pfsense doesn't block port on wan
-
Post your entire WAN rule set and tell us exactly what you are doing to test it.
I just tested this and your original assertion (that block rules to WAN address do not work) is incorrect. It works fine.
It is highly unlikely that you will discover a "bug" in port forwarding or the implementation of pf. It is almost certainly a misunderstanding or misconfiguration.
-
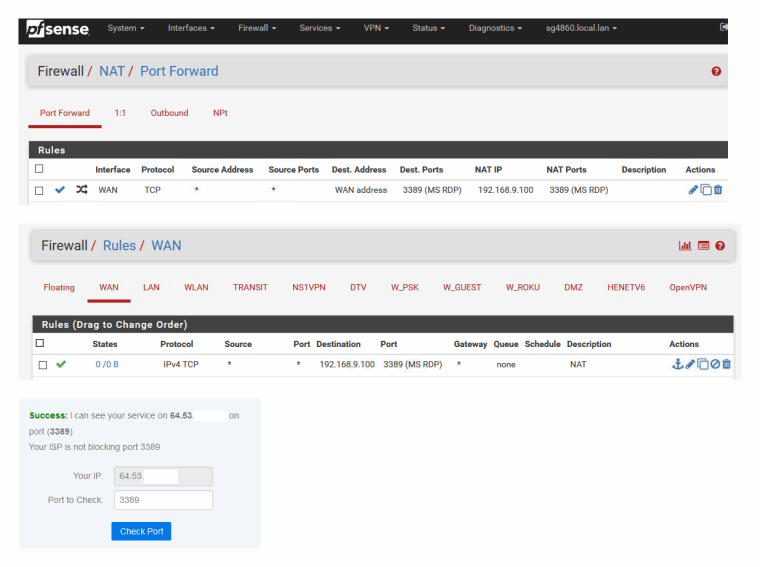
Firewall / NAT / Port Forward
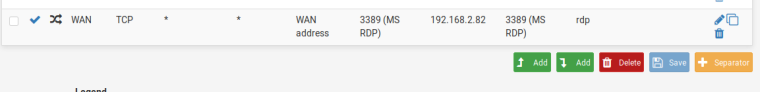
For example, I created a new NAT rule.
Destination port range: 3389
Redirect target IP: 192.168.2.82
Redirect target port: 3389
SaveFirewal / lRules / WAN
I can access this server from everywhere. Then I create a new WAN rule:
Action Block
Source address: 5.191.18.8
Destination: WAN address
Save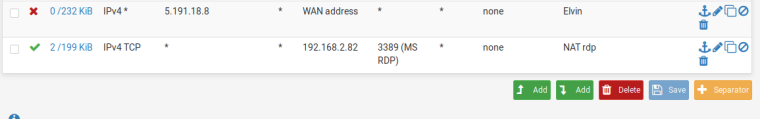
I lift this rule above the automatic created nat rule. Save. Eventually it should block access from this ip addres, but it doesn't block. If I choose "Any" in Destionation, then it blockes requests from this ip addres.
-
Nope. NAT has already happened before the firewall rules are consulted.
Block source 5.191.18.8 to destination 192.168.2.82 port 3389
If you were to, say, ping WAN Address from 5.191.18.8 with that existing configuration you will see that traffic blocked in the firewall logs because that traffic does not match the NAT so NAT is not performed and Destination WAN Address will match.
Destination Any matches 192.168.2.82 as well as WAN Address so the traffic is blocked even though NAT has happened first.
-
I can show you exactly when I give teamviewer id to you. Do you have a teamviewer program in your computer?
-
I just explained it all.
No, I won't teamviewer into your computer.
-
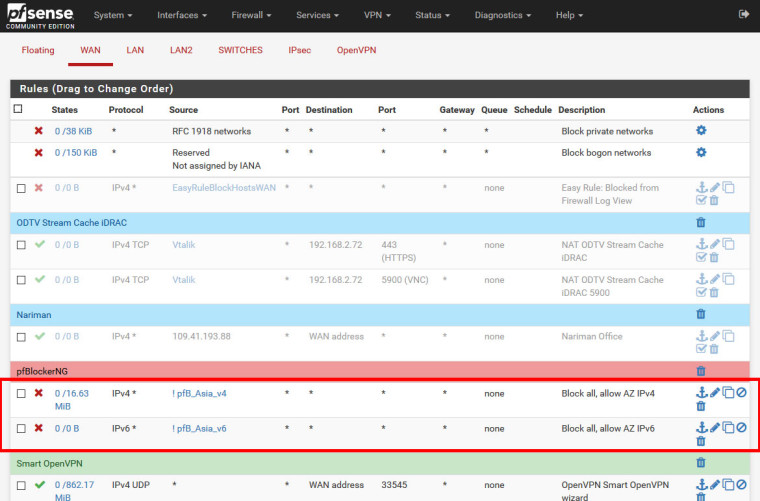
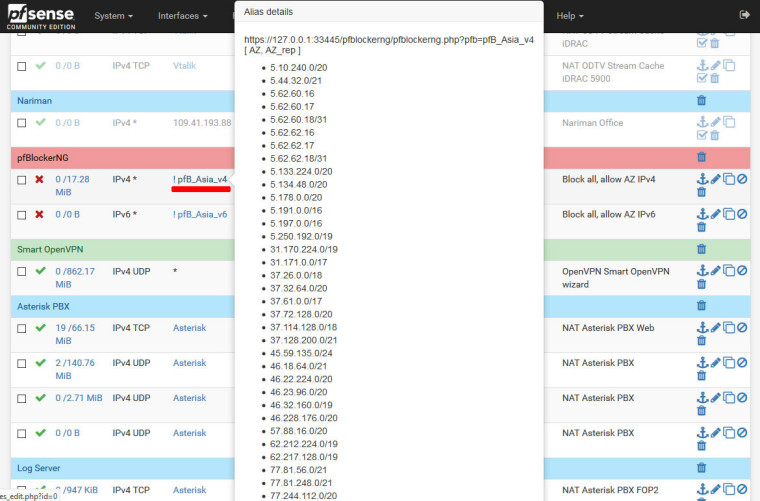
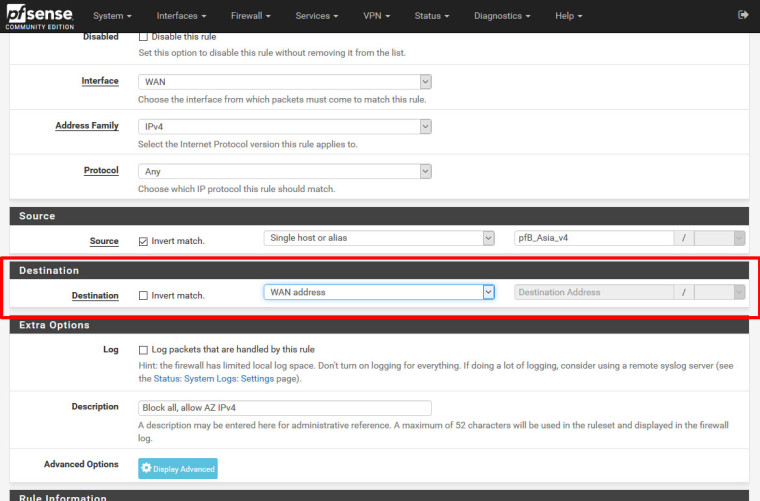
What I mean is: I have an Alias that should be blocked by pfsense.
In WAN rules, Alias is in the top of page, above all the rules. I have chosen to block all requests from this Alias. Destination address is "WAN Address". It doesn't block requests from this Alias. But if I choose "Any" in Destination, then it blocks all requests from this Alias. That's what I mean. Because I have used this rule in 2.4.3p1 and it used to work. Please do the same steps in your pfsense and you will see what I mean.
-
I explained exactly what is going on based on what you have posted.
I cannot explain to you that which is not shown. You are posting rules/screen shots for one thing, getting a complete explanation, then saying something else isn't working.
Does the table in Diagnostics > Tables contain the IP addresses you expect to be blocked?
Please show everything about that alias and the rules in question.
-
Today I will have a screen recorder and will attach the link here for your review.
-
Just post the rule sets, the contents of the alias, and what you think should be happening. Not going to watch movies.
-
Firewall / Rules / WAN Destionation is "any"
Alias
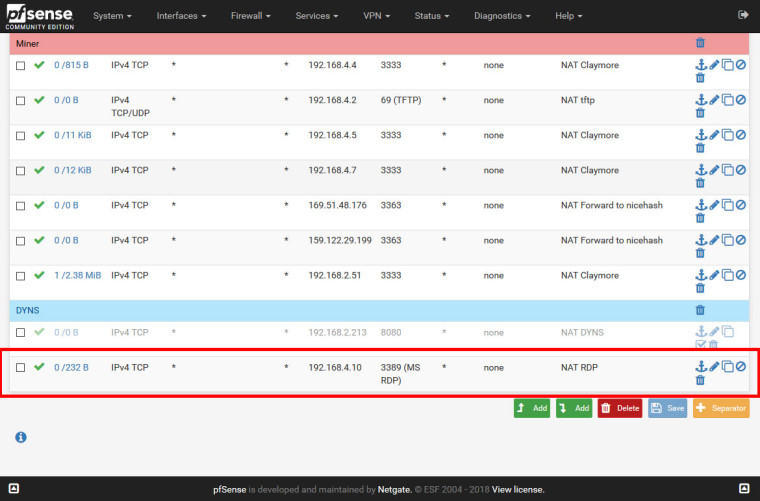
Firewall / NAT / Port Forward
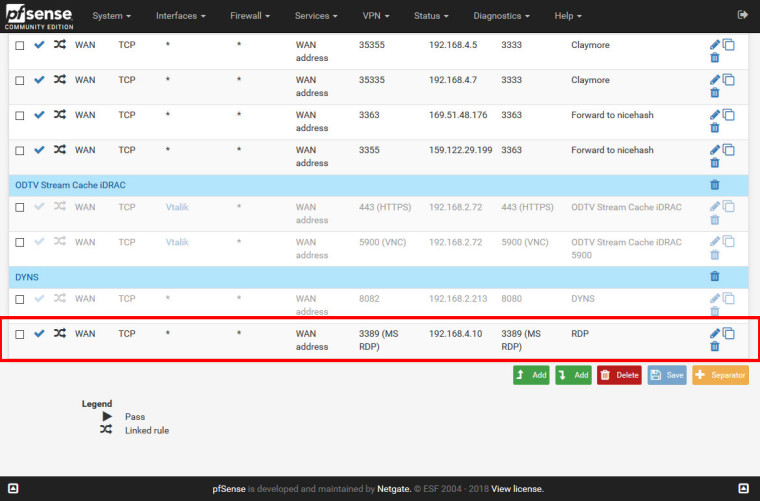
Firewall / Rules / WAN
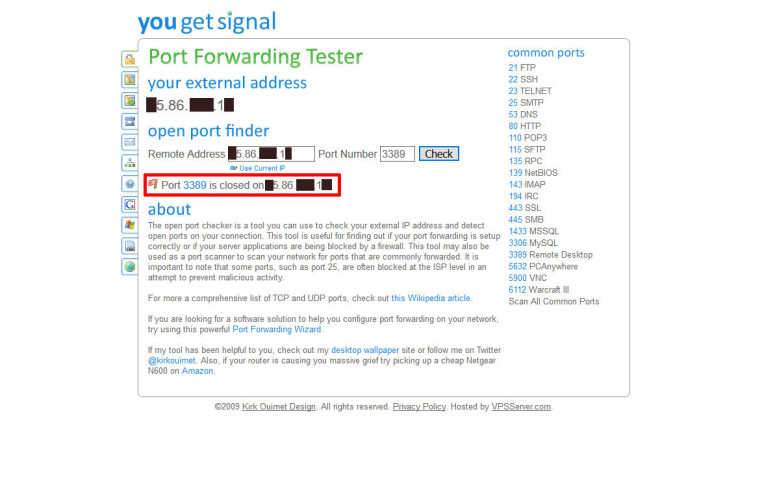
Port check
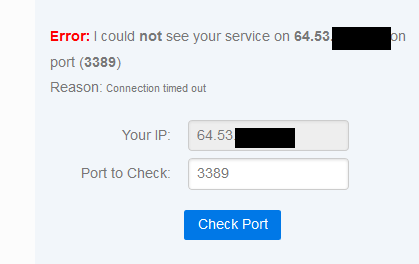
Firewall / Rules / WAN Destionation is "WAN Address"
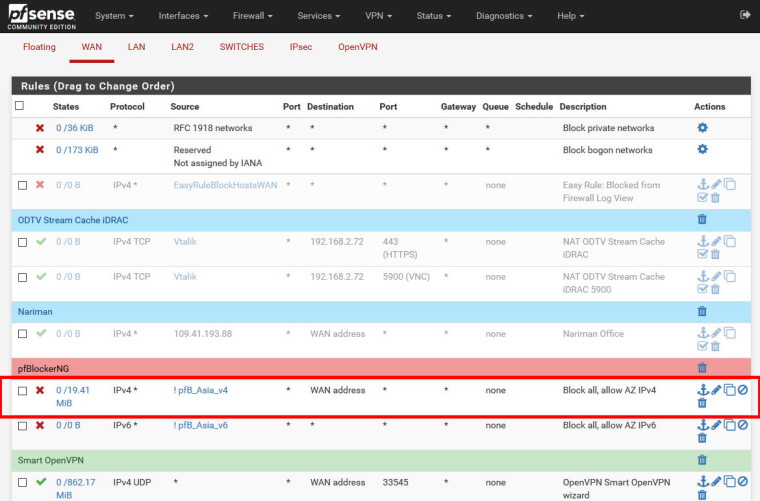
Port check
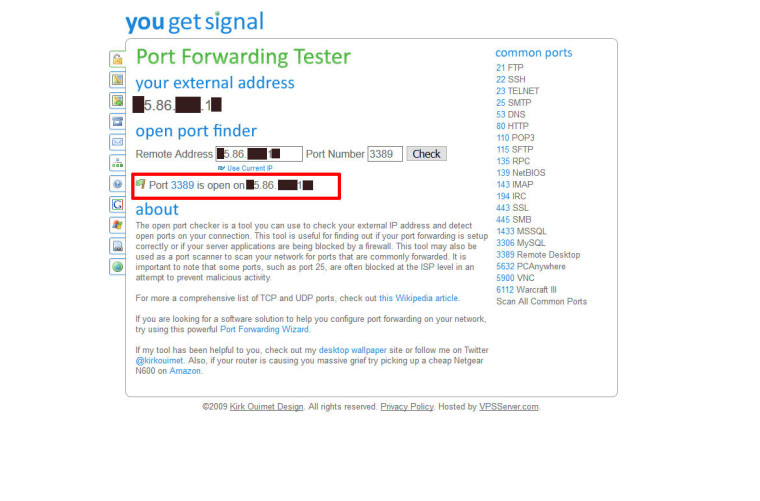
When Destination in WAN Rules is "any", pfsense blocks, but if Destionation is "WAN Address", pfsense doesn't block.
-
@emammadov said in pfsense doesn't block port on wan:
When Destination in WAN Rules is "any", pfsense blocks, but if Destionation is "WAN Address", pfsense doesn't block.
That is, as already explained above, because the NAT port forward has already changed the destination address.
Btw. opening RDP to the WAN is plain stupid, use a VPN for remote administration.
-
@grimson But it has been worked in 2.4.3p1 version.
-
No it didn't - atleast not the way you think it was..
-
Then, you mean, if I want to block source ip, I have to choose "any" in Destination address and if I allow source ip to my pfsense, then i have to choose "WAN Address" in Destination address, right?
-
Post your rules HOW they are set, and what is not happening.. Lan rules have ZERO to on what happens inbound to the WAN..
Your running pfblocker - and you have rules in floating that block traffic.. If so then they could be blocking access to your port forward..
Unless you are using a VIP address on your wan, port forward will always be to wan address - which is the default. It will auto create the firewall rule for you by default. If you to limit to a specific alias as source that has zero to do with the dest address and can be be used in your port forward rule.
-
I have sent you private message. By the way, I am using pfblocker, but Action in pfblocker is "Alias Native". I don't use floating rules.
-
Dude I am not going to watch a freaking movie.. You scrolling around your rules makes it IMPOSSIBLE to see what might or might not be wrong.
Its this simple post your port forward, post your wan rules. Post your floating rules. (if nothing in there - still post them).. State what doesn't work.
https://www.netgate.com/docs/pfsense/nat/port-forward-troubleshooting.htmlJust because your port test says not open doesn't mean the port forward didn't work btw. Maybe your client not listening or sending back RST because it doesn't allow rdp from IP other than its local lan, etc.. Run through the troubleshooting guide..
Port forwarding to 3389 is this simple.
Once I remove the rule - bam its BLOCKED!! You have to kill any open states that might exist..
-
You approached. Now create a rule on wan interface, select block in action, add a public ip address you know to the source, choose "wan address " in destination, save and drag it to the above of the rule you created for rdp. You will see that ip addresses in source still can access your server via rdp, but if you select "any" in destination in the rule of wan address, pfsense will block the traffic from that public ip address.
-
Man. NAT HAPPENS BEFORE FIREWALL RULES ARE EVALUATED! WAN ADDRESS WILL NOT MATCH AS A DESTINATION ADDRESS FOR TRAFFIC MATCHING THE PORT FORWARD! THE DESTINATION ADDRESS HAS BEEN TRANSLATED TO THE SERVER ADDRESS!
-
As Derelict has been trying to tell you for this whole thread. Now create your firewall rule with dest of your IP of your nat, ie 192.168.x.x
Put that above your rule that allows it.. And that IP would be blocked.