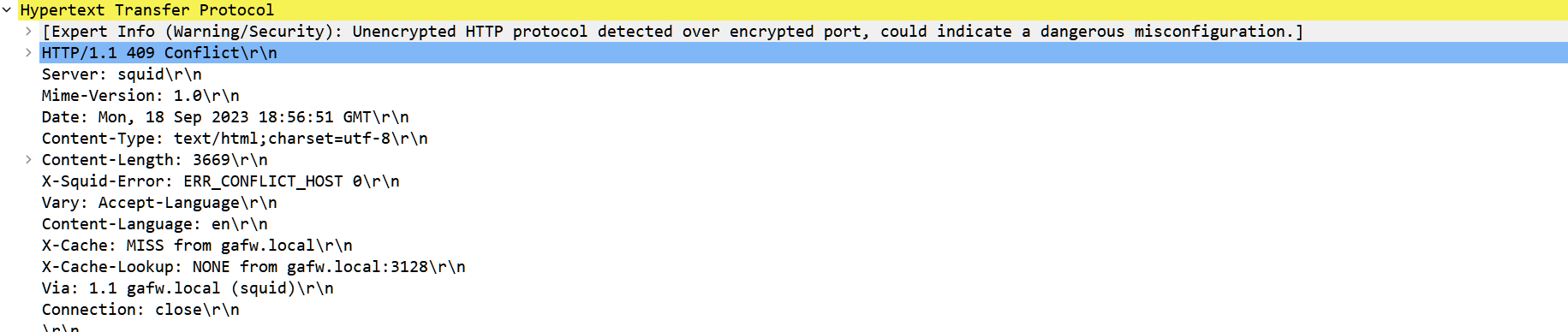
Setting low TTL to fix Squid issue
-
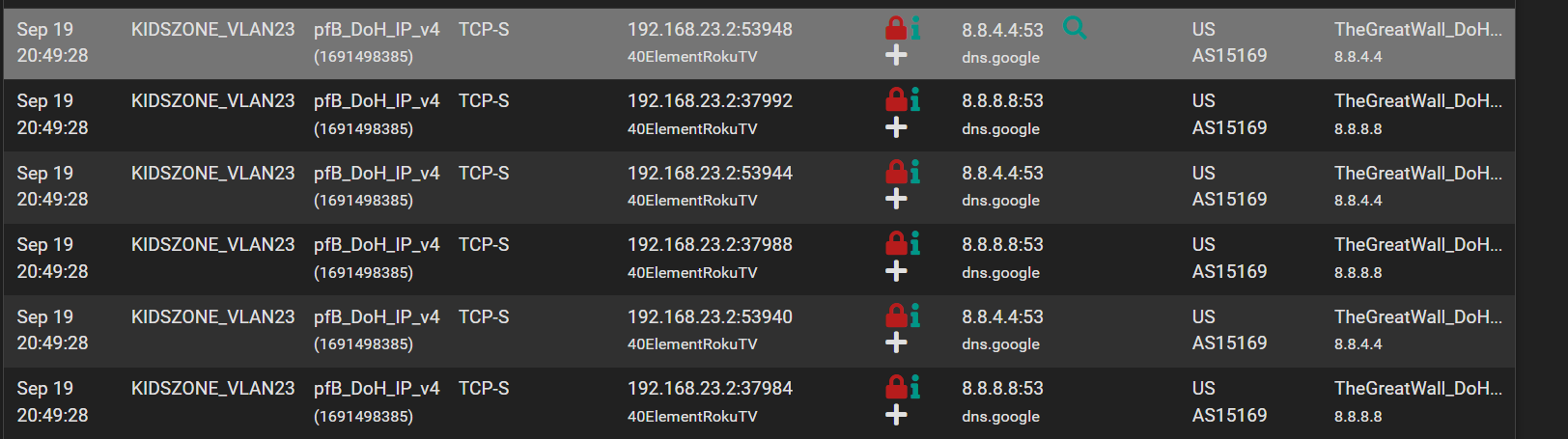
But to my point about devices with hard coded dns servers
Look at this. My IoT television gets its DHCP from my pfsenese. Pfsense hands its IP out as the DNS server yet as you can see from pfblocker its still requesting a google dns.
Its hard coded in a lot of these devices which is an issue but dont think thats why squid breaks.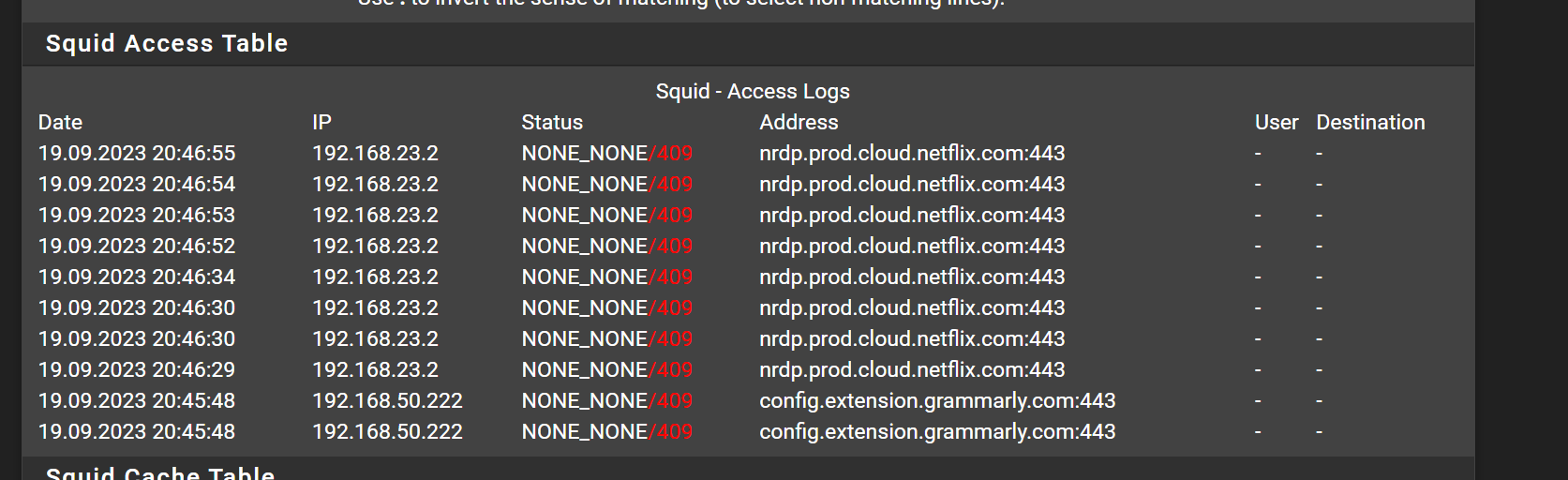
-
-
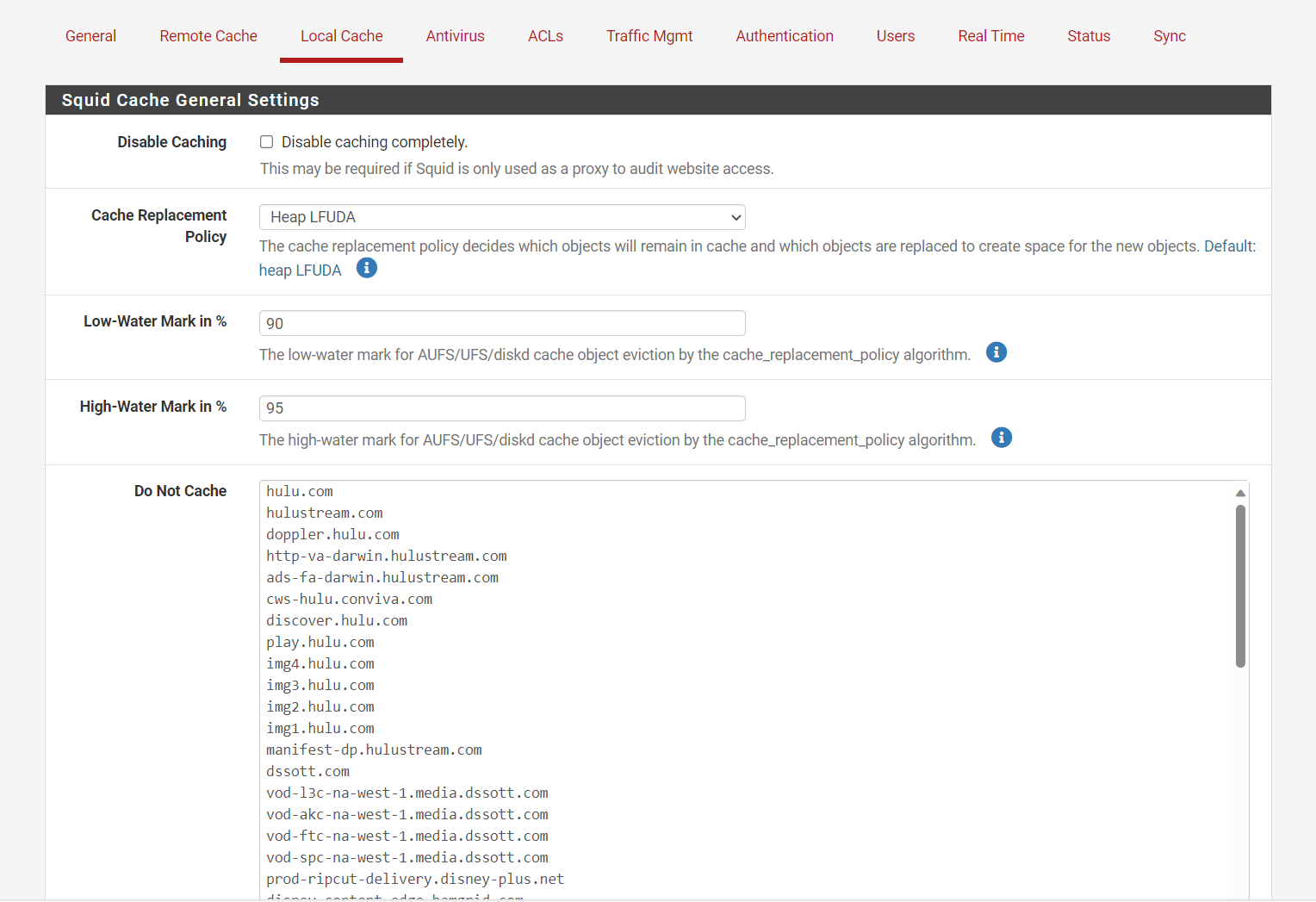
I wanted to check with you on Netflix, I forgot to mention I have Hulu and other streaming services set to no cache. Are you attempting to cache Netflix?
I set them to never cache on Squid
Did you set a NAT for the DNS rules to force all devices to use the firewall?
That should help if you NAT it.
-
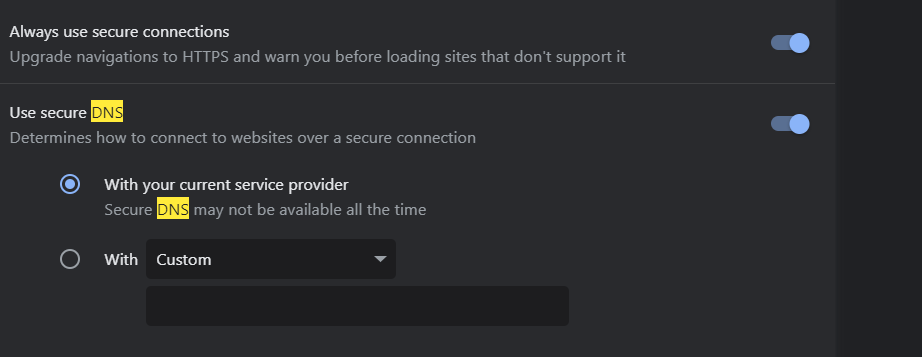
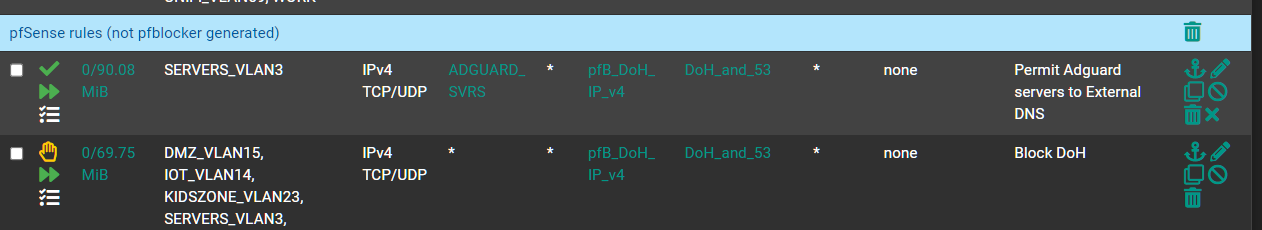
@michmoor Are you blocking port 53 for 8.8.8.8? it shows a red lock, it should only block port 443 for 8.8.8.8, 53 is the standard or if you use dns over tls ssl 853 that might be the issue, TheGreatWall_DoH is blocking standard port 53 over just the 443 DoH access.
Create a NAT rule for all DNS requests that are not being sent to the firewall or it's loopback. And force it to go to the firewall.
-
Interesting conversation here, indeed...thanks for sharing!
-
@JonathanLee
Im blocking 53 and 443
The red lock in pfblocker should indicate that traffic is being blocked - sinkholed so dont think theres any worry about that.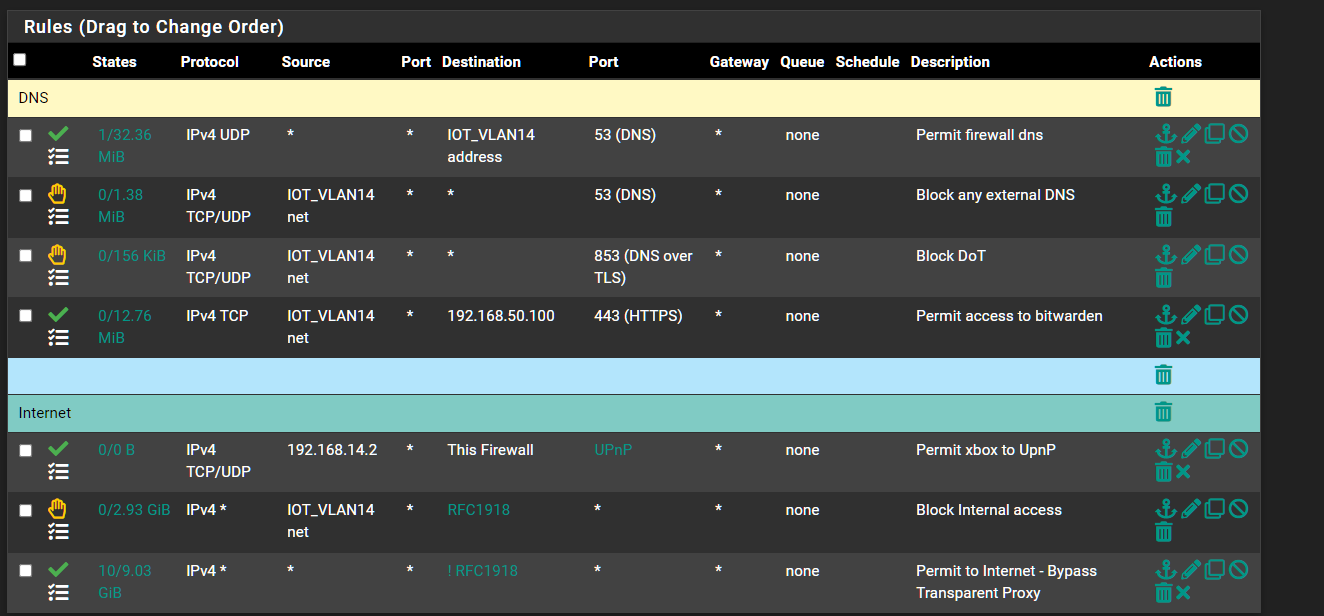
Floating Rule
So in my case theres no reason i can think of to use Port Forards.
-
@michmoor with pfBlocker don't you still need to redirect the clients that are ignoring the DNS settings still? That is interesting, I always have clients that will attempt to use a different DNS all the time with NAT it doesn't matter they go where I configured them too unless they use some new experimental protocol.
-
@JonathanLee I will try adding a nat redirect just to test to see if it makes things better.
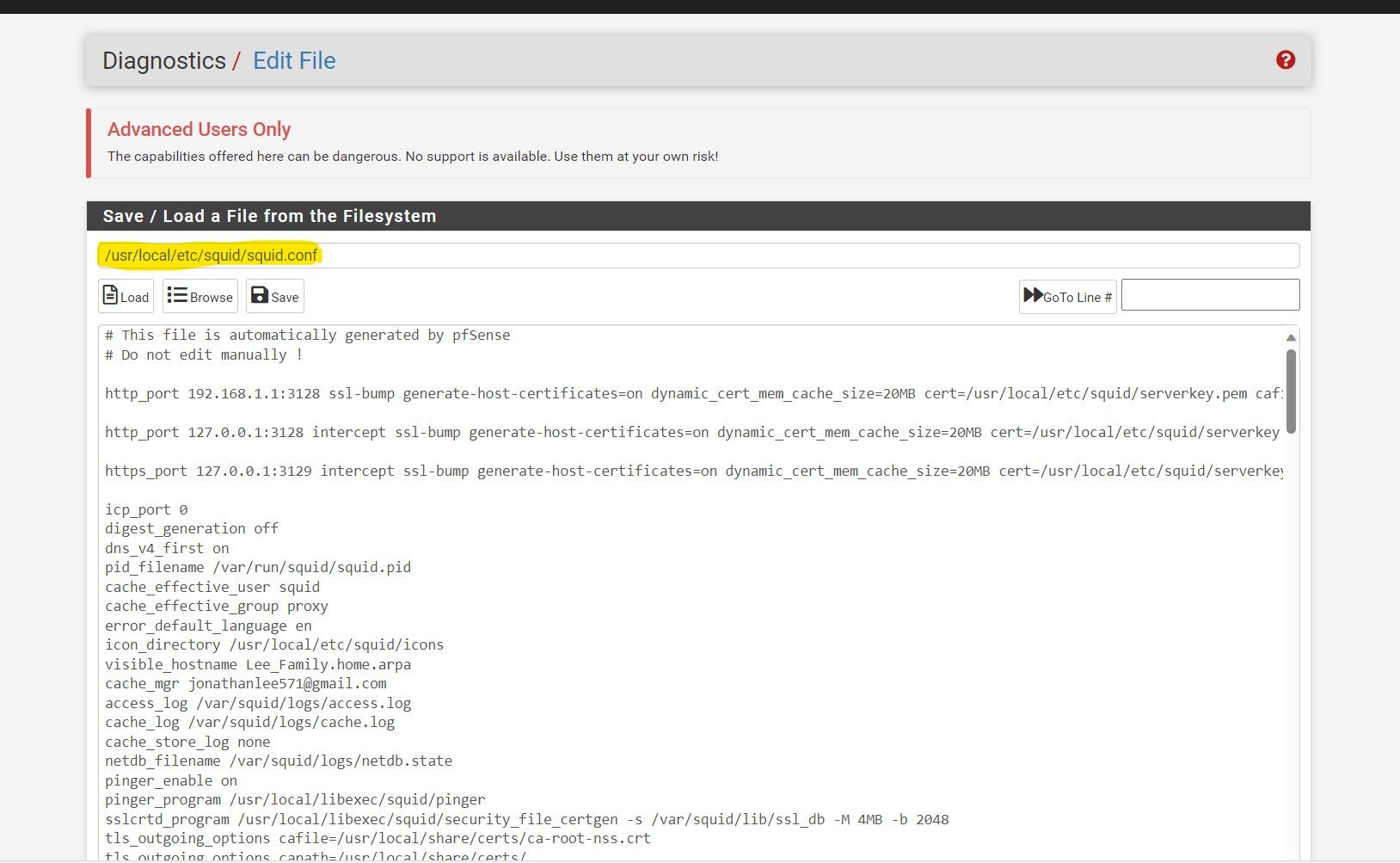
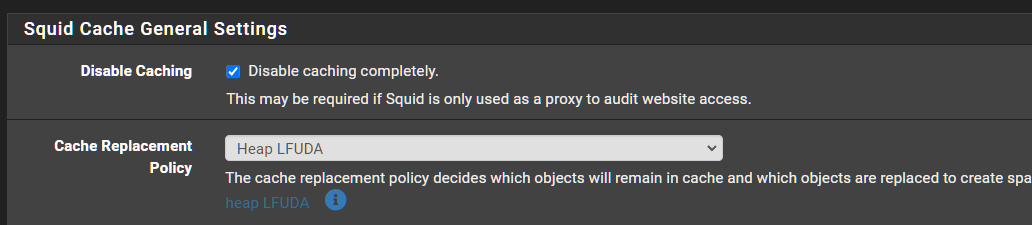
To your other question, i am not using Squid Proxy to cache anything.
-
@michmoor I love the cache I have DSL/ copper it acts as an accelerator
-
@JonathanLee ahhh
Im on 500/500 Fiber.