HEADS UP: OpenVPN deprecating shared key mode, requires TLS, deprecating cipher selection
-
@randyw said in HEADS UP: OpenVPN deprecating shared key mode, requires TLS, deprecating cipher selection:
@jimp
Hi, this was an interesting read. Unfortunately the v2.6 also killed my PureVPN connection and even the tecks couldn't find the reason for not even connecting at all to their servers. They even logged into my system and said that PFsense v2.6 is incompatible with their servers. BONG... what happened ?
I thought v2.6 was up to date on all of these changes.
pfSense CE 2.6.0 does not use OpenVPN 2.6.0, this post is about OpenVPN 2.6.0 which is still not released yet. Start your own thread with details about your problem, it's most likely an issue in your settings. OpenVPN is OpenVPN and is very good about compatibility but occasionally needs some adjustments as they change options/protocol details.
-
Thanks for the post! I've read through documentation and watched a few videos. This maybe a foolish question, but if I have multiple "clients" connecting to our server. Do I need recreate a new CA and Certificate for each "client" OR Do I simply need to generate unique client certificate's? And apply the same server TLS key to each client?
-
With certificate generation with Lets Encrypt integration?
-
@mzaknoen said in HEADS UP: OpenVPN deprecating shared key mode, requires TLS, deprecating cipher selection:
Thanks for the post! I've read through documentation and watched a few videos. This maybe a foolish question, but if I have multiple "clients" connecting to our server. Do I need recreate a new CA and Certificate for each "client" OR Do I simply need to generate unique client certificate's? And apply the same server TLS key to each client?
I have followed this guide:
https://docs.netgate.com/pfsense/en/latest/recipes/openvpn-s2s-tls.htmlI export the CA and client certificates, then import them into the client netgate appliances. Read the entire doc because I missed some things at first regarding client specific overrides but after a couple times reading and actual hands-on it makes sense.
-
@mzaknoen said in HEADS UP: OpenVPN deprecating shared key mode, requires TLS, deprecating cipher selection:
Thanks for the post! I've read through documentation and watched a few videos. This maybe a foolish question, but if I have multiple "clients" connecting to our server. Do I need recreate a new CA and Certificate for each "client" OR Do I simply need to generate unique client certificate's? And apply the same server TLS key to each client?
If your server is setup as SSL/TLS and allows multiple clients on a single server, then it's already not using shared key or P2P mode and it will be fine.
The problematic setups are ones using shared key mode specifically (one server with one client, no certificates).
If you have multiple servers each with a single client and want to convert them, you can do so individually (still one server for each client) or collectively (convert them to one sever and multiple clients). How you handle the CA structure is up to you. You can use a unique CA per server if you want, but it's not strictly necessary. Each server should have a unique TLS key though, which will also help ensure that a client with the "wrong" cert won't be able to connect to a server it shouldn't be using if you have multiple.
-
I ironmonkey referenced this topic on
-
I ironmonkey referenced this topic on
-
@cool_corona Are you suggesting that everybody that can use LetsEncrypt should be able to connect to your VPN :-?

-
 G Gertjan referenced this topic on
G Gertjan referenced this topic on
-
 G Gertjan referenced this topic on
G Gertjan referenced this topic on
-
 G Gertjan referenced this topic on
G Gertjan referenced this topic on
-
 G Gertjan referenced this topic on
G Gertjan referenced this topic on
-
 J jimp forked this topic on
J jimp forked this topic on
-
 G Gertjan referenced this topic on
G Gertjan referenced this topic on
-
S SteveITS referenced this topic on
-
Dear Admins,
Can we have a post with the successful procedure of migrating 2.6 to 2.7 , in relation to open VPN Shared key VS SSL/TLS method ?
Here are some referenced posts with issues:
https://forum.netgate.com/topic/183854/open-vpn-2-7-site-to-site-odd-routing-issue/16
https://forum.netgate.com/topic/183644/site-to-site-with-shared-key-gateway-bug/3Are those resolved with 2.7.1 / 2.7.2 ? What is the recommendation for migrating ?
-
Something isn't / wasn't working ?
"Shared keys" was already depreciated many moons ago.So : setup a server (create a second ?!), and when done, redeploy the client "opvn" files to the OpeVN clients / users.
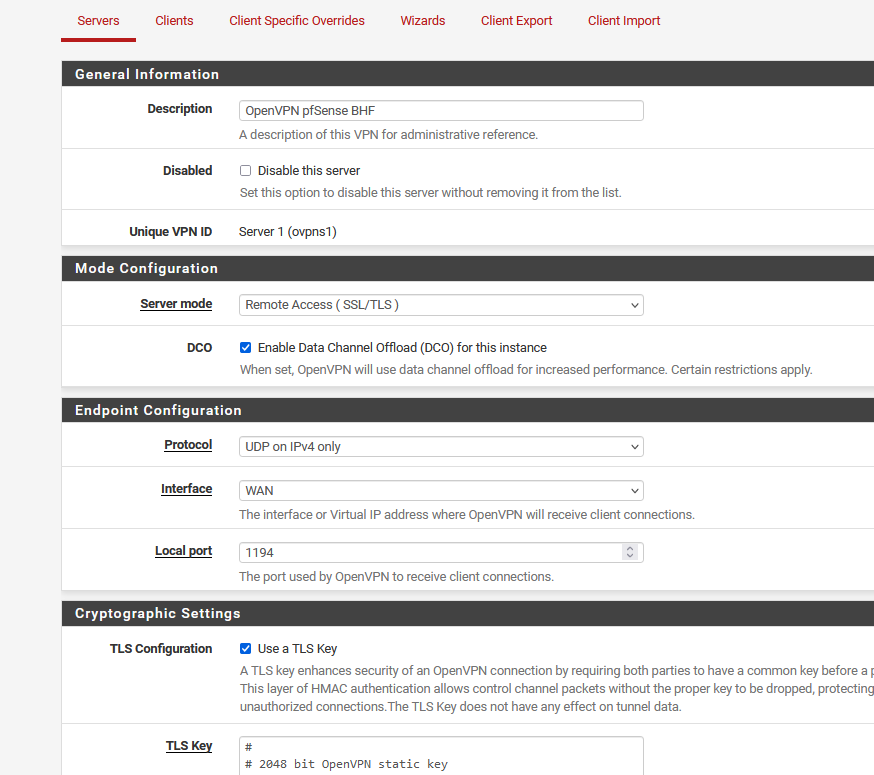
I use "Remote Access (SSL/TLS)", you could also chose for "Remote Access (SSL/TLS + User Auth).
-
@Gertjan thanks for the tips !
for the remote access VPN, if is SSL/TLS + User auth, does this working with freeradius as well ?
For site to site VPN with shared key, according this post: https://forum.netgate.com/topic/183644/site-to-site-with-shared-key-gateway-bug/3 there is no compatibility if server is V2.6 and client V2.7. Will the SSL/TLS tunnel will work between them ?? i have many 2.6 versions clients to upgrade.
-
@Bambos said in HEADS UP: OpenVPN deprecating shared key mode, requires TLS, deprecating cipher selection:
for the remote access VPN, if is SSL/TLS + User auth, does this working with freeradius as well ?
I'm using FreeRadius myself for the captive portal.
Never tried to do this ...
You probably want also see this one also : FreeRadius on pfSense software for Two Factor Authentication although I presume that article was written for those who wanted to "why do things the easy way if much harder is so much better ?"
@Bambos said in HEADS UP: OpenVPN deprecating shared key mode, requires TLS, deprecating cipher selection:
i have many 2.6 versions clients to upgrade
Keep in mind that 2.6.0 uses the "old" (now completly ditched because of security) OpenVPN (and now also old OpenSSL !!) libaries.
The recent pfSense uses the more modern OpenVPN and OpenSSL.All this means that some options won't work anymore.
Some more options will work, but will be depreciated soon (as usual).
I Use OpenVPN myself, so I always have a look at the "source" : web pages like this and the classic openvpn support forum.The OpenVPN client also changed to support the newer OpenVPN server.
And yes, I agree, syncing the entire openvpn user fleet can be a hassle.
-
 G Gertjan referenced this topic on
G Gertjan referenced this topic on
-
 G Gertjan referenced this topic on
G Gertjan referenced this topic on
-
 G Gertjan referenced this topic on
G Gertjan referenced this topic on