Netgate shared root with ISP? ¯\_(❞⦈)_/¯
-
I was thinking the same thing... While pfblocker is a great package, I am not a fan of anything that auto manipulates rules.. I use it really as just fancy aliases management - I have it create the aliases, and then I use those in my rules as I want.
But I would have to assume any changes to rules would be listed in the configuration history, but since I don't have pfblocker manipulating my rules, not sure how that would look in the log?
-
What I know and experienced, pfBlockerNG only prioritizes their rules in floating rules order, but it never deleted any custom rules.
If you do not believe me, try to install pfBlockerNG, make custom rules to block AmazonAWS (hackers virtual machines) and then do a cron update.
Here is AmazonAWS’s IP range: AWS IP address ranges -
And did you bother to look in your config history... Anything that changes the config should be listed there..
-
@johnpoz said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
And did you bother to look in your config history... Anything that changes the config should be listed there..
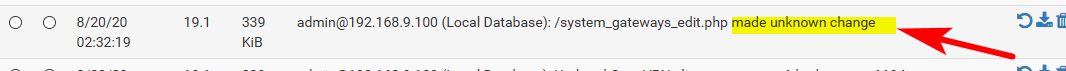
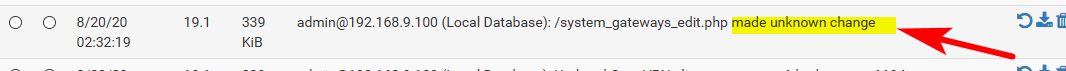
Config history says "Edited a firewall alias, made unkown change" However I did not login to SSH or GUI at that specific time.
It does not matter anymore because even after factory reset, everytime the hackers knew how to bypass the password protection.
I still give Netgate the benefit of doubt. Maybe there are some bugs or loopholes (e.g. superuser's backdoor) in PfSense version 2.4.5-p1.I really wish that I can hardening PfSense with Firejail and Apparmor.
-
@TheHowTo said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
"Edited a firewall alias, made unkown change"
And what did it say did that that unknown change.. Post a screenshot of your config history showing these changes..
OMG - I've been hacker3d
-
@johnpoz said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
And what did it say did that that unknown change.. Post a screenshot of your config history showing these changes..
OMG - I've been hacker3d
Gotcha!
-
@stephenw10 Would you please tell Dev to fix these loophole (superuser's backdoor) and bug (openvpn over tcp) on the next PfSense version.
Thank you. -
OMG dude - there is not a "superuser" backdoor.. And what bug in openvpn over tcp... It work it just fine. Where is the redmine link to this "bug"??
-
If you think you have found a bug (you almost certainly haven't) then you should open a redmine ticket with the details and how to replicate.
You are going to have to present some evidence though. There is no reason you can't post screenshots of your config history or system log text with your public IPs removed. That gives away nothing that you should care about.
Otherwise it just looks like you're trolling. We will have to lock the thread.Steve
-
Hi all, I had similar problem with (2.4.5-p1) openvpn running over TCP specifically the client site. You need to edit your openvpn.inc file to fix this.
@johnpoz said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
OMG dude - there is not a "superuser" backdoor.. And what bug in openvpn over tcp... It work it just fine. Where is the redmine link to this "bug"??
-
@C3G3K4 said in Netgate shared root with ISP? ¯\_(❞⦈)_/¯:
You need to edit your openvpn.inc file to fix this.
And where is the link to this bug report? Or even the thread discussing this issue, or what exactly did you change.
And lets be specific.. Stating there is a "bug" in openvpn tcp, as a client to to some vpn service? With site 2 site? I run tcp client to pfsense from my phone, from my pc at work over tcp and have not seen any "bugs" or issues at all.
Saying there is a "bug" doesn't help anyone nor is going to get anything fixed if there is an actual issue.
-
i don't intend to feed the troll, reported him for 3 post without any meaning, registered 27 minutes ago,I start collecting bets, 5$ .. he's a spammer
-
Hi all, I am just trying to help and contribute, but why do I get aggressive and hostile treatments?
If you do not know how to edit an openvpn.inc file, then I suggest you have to wait for the next pfsense version. Don’t falsely accused someone, specially without established proof.Anyway, my family and I believe, good acts will have good consequences, bad acts will have bad ones. You'd think by now people would understand…
that you reap what you sow.Happy Sunday Everyone.
-
What did you have to change in the client side config file?
How did the issue present before you made that change?
I'm not aware of any OpenVPN TCP issue in 2.4.5p1, if you have found something you should open a redmine bug report: https://redmine.pfsense.org/
Steve
-
Great you want to help, then actually provide that vs just saying "you" fixed something...
Saying there is bug, and "you" fixed by editing openvpn.inc doesn't help or contribute anything.. Posting what was fixed, and how you fixed it would be information people could actually use.
-
The OpenVPN TCP issue has already been fixed in the repo. You can install the System Patches package and then create an entry for
e1c689eeb3a4439f3a66e8686b1fc32db536ac78to apply the fix.There is no "superuser backdoor". You still have not shown any evidence that anything was changed by someone other than yourself, a package you installed, or as a consequence of a configuration change you made.
-
Locking this. If no solid evidence has turned up by now after they have been asked repeatedly for details, they are trolling or otherwise being deliberately disingenuous with their posts.