DNS Resolver - only on 443 > DNS_PROBE_FINISHED_NXDOMAIN
-
Hey guys,
I resetted my entire network and started from scratch with basic settings. I hope someone can point me in the right direction.
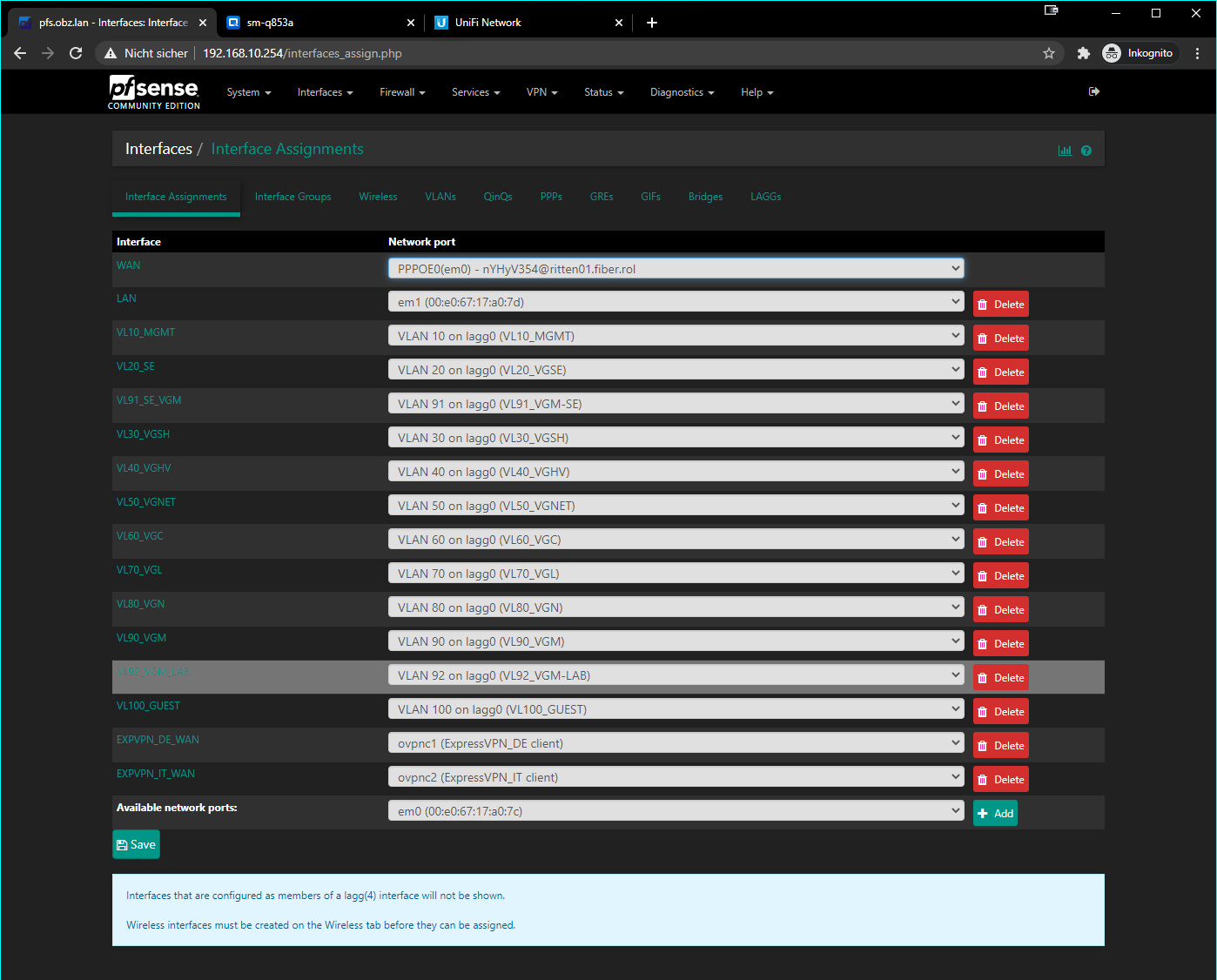
I got basically all services running I need BUT with one exception: Most of my vlans are leaving the network trough a VPN (expressvpn), IoT and Smart Devices have no problems with netflix, but when trying to reach netflix.com on a browser I get DNS_PROBE_FINISHED_NXDOMAIN > EVEN on devices which are not on the VPN vlans.
Where did I miss?
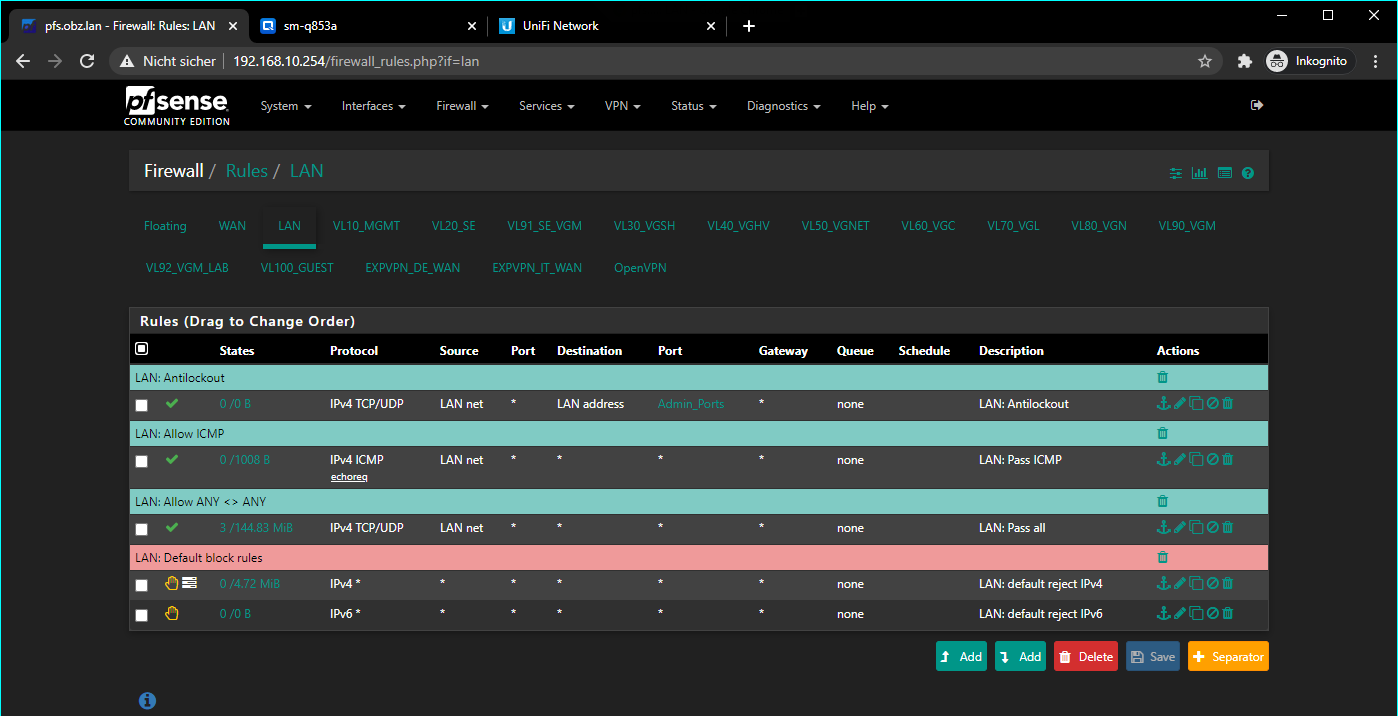
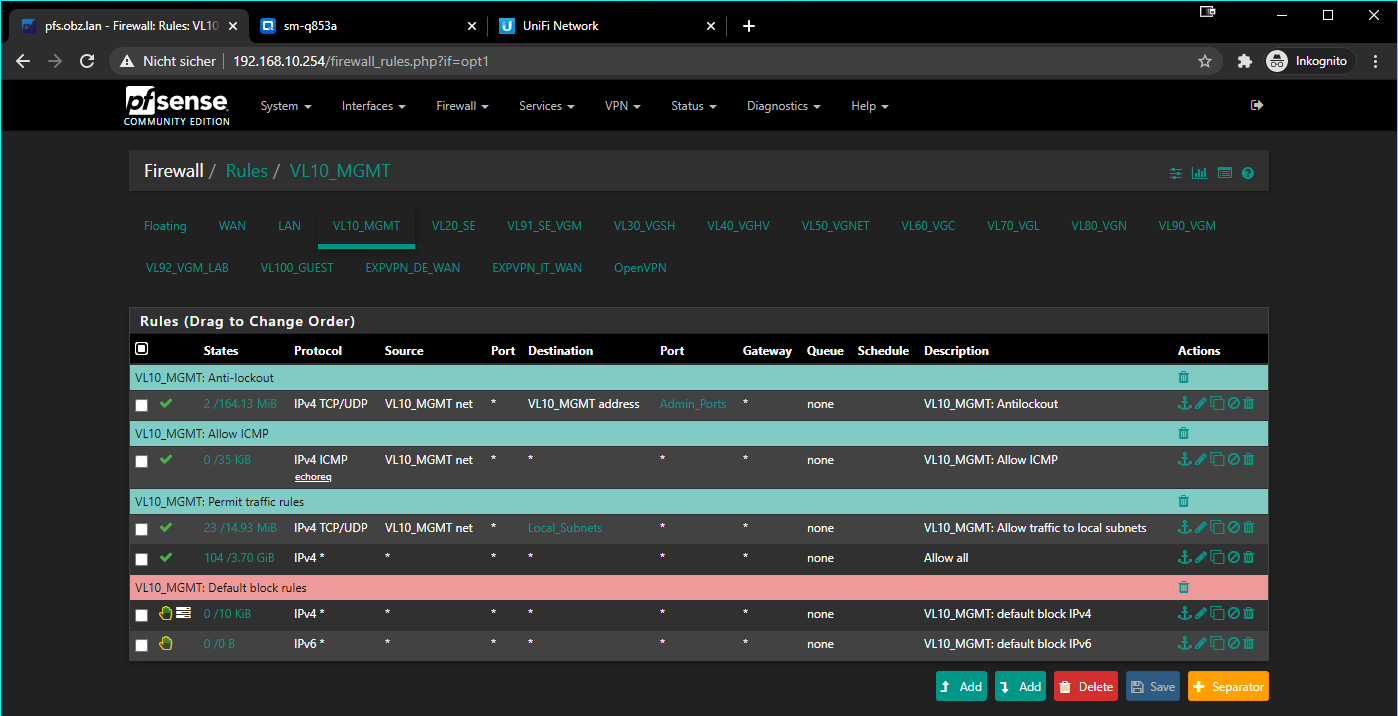
-NO VPN > LAN + VL10_MGMT
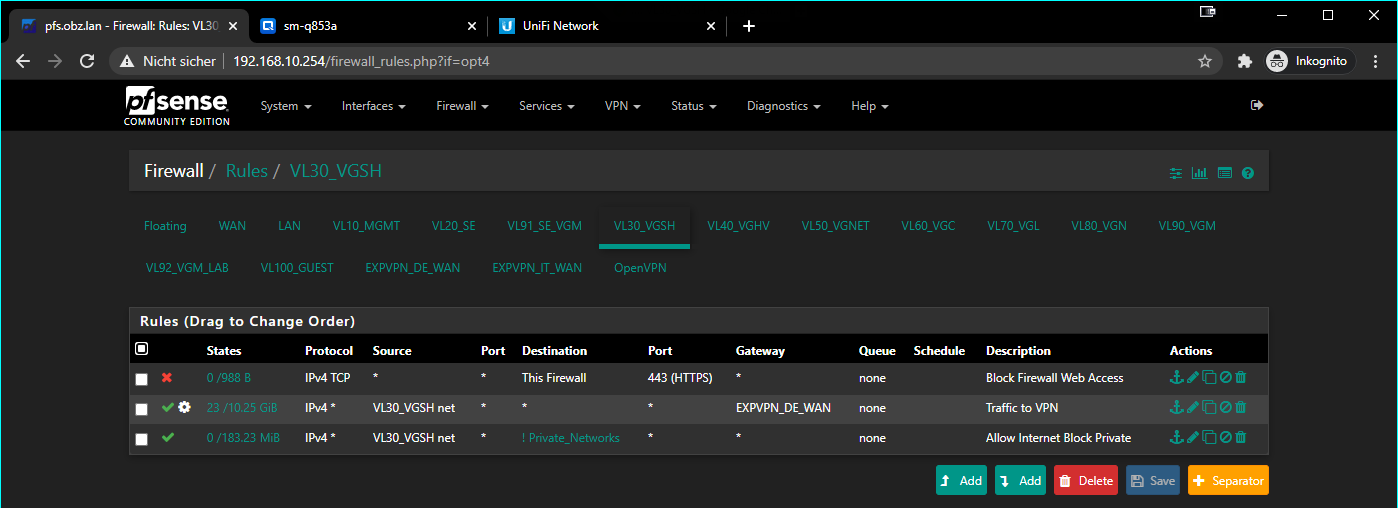
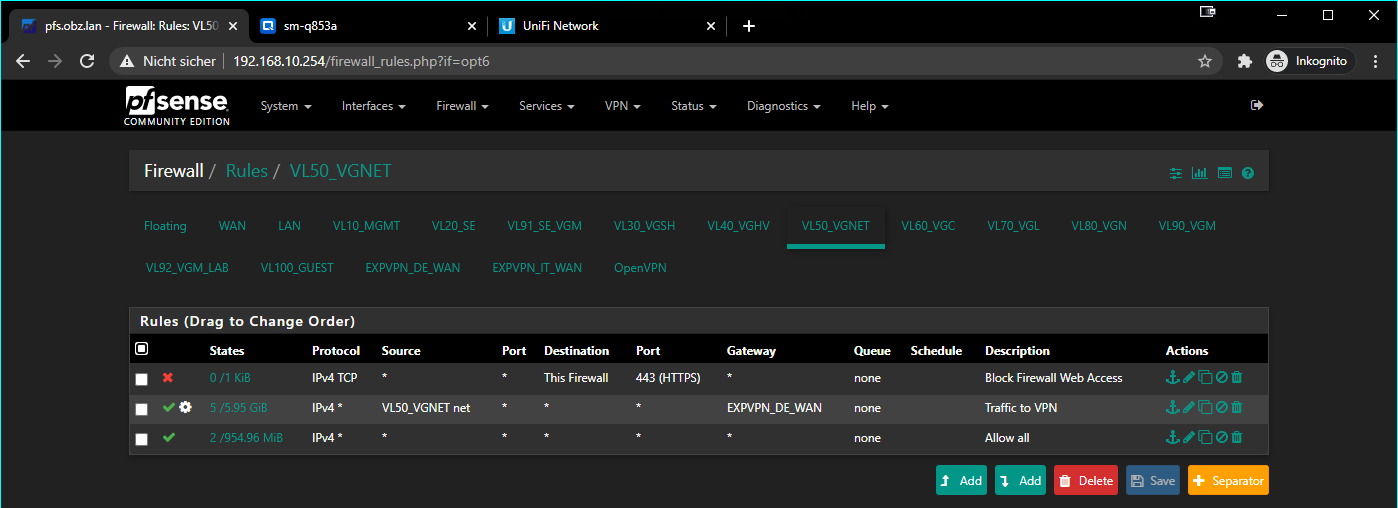
-VPN > VL30_VGSH + VL50_VGNET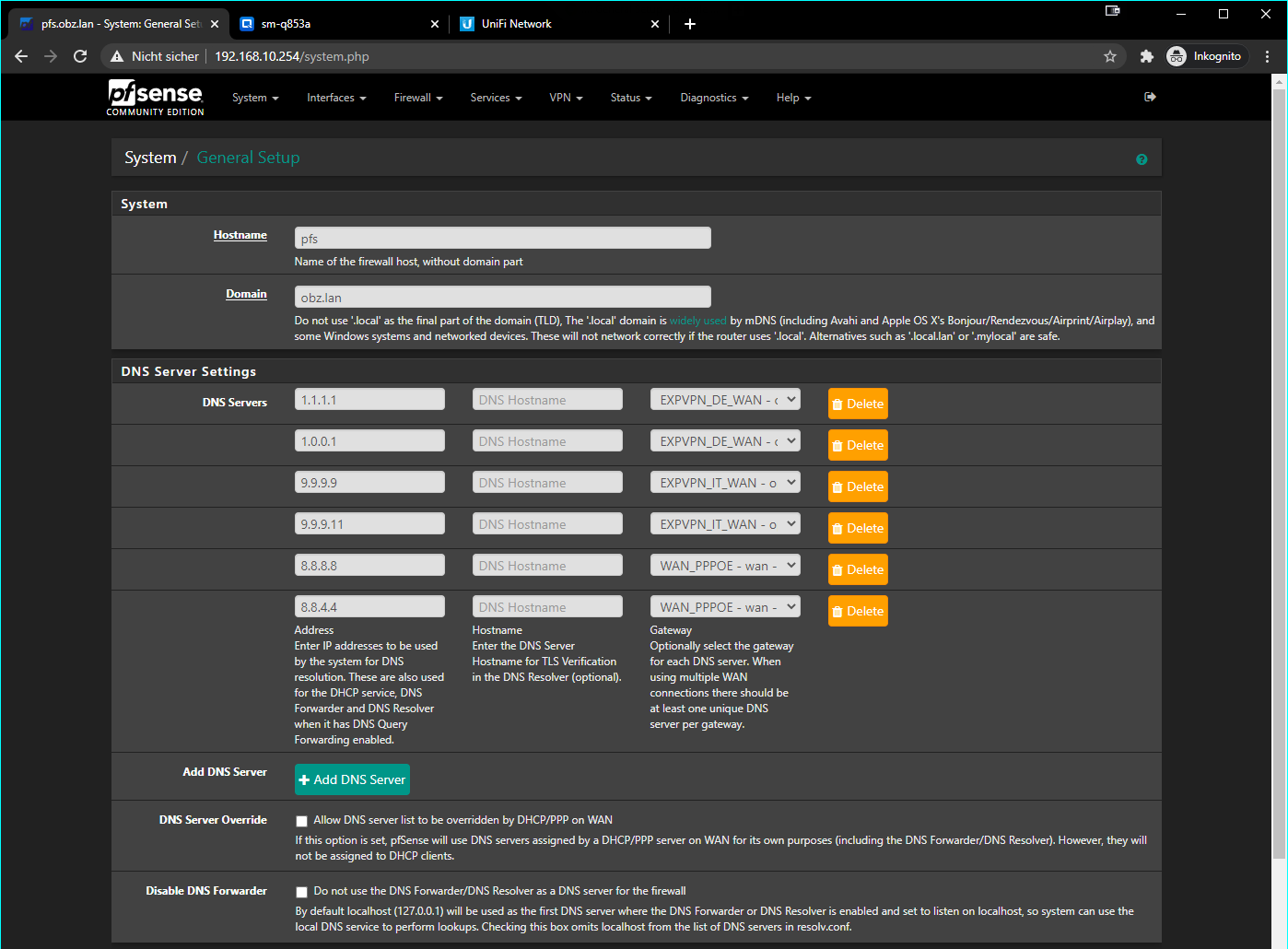
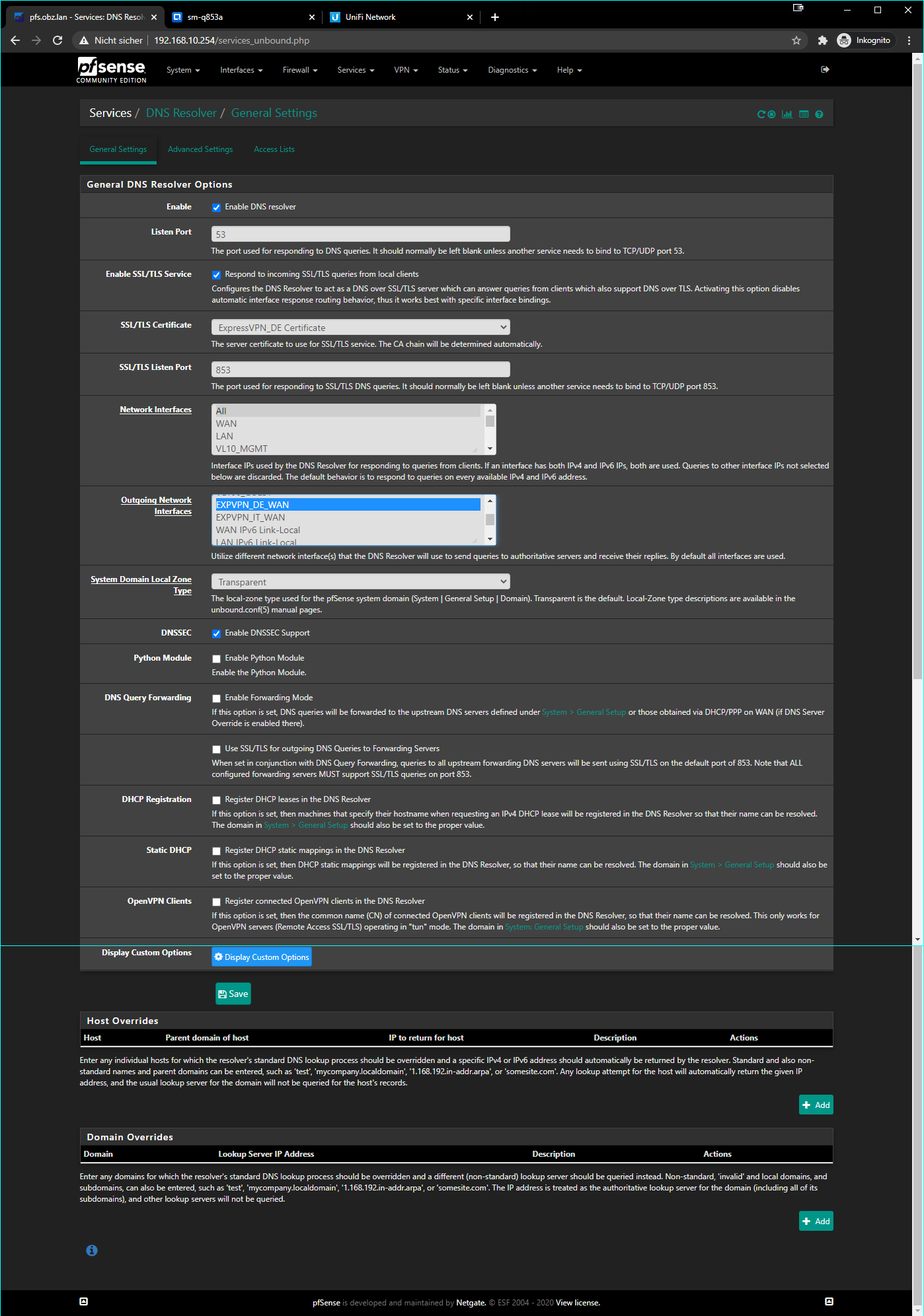
Unbound enabled / dnsmasq disabled
Have a great day!
-
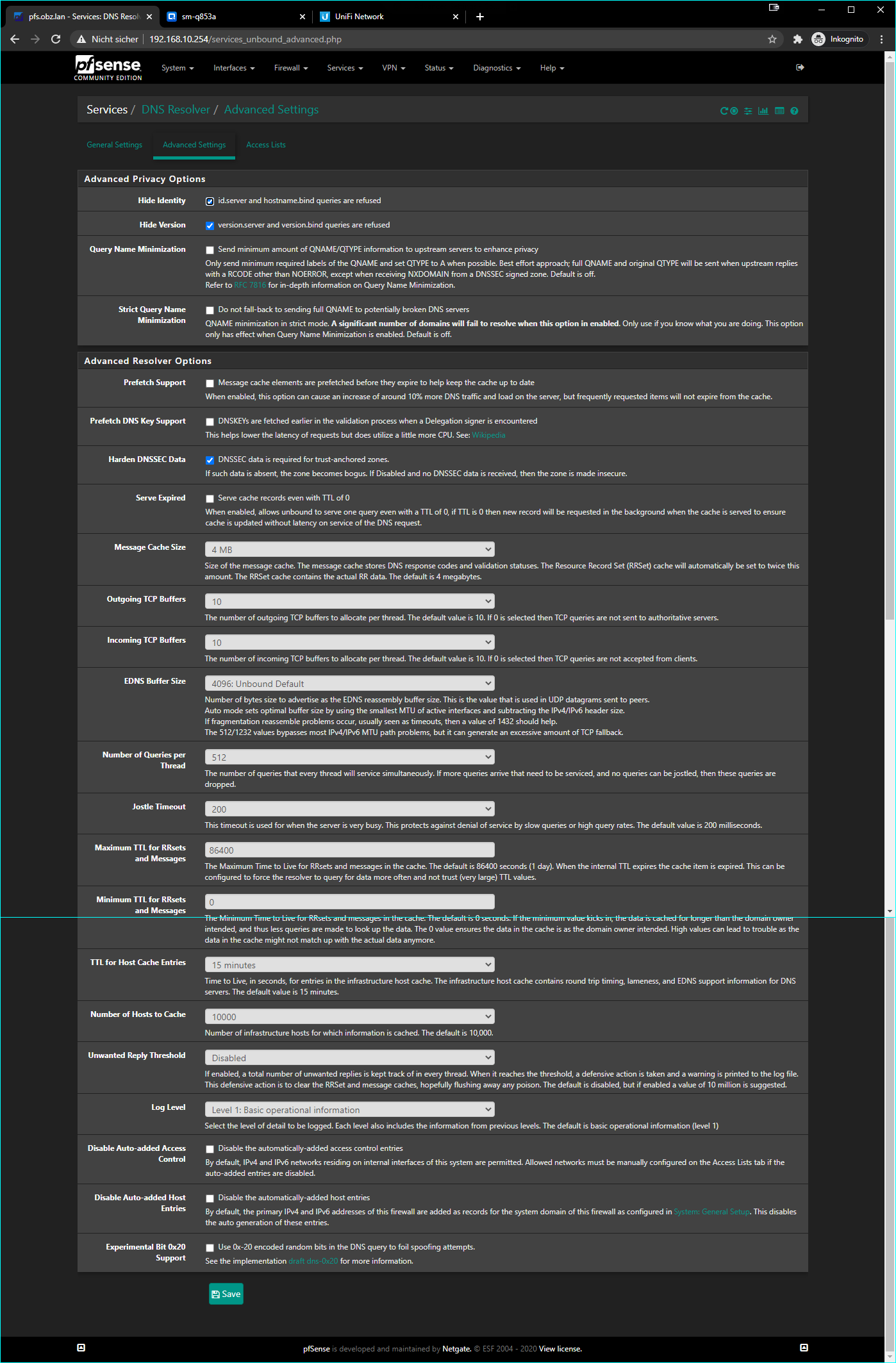
i can tell you that you don't need dnssec
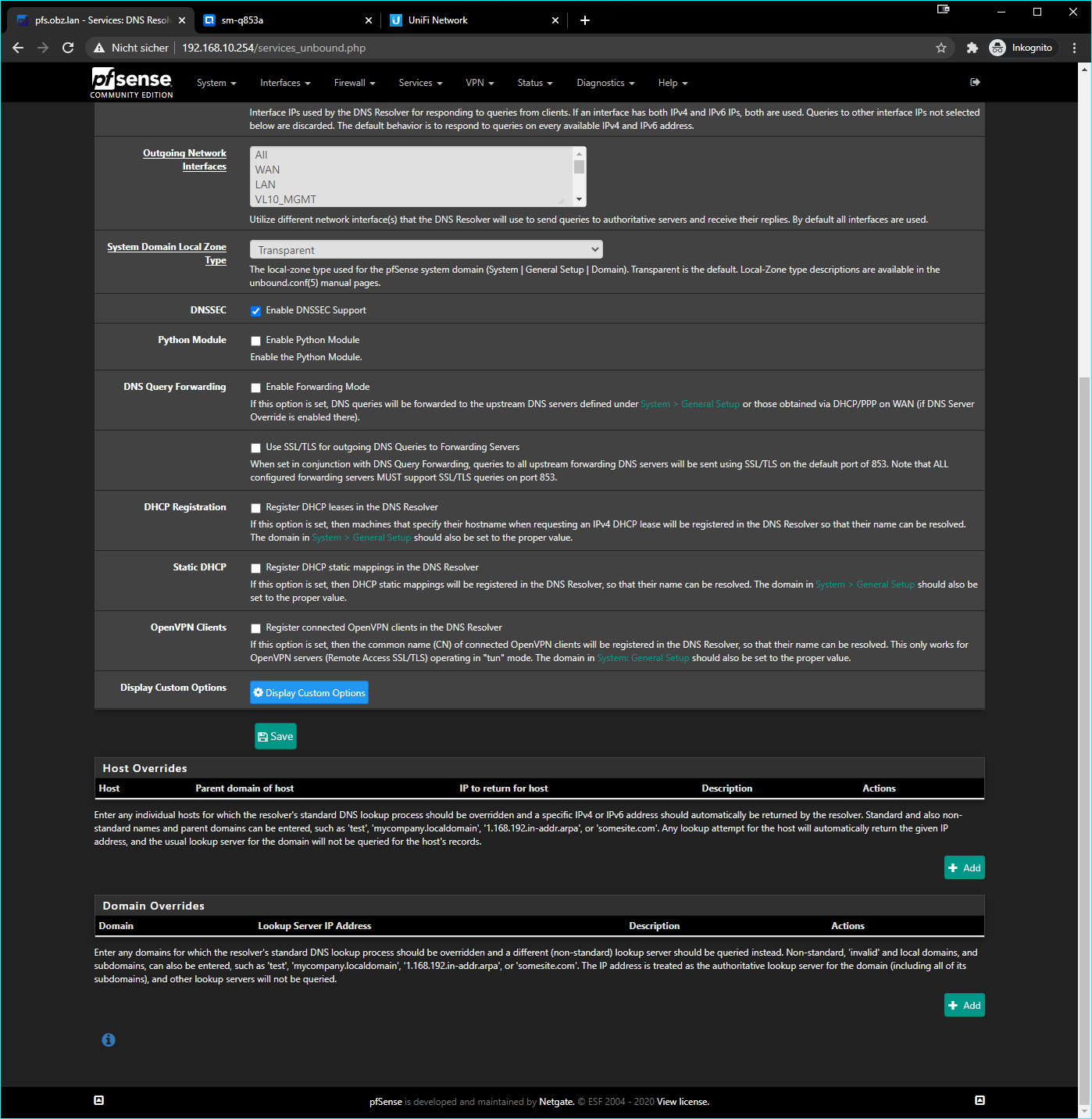
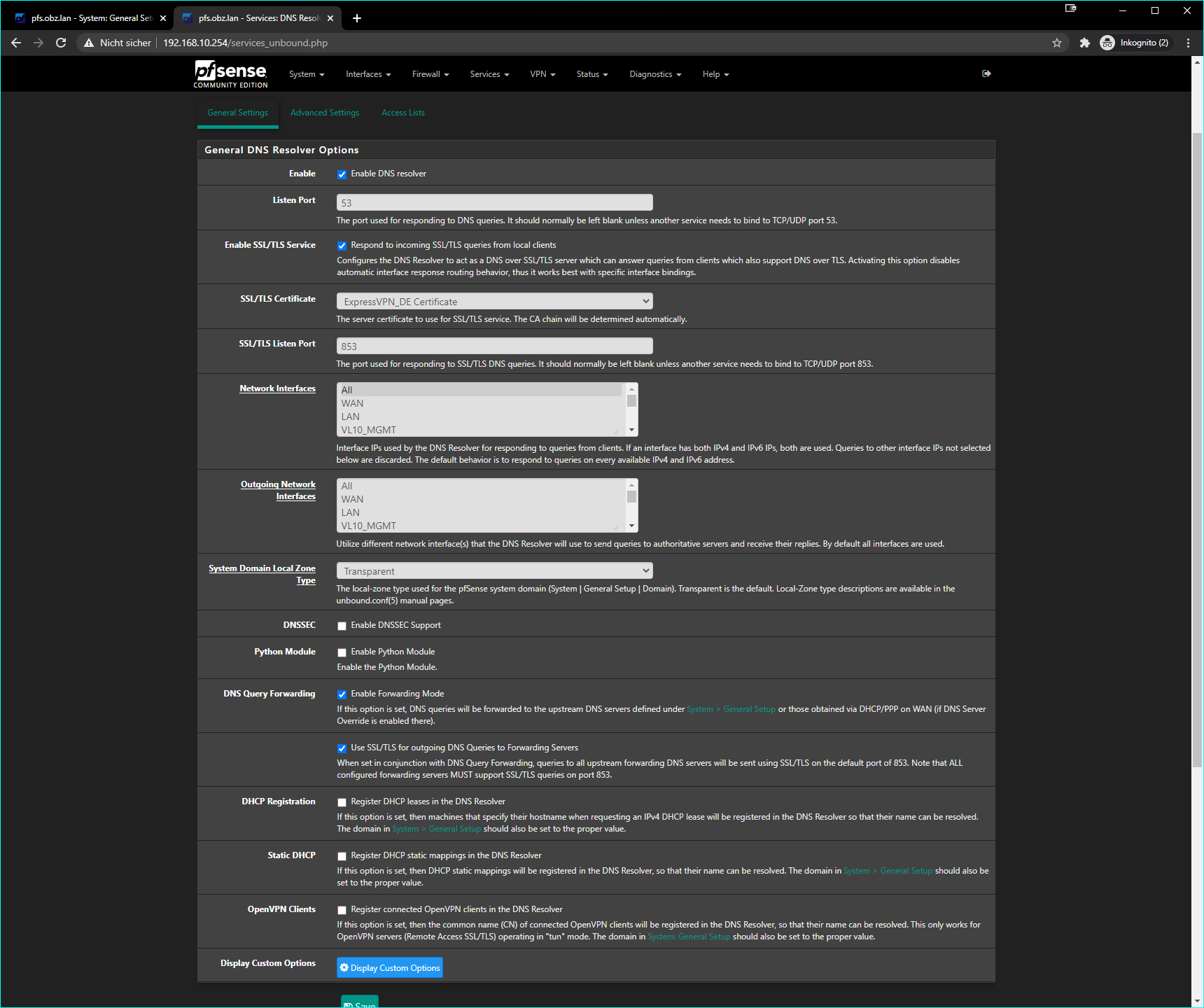
and you are not forwarding dns request
maybe try with DNS Query Forwarding enabled
I don't notice anything wrong with your screenshots but perhaps the error escapes me -
@kiokoman said in DNS Resolver - only on 443 > DNS_PROBE_FINISHED_NXDOMAIN:
i can tell you that you don't need dnssec
Why is that, he is not forwarding in unbound - so he would prob want dnssec.. Only if he is forwarding would he not want dnssec checked.
Maybe I need more coffee.. But Im a bit confused on what your wanting to accomplish for clients.. So you want to route them out the vpn.. But what do you want them to use for dns?
Looks like you have your resolver trying to resolve, not forward.. And have clients be able to use dot to unbound, but then unbound would just resolve out using this 1 vpn connection?
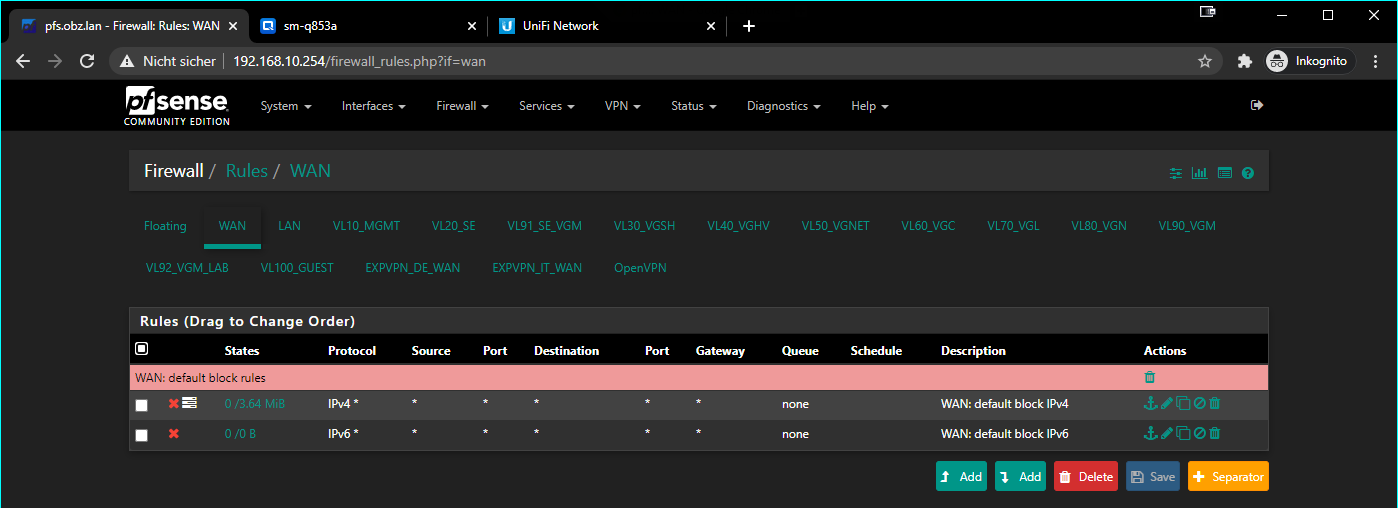
But your not allowing the devices to talk to unbound on 853 per your rules, you forcing all traffic out gateway?
You understand browsers these days also like to turn on doh by default, maybe your browser is trying to use doh, which you are routing through a vpn, and that might be blocked by the vpn?
Maybe vpn providers tell you to only use their NSers - or your "leaking" ;)
I really do not understand the use of dot or doh locally? Who are you trying to hide dns queries from on your local network? Yourself?
What exactly are you wanting to happen? What do you want the clients to use for dns? Where do you want pfsense to resolve? Understanding that anything put in general is possible for pfsense to use for its own internal resolving, and it would not use dot or doh to talk to these servers.
There is a redmine out to be able to adjust this behavior going forward.
https://redmine.pfsense.org/issues/10931 -
that's what confused me, if he does not want to forward why setting dns in general setup with gateway specified?
or I am the one that need more coffee -
Yeah - not exactly sure what his end goal here is?? Its a bit of hodge podge of settings, or maybe I just need a few more cups ;)
-
Please grab a drink and spend some time with a fool.
I had it all in openwrt, the vlans as regular internal networks/lan and clients going out the vpn.
-
Last time I Played with open or ddwrt was a really long time ago, but I do not believe it ran resolve - it ran forwarder.
If you want some outside dns to be used, then either point all your clients to those directly, or setup unbound to forward. In your current screenshots your resolving.. So those entries in general don't have anything to do with your clients that ask pfsense (unbound) for dns.
-
@johnpoz said in DNS Resolver - only on 443 > DNS_PROBE_FINISHED_NXDOMAIN:
Maybe vpn providers tell you to only use their NSers - or your "leaking" ;)
In another thread here in the forum I read that those DNS-servers are neccessary for Netflix to load everything as usual using a VPN inbetween
or setup unbound to forward
Disabled DNSSEC and setup unbound to forward, I'm now able to reach netflix.com via https, thanks
But your not allowing the devices to talk to unbound on 853 per your rules, you forcing all traffic out gateway?
Could you please elaborate on this? I really don't want anything exposed to the world
Kind regards
Max -
@charles_moody said in DNS Resolver - only on 443 > DNS_PROBE_FINISHED_NXDOMAIN:
elaborate
Here : https://forum.netgate.com/topic/139771/setup-dns-over-tls-on-pfsense-2-4-4-p2-guide/66?_=1603282378283
-
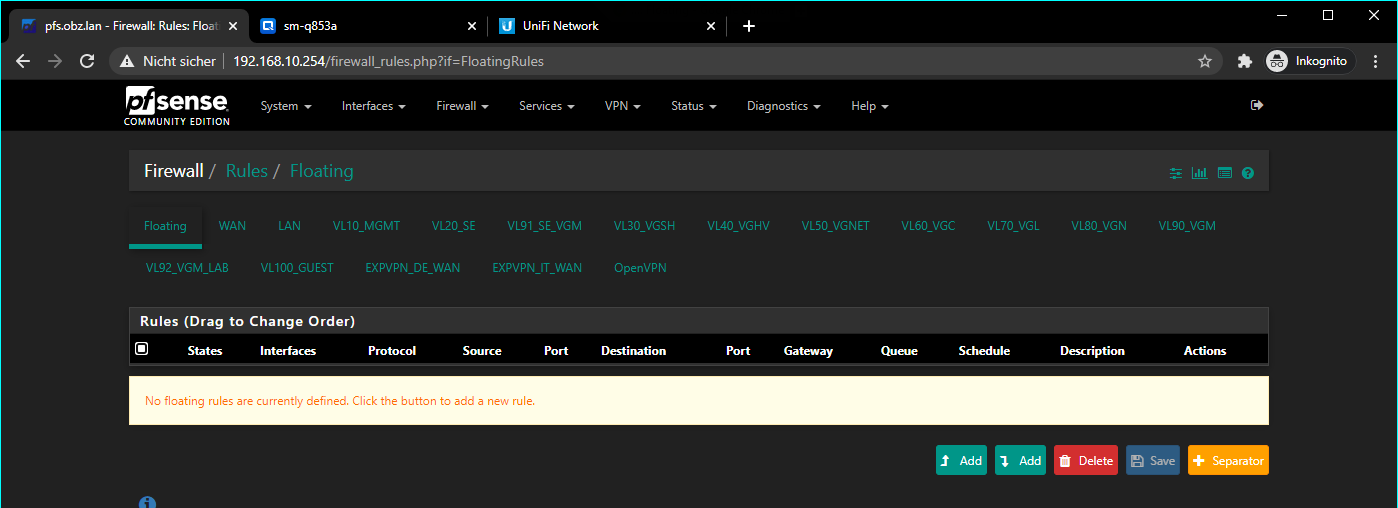
Your rules force all traffic out the gateway.
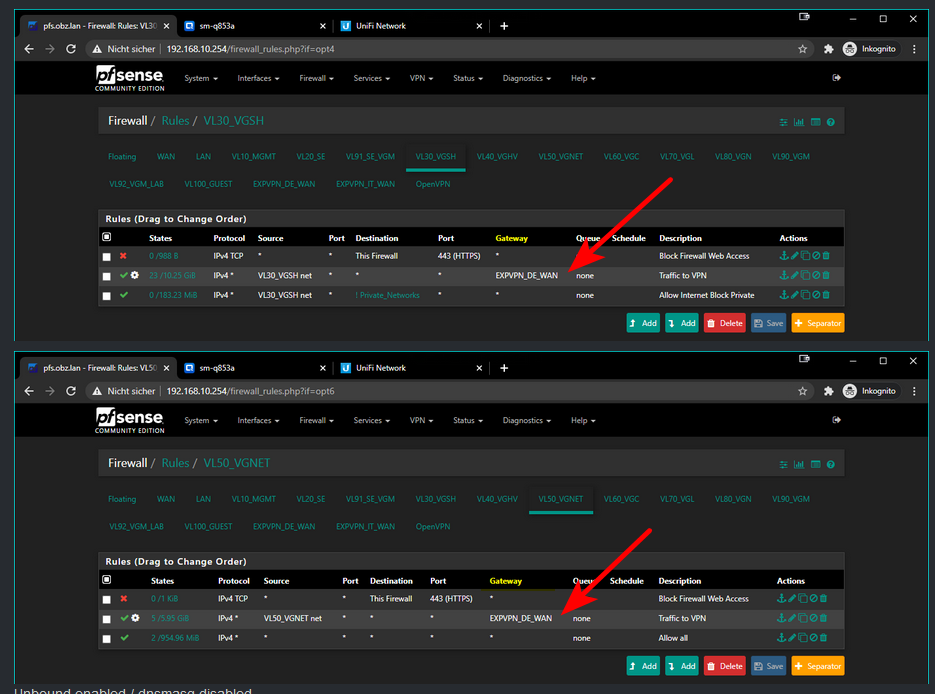
And the rules below that make no sense, because rules are evaluated top down, first rule to trigger wins, no other rules are evaluated.
So your rule sending traffic out your gateway is any any.. When would there be traffic that does trigger that rules.
When would there be traffic to ! private, that does not match the rule above it any any?
If you want your clients to talk to pfsense IP.. Where do you allow that? You block talking to pfsense on 443, then your next rule says go out the vpn.. How does vpn have access to pfsense vlan30 interface for example?