DNS and ISP provider
-
@The-Party-of-Hell-No If set outgoing interface to lpcal and mullvad in dns resolver internet not working at all
-
@Antibiotic said in DNS and ISP provider:
trying to understand how they are doing this, if me do not use them DNS
because they most likely are intercepting.. Its not difficult, there is a guide on how to do it on pfsense.. Do you not think isp could do such a simple thing.
Quick test just do the dig test to 1.2.3.4, if you get an answer your dns is being intercepting
[23.09.1-RELEASE][admin@sg4860.home.arpa]/root: dig @1.2.3.4 www.cnn.com ;; communications error to 1.2.3.4#53: timed out ;; communications error to 1.2.3.4#53: timed out ;; communications error to 1.2.3.4#53: timed out ; <<>> DiG 9.18.16 <<>> @1.2.3.4 www.cnn.com ; (1 server found) ;; global options: +cmd ;; no servers could be reached [23.09.1-RELEASE][admin@sg4860.home.arpa]/root:If you get a response your being intercepted, there multiple other ways to check, maybe they only intercept specific dns? etc.. but if you get an answer to that query its a smoking gun that upstream of where you doing the query from interception of dns is happening.
-
-
@johnpoz OK, than what to do?
-
@johnpoz said in DNS and ISP provider:
there is a guide on how to do it on pfsense
Could you please give a link? Because did not found any here
-
@Antibiotic
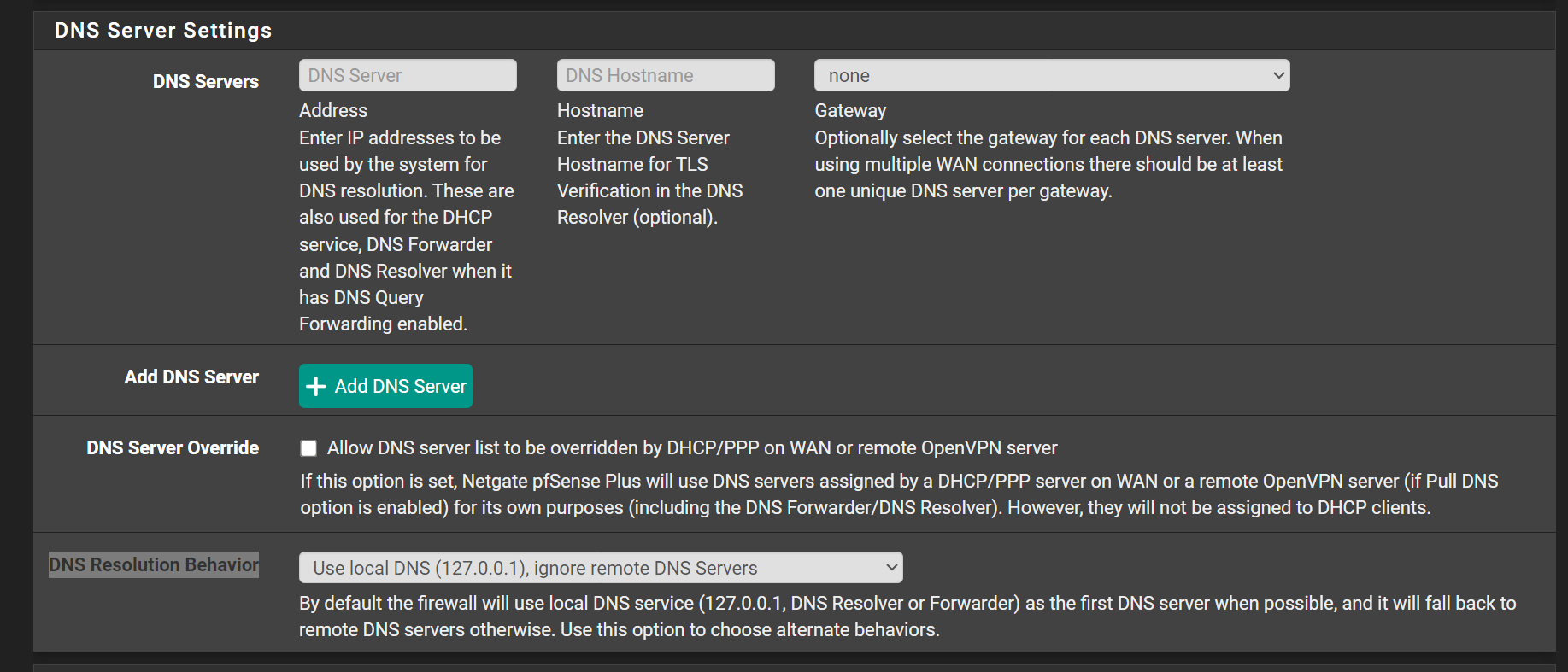
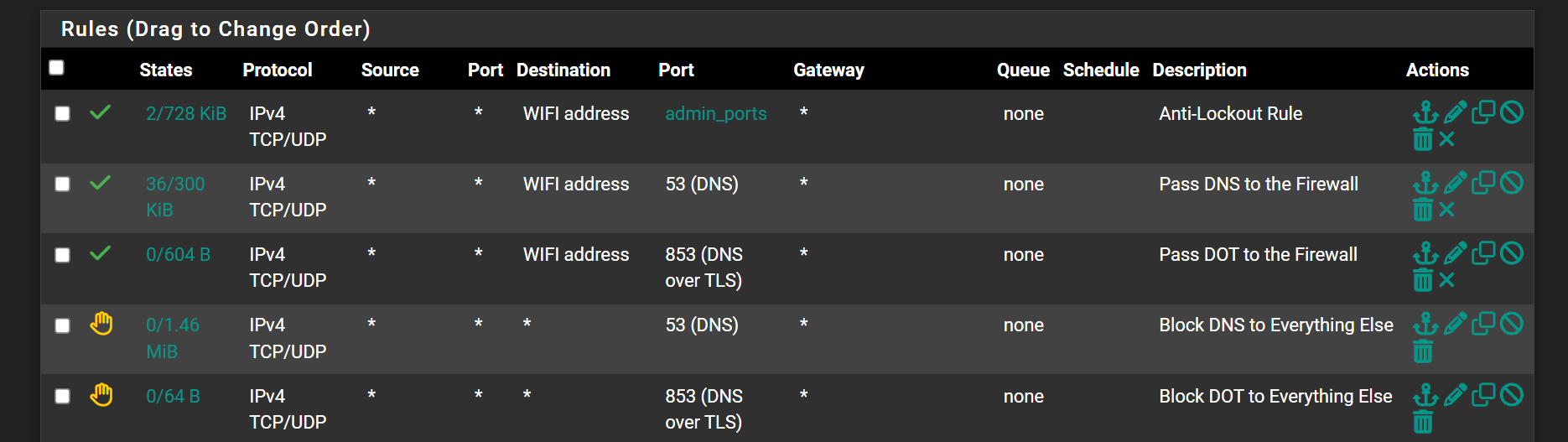
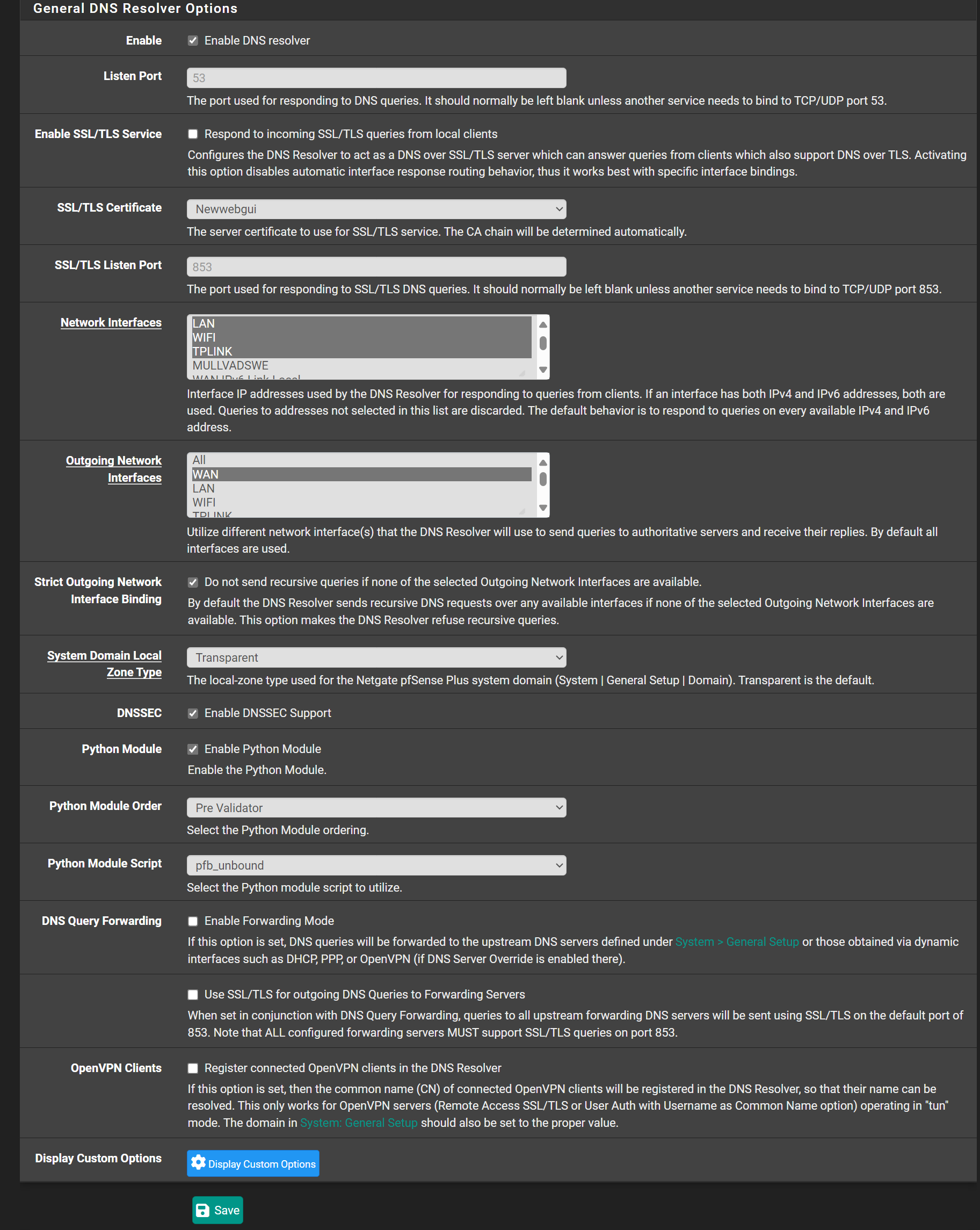
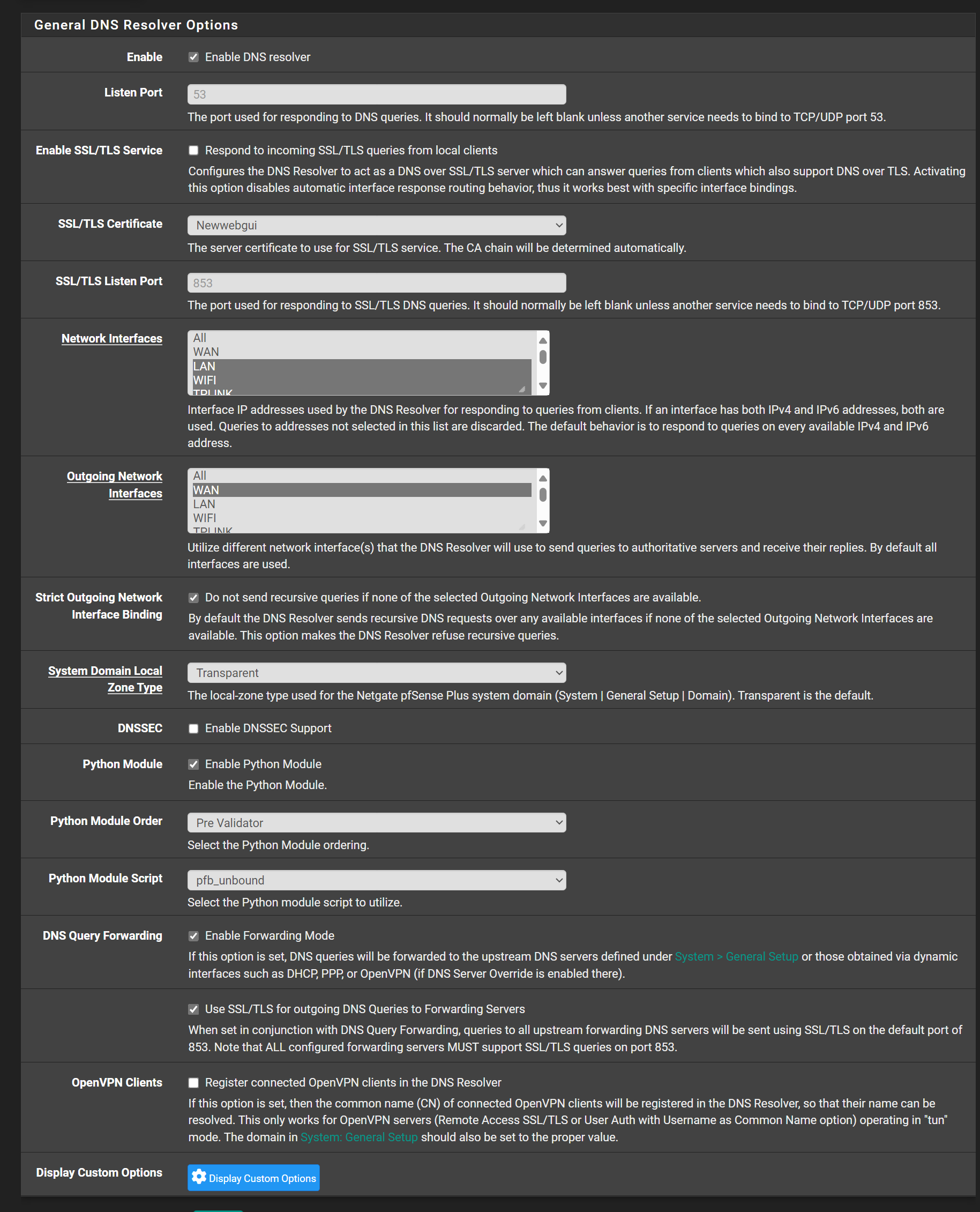
Outgoing Network Interfaces - you still have the WAN highlighted. I don't know if you have the mullvad Interface highlighted. Only the VPN interfaces should be highlighted. Sorry I was calling them gateways should have been using the corrrect terminology - interfaces. -
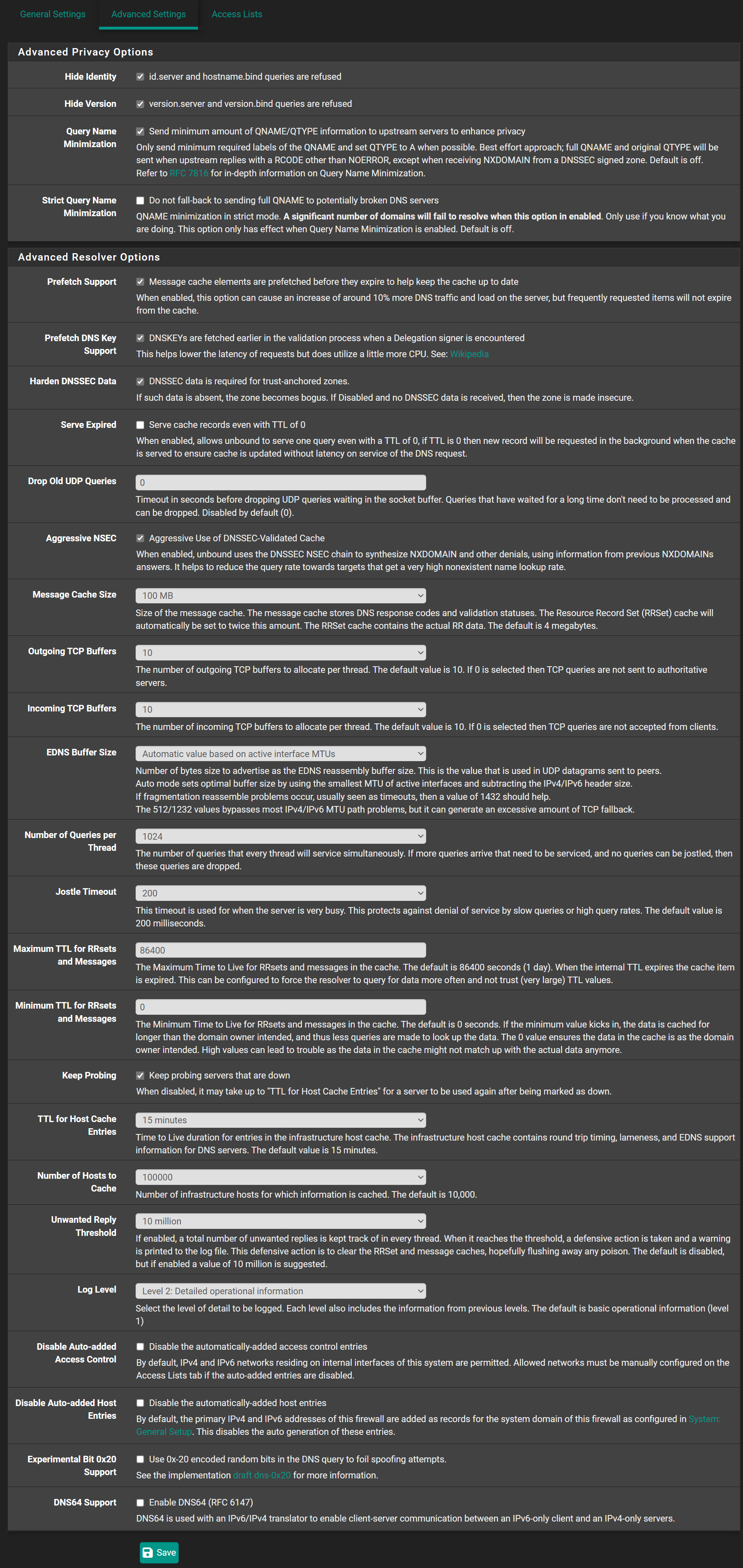
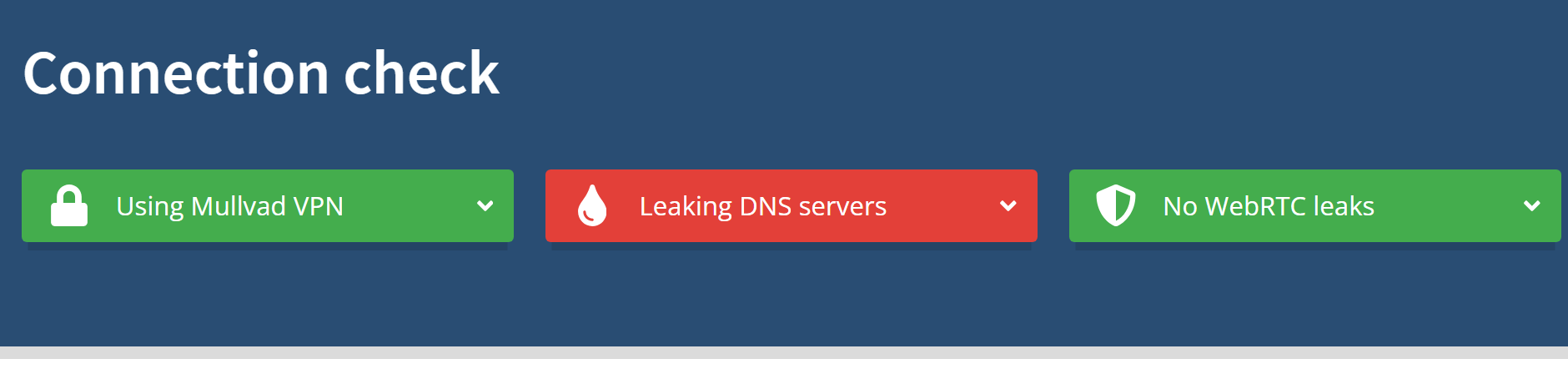
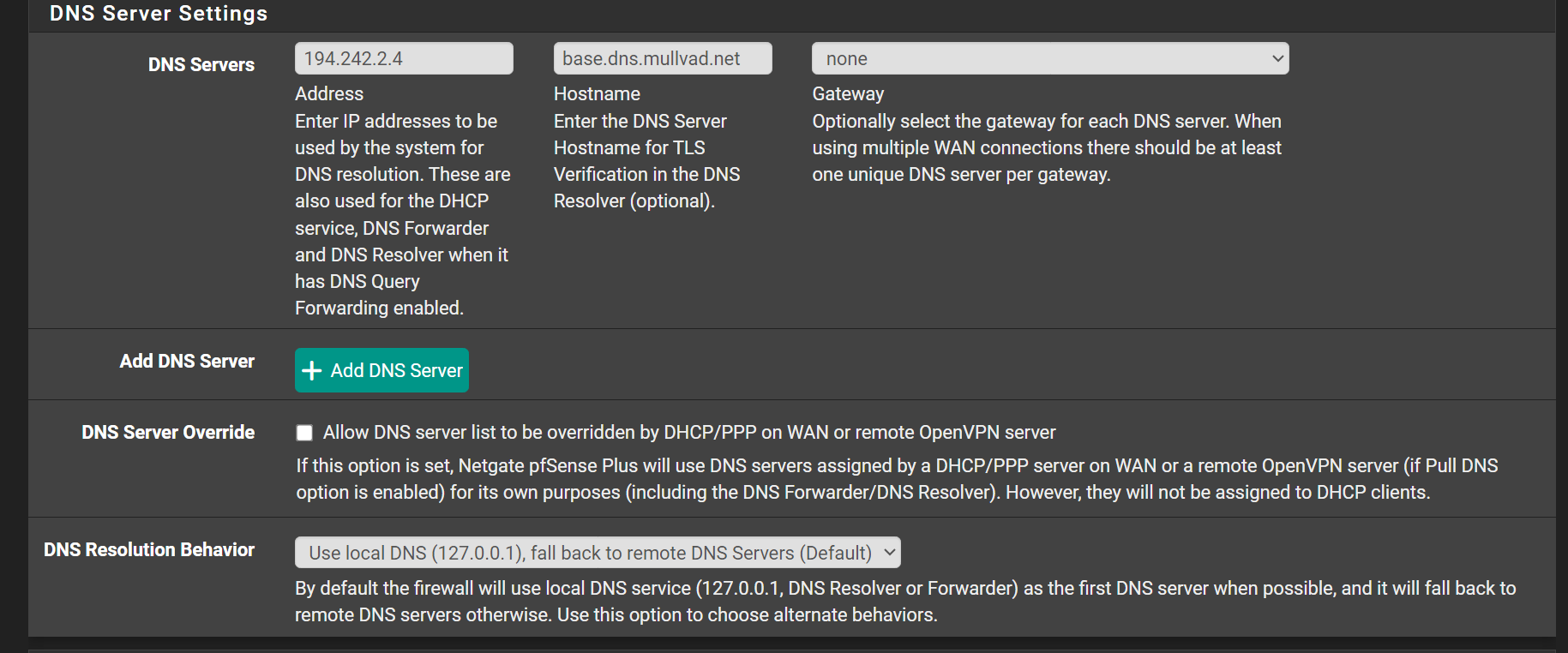
@The-Party-of-Hell-No Yea but me using vpn only for one interface also using other interface without vpn. But anyway after did forwarding to mullvad dns in general setting and set tls over dns. Outgoing IN DNS RESOLVER set to only local Inernet start working.
-
@Antibiotic
You are making progress - I have to post my own difficulties with DNS so I can try and resolve my own thinking.There are ways to make multiple openvpn interfaces and I am sure Mullvad allows this. If it is wireguard you can do that also - just not as easy.
When I made multiple openvpn interfaces I copied the first interface and just changed the "Server Host or Address" to another server provided by the vpn service and save.
Another thing if you want to use both mullvad DNS servers - in case one goes down - just add it as another DNS server. The only time you run into problems if you try to send it out the same gateway. if you do not specify a gateway it will allow you to add the second.
Not sure if this is correct - I wait to be corrected, By only selecting the pfsense dns server 127.0.0.1 if it cannot resolve there is no higher DNS server to refer to.
-
@viragomann said in DNS and ISP provider:
Anyway, I saw a thread here, where an ISP blocked the DNS root servers
Oh, this is answer for blocking, i think
-
@The-Party-of-Hell-No said in DNS and ISP provider:
There are ways to make multiple openvpn interfaces
What the reason? Like a back up server in case main is felt down? But in this case you need all time to make new route to this gateway again?
-
@Antibiotic yeah you can create failover, vpn is just another wan interface as far as pfsense is concerned. So yeah if you loose connectivity to a specific pop you could use another one you have setup.
https://docs.netgate.com/pfsense/en/latest/multiwan/load-balance-and-failover.html
-
@The-Party-of-Hell-No said in DNS and ISP provider:
Another thing if you want to use both mullvad DNS servers - in case one goes down - just add it as another DNS server
They are use anycast, only one is ok. If he is going down the next one close to your location will use!
-
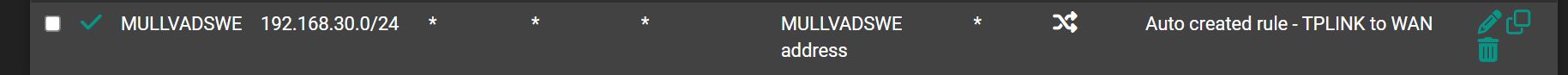
@johnpoz So, I have 3 Nic's and two of them use VPN interface and one use WAN interface. This setting will correct?
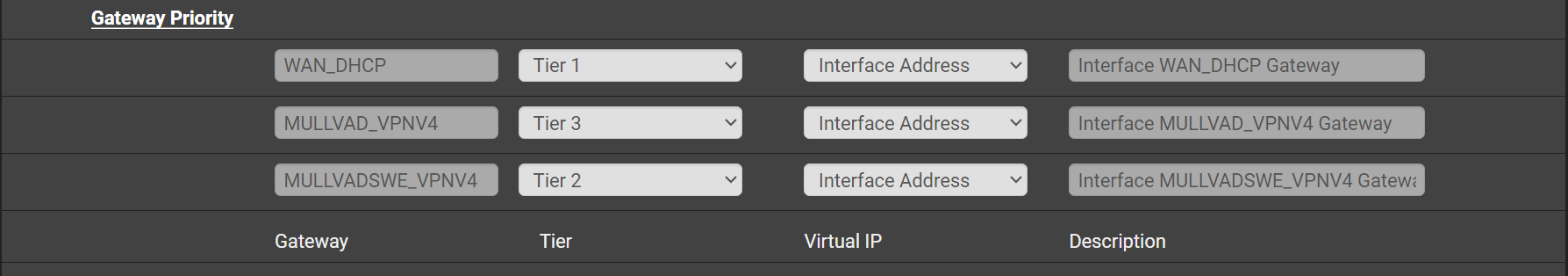
or How to setup only failover for VPN only inetfaces?
adjust WAN to never? But in this case will WAN interface even use for non VPN nic? -
@Antibiotic of the top of my head no that wouldn't be right.. If your going to policy route out some vpn connection(s) those would be your gateway group you setup.. Your normal wan would not be in that group.
-
@johnpoz Misunderstanding, WAN should not appear in group or should set to never?In case set up failover for OpenVPN and second question this spare VPN gateway will route auto, because me set NAT gateway and LAN gateway to first VPN gateway?
-
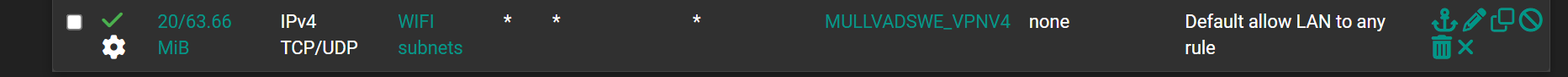
@Antibiotic
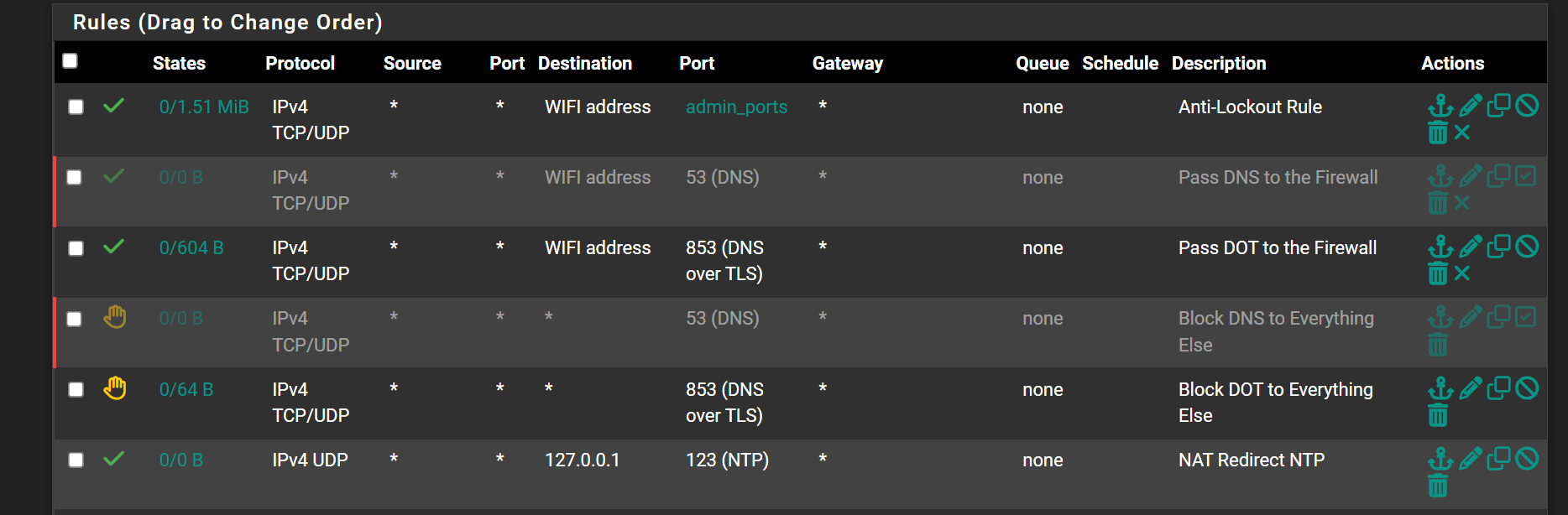
The Wan can be used, however the purpose of the VPN Gateways is to see all traffic is routed out the vpn tunnels. So if this is your intent the WAN_DHCP should be never. Adjust the two VPN's to Tier 1 and Tier 2.When the Gateway Group is created, return to the LAN rules page, go to the bottom to the default allow to any rule. Using the edit button open it up, scroll down and click on the advanced options and scroll down to Gateway, it probably says WAN_DHCP click on the down arrow and select the Gateways Group you created and save. This routes the LAN out the Gateways Group rather than the WAN.
-
@Antibiotic said in DNS and ISP provider:
to be in Europe
Can you be more precise ?
In Europe, there are places where 'entities' intercept DNS. I think about schools, prisons, and some hotel owners using pfSense
All the other can not exist, as no one would chose them as an ISP.
And a VPN ISP is yet another ISP like supplier. -
@Gertjan In Europe. it mean me like a simple user at home whom censuring simple city ISP according simple stupid goverment
-
If your ISP is intercepting / doing things with your DNS traffic, then you have a good reason to use a VPN, or DNS Forward over TLS.
But, because it's Europe, I wouldn't be a client of this ISP in the first place.
-
@Gertjan MullvadVPN fine for privacy, I do not like VPN whom belong to KAPE alienses, like ExpressVPN for example