Please help me oh mighty gods of pfsense and nat reflection
-
here is an update
the pfsense part was quite straightforward, so im positive i managed to do exactly as you suggested.
but the ad part is a little bit off for me..
in ad there is two zones on dns, the direct and reverse, right?... i assuming you told to add in the direct,
but my domain (Active directory domain) is different from the domain used for reaching my firewall from outside and into the nats.
my active directory domain name is only used locally for my network user management. should it be the same?
in that example of mine, my outside domain is mypfsense.com but my active directory domain is something.elsedont really know how to handle that
but lets imagine i make it work at some some point.. then i should use pure nat?
-
@fagoti said in Please help me oh mighty gods of pfsense and nat reflection:
in ad there is two zones on dns, the direct and reverse, right?... i assuming you told to add in the direct,
but my domain (Active directory domain) is different from the domain used for reaching my firewall from outside and into the nats.So you have to add a new zone for your public domain, according your example mypfsense.com.
Then add a host in this zone. For mypfsense.com itself the name should be blank or a dot, not sure. -
oh that i could understand, ok, sucessfully did that, new zone , new host.
but no success on that doing the trick.
i did some testing here ...
i took one of this hosts behind router (192.168 behind a 172.16.200.x) , and assigned to it only my AD dns, and no gateway, and no escape to internet.
i does translate mypfsense.com to the local ip correctly, wich means my ad/dns is doing its job. but it cant use ports with pure nat for some reason, it can only use the (nat + proxy)besides, even if i use the actual ip of the pfsense in the addressbar, with the ports.. it doesnt work with the port set in pure nat, only on the ports with nat + proxy.
and that is a case only for hosts behind routers (using the common 192.168) -
@fagoti i can only think proxy is interfering in some way, and blocking pure nats when source is from different ip class other then his own. because hosts not behind routers, sharing same network manage to access it alright..
-
@fagoti
Ah yes, that's an issue. DNS does not consider your port translations.You can only resolve a single host name to a single IP.
E.g.
host1.mypfsense.com > 172.16.100.11
host2.mypfsense.com > 172.16.100.12So you would need to call host2.mypfsense.com:2222 to get to 172.16.100.12:2222.
i can only think proxy is interfering in some way, and blocking pure nats when source is from different ip class other then his own.
The NAT proxy is out of play with DNS overrides.
-
thats a bummer :(
well, i guess thats thats a way to solve it .maybe i should create and redo all links in that fashion
dont know if im really happy with it, but i think i will start doing it right away, so that really becomes an option.
its sad cause.. it would be fantastic if a single domainlink could work inside and outside my network, always reaching for the pfsense and always getting translated to according port.
but for now i think i gonna stop the efforts.
now im just eager to know why pure nat over proxy still works on the same network but not in the subnetworks routed.....
-
@fagoti
The issue with the NAT reflection, which you described in the first post, may possibly indicate an asymmetric routing issue. But you would have to investigate this.
You can use packet capture on pfSense to check if request and response packets passes pfSense properly. -
@viragomann i will try that, im afraid im not exactly great on that , but im try my best.
as for your suggestion , i just did a sample here, and it works well.. but yes... im gonna have to notify every client, change every link in every station.
and will be exactly like this
host1.mypfsense.com > 172.16.100.11
host2.mypfsense.com > 172.16.100.12the ultimate bummer, is that, one might think it would be really nice to use that oportunity to have outside domainnames that can be typed without the ports and redirected apropriatedly,...
but, if i do that, i will have to use a link for for external (with no ports) and a link for internal (with ports)... and to have 2 links will drive people nuts...so unfortunatelly i will be creating those subdomains with the redirects without ports,, and use the ports in every link so the external and internal links match.
thanks for all your time and attention
greating from brazil!
-
@fagoti
Yes, when using certain ports with NAT reflection, it cannot be simply replaced with DNS overrides.However, there is a simpler method to detect asymmetric routing, assuming the issue concerns to TCP connections:
In Status > System Logs > Settings ensure that "Log packets matched from the default block rules in the ruleset" is enabled.After facing an issue check the firewall log. If you have asymmetric routing you would see block of TCP packets with other than SYN flags, e.g. RA, PA.
-
@fagoti said in Please help me oh mighty gods of pfsense and nat reflection:
active directoty /dns - 172.16.100.1
main local network 172.16.0.0 / 16
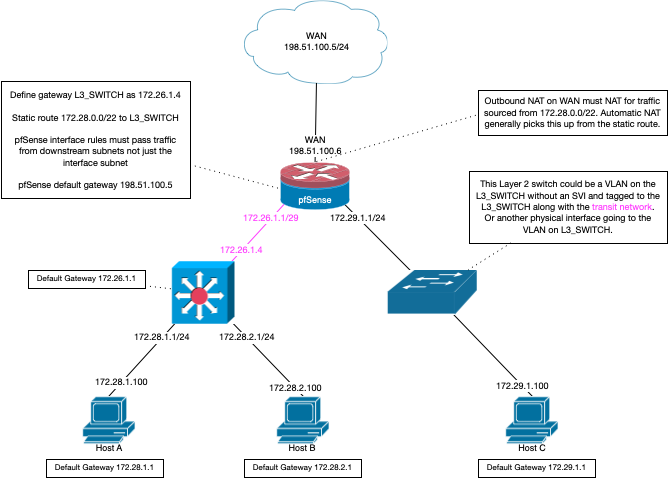
routers 172.16.200.0 / 24Ok this problematic - so your lan is 172.16/16 but you have some other router a 172.16.200/24 - that overlaps.. Can you do a drawing.. If you have a downstream router that really should be on a transit, unless this downstream router is doing nat? if that is the case why would it be on some 172.16.200/24 that overlaps your /16?
-
thanks for trying to help too john,
my lan is indeed /16 and the subclass 200.X is reserved to routers
then , this routers are all 200.x on wan and have dhcp 192.168.x.x for their lan.client 192.168.x.x access without problems servers on 172.16.x.x
but those routers are not using nat of any kind.
-
@fagoti so its really just 172.16/16 your just putting all your routers on 172.16.200/16 range of IPs
but those routers are not using nat of any kind.
That is going to be asymmetrical, if your downstream routers are not doing nat, then that network from your upstream to downstream should be a transit network, no hosts on it..
If I am understanding yoru setup this is asymmetrical.
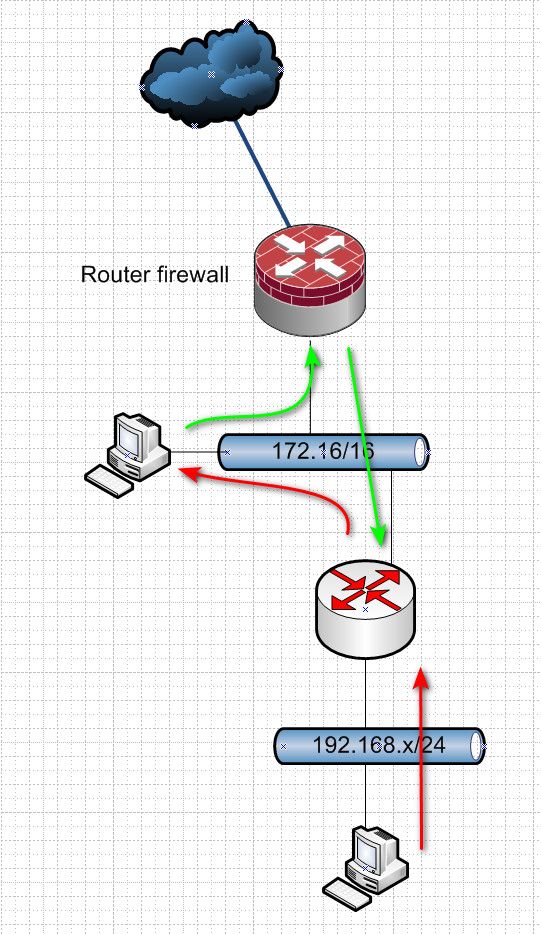
either direction ends up with asymmetrical flow, unless you were doing host routing on the clients on your 172.16/16 network
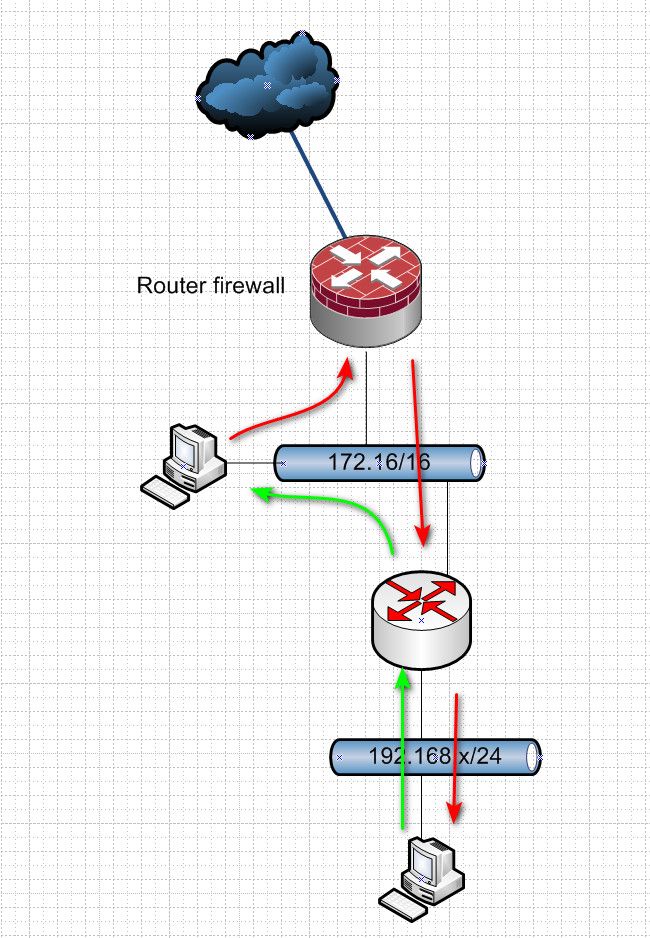
When you use downstream routers that do not nat, you should be using a transit network.
-
@johnpoz oh my, you even made diagrams... :) , thanks again, but now it got a little overwhelmed with that many networks and information
i wont be asking for more until i manage to study this with the same care and fully understand it
but it seems like a lot of changes for my already huge network.
-
@fagoti said in Please help me oh mighty gods of pfsense and nat reflection:
but it seems like a lot of changes for my already huge network.
Creating a transit is not a lot of work.. But running downstream routers that don't nat are going to cause you all kinds of grief without a transit network.. Or doing host routing on ever host..
Transit network is the correct solution..
-
im trying to reply but i keep receiving akismet spam message :/
-
im gonna try breaking my reply in parts
-
It seems you know what you are talking about.
I will give it a shot on a smaller scale here. -
I have just finished doing the "B PLAN" kindly suggested by @viragomann , and its working,
its not pretty, and has lots of places to check when it goes bad,.. but works.
i will be planning how to change all those links for everyone...
but even if i later manage to use your refined transit idea, i can still use those new links i build for split dns, so.. i guess its a good idea to go all the way with it.
-
thanks john
and by the way @viragomann thanks again, because of your quick tip i ended up improving my understanding of my win.dns features.
-
@viragomann i managed to implement a working split dns here. im quite satisfyied.
i still want to test @johnpoz advices. (but its crazy here, i have like 50 routers.. i think it would be a mess to go with it)