ATT Internet AIr
-
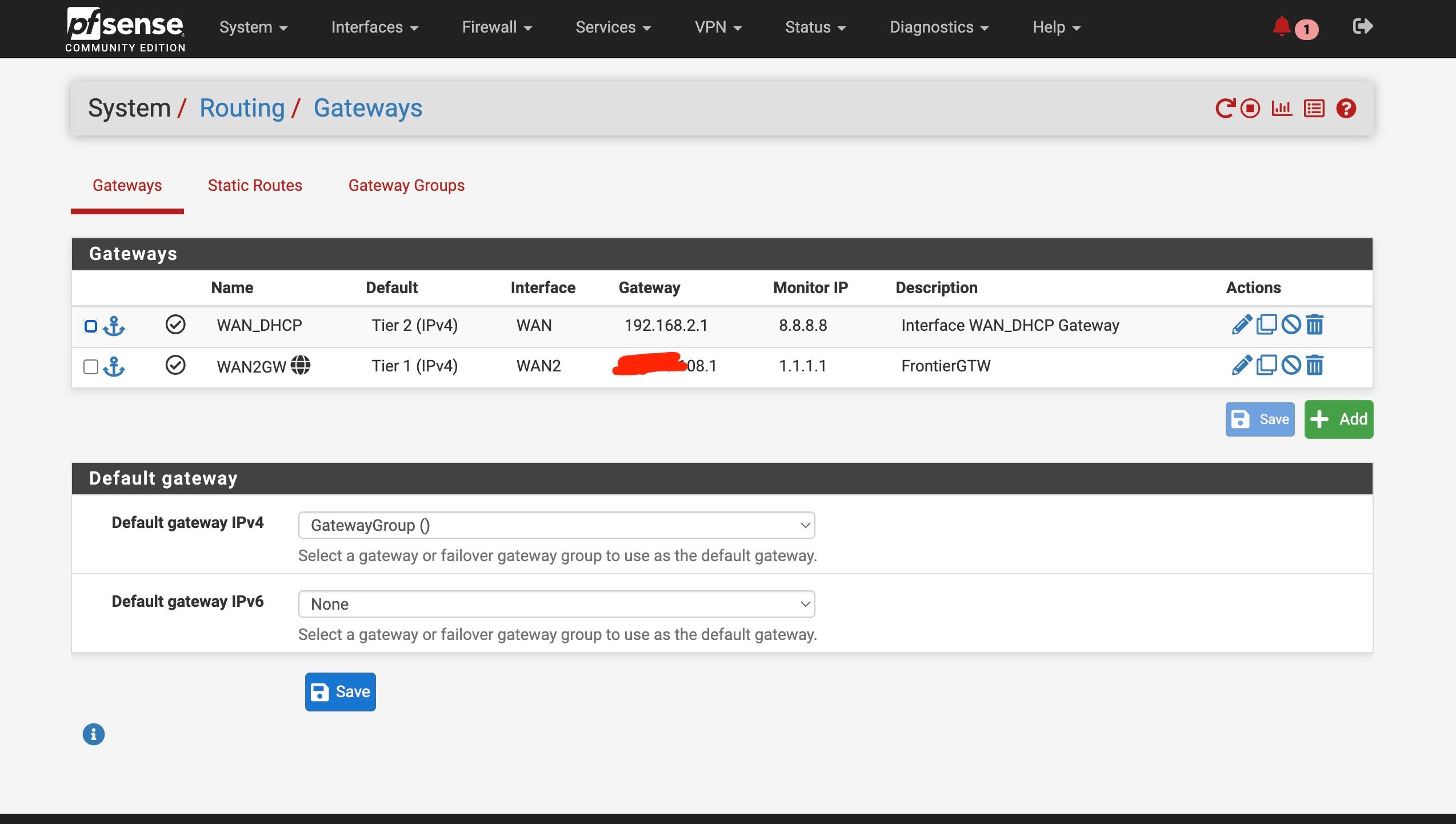
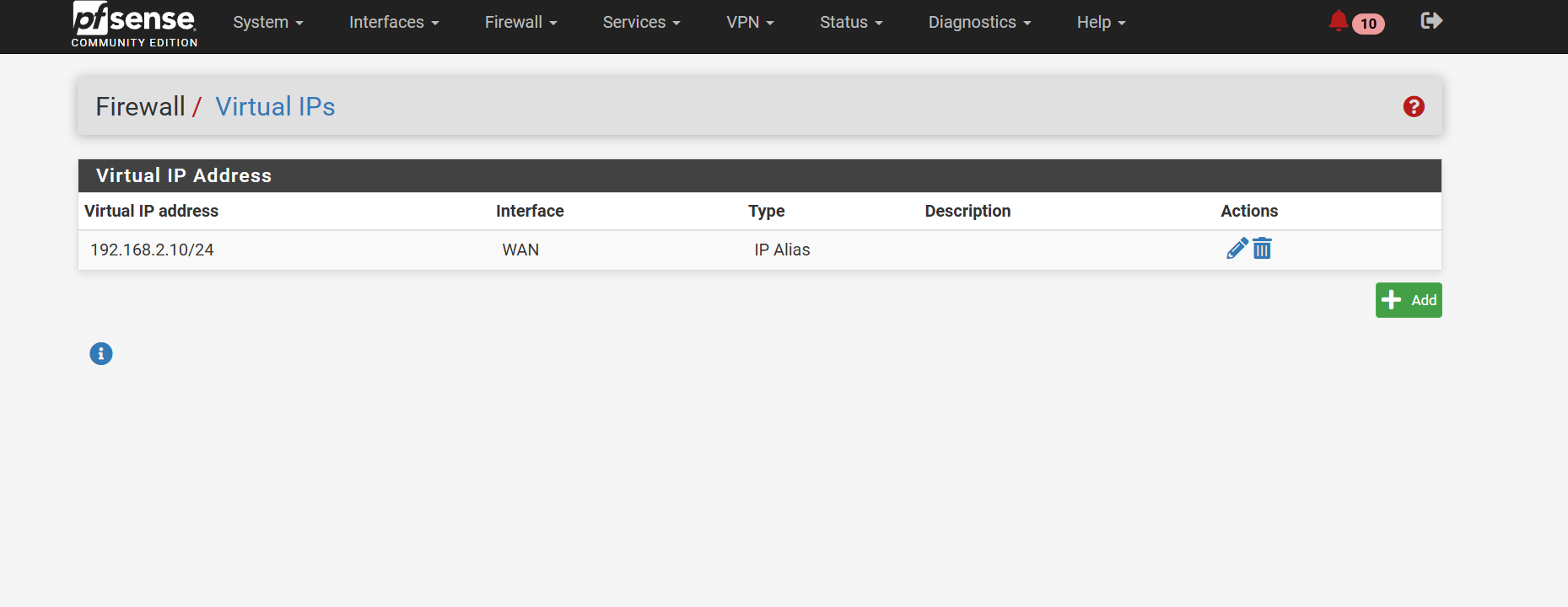
The VIP is good as long as the Nighthawk is using a different IP in the 192.168.2.0/24 subnet.
-
@stephenw10
So the Nighthawk is using 192.168.2.1
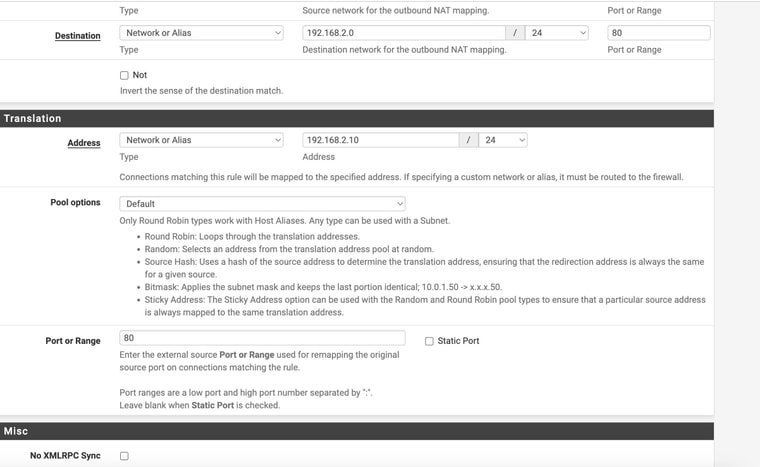
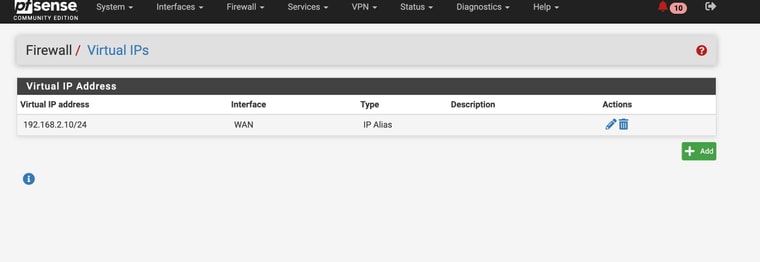
So my VIP needs to be somehting differnet in that subnet , like 192.168.2.10 ?Then I gotta figure out the outbound rule thing
-
@stephenw10
Should the VIP be setup on the WAN or the LAN interface??
Sorry probably sounds dumb -
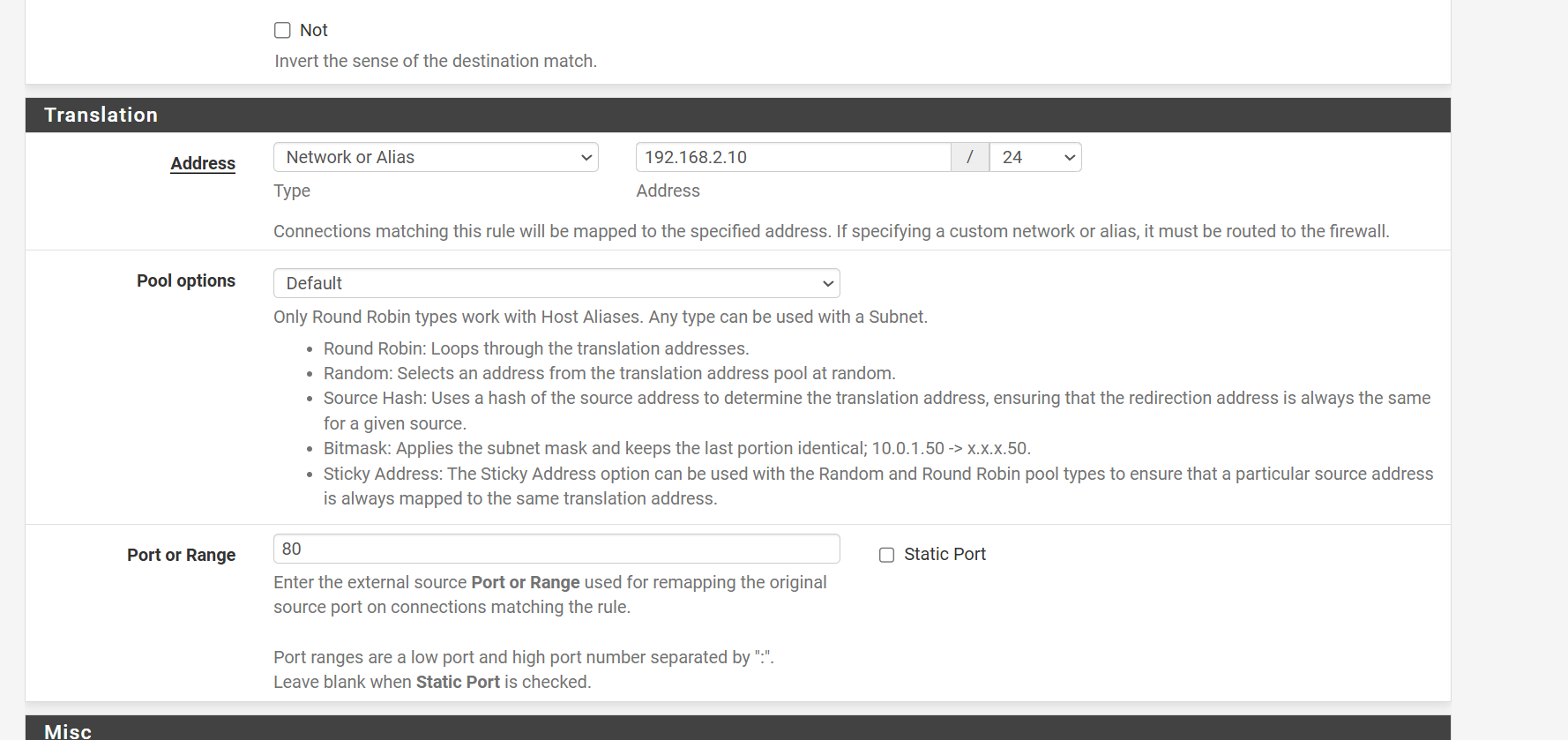
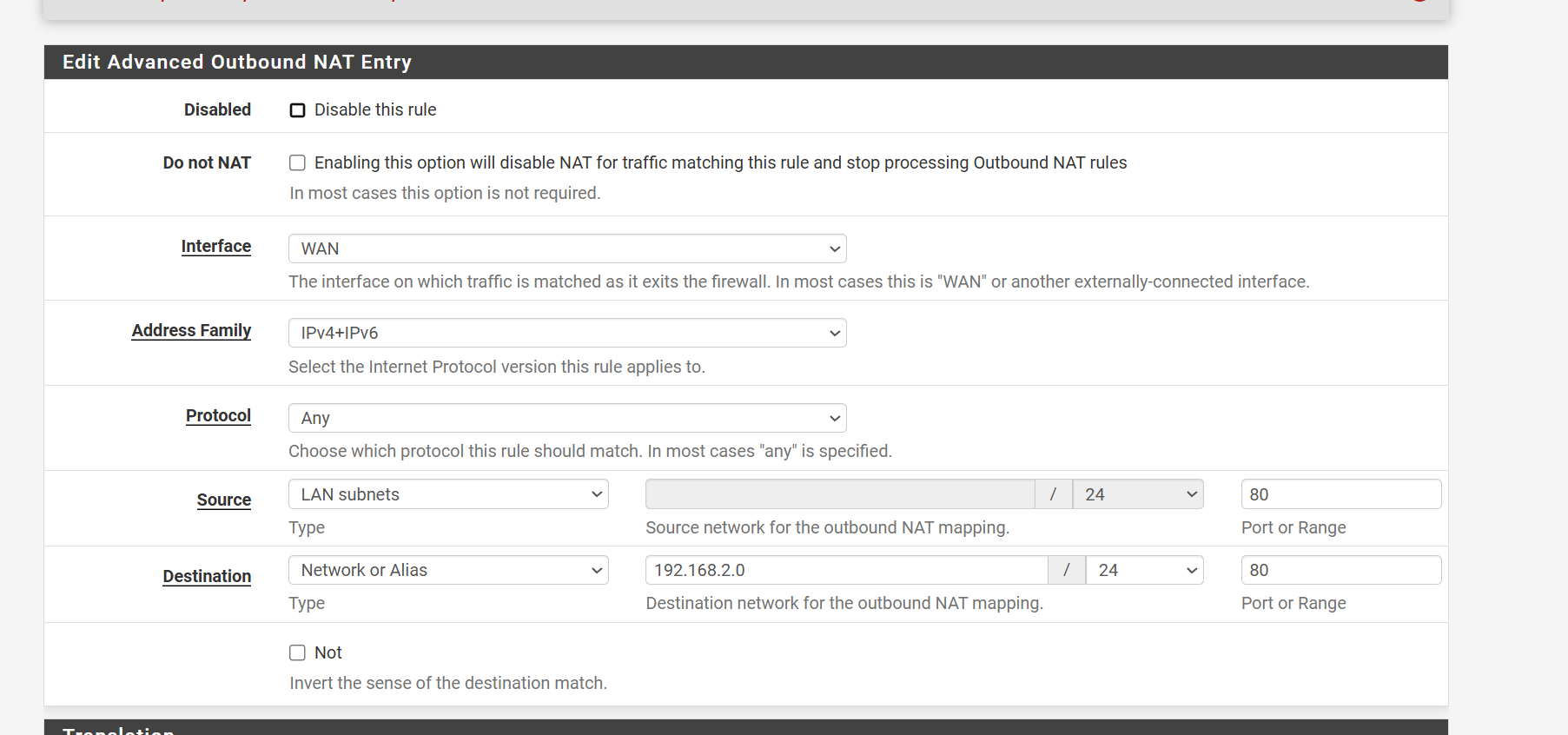
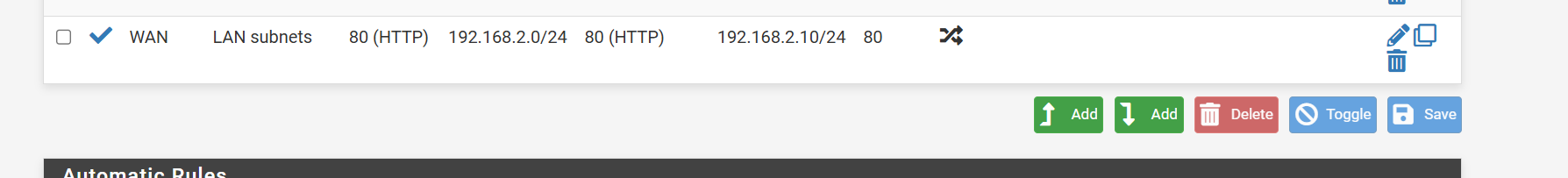
@stephenw10 ok this finally worked --- look ok??
-
Yup exactly like that.

-
Though the source port should be empty because that's the port the client uses to connect from which is usually some high numbered random port.
Also you should se https (or both) if the router supports it.
-
@stephenw10
So freaking weird
I made the change of the source port and then I could no longer access http://192.168.2.1
I can still ping the addressSo weird - I tried changing it back and it still wouldn't work
hitting my head lol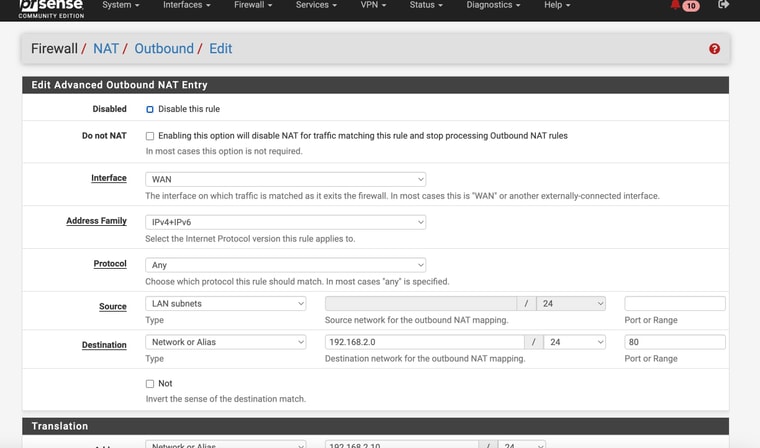
-
Hmm, odd. Try removing the ports entirely. There's no real reason to specify a port there, all traffic between LAN and the modem would need to be NAT'd.
-
@stephenw10 Well I tried to remove all the port entries and still no success
Whats really odd is that if I activate my Wireguard VPN into my network -- viola , I have access to http://192.168.2.1. (notice in my settings for the tunnel I have allowed IP ranges including 192.168.2.0/24
-
Hmm, almost sounds like that NAT rule is actually breaking the connection. Since with the source port set to 80 it would not have been matching the traffic.
Try disabling the rule.
-
@stephenw10 OMG!! That worked - after all that
Thanks again
-
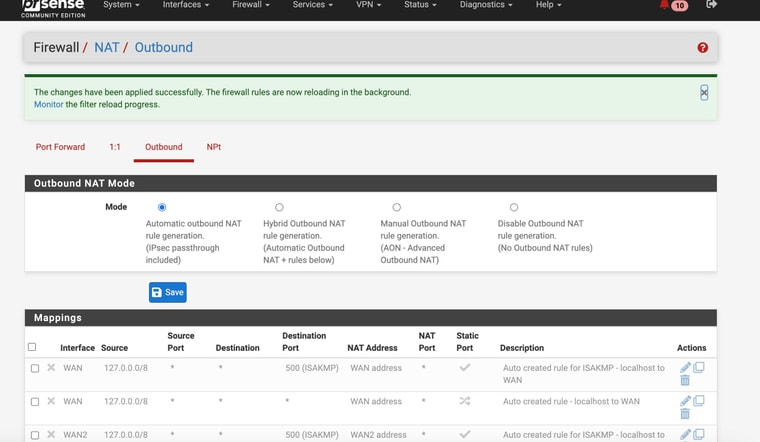
@stephenw10 Oddly I changed back to "Auto Mode" for Outbound NAT and it still worked
-
Hmm, interesting! That still using 192.168.2.1 to access it? It seems like the Nighthawk has a route to the public IP then. In which case that's no problem.
-
@stephenw10 yes still using 192.168.2.1
-
Should be fine then. Some modems do not require a NAT rules and can use the public IP on WAN to reply to.
-
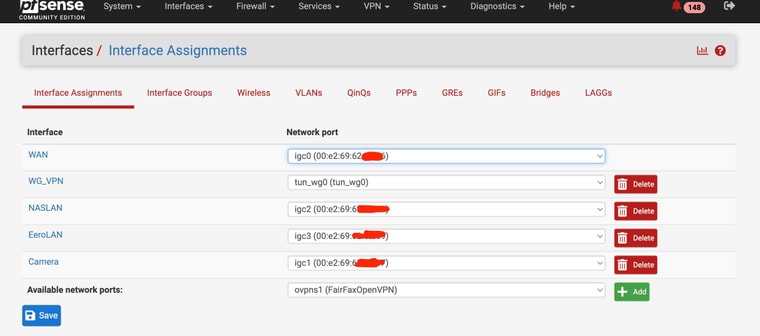
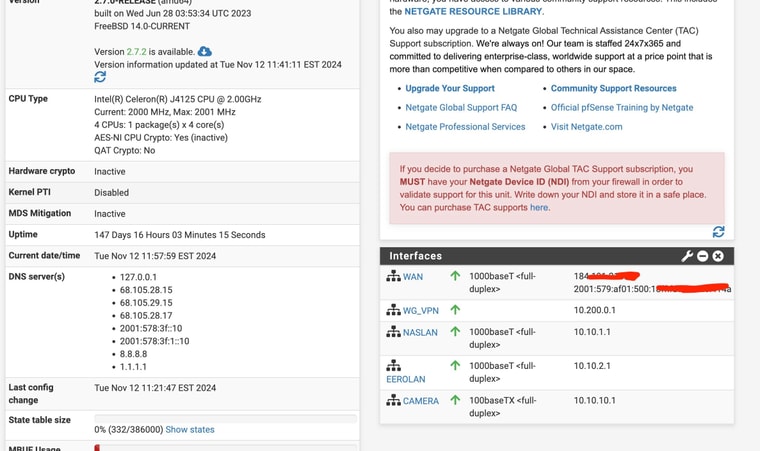
@stephenw10
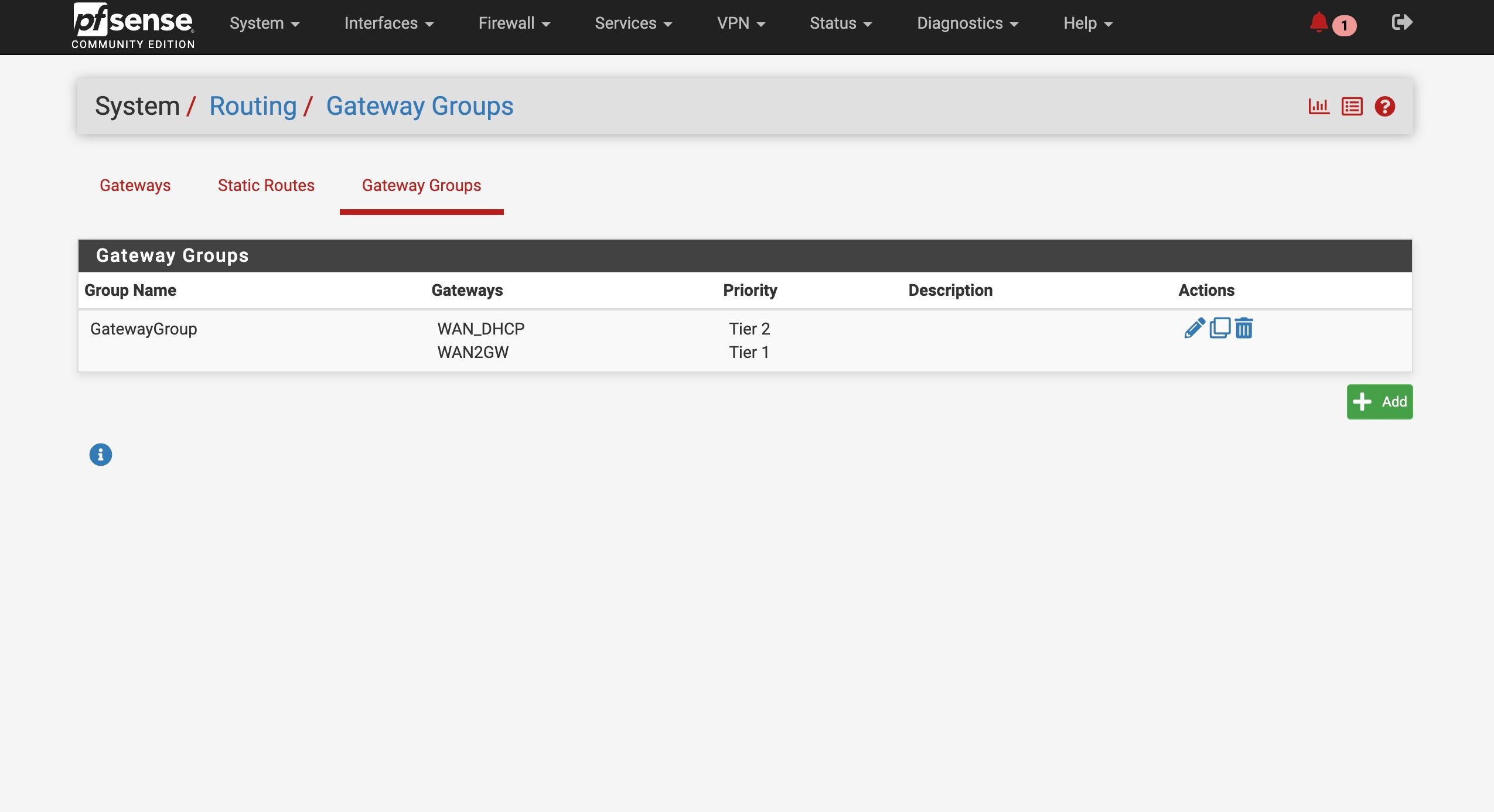
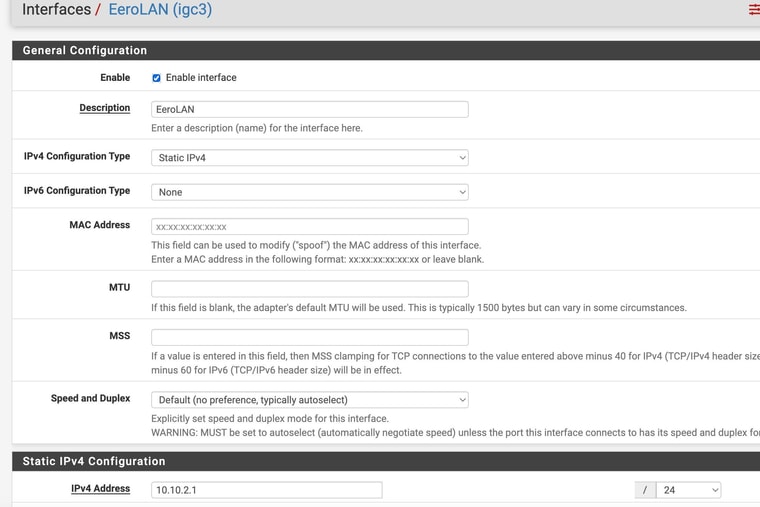
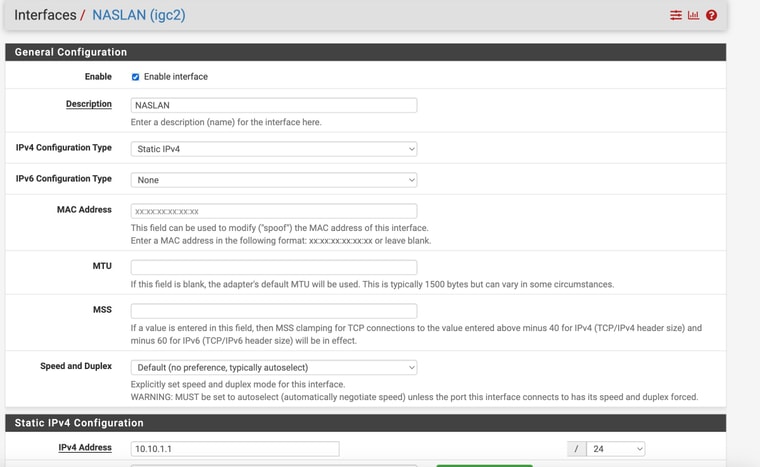
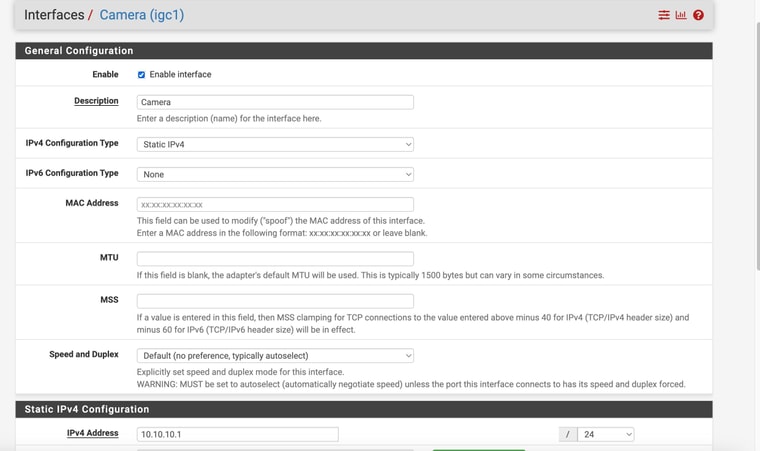
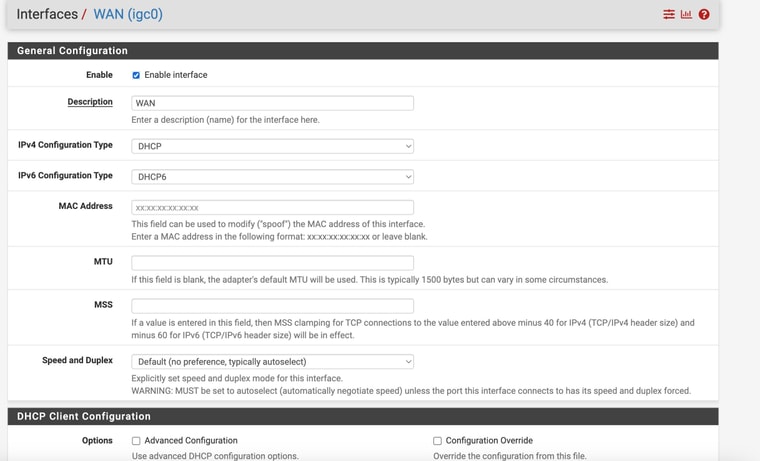
Now that I have survived that ordeal , lol (with you help) - I have to replicate the process at our second location.My pfsense device at that location only has 4 ethernet ports just like the one I have at location 1 - however, at location 2, I have all 4 ports used as per the pics. 2 are for security camera ports, one for and eero wifi and 1 for my NAS.
I have them on differnt networks.
What would be the best way to salvage my current equipment and still setup a failover internet (second WAN)? since my ports are filled
-
-
Add a VLAN capable switch and use it to separate some ports is what I would do there.
It might be possible to use the eero device to do that if it supports VLANs.
I assume you need to be able to filter between those three interal interfaces with different rules for each?
-
@stephenw10
Haven’t used VLAN for this but wanted to make sure == I could buy this $20 switch
Change maybe my pFsense Camera interface to a VLAN parent interface?
Connect to one of the switch ports
And then have one port assigned as the Camera VLAN
And then could I assign another VLAN port as the WAN2 connection for my ATT failover ??Would that work? Can a VLAN port be used as a WAN connection
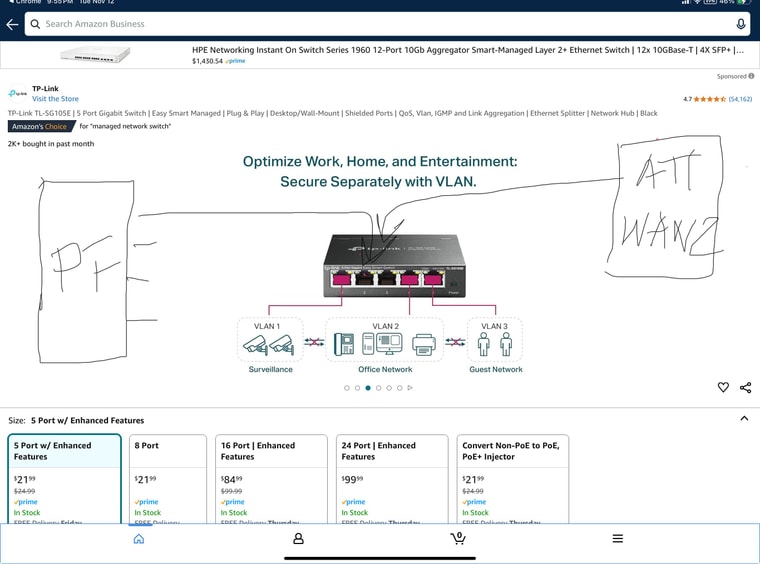
-
Yes exactly like that. The ports on the switch can be configured as access ports on different VLANs. The link to pfSense can carry all the VLANs. pfSense treats the VLANs as separate interfaces. And yes it can be a WAN, or any interface type.