22.05-RELEASE (amd64) Unable to check for updates?
-
I still wouldn't expect it to be blocking all outgoing DNS queries though.
Did you test switching to the resolver directly?
-
@TAC57 said in 22.05-RELEASE (amd64) Unable to check for updates?:
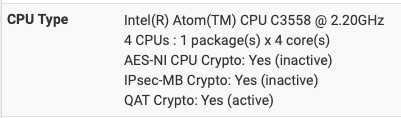
@DefenderLLC I'm running pfsense on a Zima SBC:
Intel(R) Celeron(R) CPU N3450 @ 1.10GHz, 4GB RAM
4 CPUs : 1 package(s) x 4 core(s)
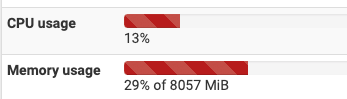
AES-NI CPU Crypto: Yes (active)Just for context, I have a Netgate 6100 MAX running pfBlockerNG and Snort both of which are configured with very aggressive rulesets. I have Snort IPS enabled on the WAN interface and Snort IDS on the LAN interface. (Note: I have a UniFi UDM-SE behind the pfSense managing the actual client devices, so pfSense only sees that single IP anyway). I am basically just using my pfSense as a DMZ firewall and for DNS/IPS/IDS only.
This is during an idle period with just me passing traffic. The CPU and RAM can easily spike up to 50% utilization (or more) during heavy traffic loads. You will need more horsepower if plan on running these two packages let alone everything else you have installed.
-
@stephenw10 My VPN provider said my service has quit working because 'DNS on pfsense is failing to resolve the hostname,'
Can what I should do to make sure my system goes back to the totally defaulted DNS server?
-
Did you try disabling DNAMasq and enabling Unbound in resolving mode yet? That's what the default is.
-
@stephenw10 Can you tell me where to find the DNAMasq and Unbound options?
-
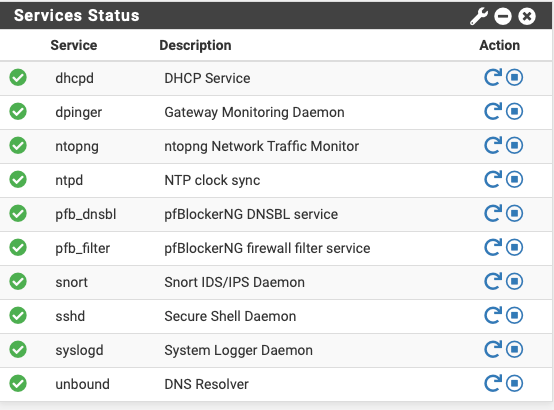
@TAC57 said in 22.05-RELEASE (amd64) Unable to check for updates?:
@stephenw10 Can you tell me where to find the DNAMasq and Unbound options?
here:
DNS Forwarder is not enabled by default. DNS Resolver runs Unbound. -
DNSMasq is the forwarder so in Services > DNS Forwarder.
Unbound is the resolver (though it can run in forwarding mode) so in Services > DNS Resolver. -
@stephenw10 Ok, I made sure the DNS Forwarder is NOT enabled, and made sure the DNS Resolver IS enabled.
If I clear all my notices, then next time I make a change to my config file I should not see this notice again.
'An error occurred while uploading the encrypted Netgate pfSense Plus configuration to https://acb.netgate.com/save ( Unable to resolve acb.netgate.com ) @ 2023-06-05 15:20:02' -
@TAC57 Also, if this issues is taken care of shouldn't I be able to put an IP address (8.8.8.8) or a DNS (www.google.com) in pfsenses Diag / DNS Lookup / Hostname field and get a response?
-
If unbound is running in resolving mode then, yes, you should see see answers from 127.0.0.1 when querying a host.
You can't enter an IP in DNS Lookup though.
If you still can't resolve anything then something is blocking outgoing DNS.
You mentioned you have a VPN provider. Did you add any rules to force DNS queries over a VPN?
Or specific rules to block DNS leaving over the WAN? -
@stephenw10 In the past (see above) I've enter firmware.netgate.com in DNS Lookup and got a response but get nothing now.
I have no rules anywhere that have anything to do with port 53 or 853.
I previously setup a Gateway that sent ONLY my SABnzbd traffic through the VPN and it worked just fine. That has quit working and my VPN provider says it's because 'Per Logs, DNS on pfsense is failing to resolve the hostname.'
-
Hmm, so no configured DNS servers are responding at all when you test there now?
Is Unbound actually running in Status > Services? -
Try dig from Client and pfsense if you capture on WAN with Port 53, do you see DNS querys in the pcap?
You found Package Capture in the Diag Menu.
-
@stephenw10 Status > Services, Unbond, DNS Resolver is checked.
-
Ok, check the state tables in Diag > States for traffic from the firewall only on port 53 when you try to resolve something in Diag > DNS Lookup.
Something must be blocking or at least re-routing that traffic.
-
You don't have a UniFi device with ad blocking enabled, do you? Because if you do, it redirects all 53/UDP traffic to it's own resolver regardless what you have configured on your client devices.
-
@stephenw10 It's weird DNS Lookup will find things and now I just ran it again with 'firmware.netgate.com' and I get 'could not be resolved'.
-
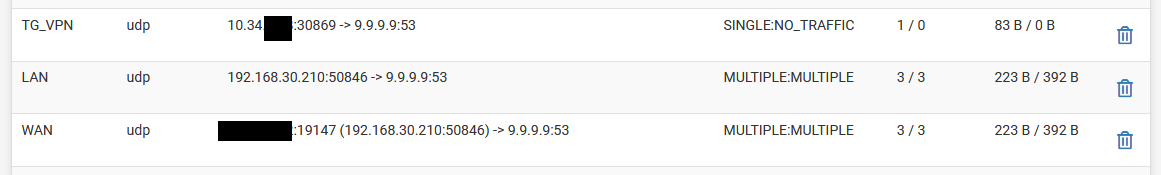
Ok, so there you've got a LAN client successfully connecting to 9.9.9.9 creating states on LAN and WAN.
And you have an unsuccessful connection via the TG_VPN interface.Is Unbound configured to use TG_VPN as it's outbound interface? And that interface is down?
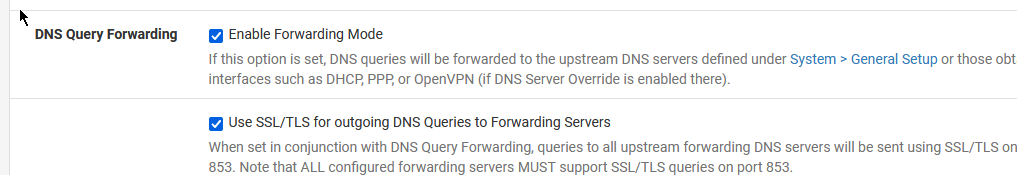
The fact it's connecting to 9.9.9.9 there though means it's not Unbound resolving directly. Is it still set to forwarding mode?
All of that looks like you might have followed some instructions from a VPN provider at some point. Is that possible?
Steve
-
@stephenw10
Is Unbound configured to use TG_VPN as it's outbound interface? And that interface is down?
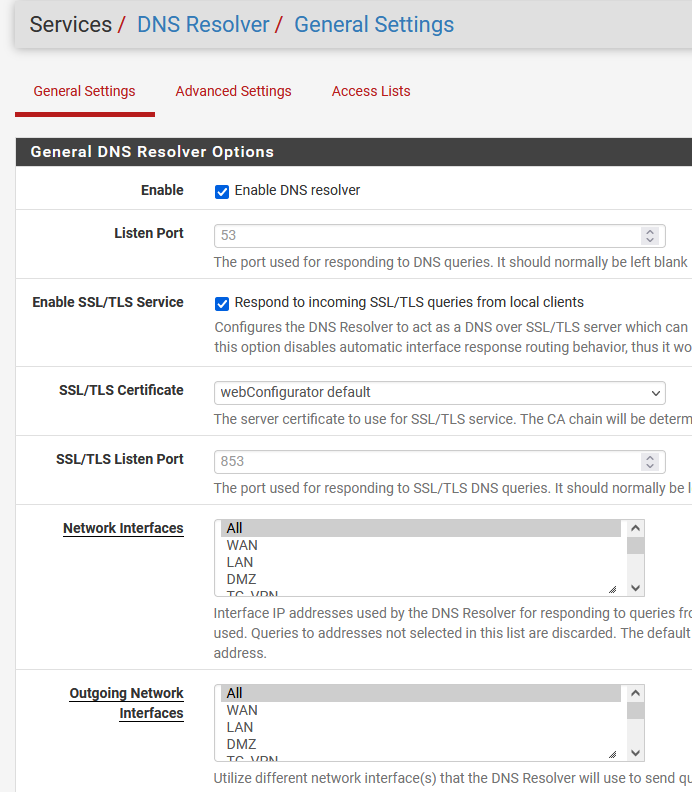
The fact it's connecting to 9.9.9.9 there though means it's not Unbound resolving directly. Is it still set to forwarding mode?
All of that looks like you might have followed some instructions from a VPN provider at some point. Is that possible?
Yes, but I've set a rule to force a single source (192.168.30.117) through the TorGuard VPN gateway
https://torguard.net/article/254/how-to-setup-the-latest-pfsense-openvpn-client.html -
H haraldinho referenced this topic on
-