to hide something shouldn't use Internet at all ;)Anyway.
Have a look at some of the discussions about DNSSEC and forwarder usage on this forum.
Surprise : these two are mutual exclusive.
So if you use a forwarder (you're forwarding to OpenDNS - OpenDNS is a resolver) you loose DNSSEC advantages.
Ok, if you fully trust OpenDNS - and you fully trust your ISP (the could be MITM your DNS requests ;) ), your good. If not, use a resolver (like unbound) that checks DNSSEC for you on your premisses, with a device you control - pfSense.
Note : you can 'check' the DNSSEC option when using the resolver as a forwards. The effect will be "null". -
Completely off topic, but I think it's a personal / psychological thing. I remember once I was at University of Chicago. They had these parking ticket dispenser looking machines. I asked someone what those are for. They said if you're walking (especially alone after dark), and you sense some danger, you hit the red button on these boxes and the police will show up.
You could argue those boxes should make you feel safer. They had the opposite effect on me though. Because I was completely ignorant of the danger before.
Same way, I wasn't really aware that a fundamental gateway to the internet, the DNS service, is not really secure. All someone has to do is to poison the server I hit, and they control me. Reading about DNSSEC made me aware of that danger.
I felt more secure before, tucked under my blanket of ignorance.
-
@DrPhil said in Can't seem to force OpenDNS:
I felt more secure before, tucked under my blanket of ignorance.
The world is happy/safe place - until you watch the news ;)