Netgate shared root with ISP? ¯\_(❞⦈)_/¯
-
@TheHowTo said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
After that they changed my PfSense settings (e.g. disabling some firewall rules, changing DNS, DHCP and so on).
Well that's complete nonsense, and doesn't happen with a NORMAL install of pfsense. And when I say normal, I mean, you didn't turn off the top 2 deny rules for the WAN interface:
- Block private networks
- Block bogon networks
Show us a screenshot of your WAN rules, and mask out any sensitive information.
-
ttyv0is the physical video console. Nobody can login to that remotely. It can only be accessed via keyboard and monitor. Similarly,ttyu0is a serial (uart) console and cannot be logged into remotely, only via local serial connection.Seeing a login on
ttyv0just means the menu redrew itself. If you see it a lot, something is probably corrupted on your filesystem leading to a problem with the tty itself.Nobody has shared root access with your ISP or anyone else. There are no backdoors.
-
@stephenw10 said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
So the logs you are seeing are like, for example?:
Aug 16 12:14:22 syslogd kernel boot file is /boot/kernel/kernel Aug 16 12:14:22 kernel done. Aug 16 12:14:23 php-fpm 343 /rc.start_packages: Restarting/Starting all packages. Aug 16 12:14:24 login login on ttyv0 as root Aug 16 12:15:34 check_reload_status rc.newwanip starting igb0 Aug 16 12:15:35 php-fpm 343 /rc.newwanip: rc.newwanip: Info: starting on igb0.That is expected and not an indication some bad actor is connected to your firewall as that link shows.
Steve
Thanks Steve, but that is not what I see. Your log indicated services restarting because wan dhcp lease renewal process.
Ok, let just say there are no bad actors.Would you please explain to me the Unexplained Phenomena, like why I see my floating firewall rules being changed, some were edited and some deleted (e.g. AmazonAWS IP Range) with log messages: "Syncing firewall, Reloading filter"?
-
When logging in to the GUI, you'll see this :

Logging in using a ssh client :
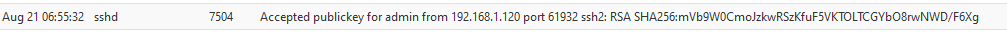
The IP's "192.168.1.120" and "2001:470:1f13:5c0:2::84" are both the ones from my LAN network.
Let's say : it's an inside job. It's me using a device on my LAN.Btw : great : your ISP is helping you administrating your pfSense ?!!
What are your WAN firewall rules ? Or did you install a KVM module for them so they can remotely using a keyboard / VGA ? ( @jimp : people often omit to mention the most incredible details about their installation ) They have a OpenVPN access for remote administration ?For me, it just an inside job. Or the (one of) the other you(s).
-
@TheHowTo said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
I see my floating firewall rules being changed, some were edited and some deleted
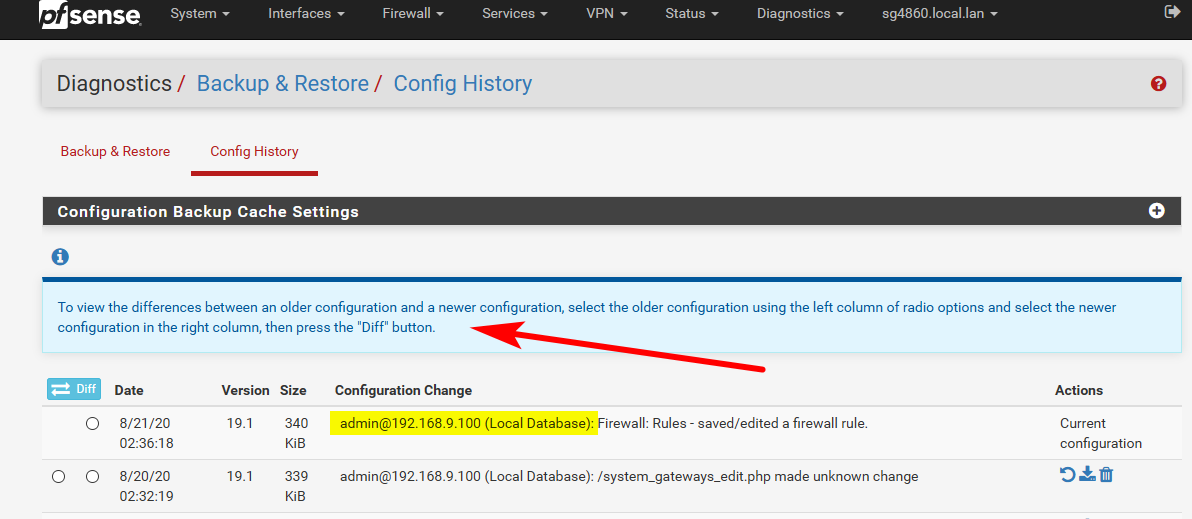
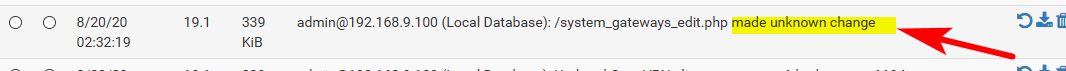
And what does your config history show.. example
-
@TheHowTo said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
Would you please explain to me the Unexplained Phenomena, like why I see my floating firewall rules being changed, some were edited and some deleted (e.g. AmazonAWS IP Range) with log messages: "Syncing firewall, Reloading filter"?
Maybe you have something like pfBlockerNG which is automatically managing your rules? It does exactly those kinds of things.
-
I was thinking the same thing... While pfblocker is a great package, I am not a fan of anything that auto manipulates rules.. I use it really as just fancy aliases management - I have it create the aliases, and then I use those in my rules as I want.
But I would have to assume any changes to rules would be listed in the configuration history, but since I don't have pfblocker manipulating my rules, not sure how that would look in the log?
-
What I know and experienced, pfBlockerNG only prioritizes their rules in floating rules order, but it never deleted any custom rules.
If you do not believe me, try to install pfBlockerNG, make custom rules to block AmazonAWS (hackers virtual machines) and then do a cron update.
Here is AmazonAWS’s IP range: AWS IP address ranges -
And did you bother to look in your config history... Anything that changes the config should be listed there..
-
@johnpoz said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
And did you bother to look in your config history... Anything that changes the config should be listed there..
Config history says "Edited a firewall alias, made unkown change" However I did not login to SSH or GUI at that specific time.
It does not matter anymore because even after factory reset, everytime the hackers knew how to bypass the password protection.
I still give Netgate the benefit of doubt. Maybe there are some bugs or loopholes (e.g. superuser's backdoor) in PfSense version 2.4.5-p1.I really wish that I can hardening PfSense with Firejail and Apparmor.
-
@TheHowTo said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
"Edited a firewall alias, made unkown change"
And what did it say did that that unknown change.. Post a screenshot of your config history showing these changes..
OMG - I've been hacker3d
-
@johnpoz said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
And what did it say did that that unknown change.. Post a screenshot of your config history showing these changes..
OMG - I've been hacker3d
Gotcha!
-
@stephenw10 Would you please tell Dev to fix these loophole (superuser's backdoor) and bug (openvpn over tcp) on the next PfSense version.
Thank you. -
OMG dude - there is not a "superuser" backdoor.. And what bug in openvpn over tcp... It work it just fine. Where is the redmine link to this "bug"??
-
If you think you have found a bug (you almost certainly haven't) then you should open a redmine ticket with the details and how to replicate.
You are going to have to present some evidence though. There is no reason you can't post screenshots of your config history or system log text with your public IPs removed. That gives away nothing that you should care about.
Otherwise it just looks like you're trolling. We will have to lock the thread.Steve
-
Hi all, I had similar problem with (2.4.5-p1) openvpn running over TCP specifically the client site. You need to edit your openvpn.inc file to fix this.
@johnpoz said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
OMG dude - there is not a "superuser" backdoor.. And what bug in openvpn over tcp... It work it just fine. Where is the redmine link to this "bug"??
-
@C3G3K4 said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
You need to edit your openvpn.inc file to fix this.
And where is the link to this bug report? Or even the thread discussing this issue, or what exactly did you change.
And lets be specific.. Stating there is a "bug" in openvpn tcp, as a client to to some vpn service? With site 2 site? I run tcp client to pfsense from my phone, from my pc at work over tcp and have not seen any "bugs" or issues at all.
Saying there is a "bug" doesn't help anyone nor is going to get anything fixed if there is an actual issue.
-
i don't intend to feed the troll, reported him for 3 post without any meaning, registered 27 minutes ago,I start collecting bets, 5$ .. he's a spammer
-
Hi all, I am just trying to help and contribute, but why do I get aggressive and hostile treatments?
If you do not know how to edit an openvpn.inc file, then I suggest you have to wait for the next pfsense version. Don’t falsely accused someone, specially without established proof.Anyway, my family and I believe, good acts will have good consequences, bad acts will have bad ones. You'd think by now people would understand…
that you reap what you sow.Happy Sunday Everyone.
-
What did you have to change in the client side config file?
How did the issue present before you made that change?
I'm not aware of any OpenVPN TCP issue in 2.4.5p1, if you have found something you should open a redmine bug report: https://redmine.pfsense.org/
Steve