Major DNS Bug 23.01 with Quad9 on SSL
-
I don't know why the timestamp in logs is broken, loglevel is 4. The log looks inconsistent and not full also, like it was interrupted and continiued.
I'm not sure if something in the log is wrong or out of the ordinary, so I don't have enough knowledge, but it looks like nothing happened except the time stamp is broken...Apr 19 00:02:59 unbound 51656 [51656:1] debug: comm point listen_for_rw 30 0 Apr 19 00:02:59 unbound 51656 [51656:1] debug: comm point start listening 30 (-1 msec) Apr 19 00:02:59 unbound 51656 [51656:1] debug: the query is using TLS encryption, for dns.google Apr 19 00:02:59 unbound 51656 [51656:1] debug: tcp bound to src ip4 84.52.23.160 port 0 (len 16) Apr 19 00:02:59 unbound 51656 [51656:1] debug: serviced send timer Apr 19 00:02:59 unbound 51656 [51656:1] debug: cache memory msg=91674 rrset=125505 infra=7808 val=0 Apr 19 00:02:59 unbound 51656 [51656:1] info: 0RDd mod1 rep feodotracker.abuse.ch. AAAA IN Apr 19 00:02:59 unbound 51656 [51656:1] info: mesh_run: end 1 recursion states (1 with reply, 0 detached), 1 waiting replies, 0 recursion replies sent, 0 replies dropped, 0 states jostled out Apr 19 00:02:59 unbound 51656 [51656:1] debug: mesh_run: iterator module exit state is module_wait_reply Apr 19 00:02:59 unbound 51656 [51656:1] debug: dnssec status: not expected Apr 19 00:02:59 unbound 51656 [51656:1] debug: sending to target: <.> 8.8.8.8#853 Apr 19 00:02:59 unbound 51656 [51656:1] info: sending query: p2.shared.global.fastly.net. AAAA IN Apr 19 00:02:59 unbound 51656 [51656:1] debug: selrtt 376 Apr 19 00:02:59 unbound 51656 [51656:1] debug: rpz: iterator module callback: have_rpz=0 Apr 19 00:02:59 unbound 51656 [51656:1] debug: attempt to get extra 3 targets Apr 19 00:02:59 unbound 51656 [51656:1] debug: [cloudflare-dns.com] ip4 1.1.1.1 port 853 (len 16) Apr 19 00:02:59 unbound 51656 [51656:1] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1111 port 853 (len 28) Apr 19 00:02:59 unbound 51656 [51656:1] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1001 port 853 (len 28) Apr 19 00:02:59 unbound 51656 [51656:1] debug: [cloudflare-dns.com] ip4 1.0.0.1 port 853 (len 16) Apr 19 00:02:59 unbound 51656 [51656:1] debug: [dns.google] ip4 8.8.8.8 port 853 (len 16) Apr 19 00:02:59 unbound 51656 [51656:1] debug: [dns.google] ip4 8.8.4.4 port 853 (len 16) Apr 19 00:02:59 unbound 51656 [51656:1] debug: [dns.google] ip6 2001:4860:4860::8888 port 853 (len 28) Apr 19 00:02:59 unbound 51656 [51656:1] debug: [dns.google] ip6 2001:4860:4860::8844 port 853 (len 28) Apr 19 00:02:59 unbound 51656 [51656:1] info: DelegationPoint<.>: 0 names (0 missing), 8 addrs (0 result, 8 avail) parentNS Apr 19 00:02:59 unbound 51656 [51656:1] debug: processQueryTargets: targetqueries 0, currentqueries 0 sentcount 0 Apr 19 00:02:59 unbound 51656 [51656:1] info: processQueryTargets: feodotracker.abuse.ch. AAAA IN Apr 19 00:02:59 unbound 51656 [51656:1] debug: iter_handle processing q with state QUERY TARGETS STATE Apr 19 00:02:59 unbound 51656 [51656:1] debug: forwarding request Apr 19 00:02:59 unbound 51656 [51656:1] debug: request has dependency depth of 0 Apr 19 00:02:59 unbound 51656 [51656:1] info: resolving feodotracker.abuse.ch. AAAA IN Apr 19 00:02:59 unbound 51656 [51656:1] debug: iter_handle processing q with state INIT REQUEST STATE Apr 19 00:02:59 unbound 51656 [51656:1] debug: returning CNAME response from cache Apr 19 00:02:59 unbound 51656 [51656:1] debug: msg ttl is 1026, prefetch ttl 924 Apr 19 00:02:59 unbound 51656 [51656:1] info: msg from cache lookup ;; ->>HEADER<<- opcode: QUERY, rcode: NOERROR, id: 0 ;; flags: qr ; QUERY: 1, ANSWER: 3, AUTHORITY: 0, ADDITIONAL: 0 ;; QUESTION SECTION: feodotracker.abuse.ch. IN AAAA ;; ANSWER SECTION: feodotracker.abuse.ch. 1026 IN CNAME p2.shared.global.fastly.net. feodotracker.abuse.ch. 1026 IN RRSIG CNAME 5 3 60 20230504155253 20230404155253 12765 abuse.ch. N2C1reBZgD3r15ldnR/wDqmbYumI2kEgDGvbTqCgWKsa82Ds9TZUN/T4SlUmC5W6HsGD7QyZZHTjygXwlDETvnhImYl9SDZgtePRinjnfjinFthzcpTVEVGxtXCLIYOqCATAUwZotkKGtUE1u4aVqkArtSADJYpnk+MQPuYmrS7FEPxILrwoSDFryA8Lpdv3ut3+UzATfqbrB7W+P5qYdel/ODEjJozdOkK2PrmhiYp2uHXj5qicxZiPMuytjKhMmLwXBXQlNA4s2o4KFAYcHf7X4M+W3H/JFoCHIRfl28yZPqcWY6mjAkLpxa2SVcFI39zadQyf513ed+LMsFypng== ;{id = 12765} feodotracker.abuse.ch. 1026 IN RRSIG CNAME 14 3 60 20230514214831 20230414214831 45114 abuse.ch. RHzCfLewwoSmpqmk5cwhrG7bOiAP0HHpAx3AP/R0iUBAsaeF6ISc7/Nz/nIq+w6luZX9vypQgACpR++woKFWQO/+/M6cBBWkJN1HAMl14qNZ0brKxvNaBFRE4eN5Caog ;{id = 45114} ;; AUTHORITY SECTION: ;; ADDITIONAL SECTION: ;; MSG SIZE rcvd: 512 Apr 19 00:02:59 unbound 51656 [51656:1] debug: request has dependency depth of 0 Apr 19 00:02:59 unbound 51656 [51656:1] info: resolving feodotracker.abuse.ch. AAAA IN Apr 19 00:02:59 unbound 51656 [51656:1] debug: iter_handle processing q with state INIT REQUEST STATE Apr 19 00:02:59 unbound 51656 [51656:1] debug: process_request: new external request event Apr 19 00:02:59 unbound 51656 [51656:1] debug: iterator[module 1] operate: extstate:module_state_initial event:module_event_pass Apr 19 00:02:59 unbound 51656 [51656:1] debug: mesh_run: python module exit state is module_wait_module Apr 19 00:02:59 unbound 51656 [51656:1] debug: mesh_run: start Apr 19 00:02:59 unbound 51656 [51656:1] info: receive_udp on interface: 127.0.0.1 Apr 19 00:02:59 unbound 51656 [51656:2] info: send_udp over interface: 127.0.0.1 Apr 19 00:02:59 unbound 51656 [51656:2] info: receive_udp on interface: 127.0.0.1 Apr 19 00:02:59 unbound 51656 [51656:2] info: send_udp over interface: 192.168.77.5 Apr 19 00:02:59 unbound 51656 [51656:2] info: receive_udp on interface: 192.168.77.5 Apr 19 00:02:59 unbound 51656 [51656:0] info: send_udp over interface: 192.168.77.5 Apr 19 00:02:59 unbound 51656 [51656:0] info: receive_udp on interface: 192.168.77.5 Apr 19 00:02:57 unbound 51656 [51656:0] debug: close fd 30 Apr 19 00:02:57 unbound 51656 [51656:0] debug: remote control operation completed Apr 19 00:02:57 unbound 51656 [51656:0] info: control cmd: load_cache Apr 19 00:02:57 unbound 51656 [51656:0] debug: remote control connection authenticated Apr 19 00:02:57 unbound 51656 [51656:0] debug: comm point start listening 30 (120000 msec) Apr 19 00:02:57 unbound 51656 [51656:0] debug: comm point stop listening 30 Apr 19 00:02:57 unbound 51656 [51656:0] debug: new control connection from ip4 127.0.0.1 port 34952 (len 16) Apr 19 00:02:57 unbound 51656 [51656:0] debug: close fd 30 Apr 19 00:02:57 unbound 51656 [51656:0] debug: remote control operation completed Apr 19 00:02:57 unbound 51656 [51656:0] info: control cmd: status Apr 19 00:02:57 unbound 51656 [51656:0] debug: remote control connection authenticated Apr 19 00:02:57 unbound 51656 [51656:2] debug: cache memory msg=66072 rrset=66072 infra=7808 val=0 Apr 19 00:02:57 unbound 51656 [51656:2] debug: no config, using builtin root hints. Apr 19 00:02:57 unbound 51656 [51656:1] debug: cache memory msg=66072 rrset=66072 infra=7808 val=0 Apr 19 00:02:57 unbound 51656 [51656:1] debug: no config, using builtin root hints. Apr 19 00:02:57 unbound 51656 [51656:2] debug: [dns.google] ip6 2001:4860:4860::8844 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:2] debug: [dns.google] ip6 2001:4860:4860::8888 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:2] debug: [dns.google] ip4 8.8.4.4 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:2] debug: [dns.google] ip4 8.8.8.8 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:2] debug: [cloudflare-dns.com] ip4 1.0.0.1 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:2] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1001 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:2] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1111 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:2] debug: [cloudflare-dns.com] ip4 1.1.1.1 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:2] info: DelegationPoint<.>: 0 names (0 missing), 8 addrs (0 result, 8 avail) parentNS Apr 19 00:02:57 unbound 51656 [51656:2] debug: Forward zone server list: Apr 19 00:02:57 unbound 51656 [51656:1] debug: [dns.google] ip6 2001:4860:4860::8844 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:1] debug: [dns.google] ip6 2001:4860:4860::8888 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:1] debug: [dns.google] ip4 8.8.4.4 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:1] debug: [dns.google] ip4 8.8.8.8 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:1] debug: [cloudflare-dns.com] ip4 1.0.0.1 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:1] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1001 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:1] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1111 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:3] debug: cache memory msg=66072 rrset=66072 infra=7808 val=0 Apr 19 00:02:57 unbound 51656 [51656:3] debug: no config, using builtin root hints. Apr 19 00:02:57 unbound 51656 [51656:3] debug: [dns.google] ip6 2001:4860:4860::8844 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:3] debug: [dns.google] ip6 2001:4860:4860::8888 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:3] debug: [dns.google] ip4 8.8.4.4 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:3] debug: [dns.google] ip4 8.8.8.8 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:3] debug: [cloudflare-dns.com] ip4 1.0.0.1 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:3] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1001 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:3] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1111 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:3] debug: [cloudflare-dns.com] ip4 1.1.1.1 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:3] info: DelegationPoint<.>: 0 names (0 missing), 8 addrs (0 result, 8 avail) parentNS Apr 19 00:02:57 unbound 51656 [51656:3] debug: Forward zone server list: Apr 19 00:02:57 unbound 51656 [51656:1] debug: [cloudflare-dns.com] ip4 1.1.1.1 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:1] info: DelegationPoint<.>: 0 names (0 missing), 8 addrs (0 result, 8 avail) parentNS Apr 19 00:02:57 unbound 51656 [51656:1] debug: Forward zone server list: Apr 19 00:02:57 unbound 51656 [51656:0] debug: comm point start listening 30 (120000 msec) Apr 19 00:02:57 unbound 51656 [51656:0] debug: comm point stop listening 30 Apr 19 00:02:57 unbound 51656 [51656:0] debug: new control connection from ip4 127.0.0.1 port 31664 (len 16) Apr 19 00:02:57 unbound 51656 [51656:0] info: start of service (unbound 1.17.1). Apr 19 00:02:57 unbound 51656 [51656:0] debug: cache memory msg=66072 rrset=66072 infra=7808 val=0 Apr 19 00:02:57 unbound 51656 [51656:0] debug: no config, using builtin root hints. Apr 19 00:02:57 unbound 51656 [51656:0] debug: [dns.google] ip6 2001:4860:4860::8844 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:0] debug: [dns.google] ip6 2001:4860:4860::8888 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:0] debug: [dns.google] ip4 8.8.4.4 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:0] debug: [dns.google] ip4 8.8.8.8 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:0] debug: [cloudflare-dns.com] ip4 1.0.0.1 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:0] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1001 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:0] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1111 port 853 (len 28) Apr 19 00:02:57 unbound 51656 [51656:0] debug: [cloudflare-dns.com] ip4 1.1.1.1 port 853 (len 16) Apr 19 00:02:57 unbound 51656 [51656:0] info: DelegationPoint<.>: 0 names (0 missing), 8 addrs (0 result, 8 avail) parentNS Apr 19 00:02:57 unbound 51656 [51656:0] debug: Forward zone server list: Apr 19 00:02:57 unbound 51656 [51656:3] debug: libevent 2.1.12-stable uses kqueue method. Apr 19 00:02:57 unbound 51656 [51656:2] debug: libevent 2.1.12-stable uses kqueue method. Apr 19 00:02:57 unbound 51656 [51656:1] debug: libevent 2.1.12-stable uses kqueue method. Apr 19 00:02:57 unbound 51656 [51656:0] debug: libevent 2.1.12-stable uses kqueue method. Apr 19 00:02:57 unbound 51656 [51656:0] debug: start threads Apr 19 00:02:57 unbound 51656 [51656:0] debug: total of 59448 outgoing ports available Apr 19 00:02:57 unbound 51656 [51656:0] debug: donotq: ::1 Apr 19 00:02:57 unbound 51656 [51656:0] debug: donotq: 127.0.0.0/8 Apr 19 00:02:57 unbound 51656 [51656:0] debug: target fetch policy for level 4 is 0 Apr 19 00:02:57 unbound 51656 [51656:0] debug: target fetch policy for level 3 is 0 Apr 19 00:02:57 unbound 51656 [51656:0] debug: target fetch policy for level 2 is 1 Apr 19 00:02:57 unbound 51656 [51656:0] debug: target fetch policy for level 1 is 2 Apr 19 00:02:57 unbound 51656 [51656:0] debug: target fetch policy for level 0 is 3 Apr 19 00:02:57 unbound 51656 [51656:0] notice: init module 1: iterator Apr 19 00:02:57 unbound 51656 [51656:0] info: [pfBlockerNG]: init_standard script loaded Apr 19 00:02:53 unbound 51656 [51656:0] info: [pfBlockerNG]: pfb_unbound.py script loaded Apr 19 00:02:53 unbound 51656 [51656:0] notice: init module 0: python Apr 19 00:02:53 unbound 51656 [51656:0] debug: module config: "python iterator" Apr 19 00:02:53 unbound 51656 [51656:0] debug: ignoring duplicate RR: localhost. A 127.0.0.1 Apr 19 00:02:53 unbound 51656 [51656:0] debug: ignoring duplicate RR: localhost. AAAA ::1 Apr 19 00:02:53 unbound 51656 [51656:0] info: implicit transparent local-zone int. TYPE0 IN Apr 19 00:02:53 unbound 51656 [51656:0] debug: duplicate acl address ignored. Apr 19 00:02:53 unbound 51656 [51656:0] debug: drop user privileges, run as unbound Apr 19 00:02:53 unbound 51656 [51656:0] debug: chroot to /var/unbound Apr 19 00:02:53 unbound 51656 [51656:0] debug: chdir to /var/unbound Apr 18 19:01:42 unbound 72249 [72249:1] debug: comm point listen_for_rw 31 0 Apr 18 19:01:42 unbound 72249 [72249:1] debug: comm point start listening 31 (-1 msec) Apr 18 19:01:42 unbound 72249 [72249:1] debug: the query is using TLS encryption, for cloudflare-dns.com Apr 18 19:01:42 unbound 72249 [72249:1] debug: tcp bound to src ip6 2001:470:27:191::2 port 0 (len 28) Apr 18 19:01:42 unbound 72249 [72249:1] debug: serviced send timer Apr 18 19:01:42 unbound 72249 [72249:1] debug: cache memory msg=118707 rrset=173008 infra=7808 val=0 Apr 18 19:01:42 unbound 72249 [72249:1] info: 0RDd mod1 rep feodotracker.abuse.ch. AAAA IN Apr 18 19:01:42 unbound 72249 [72249:1] info: mesh_run: end 1 recursion states (1 with reply, 0 detached), 1 waiting replies, 0 recursion replies sent, 0 replies dropped, 0 states jostled out Apr 18 19:01:42 unbound 72249 [72249:1] debug: mesh_run: iterator module exit state is module_wait_reply Apr 18 19:01:42 unbound 72249 [72249:1] debug: dnssec status: not expected Apr 18 19:01:42 unbound 72249 [72249:1] debug: sending to target: <.> 2606:4700:4700::1111#853 Apr 18 19:01:42 unbound 72249 [72249:1] info: sending query: p2.shared.global.fastly.net. AAAA IN Apr 18 19:01:42 unbound 72249 [72249:1] debug: selrtt 376 Apr 18 19:01:42 unbound 72249 [72249:1] debug: rpz: iterator module callback: have_rpz=0 Apr 18 19:01:42 unbound 72249 [72249:1] debug: attempt to get extra 3 targets Apr 18 19:01:42 unbound 72249 [72249:1] debug: [cloudflare-dns.com] ip4 1.1.1.1 port 853 (len 16) Apr 18 19:01:42 unbound 72249 [72249:1] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1111 port 853 (len 28) Apr 18 19:01:42 unbound 72249 [72249:1] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1001 port 853 (len 28) Apr 18 19:01:42 unbound 72249 [72249:1] debug: [cloudflare-dns.com] ip4 1.0.0.1 port 853 (len 16) Apr 18 19:01:42 unbound 72249 [72249:1] debug: [dns.google] ip4 8.8.8.8 port 853 (len 16) Apr 18 19:01:42 unbound 72249 [72249:1] debug: [dns.google] ip4 8.8.4.4 port 853 (len 16) Apr 18 19:01:42 unbound 72249 [72249:1] debug: [dns.google] ip6 2001:4860:4860::8888 port 853 (len 28) Apr 18 19:01:42 unbound 72249 [72249:1] debug: [dns.google] ip6 2001:4860:4860::8844 port 853 (len 28) Apr 18 19:01:42 unbound 72249 [72249:1] info: DelegationPoint<.>: 0 names (0 missing), 8 addrs (0 result, 8 avail) parentNS Apr 18 19:01:42 unbound 72249 [72249:1] debug: processQueryTargets: targetqueries 0, currentqueries 0 sentcount 0 Apr 18 19:01:42 unbound 72249 [72249:1] info: processQueryTargets: feodotracker.abuse.ch. AAAA IN Apr 18 19:01:42 unbound 72249 [72249:1] debug: iter_handle processing q with state QUERY TARGETS STATE Apr 18 19:01:42 unbound 72249 [72249:1] debug: forwarding request Apr 18 19:01:42 unbound 72249 [72249:1] debug: request has dependency depth of 0 Apr 18 19:01:42 unbound 72249 [72249:1] info: resolving feodotracker.abuse.ch. AAAA IN Apr 18 19:01:42 unbound 72249 [72249:1] debug: iter_handle processing q with state INIT REQUEST STATE Apr 18 19:01:42 unbound 72249 [72249:1] debug: returning CNAME response from cache Apr 18 19:01:42 unbound 72249 [72249:1] debug: msg ttl is 1103, prefetch ttl 993 Apr 18 19:01:42 unbound 72249 [72249:1] info: msg from cache lookup ;; ->>HEADER<<- opcode: QUERY, rcode: NOERROR, id: 0 ;; flags: qr ; QUERY: 1, ANSWER: 3, AUTHORITY: 0, ADDITIONAL: 0 ;; QUESTION SECTION: feodotracker.abuse.ch. IN AAAA ;; ANSWER SECTION: feodotracker.abuse.ch. 1103 IN CNAME p2.shared.global.fastly.net. feodotracker.abuse.ch. 1103 IN RRSIG CNAME 5 3 60 20230504155253 20230404155253 12765 abuse.ch. N2C1reBZgD3r15ldnR/wDqmbYumI2kEgDGvbTqCgWKsa82Ds9TZUN/T4SlUmC5W6HsGD7QyNNHTjygXwlDETvnhImYl9SDZgtePRinjnfjinFthzcpTVEVGxtXCLIYOqCATAUwZotkKGtUE1u4aVqkArtSADJYpnk+MQPuYmrS7FEPxILrwoSDFryA8Lpdv3ut3+UzATfqbrB7W+P5qYdel/ODEjJozdOkK2PrmhiYp2uHXj5qicxZiPMuytjKVVmLwXBXQlNA4s2o4KFAYcHf7X4M+W3H/JFoCHIRfl28yZPqcWY6mjAkLpxa2SVcFI39zadQyf513ed+LMsFypng== ;{id = 12765} feodotracker.abuse.ch. 1103 IN RRSIG CNAME 14 3 60 20230514214831 20230414214831 45114 abuse.ch. RHzCfLewwoSmpqmk5cwhrG7bOiAP0HHpAx3AP/R0iUBAsaeF6ISc7/Nz/nIq+w6luZX9vypQgACpR++woKFWQO/+/M6cBBWkJN1HAMl14qNZ0brKxvNaBFRE4eN5Caog ;{id = 45114} ;; AUTHORITY SECTION: ;; ADDITIONAL SECTION: ;; MSG SIZE rcvd: 512 Apr 18 19:01:42 unbound 72249 [72249:1] debug: request has dependency depth of 0 Apr 18 19:01:42 unbound 72249 [72249:1] info: resolving feodotracker.abuse.ch. AAAA IN Apr 18 19:01:42 unbound 72249 [72249:1] debug: iter_handle processing q with state INIT REQUEST STATE Apr 18 19:01:42 unbound 72249 [72249:1] debug: process_request: new external request event Apr 18 19:01:42 unbound 72249 [72249:1] debug: iterator[module 1] operate: extstate:module_state_initial event:module_event_pass Apr 18 19:01:42 unbound 72249 [72249:1] debug: mesh_run: python module exit state is module_wait_module Apr 18 19:01:42 unbound 72249 [72249:1] debug: mesh_run: start Apr 18 19:01:42 unbound 72249 [72249:1] info: receive_udp on interface: 127.0.0.1 Apr 18 19:01:42 unbound 72249 [72249:1] info: send_udp over interface: 127.0.0.1 Apr 18 19:01:42 unbound 72249 [72249:1] info: receive_udp on interface: 127.0.0.1 Apr 18 19:01:41 unbound 72249 [72249:3] debug: comm point start listening 30 (30000 msec) Apr 18 19:01:41 unbound 72249 [72249:3] debug: comm point stop listening 30 Apr 18 19:01:41 unbound 72249 [72249:3] debug: comm point start listening 30 (30000 msec) Apr 18 19:01:41 unbound 72249 [72249:3] debug: comm point stop listening 30 Apr 18 19:01:41 unbound 72249 [72249:3] debug: using localzone xxxnetxxx. static Apr 18 19:01:41 unbound 72249 [72249:3] debug: Reading ssl tcp query of length 128 Apr 18 19:01:41 unbound 72249 [72249:3] debug: comm point start listening 30 (30000 msec) Apr 18 19:01:41 unbound 72249 [72249:3] debug: comm point stop listening 30 Apr 18 19:01:41 unbound 72249 [72249:3] debug: comm point start listening 30 (30000 msec) Apr 18 19:01:41 unbound 72249 [72249:3] debug: comm point stop listening 30 Apr 18 19:01:41 unbound 72249 [72249:3] debug: using localzone xxxnetxxx. static Apr 18 19:01:41 unbound 72249 [72249:3] debug: Reading ssl tcp query of length 128 Apr 18 19:01:41 unbound 72249 [72249:3] debug: SSL connection ip4 192.168.77.156 port 38692 (len 16) Apr 18 19:01:41 unbound 72249 [72249:3] debug: comm point start listening 30 (30000 msec) Apr 18 19:01:40 unbound 72249 [72249:0] debug: close fd 30 Apr 18 19:01:40 unbound 72249 [72249:0] debug: remote control operation completed Apr 18 19:01:40 unbound 72249 [72249:0] info: control cmd: load_cache Apr 18 19:01:40 unbound 72249 [72249:0] debug: remote control connection authenticated Apr 18 19:01:40 unbound 72249 [72249:0] debug: comm point start listening 30 (120000 msec) Apr 18 19:01:40 unbound 72249 [72249:0] debug: comm point stop listening 30 Apr 18 19:01:40 unbound 72249 [72249:0] debug: new control connection from ip4 127.0.0.1 port 8654 (len 16) Apr 18 19:01:40 unbound 72249 [72249:0] debug: close fd 30 Apr 18 19:01:40 unbound 72249 [72249:0] debug: remote control operation completed Apr 18 19:01:40 unbound 72249 [72249:0] info: control cmd: status Apr 18 19:01:40 unbound 72249 [72249:0] debug: remote control connection authenticated Apr 18 19:01:40 unbound 72249 [72249:3] debug: cache memory msg=66072 rrset=66072 infra=7808 val=0 Apr 18 19:01:40 unbound 72249 [72249:3] debug: no config, using builtin root hints. Apr 18 19:01:40 unbound 72249 [72249:3] debug: [dns.google] ip6 2001:4860:4860::8844 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:3] debug: [dns.google] ip6 2001:4860:4860::8888 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:3] debug: [dns.google] ip4 8.8.4.4 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:3] debug: [dns.google] ip4 8.8.8.8 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:3] debug: [cloudflare-dns.com] ip4 1.0.0.1 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:3] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1001 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:3] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1111 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:3] debug: [cloudflare-dns.com] ip4 1.1.1.1 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:3] info: DelegationPoint<.>: 0 names (0 missing), 8 addrs (0 result, 8 avail) parentNS Apr 18 19:01:40 unbound 72249 [72249:3] debug: Forward zone server list: Apr 18 19:01:40 unbound 72249 [72249:1] debug: cache memory msg=66072 rrset=66072 infra=7808 val=0 Apr 18 19:01:40 unbound 72249 [72249:1] debug: no config, using builtin root hints. Apr 18 19:01:40 unbound 72249 [72249:1] debug: [dns.google] ip6 2001:4860:4860::8844 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:1] debug: [dns.google] ip6 2001:4860:4860::8888 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:1] debug: [dns.google] ip4 8.8.4.4 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:1] debug: [dns.google] ip4 8.8.8.8 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:1] debug: [cloudflare-dns.com] ip4 1.0.0.1 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:1] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1001 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:1] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1111 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:1] debug: [cloudflare-dns.com] ip4 1.1.1.1 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:1] info: DelegationPoint<.>: 0 names (0 missing), 8 addrs (0 result, 8 avail) parentNS Apr 18 19:01:40 unbound 72249 [72249:1] debug: Forward zone server list: Apr 18 19:01:40 unbound 72249 [72249:2] debug: cache memory msg=66072 rrset=66072 infra=7808 val=0 Apr 18 19:01:40 unbound 72249 [72249:2] debug: no config, using builtin root hints. Apr 18 19:01:40 unbound 72249 [72249:2] debug: [dns.google] ip6 2001:4860:4860::8844 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:2] debug: [dns.google] ip6 2001:4860:4860::8888 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:2] debug: [dns.google] ip4 8.8.4.4 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:2] debug: [dns.google] ip4 8.8.8.8 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:2] debug: [cloudflare-dns.com] ip4 1.0.0.1 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:2] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1001 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:2] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1111 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:2] debug: [cloudflare-dns.com] ip4 1.1.1.1 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:2] info: DelegationPoint<.>: 0 names (0 missing), 8 addrs (0 result, 8 avail) parentNS Apr 18 19:01:40 unbound 72249 [72249:2] debug: Forward zone server list: Apr 18 19:01:40 unbound 72249 [72249:0] debug: comm point start listening 30 (120000 msec) Apr 18 19:01:40 unbound 72249 [72249:0] debug: comm point stop listening 30 Apr 18 19:01:40 unbound 72249 [72249:0] debug: new control connection from ip4 127.0.0.1 port 61004 (len 16) Apr 18 19:01:40 unbound 72249 [72249:0] info: start of service (unbound 1.17.1). Apr 18 19:01:40 unbound 72249 [72249:0] debug: cache memory msg=66072 rrset=66072 infra=7808 val=0 Apr 18 19:01:40 unbound 72249 [72249:0] debug: no config, using builtin root hints. Apr 18 19:01:40 unbound 72249 [72249:0] debug: [dns.google] ip6 2001:4860:4860::8844 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:0] debug: [dns.google] ip6 2001:4860:4860::8888 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:0] debug: [dns.google] ip4 8.8.4.4 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:0] debug: [dns.google] ip4 8.8.8.8 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:0] debug: [cloudflare-dns.com] ip4 1.0.0.1 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:0] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1001 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:0] debug: [cloudflare-dns.com] ip6 2606:4700:4700::1111 port 853 (len 28) Apr 18 19:01:40 unbound 72249 [72249:0] debug: [cloudflare-dns.com] ip4 1.1.1.1 port 853 (len 16) Apr 18 19:01:40 unbound 72249 [72249:0] info: DelegationPoint<.>: 0 names (0 missing), 8 addrs (0 result, 8 avail) parentNS Apr 18 19:01:40 unbound 72249 [72249:0] debug: Forward zone server list: Apr 18 19:01:40 unbound 72249 [72249:1] debug: libevent 2.1.12-stable uses kqueue method. Apr 18 19:01:40 unbound 72249 [72249:2] debug: libevent 2.1.12-stable uses kqueue method. Apr 18 19:01:40 unbound 72249 [72249:3] debug: libevent 2.1.12-stable uses kqueue method. Apr 18 19:01:40 unbound 72249 [72249:0] debug: libevent 2.1.12-stable uses kqueue method. Apr 18 19:01:40 unbound 72249 [72249:0] debug: start threads Apr 18 19:01:40 unbound 72249 [72249:0] debug: total of 59448 outgoing ports available Apr 18 19:01:40 unbound 72249 [72249:0] debug: donotq: ::1 Apr 18 19:01:40 unbound 72249 [72249:0] debug: donotq: 127.0.0.0/8 Apr 18 19:01:40 unbound 72249 [72249:0] debug: target fetch policy for level 4 is 0 Apr 18 19:01:40 unbound 72249 [72249:0] debug: target fetch policy for level 3 is 0 Apr 18 19:01:40 unbound 72249 [72249:0] debug: target fetch policy for level 2 is 1 Apr 18 19:01:40 unbound 72249 [72249:0] debug: target fetch policy for level 1 is 2 Apr 18 19:01:40 unbound 72249 [72249:0] debug: target fetch policy for level 0 is 3 Apr 18 19:01:40 unbound 72249 [72249:0] notice: init module 1: iterator Apr 18 19:01:40 unbound 72249 [72249:0] info: [pfBlockerNG]: init_standard script loaded Apr 18 19:01:36 unbound 72249 [72249:0] info: [pfBlockerNG]: pfb_unbound.py script loaded Apr 18 19:01:36 unbound 72249 [72249:0] notice: init module 0: python Apr 18 19:01:36 unbound 72249 [72249:0] debug: module config: "python iterator" Apr 18 19:01:36 unbound 72249 [72249:0] debug: ignoring duplicate RR: localhost. A 127.0.0.1 Apr 18 19:01:36 unbound 72249 [72249:0] debug: ignoring duplicate RR: localhost. AAAA ::1 Apr 18 19:01:36 unbound 72249 [72249:0] info: implicit transparent local-zone int. TYPE0 IN Apr 18 19:01:36 unbound 72249 [72249:0] debug: duplicate acl address ignored. Apr 18 19:01:36 unbound 72249 [72249:0] debug: drop user privileges, run as unbound Apr 18 19:01:36 unbound 72249 [72249:0] debug: chroot to /var/unbound Apr 18 19:01:36 unbound 72249 [72249:0] debug: chdir to /var/unbound -
 G getcom referenced this topic on
G getcom referenced this topic on
-
 G getcom referenced this topic on
G getcom referenced this topic on
-
I found a new bug !
With version 23.01 i have only 50% of download bandwich ! Upload is ok 100%
I put back 22.05 and 2.6.0(community edition)
Download and upload reach 100%Chelsio 520 on lan side
Intel pro nic on wan sideI mean that a weird bug
Maybe netgate should not code with a non existent freebsd 14 version mention « CURRENT » when it’s not even officially out as release date yethttps://www.freebsd.org/releng/
https://www.freebsd.org/releases/14.0R/schedule/Maybe netgate pull out freebsd 14 from kinder suprise candy !
imo is based on freebsd release info
Thnk
So i stick to community for now
-
@jimbohello There are a few threads already for Chelsio.
https://forum.netgate.com/topic/177885/upgrade-to-23-01-wan-speed-halved/
https://forum.netgate.com/topic/177972/download-speeds-cut-in-half/
-
Yup, that's a separate issue. But do you have a T520-SO by any chance?
-
em0@pci0:1:0:0: class=0x020000 card=0xa01f8086 chip=0x10d38086 rev=0x00 hdr=0x00 vendor = 'Intel Corporation' device = '82574L Gigabit Network Connection' class = network subclass = ethernet t5iov0@pci0:2:0:0: class=0x020000 card=0x00001425 chip=0x50011425 rev=0x00 hdr=0x00 vendor = 'Chelsio Communications Inc' device = 'T520-CR Unified Wire Ethernet Controller' class = network subclass = ethernet t5iov1@pci0:2:0:1: class=0x020000 card=0x00001425 chip=0x50011425 rev=0x00 hdr=0x00 vendor = 'Chelsio Communications Inc' device = 'T520-CR Unified Wire Ethernet Controller' class = network subclass = ethernet t5iov2@pci0:2:0:2: class=0x020000 card=0x00001425 chip=0x50011425 rev=0x00 hdr=0x00 vendor = 'Chelsio Communications Inc' device = 'T520-CR Unified Wire Ethernet Controller' class = network subclass = ethernet t5iov3@pci0:2:0:3: class=0x020000 card=0x00001425 chip=0x50011425 rev=0x00 hdr=0x00 vendor = 'Chelsio Communications Inc' device = 'T520-CR Unified Wire Ethernet Controller' class = network subclass = ethernet t5nex0@pci0:2:0:4: class=0x020000 card=0x00001425 chip=0x54011425 rev=0x00 hdr=0x00 vendor = 'Chelsio Communications Inc' device = 'T520-CR Unified Wire Ethernet Controller' class = network subclass = ethernet -
Ok. Unfortunately it doesn't appear to affect the one Chelsio NIC I have available.
You could add that data point to the other thread. -
S SteveITS referenced this topic on
-
S SteveITS referenced this topic on
-
It seems to me that this problem no longer appears on version 23.05
-
Ah, well that would be a very interesting result. Can anyone else hitting this verify that?
-
Running the SG-1100, I have been fighting this problem for a while. I did notice the problem self resolved once I applied all the recommended patches on 23.01 and reboot. I have not gone in and attempted to figure out which one or combo fixes it, with a 1100 it is just too slow

Curious to know if this solution helps anyone else.
-
@defunct78 I'm running 23.01-Release on SG-5100. I'm still plagued with this issue and today I threw up my hands and reverted to port 53 and disabled python mode in both the resolver & pfBlocker.
I am now watching to see how my system responds.
-
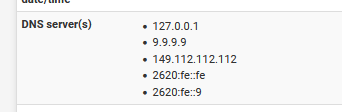
The reverse on my side :
I'm using a 23.01-Release on SG-4100.I changed from default resolving to forwarding to quad9 :
As per instructions :
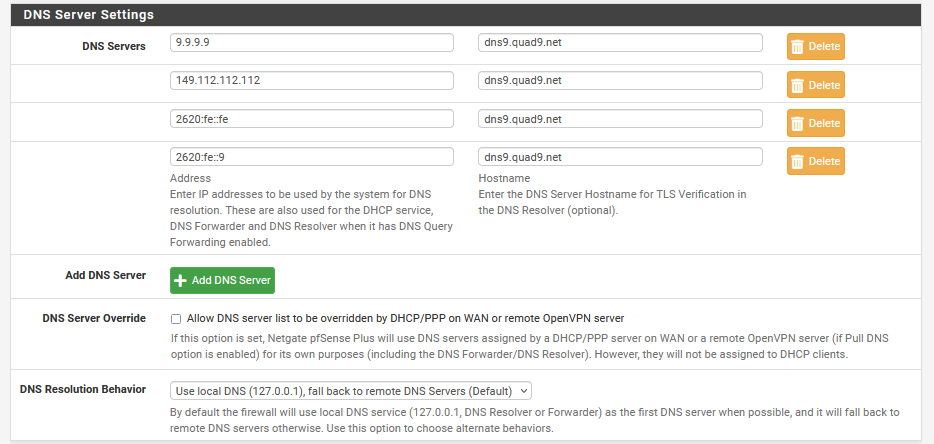
and then :
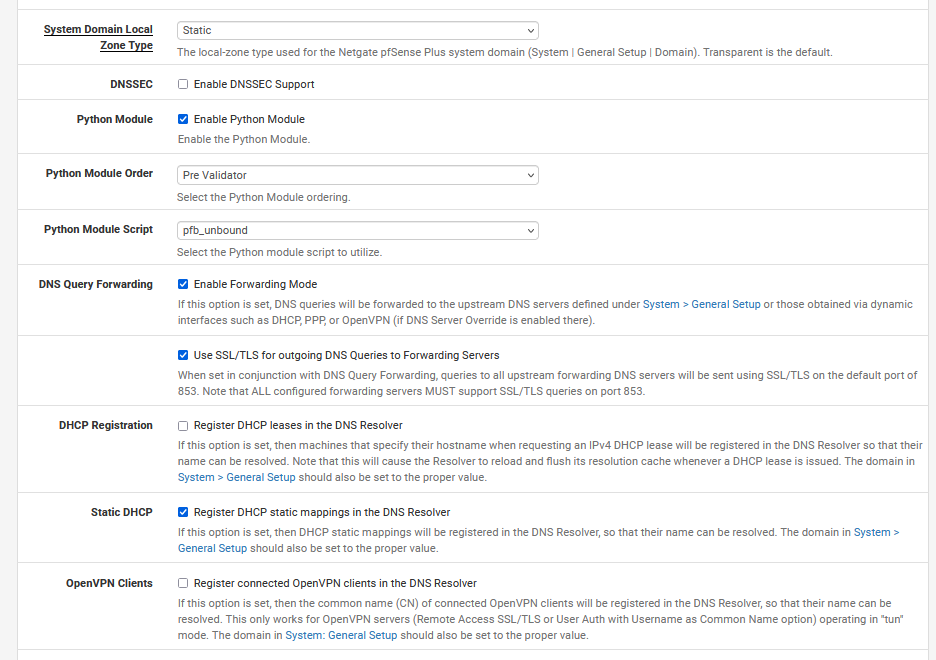
So :
Python mode (of course)
DNSSEC : of course not
Forwarding : that's what this all about : Yes
TLS : over TLS using port 853.
[suspicious mode : ON]
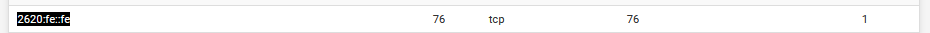
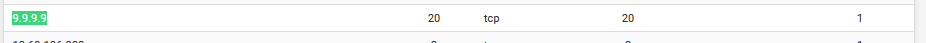
Look at the number of open TCP connections .... every one of them has an opened TLS state.
Nice .... but is it ?
These TLS connections are established by pfSense, not some LAN device.
To fire of a classic DNS request, using UDP, thousands of code lines are needed to handle the request, answers etc.
For TLS : that will be hundreds of thousands per connection - and I'm probably still not even close. Because now, it's TCP, far more complex as UDP, and then ... TLS.
To (re)build a TLS connections, entropy is going through the drain fast.
I never really found a way to measure available entropy, but what I know : if this one goes to zero, my web multi home server becomes slow. Note that the processor of my web (mail, bind, etc) server uses a quad core Intel(R) Xeon(R) CPU 3Ghz, way more power as my pfSense (a 4100).Instead of using the word 'bug' or 'problem' I use this, which permits to to see more clearly what's going on.
Note that I've switched from resolving mode to forwarding mode over TLS on May 4,2023 @08h00.On the other hand : I was forwarding to 1.1.1.1 and friends for a week or two.
Using TLS of course. I've found no (unbound or DNS) issues what so ever.Probably important :
My IPv4 and IPv6 are, afaik, without issues.[suspicious mode : OFF]
Now, let's wait for thread the subject "Major DNS Bug 23.01 with Quad9 on SSL" to happen.
-
I would argue this is a bug because the same load in 22.05 did not cause any problems even in much larger environments.
However has anyone verified that this still happens in 23.05?
We have one report saying that after upgrading the problem was solved.Steve
-
I have been using pfSense w/ Unbound configured for DNS over TLS forwarding for years. Recently, it appears that there is a serious issue with the resolver. I get intermittent errors with the following:
2023-05-04 10:24:53.905770-05:00 unbound 3136 [3136:2] debug: comm point listen_for_rw 46 0
2023-05-04 10:24:53.905752-05:00 unbound 3136 [3136:3] debug: comm point listen_for_rw 47 0
2023-05-04 10:24:53.905719-05:00 unbound 3136 [3136:1] debug: comm point listen_for_rw 48 0
2023-05-04 10:24:53.882272-05:00 unbound 3136 [3136:1] debug: the query is using TLS encryption, for an unauthenticated connection
2023-05-04 10:24:53.882209-05:00 unbound 3136 [3136:3] debug: the query is using TLS encryption, for an unauthenticated connection
2023-05-04 10:24:53.882148-05:00 unbound 3136 [3136:1] debug: serviced send timerEventually, DNS queires from devices with IPv6 addresses fail causing mobile apps to crash on the connected device. The errors happen with or without pfBlocker DNSBL active
I can restart the Unbound service, it will work for a while then the errors return.
Also get this now with DNSBL:
servicewatchdog_cron.php: The command '/usr/local/sbin/unbound -c /var/unbound/unbound.conf' returned exit code '1', the output was '[1683215282] unbound[54733:0] debug: creating udp4 socket 192.168.246.1 53 [1683215282] unbound[54733:0] error: bind: address already in use [1683215282] unbound[54733:0] fatal error: could not open ports' -
Are you using Quad9? Are you running 23.01? can you test 23.05?
-
@n0m0fud Have you disabled DNSSEC and/or DNS over TLS as discussed above?
re: watchdog and DNSBL...pfBlocker updates and DHCP registrations will restart unbound so watchdog should not try to also start it. It can end up starting twice which is presumably why it is saying the address/port is already in use. Same thing with Suricata/Snort or other services that restart as part of normal behavior.
-
@stephenw10 Running 23.05 forwarding to Cloudflare. Its definitely an IPv6 issue. DNS does not resolve via DNS over TLS on IPv6 Interfaces. I rebooted the router which kills IPv6 for a time after the reboot. Everything worked fine until the IPv6 addresses activated and RADV started. Logs:
2023-05-04 11:01:43.286399-05:00 kernel - cannot forward src fe80:2::1ab4:30ff:fe03:3db, dst 2604:2d80:b208:f300:201:2eff:fe5a:6a7c, nxt 17, rcvif re1, outif re0
2023-05-04 11:01:07.981963-05:00 kernel - cannot forward src fe80:2::557:1ce2:51f6:763c, dst 2600:1402:b800:1a::6847:8fc5, nxt 6, rcvif re1, outif re0
2023-05-04 11:01:07.981902-05:00 kernel - cannot forward src fe80:2::557:1ce2:51f6:763c, dst 2600:1402:b800:1a::6847:8fd0, nxt 6, rcvif re1, outif re0AND
2023-05-04 11:00:29.311174-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 89 0
2023-05-04 11:00:29.311008-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 92 0
2023-05-04 11:00:29.310857-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 91 0
2023-05-04 11:00:29.310710-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 85 0
2023-05-04 11:00:29.310546-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 86 0
2023-05-04 11:00:29.310400-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 87 0
2023-05-04 11:00:29.310242-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 90 0
2023-05-04 11:00:29.310094-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 84 0
2023-05-04 11:00:29.309943-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 88 0
2023-05-04 11:00:29.309776-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 81 0
2023-05-04 11:00:29.309627-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 82 0
2023-05-04 11:00:29.309463-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 83 0
2023-05-04 11:00:29.309314-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 77 0
2023-05-04 11:00:29.309160-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 80 0
2023-05-04 11:00:29.308995-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 79 0
2023-05-04 11:00:29.308839-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 78 0
2023-05-04 11:00:29.308673-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 76 0
2023-05-04 11:00:29.308519-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 73 0
2023-05-04 11:00:29.308369-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 75 0
2023-05-04 11:00:29.308191-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 67 0
2023-05-04 11:00:29.307997-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 70 0
2023-05-04 11:00:29.307829-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 61 0
2023-05-04 11:00:29.307696-05:00 unbound 52706 [52706:3] debug: comm point listen_for_rw 74 0
2023-05-04 11:00:29.307645-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 63 0
2023-05-04 11:00:29.307402-05:00 unbound 52706 [52706:1] debug: comm point listen_for_rw 69 0
2023-05-04 11:00:29.307354-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 62 0
2023-05-04 11:00:29.307164-05:00 unbound 52706 [52706:1] debug: comm point listen_for_rw 72 0
2023-05-04 11:00:29.307124-05:00 unbound 52706 [52706:2] debug: comm point listen_for_rw 66 0
2023-05-04 11:00:29.307052-05:00 unbound 52706 [52706:3] debug: comm point listen_for_rw 64 0
2023-05-04 11:00:29.306942-05:00 unbound 52706 [52706:1] debug: comm point listen_for_rw 65 0
2023-05-04 11:00:29.306894-05:00 unbound 52706 [52706:2] debug: comm point listen_for_rw 68 0
2023-05-04 11:00:29.306849-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 57 0
2023-05-04 11:00:29.306696-05:00 unbound 52706 [52706:1] debug: comm point listen_for_rw 71 0
2023-05-04 11:00:29.306664-05:00 unbound 52706 [52706:2] debug: comm point listen_for_rw 59 0
2023-05-04 11:00:29.306647-05:00 unbound 52706 [52706:3] debug: comm point listen_for_rw 60 0
2023-05-04 11:00:29.306475-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 54 0
2023-05-04 11:00:29.306241-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 53 0
2023-05-04 11:00:29.306079-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 55 0
2023-05-04 11:00:29.305913-05:00 unbound 52706 [52706:2] debug: comm point listen_for_rw 58 0
2023-05-04 11:00:29.305895-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 51 0
2023-05-04 11:00:29.305794-05:00 unbound 52706 [52706:3] debug: comm point listen_for_rw 56 0
2023-05-04 11:00:29.305412-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 52 0
2023-05-04 11:00:29.305247-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 50 0
2023-05-04 11:00:29.305075-05:00 unbound 52706 [52706:0] debug: comm point listen_for_rw 49 0
2023-05-04 11:00:29.294142-05:00 unbound 52706 [52706:0] debug: the query is using TLS encryption, for an unauthenticated connection
2023-05-04 11:00:29.294112-05:00 unbound 52706 [52706:0] debug: tcp bound to src ip4 173.21.178.244 port 0 (len 16)
2023-05-04 11:00:29.294090-05:00 unbound 52706 [52706:0] debug: the query is using TLS encryption, for an unauthenticated connection
2023-05-04 11:00:29.294056-05:00 unbound 52706 [52706:0] debug: tcp bound to src ip6 2604:2d80:8419:0:35e5:332b:4cf:e696 port 0 (len 28)
2023-05-04 11:00:29.294034-05:00 unbound 52706 [52706:0] debug: the query is using TLS encryption, for an unauthenticated connection
2023-05-04 11:00:29.293995-05:00 unbound 52706 [52706:0] debug: comm point start listening 89 (-1 msec)
2023-05-04 11:00:29.293989-05:00 unbound 52706 [52706:0] debug: the query is using TLS encryption, for an unauthenticated connection
2023-05-04 11:00:29.293941-05:00 unbound 52706 [52706:0] debug: the query is using TLS encryption, for an unauthenticated connection
2023-05-04 11:00:29.293899-05:00 unbound 52706 [52706:0] debug: comm point start listening 87 (-1 msec)
2023-05-04 11:00:29.293871-05:00 unbound 52706 [52706:0] debug: tcp bound to src ip4 173.21.178.244 port 0 (len 16)
2023-05-04 11:00:29.293850-05:00 unbound 52706 [52706:0] debug: the query is using TLS encryption, for an unauthenticated connection
2023-05-04 11:00:29.293810-05:00 unbound 52706 [52706:0] debug: comm point start listening 85 (-1 msec)
2023-05-04 11:00:29.293777-05:00 unbound 52706 [52706:0] debug: tcp bound to src ip6 2604:2d80:8419:0:35e5:332b:4cf:e696 port 0 (len 28)Customer Unbound Options:
server:
forward-zone:
name: "."
forward-ssl-upstream: yes
forward-addr: 1.1.1.1@853
forward-addr: 1.0.0.1@853
forward-addr: 2606:4700:4700::64@853
forward-addr: 2606:4700:4700::6400@853All Ips are pingable. The IPs are Cloudflare.
Not sure what's going on here.
-
If you set Unbound to use v4 interfaces for Outbound traffic only does that resolve it?
-
@stephenw10 Only way to do that is manually edit and save the config file. The GUI only allows selection of physical interfaces. Not IP addresses.
-
2023-05-04 11:01:07.981902-05:00 kernel - cannot forward src fe80:2::557:1ce2:51f6:763c, dst 2600:1402:b800:1a::6847:8fd0, nxt 6, rcvif re1, outif re0What has
fe80:2::557:1ce2:51f6:763c? It shouldn't be trying to send traffic to a GUA address from LL, it's invalid.What shows in the unbound config for interface binding(s)?
-
@stephenw10 And restarting the service overrides my manual changes. This used to work fine until about 2 months ago. I know its local DNS as I can manually set the DNS on mobile devices that are showing the issue and the app failure problem goes away.