@JeGr said in Can/is Snort using JA3 hashes?:
@bmeeks said in Can/is Snort using JA3 hashes?:
If JA3 support is critical to your customer, perhaps Suricata might be a better fit for them ???
That was the answer I was looking for. As Surricata didn't have (or still don't?) support for OpenAppID rules we set up Snort at the time in the past as the Netgate blog about support for OpenAppID was posted. The request about JA3 popped out of nowhere a few days ago so if that's something they absolutely want - then yes, we'd have to switch. Would take time though to test it out first, roll out on the cluster and train the team using it that is currently struggling coming to terms with Snort.
There are other options depending on their requirements. For instance, if they simply wanted to monitor/alert on JA3 hashes and not block, they could install Suricata on a separate machine (bare metal or VM) and connect it to a SPAN port on a managed switch.
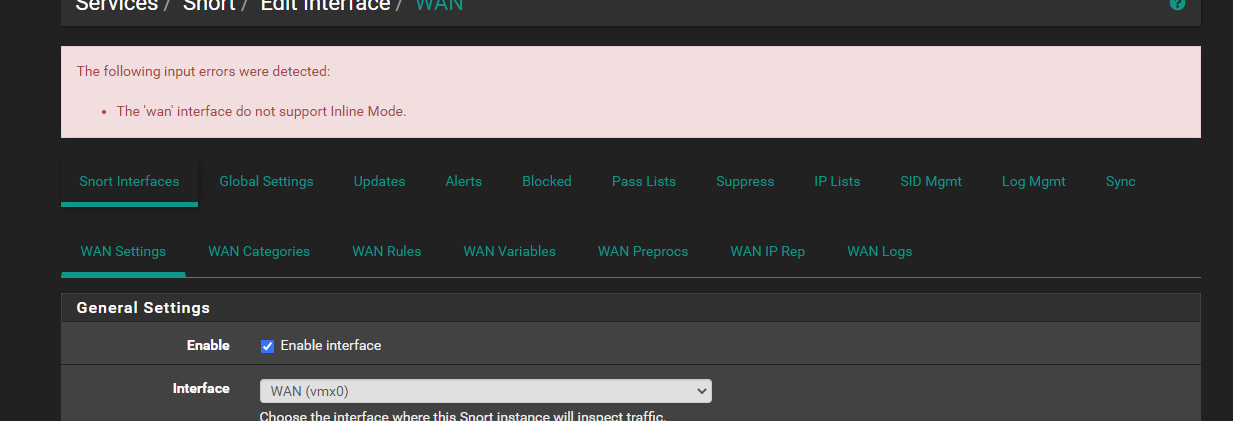
If you don't have both packages blocking in Legacy Blocking Mode, and you have the CPU horsepower and RAM, it is certainly possible to run both packages on the same pfSense instance. In that case you would run Suricata with a very stripped-down rule set concentrating solely on the JA3 hashing stuff. So in a setup like this you might configure Snort to use Inline IPS Mode (assuming your NIC hardware supports it) and Suricata to use Legacy Blocking. Or you could flip that scenario. The only caveat here is that you can't run Inline Mode and Legacy Blocking Mode on the same physical interface. So you would need to monitor the traffic on another matching interface. For example, Suricata JA3 on WAN and Snort OpenAppID on LAN (or vice versa). You could always run one in alert-only mode and the other package in blocking mode.
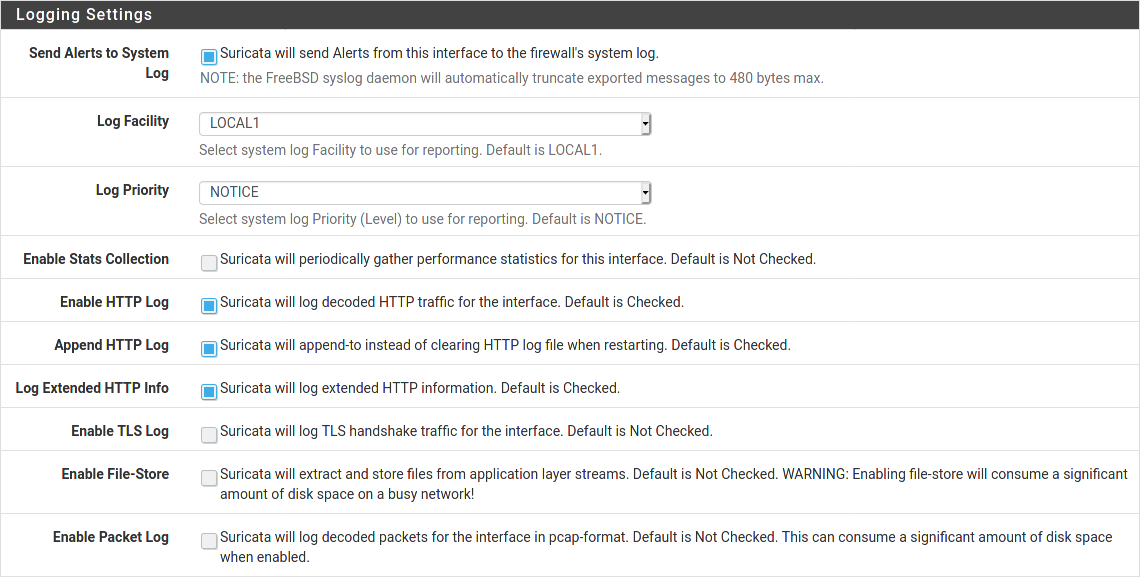
Functionally within the GUI, both packages are very, very similar. In fact, the majority of the Suricata PHP code is a copy-and-paste from the Snort GUI code. So the look and feel is the same.