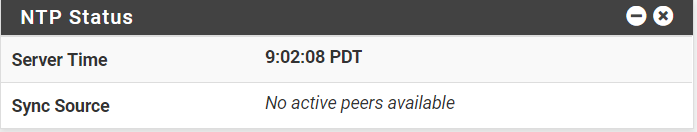
NTP Not Working [SOLVED (totally)]
-
@beremonavabi
It doesn't look like it's a DNS issue, either. I stuck the actual IP address for a public DNS serverhttp://support.ntp.org/bin/view/Servers/PublicTimeServer000011
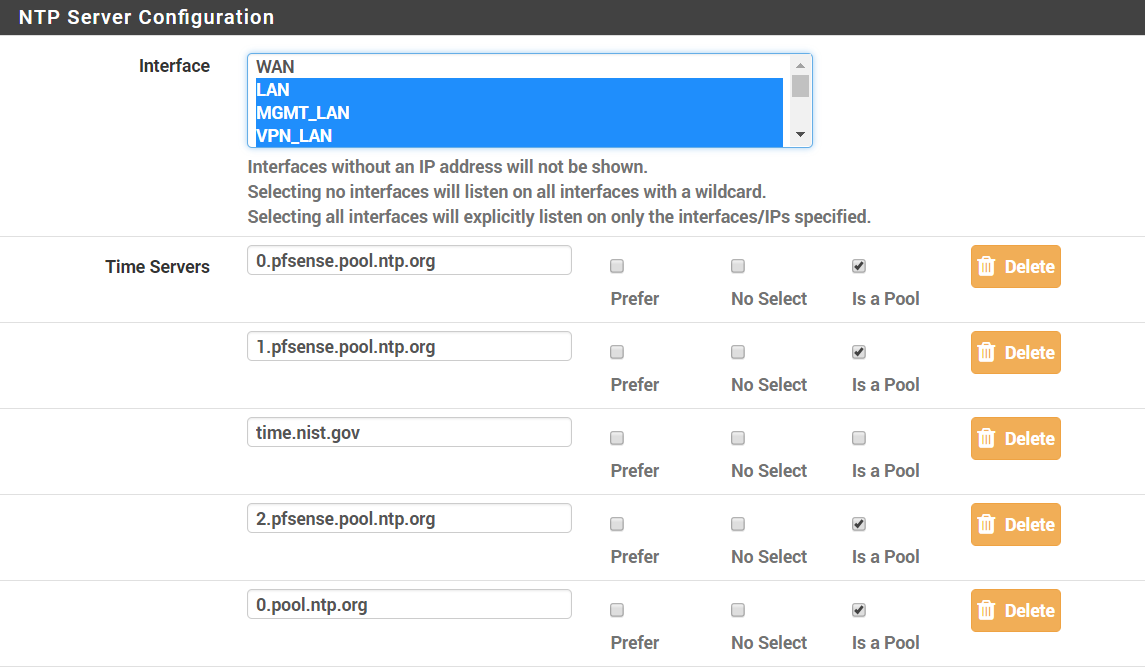
in and removed the WAN interface. Same problem: NTP doesn't start. Put the WAN back in the list and all was well.
-
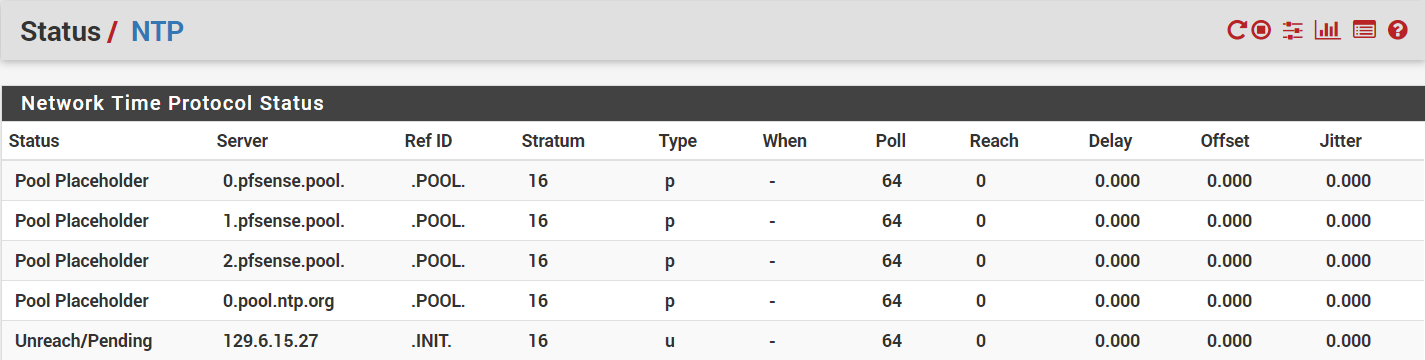
Still not working without WAN selected in Settings > NTP. For posterity, here's some information on my gateways:
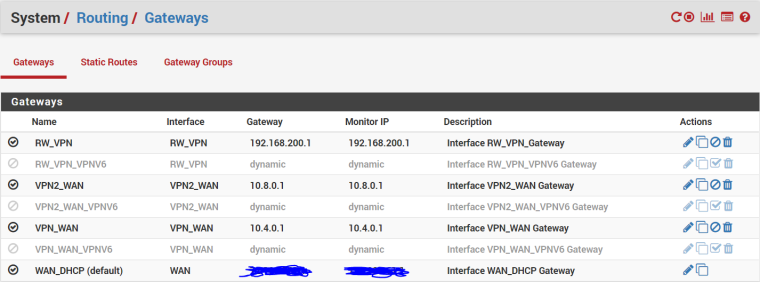
RW_VPN is my VPN server, VPNx_WAN are my two VPN clients, IPv6 is off so all the IPV6 gateways are disabled, and I've scribbled over my WAN_DHCP addresses for privacy purposes.
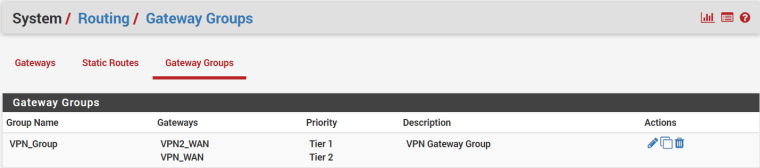
I've also got a Gateway Group:
-
See that other thread on how dicked up the other guys setup was to why it wasn't working.. A clue to why yours isn't working is prob in there as well.
-
@beremonavabi said in NTP Not Working [SOLVED (mostly)]:
RW_VPN is my VPN server
Huh? Why would you vpn server your running on pfsense be setup as a gateway?
Looks like he is shooting himself in the foot same way other guy was... Manual mode outbound nat and not natting what the ntp is trying to use as the source IP, etc.
And for what reason are you using manual for your outbound nat?
-
Just thinking and typing out loud :
Is this not just another case of trying to pass everything through the VPN tunnel ?
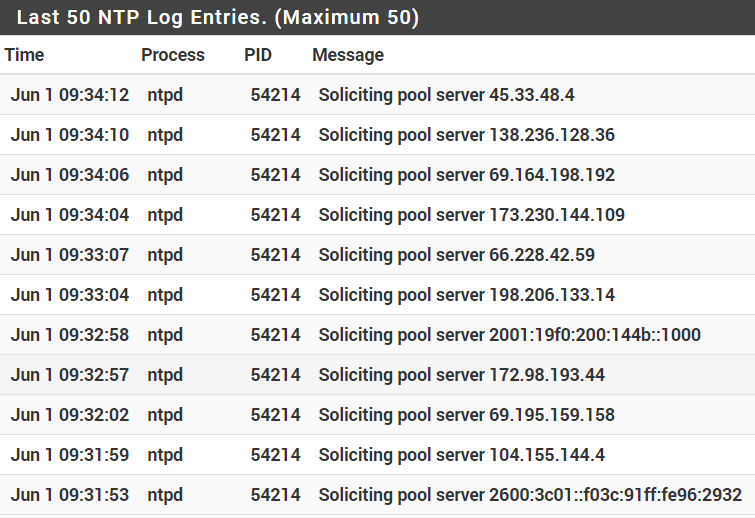
Knowing that the ntp deamon probably starts before the VPN server, it will work for a while : the WAN connections works, (NAT) rules are fine.
Then the VPN server starts, the gateways are shot in the back and reconstructed, so that all traffic goes out of the VPN, the new "WAN".
Our ntp isn't informed, and is locked out.Something like that ?
-
Firewall > NAT, Outbound tab. Add rule to top.
- Disabled: Unchecked
- Do not NAT: Unchecked
- Interface: WAN (make one of these rules for each WAN)
- Protocol: any
- Source: This Firewall (self)
- Destination: any
- Not: Unchecked
- Translation Address: Interface Address
- Port or Range: Blank
- Description: NAT anything out from the firewall itself
-
@jimp said in NTP Not Working [SOLVED (mostly)]:
Firewall > NAT, Outbound tab. Add rule to top.
Disabled: Unchecked
Do not NAT: Unchecked
Interface: WAN (make one of these rules for each WAN)
Protocol: any
Source: This Firewall (self)
Destination: any
Not: Unchecked
Translation Address: Interface Address
Port or Range: Blank
Description: NAT anything out from the firewall itselfYay! Thanks, jimp. That got it. I had to reboot the pfSense box before it would work, though. I'd tried something similar a couple of weeks ago, but it was limited to UDP on port 123, was at the end of my list of outbound NAT rules, and, probably most importantly, I didn't reboot the box.
-
You probably didn't need to reboot, just clear the states table (Diagnostics > States, Reset States tab)
-
@jimp This rule does not work for me. Rather, it works, but before the first reboot of PfSense.
-
Then you have a different issue than the OP of this thread. Start a new thread with details about your own setup.
-
T tjsober referenced this topic on
-
T tjsober referenced this topic on
-
T tjsober referenced this topic on
-
 P planedrop referenced this topic on
P planedrop referenced this topic on
-
 P planedrop referenced this topic on
P planedrop referenced this topic on
-
 P planedrop referenced this topic on
P planedrop referenced this topic on