IPsec VTI - no traffic received
-
Hi,
We are migrating to VTI based IPsec, and we are having some issues with the tunnel. Traffic is sent, but no packets are ever received. This is the same on both ends of the tunnel, and both ends are running latest stable pfSense.
Both phase 1 and phase 2 appear to come up correctly. Please see attached screenshot to view the status on the tunnel. Running a packet capture also shows no received packets inside the tunnel.
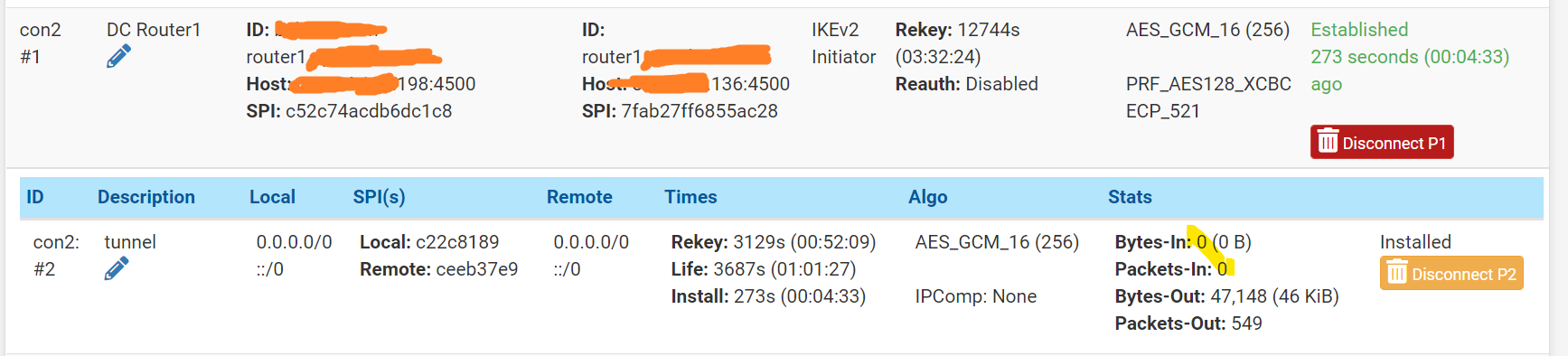
On that screenshot you can also see local and remote as 0.0.0.0/0. I do not get where this comes from, and maybe that is the problem?
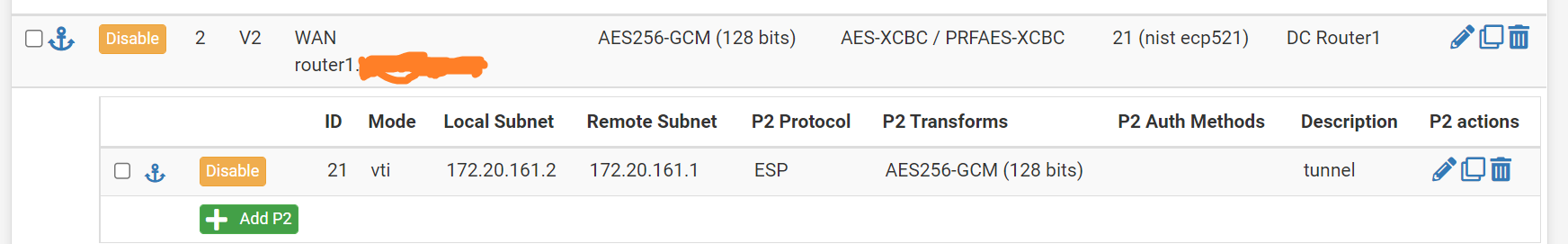
The tunnel configuration only has a single VTI phase 2, but no indication of 0.0.0.0/0. Please see:
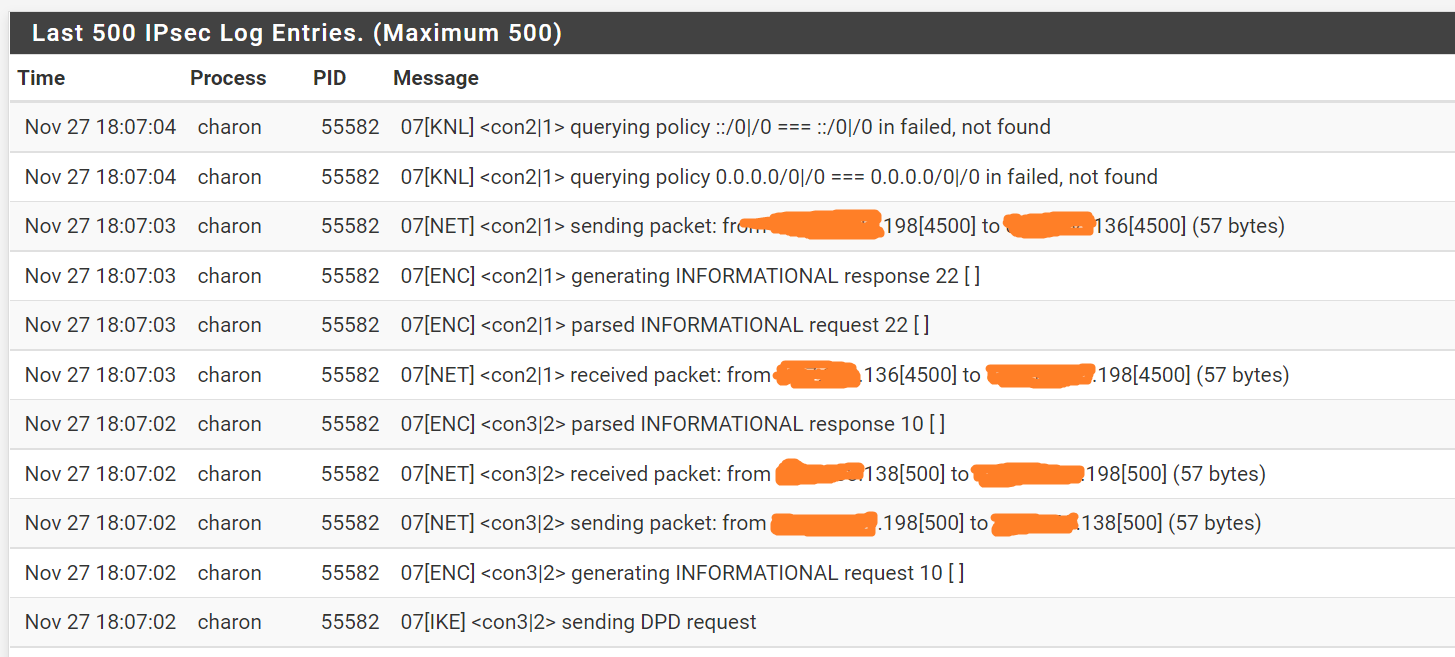
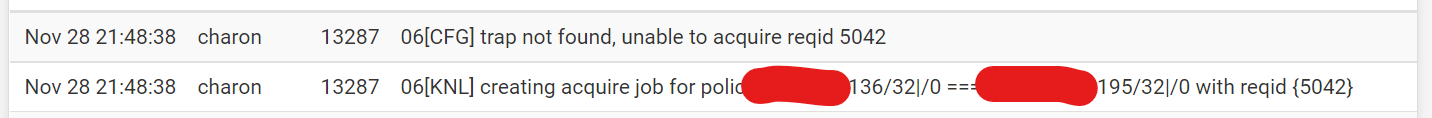
Finally, in the logs, we also see an indication that the 0.0.0.0/0 is causing the problem. Please see:
I cannot find the 0.0.0.0/0 configuration anywhere in the VPN config. Am I missing something, or is the problem really something else?
Hope someone spot the problem.
Thanks,
Christopher -
@dehaas you can disregard the 0.0.0.0/0 entries as they have no bearing. Did you create static routes, or use ospf for example to dynamically create the routes? Did you create appropriate firewall rules in the vti interface tab? Did you create policy based routing rules to specify what subnet or ips use the tunnel?
-
@gabacho4 Hi, thanks for your response. Okay, I will disregard the 0.0.0.0/0 clue. Firewall rules are currently permit any during debugging. Routing is configured using OSPF, but OSPF packages are not received on the remote end. I cannot even ping the remote VTI routing address.
/ Christopher
-
@dehaas can you show the P1 and P2 configuration for both sides please. Also, it appears one or both of your pfsense instances are behind NAT, is the firewall in front of the router(s) set to allow IPSec/other traffic to pass through?
-
@dehaas also, when you are pinging are you pinging from router to router? Or from a computer on one side to the router or network on the other side?
-
@dehaas sorry, did you also go i to the advanced settings on the IPSec tab and set the IPSec filter mode to VTI?
-
@dehaas and lastly, did you create a gateway via the remote IPSec tunnel ip on both ends?
-
@dehaas are your IPSec firewall rules set to permit all protocols?
-
@gabacho4 Hi gabacho,
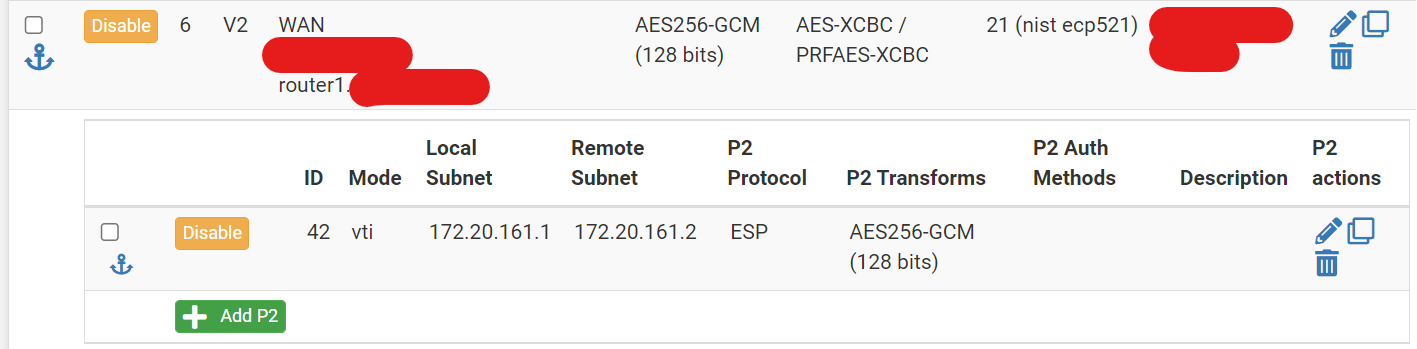
Please find the VPN configuration for the other side here:
I have tried from computer to computer, but since routing information (ospf) is not arriving that does not work. I have tried with static routes instead, but same result. I have also tried router-router ping; nothing arrives.
On both ends, the IPsec Filter Mode is the default options filtering on the ipsec tab.
I have created interfaces and gateways for both ends.
And yes, the current firewall rule is set to allow all protocols. I have also tried with a packet capture, which should show the traffic even if blocked by a firewall rule, but nothing is captured.
/ Christopher
-
@gabacho4 Sorry forgot to answer the NAT question. Neither firewall is behind NAT. They both have public addresses, with no other firewall in front.
/ Christopher
-
@dehaas try changing the filter mode to filter IPSec VTI or are you running traditional IPSec connections as well?
-
@gabacho4 I unfortunately cannot try that, as yes, I am running other traditional IPsec tunnels as well.
-
@dehaas rgr. I wonder if that might be complicating things for you. I’m stumped at this point but would probably try to redo the VTI configuration again for good measure. Your router firewall logs don’t show anything weird going on?
-
I’ve run VTI behind NAT on one end and used ospf to distribute routes so I know for certain you’re not asking it to do more than it can. There’s just gots be something in the config.
-
@gabacho4 I too am a bit stumbled and have tried re-creating the config on both sides out of desperation. Unfortunately, same result. I also do not see anything weird in the logs.
-
@gabacho4 I am seeing this message in the logs a lot. I guess it is related, but not sure how i relates to the configuration I have made.
-
@dehaas sorry for the delayed response. Had to go to bed for the night as it was 2330 were I live. So the one thing I can think of trying is to find time where you can have an outage. Then disable the policy ipsec connections and change that filter setting in the advanced settings. See if your VTI passes traffic at that time. If so, that would suggest that there’s a conflict having both types enabled or the router is getting confused about where to send responses/traffic to. That is the only way really that your config is different than mine. As you said, the IPSec connection appears to be successful, you’re just not getting traffic to pass. I really think somewhere in there the routing is being goofed up.
-
@gabacho4 Hi again. No worries at all, I am just glad you are willing to spend the time trying to help. I have tried disabling the non VTI tunnels on both sides. Unfortunately, that too does not fix the problem. I have checked the routing tables on both sides, and they look right.
-
@dehaas I had similar problems and changing the MTU to 1472 allowed traffic to pass