Chrony, PTP, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd)
-
@daddygo said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
HSO with Rubidium, OCXO, TCXO, Quartz = crystal :)
Yep, the crystal will be synced to the source and provide the correct time should you lose the connection to the source.
-
Forgot to mention, my background is in the telecom industry. Prior to IP becoming so popular, the phone network was based on time division multiplexing, which required precise synchronization. The way this was done was to include the timing in the signalling. At the company I worked for, LORAN C was used as the primary source. However, that provided a time base only and not time of day. Some of the people I worked with didn't understand the difference.
-
@jknott said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
Forgot to mention, my background is in the telecom industry.
In a way, I am also a telecom professional, I used to build telecommunication microwave networks and antenna systems
(I got a degree in RF engineering, huhu many many years ago :-))Now I am the chief engineer of a URH-FM network of several radio stations.
(yeah, but we currently have several satellite broadcasting cars, where timing is also important)BTW:
Thanks for the technical guide (NIST) I have not come across this before -
In a "Big Enterprise" where timestamping is critical , nobody would use the firewall as their NTP Master.
They would use dedicated hardware , as the Mentioned Meinberg above, or Ie.
Symmetricom.
https://prostudioconnection.com/products/symmetricom-syncserver-s300-gps-ntp-network-time-server-atomic-clock-receiver-refurbished-1They would have 2..4 of these boxes , spread over multiple sites ,and all in a "Peer setup", they might even use a couple of "selected" external NTP servers, for extra reduncancy. But their primary trust would be their internal dedicated NTP servers.
You can even get some of the bxes doing both NTP & "SYSPLEX" ... @JKnott

Dealing with timestamping firewall loglines and/or Certificate validation would easily be fulfilled, by letting the firewall be a Client to the "Inside coproprate NTP setup".
Your normal PC/server Xtal is NOT "Time-nut" worthy , and it will drift quite a lot depending on environment temperature.
The Interrupt Latency would also be variable , especially with the CPU ability to scale frequency up & down , and will contribute to the Jitter.A dedicated NTP server would often have 1-PPS timestamping in hardware , and if the buyer isn't going "Cheap" , there will be an OCXO or even a Rubidium clock source inside.
The need for the OCXO/Rubi is typically for improving the Holdover period (aka if the GPS signal is lost). A TCXO would be enough for keeping the "Specs" if one would trust that the GPS signal was always present.PHK did a "Super precise NTP server implementation" using the Soekris
https://www.febo.com/time-freq/ntp/soekris/index.htmlAnd the "Magic" was HW-timer 1-PPS timestamping , in the ELAN CPU used in the Soekris. Helped
Ohh his work on the BSD Kernel timestamping, didn't hurt either.
But that would be available for any BSD HW.Edit:
This is the drift on my Atom270 based NTP Server, using a "simple" Xtal$ cat /var/lib/ntp/ntp.drift 26.975/Bingo
-
Dear pfSense friends! (May is call You like that ? ;)
Personally I thankful to all here and each of You about suggestions and professional-grade level of discussion! A lot of interesting info for others and some - may be interesting for Pro-grade SysAdmins.
Only a few users here on forum have dedicated stand-alone Time-source device, like You refer to in several replies ago.
So, let me propose to change our direction back to the Chrony with NTS/NTPsec as replace of old/unsecured NTP. (In form of additional package with GUI for pfSense).Cheers
-
@sergei_shablovsky said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
So, let me propose to change our direction back to the Chrony
Uhum

as someone wrote above this needs to be ported, I don't think it will be included otherwise, may need a persistent and dedicated programmer with a lot of time,....hihihi
You wrote you may have time in the winter, we would welcome such an initiative
(note: as a system administrator say, it's COVID time again, ergo more work, not to mention Ransomware + APTs
-
@daddygo said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
as someone wrote above this needs to be ported
I think 3.5 is available since freebsd 12? Just in the normal freebsd packages.. So it should be possible without having to build or port, etc. Latest is 4.1?
-
@johnpoz said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
I think 3.5 is available since freebsd 12?
Ah, right it's already 4.1 currently...
https://www.freebsd.org/cgi/ports.cgi?query=Chrony&stype=all++++edit:
Then all we need is PHP, Netgate and you're done :-) -
@daddygo said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
Then all we need is PHP, Netgate and you're done
Easy peasy ;) @Sergei_Shablovsky can you knock that out this afternoon ;) hehehe
-
@daddygo said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
@johnpoz said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
I think 3.5 is available since freebsd 12?
Ah, right it's already 4.1 currently...
https://www.freebsd.org/cgi/ports.cgi?query=Chrony&stype=all++++edit:
Then all we need is PHP, Netgate and you're done :-)As You may see both for ntpd (FreeBSD) and Chrony (FreeBSD, offsite) a lot of settings are common, so most users that need NTP service on pfSense would have short adoption time and not to be disappointed by a lot of new options in NTP GUI.
The main question is still “because of ntpd was outdated is replacement to Chrony in pfSense NTP service needed, or better to keep both ntpd and Chrony as additional pfSense package”.
Anyway time of ntpd gone away (like most of old protocols) and one day this question pop up again. Why need to be so sticky to old protocol? Chrony able to keep old-fashioned ntpd clients well without any issues, Chrony already exist in FreeBSD 12 and 13...
-
@sergei_shablovsky said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
The main question is still “because of ntpd was outdated is replacement to Chrony in pfSense NTP service needed, or better to keep both ntpd and Chrony as additional pfSense package”.
NTP should not be removed from pfSense , it is still the industry standard, for timekeeping.
Anyway time of ntpd gone away (like most of old protocols) and one day this question pop up again. Why need to be so sticky to old protocol? Chrony able to keep old-fashioned ntpd clients well without any issues, Chrony already exist in FreeBSD 12 and 13...
How do you come to that conclusion : That "time of ntpd gone away" ?
It is my impression that: Before this thread you didn't even know Chrony existed .....If you can convince Netgate to or implement your self: A Chrony integration then by all means go do it. An additional pfSense Chrony package wouldn't hurt.
But don't "slaugther" the NTP package (implementation), just because you got an idea.
/Bingo
-
@bingo600 said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
@sergei_shablovsky said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
The main question is still “because of ntpd was outdated is replacement to Chrony in pfSense NTP service needed, or better to keep both ntpd and Chrony as additional pfSense package”.
NTP should not be removed from pfSense , it is still the industry standard, for timekeeping.
Anyway time of ntpd gone away (like most of old protocols) and one day this question pop up again. Why need to be so sticky to old protocol? Chrony able to keep old-fashioned ntpd clients well without any issues, Chrony already exist in FreeBSD 12 and 13...
How do you come to that conclusion : That "time of ntpd gone away" ?
It is my impression that: Before this thread you didn't even know Chrony existed .....I just try to make things better. (“better” means in technical term;)
I hands up on Your solution, because it’s better than only implementing NTS/NTPsec.
If you can convince Netgate to or implement your self: A Chrony integration then by all means go do it. An additional pfSense Chrony package wouldn't hurt.
But don't "slaugther" the NTP package (implementation), just because you got an idea.
;) Ok, let’s start with Chrony in addition to pfSense's ;)
-
@sergei_shablovsky said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
“because of ntpd was outdated
hmmmm,

This is a very tough and I think premature statement, the whole world cannot be so foolish as to trust its life to an outdated protocol, yes its life, because we depend on it at the moment
-not to mention the fact that this money-modulated world of ours is also run by this protocol in terms of money
we think it is not so important, but it is and it still works well in the background
Ok, I see that you registered at the end of 2019, ergo you can see that introducing a new thing to pfSense is not a "torch marching"
at the moment there are other more important things to be improved, which I think is a priority
https://redmine.pfsense.org/projects/pfsense/roadmapDon't get me wrong, we would love to see your work, if you take on this challenge, have here a couple of "well versed in the ways of time" colleague, you know :) and we could certainly help...
BTW:
There were some attempts that I was interested in at one time (ntpv3 vs. ntpv4), but I stayed with the multi-source (3-5) NTP
https://blog.cloudflare.com/roughtime/And for important workloads, as I mentioned above, PTP IEEE 1588-2002 / IEEE 1588-2008 for audio remains the target hardware Meinberg
-
@daddygo
What switches are you using to distribute your PTP, around on the site(s) ?
That's imho the biggest PTP Killer, that you's need all your switches to be PTP enabled.Especially if you already have an existing (working) switch infrastructure.
I for one doesn't have a single PTP enabled switch at home.
And would prob. not be paying extras for one.Then again if i needed any of my home devices to "Really" be in "sync" i would prob. just distribute my GPSDO (or PRS-10 Rubidium) 1-PPS around using balanced mode and RJ-45 cables. Not an optimal method in a large corp building.
/Bingo
-
@bingo600 said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
What switches are you using to distribute your PTP, around on the site(s) ?
Let's see.....
Enterprise level:
One that has worked for us for a long time (and since we also do video processing) is the Arista 7500 series family:
https://www.arista.com/assets/data/pdf/Whitepapers/ME-PTP-White-Paper.pdf
https://www.arista.com/assets/data/pdf/Datasheets/7500RDataSheet.pdf
My experience so far is that this cannot be done well and cost-effectively in a SOHO environment.
In our smaller studios we use the following devices, synchronized from an external clock source:
https://studio-tech.com/products/m5401a/
(with GPS module opc.)
+++ Cisco Catalyst 3800 series + 10G optic network (in-house facilities)
https://www.cisco.com/c/en/us/products/collateral/switches/catalyst-9300-series-switches/q-and-a-c67-744007.pdf@bingo600 "Especially if you already have an existing (working) switch infrastructure."
When we changed to DANTE AoIP and AES67 we changed the complete L1 - L2 infrastructure...
This is the only reasonable way to do it, as good PTP is the rule of thumb for real-time audio deliveryWe implemented this DANTE stuff almost 7 years ago, as the first radio network in Central Europe,
It has a lot of pitfalls, but once I get it right it's very convenient, I can route the sound exactly like TCP, hahahaha...Our mixing tables are also software based, no more FADER replacement because the mechanics components are tired
We represent America in Europe
https://www.arrakis-systems.com/arrakis---darc-virtual-console.html
(My company is the representative of Arrakis)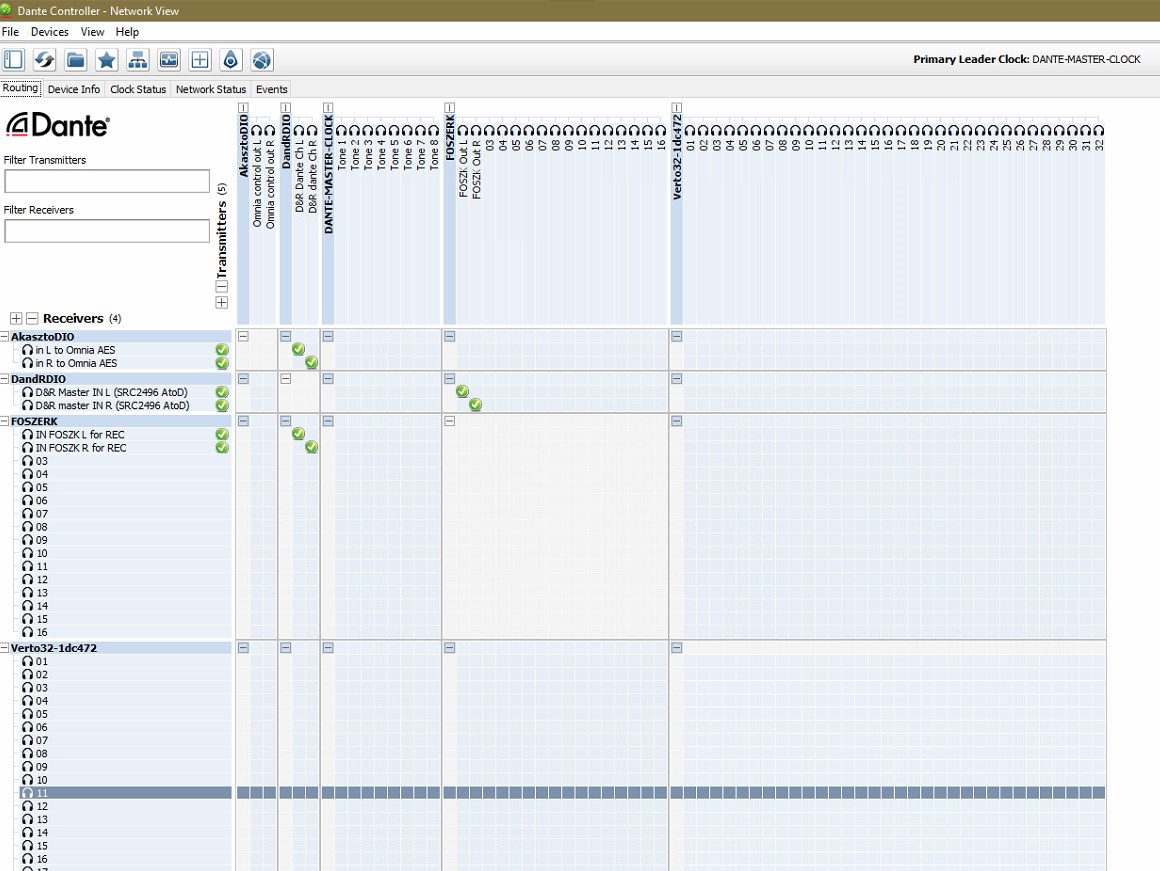
So here I encountered the concept of time in more depth, and here as well Hawking - The Time :)
-
@daddygo said in [Chrony, Network Time Security (NTS, NTPsec) to
+++ Cisco Catalyst 3800 series + 10G optic network (in-house facilities)
https://www.cisco.com/c/en/us/products/collateral/switches/catalyst-9300-series-switches/q-and-a-c67-744007.pdfI could have gotten two c3800,for less than $500, but they're power hungry and noisy. So i skipped on those.
You linked the C9300, those are nice DC Switches, but quite above a "home budget" ... Even the SFP+ are above , i'we set up a few in a DC.
, i'we set up a few in a DC.Well i'm not routing Pro audio or Video , so i'll stick to my home time-nuttery
/Bingo
-
@bingo600 said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
Well i'm not routing Pro audio or Video , so i'll stick to my home time-nuttery
Yeah, these are big boy toys....

I can't remember exactly, but the cost of acquisition was close to 350K USDIn a normal family house they are not applicable, as you write a nuclear power plant should be bringing for them...
I just took it out of the storeroom 2 pcs. Cisco UCS FI6248UP Fabric Interconnect to upgrade the UCS Manager on them before they go to the market, my wife chased me around the house with a big knife, because of the noise. (they only operated for half a day) hihihihihi
I keep animals like these at home:
1 pcs. MikroTik CRS305-1G-4S+IN for GPON distribution
2 pcs. Cisco SG500XG-8F8T (in stack)
2 pcs. Cisco SG350X-24P
1 pcs. SuperMicro M11SDV-4C-LN4F + Intel X710-DA4 for pfSense
1 pcs. SuperMicro SYS-E300-12C + Intel Xeon W1290 for VMs
1 pcs. Synology RS1221RP+ for storage
3 pcs. Cisco AIR-AP1852I-E-K9 for wirelessIt's plenty for home use :)
-
@daddygo said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
2 pcs. Cisco SG500XG-8F8T (in stack)
2 pcs. Cisco SG350X-24PThose for sure would be sweet for home use - nice! I am jealous for sure..
-
@johnpoz said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
Those for sure would be sweet for home use - nice! I am jealous for sure..
I got lucky with the 500s, I bought from an Australian guy on eBay about a year ago, he either didn't know what he was selling or was too nice to sell me a pair 500 + 6pcs. twinax cables for AUD 850.
(Oh yes, I arranged the shipping from AU, including with customs, was 180 USD)The SG350Xs are from the radio company, they just fell off the truck and I snapped them up, :)
-
@daddygo said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
3 pcs. Cisco AIR-AP1852I-E-K9 for wireless
I'm still at 1Gbit at home.
All using lowpower fanless switches.My "Server" (File,Mail, DNS & DHCP) is a Deb-10 Linux , running on an 2GHz Atom.
I just have a "Little" Acer-Revo (Core i3 - 16GB Ram + SSD) for VMware
Runs my Zabbix monitoring and PI-Hole , and a few other Debian'sI have C2702E AP's here & in the summerhouse ($42/pcs).
Those SG500's looks nice , but atm. i really have no need for 10G.
Maybe with the "Next Server" ...
But my wife has a BIGGER KNIFE than yours , and has "Fan allergy" , besides she can hear the "grass grow"I just said no to a DLP360 G9 server for free

Was NEVER going to get away with that one .... (Office next to the bedroom)/Bingo