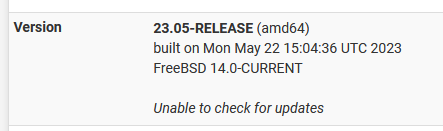
22.05-RELEASE (amd64) Unable to check for updates?
-
@TAC57 and were those DNS IPs on the Snort alert page? That’s why I asked about Snort above. Reading back it sounds like a restart fixed it in January also. Restarting would empty the Snort block table.
-
Yup, disable Snort. Reboot. Retest.
-
@SteveITS
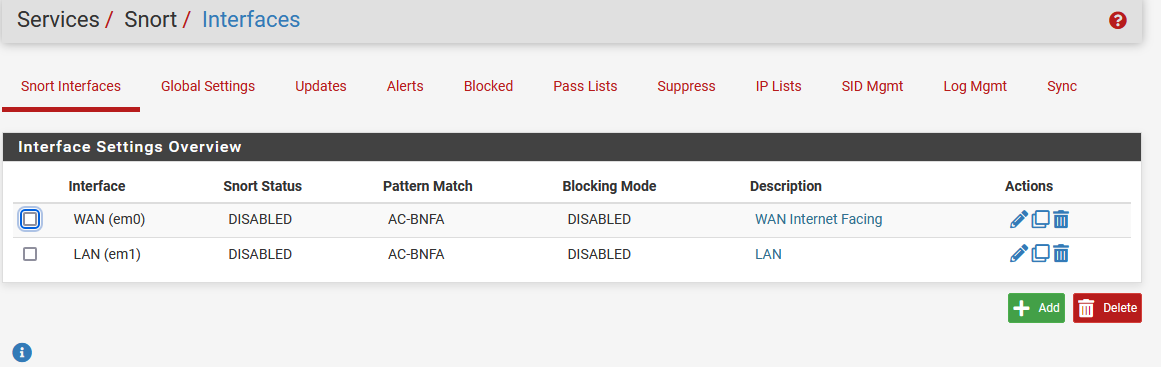
I've been running Snort forever. I'll disable it and see what happens.
I'll disable it and see what happens.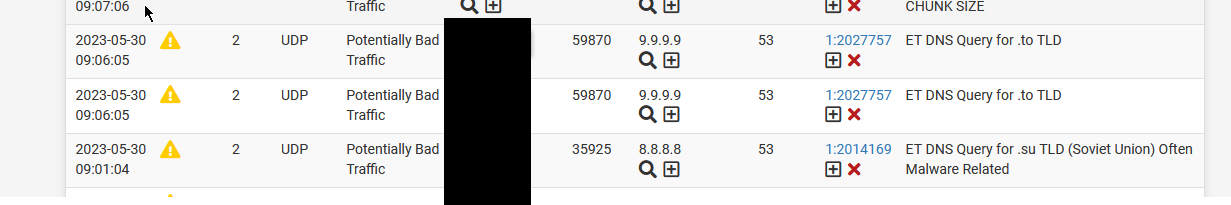
-
@stephenw10 I disabled Snort, rebooted and still unable to check for updates. Also, DNS Look up doesn't return any IPs.
-
Make sure the Snort block table is actually cleared, assuming you had Snort in blocking mode. Check Diag > Tables > Snort2c.
Snort pulls new signatures automatically. It can start alerting/blocking things that were previously fine without warning!
-
@stephenw10 Snort2c table is empty.
I've disabled Snort and have rebooted pfsense.
pfsense is still reporting 'Unable to check for updates'.
Diag / DNS Lookup times out with firmware.netgate.com, google.com, 8.8.8.8. It took about 3 minutes to get the message 'Host "firmware.netgarte.com" cound not be resolved.'
I can ping any of these host from a Raspberry Pi and replys.
To switch from the Status / Dashboard screen to the System / Update screen takes 1.5 minutes and then about another 30 seconds to report that it's Unable to check for updates.
I'm also still getting the notice "An error occurred while uploading the encrypted Netgate pfSense Plus configuration to https://acb.netgate.com/save ( Unable to resolve acb.netgate.com ) @ 2023-05-30 16:53:11"
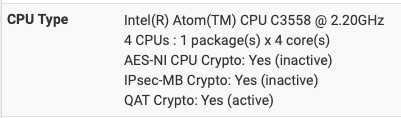
I'm running pfsense on a Zima SBC:
Intel(R) Celeron(R) CPU N3450 @ 1.10GHz
4 CPUs : 1 package(s) x 4 core(s)
AES-NI CPU Crypto: Yes (active)
IPsec-MB Crypto: Yes (inactive)
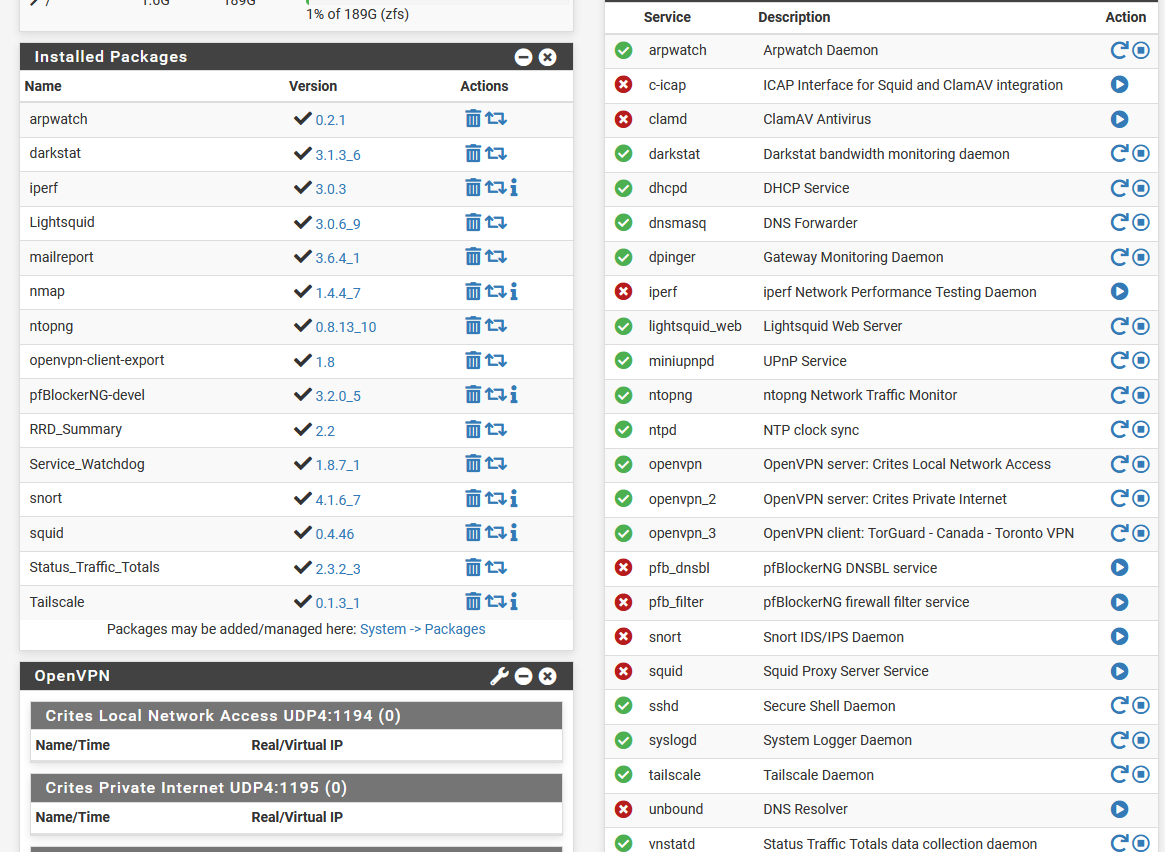
QAT Crypto: NoThese are my installed packages / Services:
-
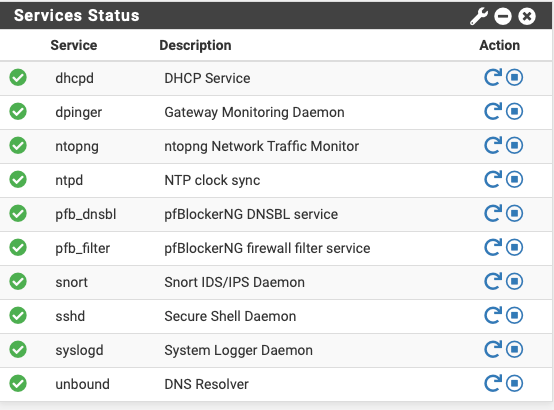
Oh you're not using the resolver (Unbound) at all. You're using the forwarder (DNSMasq).
In that as a test I would try disabling DNSMasq and enabling Unbound and see if that makes any difference. With that it should resolve directly.
-
@stephenw10 Plus he’s running practically running every pfSense package!
-
@DefenderLLC If running a homelab with a TrueNAS Plex server, a few computers, and some IOT devices, what packages do you recommend to balance security, performance, and ease of use?
I must admit I've implemented (or attempted) most of these packages after reading about, or seeing a video on, some cool package that I think I need or was interested in learning about. Most of these I've setup with videos from https://forums.lawrencesystems.com/.
-
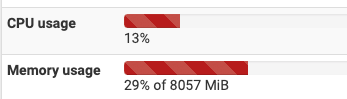
@TAC57 judging by your screenshots, your CPU is not very powerful to be running all of those packages at the same time. Just wait until you actually start doing IPS blocking or turn on a bunch of rules with pfBlockerNG. How much memory do you have allocated to this box?
-
@DefenderLLC I'm running pfsense on a Zima SBC:
Intel(R) Celeron(R) CPU N3450 @ 1.10GHz, 4GB RAM
4 CPUs : 1 package(s) x 4 core(s)
AES-NI CPU Crypto: Yes (active) -
@TAC57 That's not nearly enough horsepower to be running all of those packages. I would probably stick with pfBlockerNG and Snort only with not too many rules applied. They both require a lot of RAM if you enable too many rulesets.
-
I still wouldn't expect it to be blocking all outgoing DNS queries though.
Did you test switching to the resolver directly?
-
@TAC57 said in 22.05-RELEASE (amd64) Unable to check for updates?:
@DefenderLLC I'm running pfsense on a Zima SBC:
Intel(R) Celeron(R) CPU N3450 @ 1.10GHz, 4GB RAM
4 CPUs : 1 package(s) x 4 core(s)
AES-NI CPU Crypto: Yes (active)Just for context, I have a Netgate 6100 MAX running pfBlockerNG and Snort both of which are configured with very aggressive rulesets. I have Snort IPS enabled on the WAN interface and Snort IDS on the LAN interface. (Note: I have a UniFi UDM-SE behind the pfSense managing the actual client devices, so pfSense only sees that single IP anyway). I am basically just using my pfSense as a DMZ firewall and for DNS/IPS/IDS only.
This is during an idle period with just me passing traffic. The CPU and RAM can easily spike up to 50% utilization (or more) during heavy traffic loads. You will need more horsepower if plan on running these two packages let alone everything else you have installed.
-
@stephenw10 My VPN provider said my service has quit working because 'DNS on pfsense is failing to resolve the hostname,'
Can what I should do to make sure my system goes back to the totally defaulted DNS server?
-
Did you try disabling DNAMasq and enabling Unbound in resolving mode yet? That's what the default is.
-
@stephenw10 Can you tell me where to find the DNAMasq and Unbound options?
-
@TAC57 said in 22.05-RELEASE (amd64) Unable to check for updates?:
@stephenw10 Can you tell me where to find the DNAMasq and Unbound options?
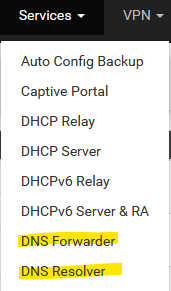
here:
DNS Forwarder is not enabled by default. DNS Resolver runs Unbound. -
DNSMasq is the forwarder so in Services > DNS Forwarder.
Unbound is the resolver (though it can run in forwarding mode) so in Services > DNS Resolver. -
@stephenw10 Ok, I made sure the DNS Forwarder is NOT enabled, and made sure the DNS Resolver IS enabled.
If I clear all my notices, then next time I make a change to my config file I should not see this notice again.
'An error occurred while uploading the encrypted Netgate pfSense Plus configuration to https://acb.netgate.com/save ( Unable to resolve acb.netgate.com ) @ 2023-06-05 15:20:02'