Setting reversed proxy
-
Hello,
I have a box running pfSense with OpenVPN ( port 443 ), pfBlockNG ( DNS blocking) and ACME
Have 3 dyndns host names setuppfsense1337.dyndns.org ( used for OpenVPN )
web1.dyndns.org
web2.dyndns.orgHave now setup 2 web servers on LAN that I want to access with both https(443) and http( port 80 for auto renew CA from Let's Encrypt).
Both have there own CA using Let's Encrypt.I have tried to read the wiki for HAProxy but couldn't grasp how do set that pkg for my.
Anyone have a guide or something that explains the logic how it works?
Second should the CA for each web server should the be on the pfSense boxa as well ?TIA
Daniel -
@varazir
Something like this looks like it would work: https://314es.pl/https-openvpn-and-ssh-on-one-port-thanks-to-haproxyThe "frontend main" would be able to make further switching decisions for different web1 / web2 servers.. Might need to use of a few custom acl's in the webgui to make it the same.
-
@piba Hmm, something like that
I have tried to follow this guide but no luck
https://github.com/PiBa-NL/pfsense-haproxy-package-doc/wiki/pfsense_2_3_haproxy_sni_plus_offloading_backends#frontend-2
-
@varazir
Can you share the haproxy.cfg you configured? Might be able to see what part needs to be adjusted.. Please also explain what part does work and what doesnt if health-checks are passing (servers shown in green) in stats page and if not with what LastChk message. -
@piba Where is it saved in pfsense ?
-
@varazir
its visible at the bottom of the haproxy settings tab. -
@piba Ahh missed that
Here it is
https://gist.github.com/varazir/319b50bef3e4de1284ef52b38aaf5e23 -
@varazir
Okay, and what part does and what doesnt work with that config?First thoughts.:
-disable the 'ssl encryption' on all 3 servers (since you didnt decrypt the traffic on the frontend there is no need to encrypt it again before sending to the backend)
-enable 'ssl health-check' on the 2 webservers, to make it pass checks again
-change healthcheck for openvpn to be 'tcp check' i dont think it would show as 'up' otherwiseCheck that all 3 servers are shown as 'up' on the stats page
After that i think at least the 2 webservers should be reachable.. the openvpn might still not be..
Please share config again and tell what does/doesn't work.
-
disable the 'ssl encryption' on all 3 servers (since you didnt decrypt the traffic on the frontend there is no need to encrypt it again before sending to the backend)
I wan't it to be encrypted traffic.
-
@varazir
Yes the client is sending encrypted traffic, the frontend as you configured it does NOT decrypt the traffic. So you can forward that traffic as-is to the webserver and it will still be encrypted.It shouldn't be encrypted twice, as the webserver will not understand the request then after decrypting it once..
-
I got one of the web servers to work but not the other one, the one I redirect to port 446.
It reports that server is down
Edit: I got Openvpn servar as online changing to Basic Health check.
But I get Transport error when I try to connect with my OpenVPN client.
TCP recv EOF -
ok got both of the web servers to work I had to change the Health checking to basic and enable SSL checks
-
@varazir
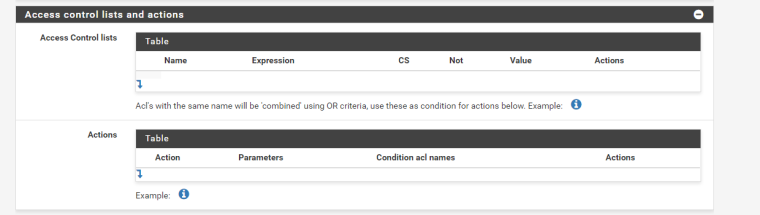
Though it works its probably better to change health-check's for the webservers back to http, and see what the LastChk column in stats says. Might be a forbidden method, or a authentication required, or it needs a sni indication in the check request, or a host header, or something. That is the thing to change and or fix to make health-checks pass on a webserver.As for the openvpn connection, i expect it is not actually sending a proper ssl encapsulated request.. As such you might need a 'special' acl where you could put the "!{ req.ssl_hello_type 1 } !{ req.len 0 }" in the acl for that use_backend action that might make it sellect the right backend, and allow it to connect.
Can you share the config as you got it now?
-
I have updated my Git https://gist.github.com/varazir/319b50bef3e4de1284ef52b38aaf5e23
The web2 keeps getting "active or backup DOWN for maintenance (MAINT) "
When I update the setting it works fine for a min or 2.Not sure where to add "!{ req.ssl_hello_type 1 } !{ req.len 0 }"
I guess there
-
I removed the check on web2
-
@varazir
What did stats page LastChk say when it was down? (hover over it with your mouse) -
@varazir
Instead of thisuse_backend Octoprint_ipvANY if Octoprintmake that like:
use_backend Octoprint_ipvANY if !{ req.ssl_hello_type 1 } !{ req.len 0 } -
That is from the config file trying to find how to set it in the GUI :P
-
@piba When it's working it say Layer7 check passed: OK
-
@varazir
You already wrote 'Octoprint' in that same textfield you can put the other acl text..As for above maint line it looks like the 'zwave' servername might not resolve DNS easily to a IP? That shouldnt depend on the type of check used anyhow.. Perhaps give it a few seconds more to resolve? And the check again? A L7 check that passes would be good..