Pfsense with pihole correct configuration?
-
@jwj of course will be nice to see your setup. Appreciate it
-
@agaitan026 Okies. Tomorrow morning I think. :)
-
@agaitan026 OK, here you go. Part 1
First things first.
These settings may not be entirely correct! I think this is complete but I’m not 100% sure. If you use them bad things may happen like:
• Your network might stop working
• Your wife might take up an annoying hobby, like playing the trumpet
• All of the kids in your neighborhood start playing on your front lawn. This will cause you to scream: “Hey you kids, get off my lawn”. Not a good look!This is all applicable to an ipv4 network. I’m not going to touch on ipv6 at all. For a lot of simple setups it still just all works. When you add in a pi-hole you’ll have to figure out a few things. That varies depending on your particular situation. Does you prefix change or not and so on. How do you turn off privacy extensions on the host your running pi-hole. What the heck are those weird looking domain names. Stuff like that. Too many moving parts and if I go down one road and it’s blindly followed it will break things on setups that have different requirements. So, sorry. Not going to get into it. I will say Dynamic prefixes suck. Not all dynamic prefixes change as long as you don’t get a new cable modem or the like. Depends. The inconstant way ipv6 is implemented vendor to vendor sucks. One Linux distro does it different that some other. It doesn’t need to be this hard. As to the issue why use ipv6 at all? Yes, you should, it’s the future. Ipv4 is broken. It’s all workaround. Will your life suck if you don’t implement ipv6? Not at the moment it won’t.
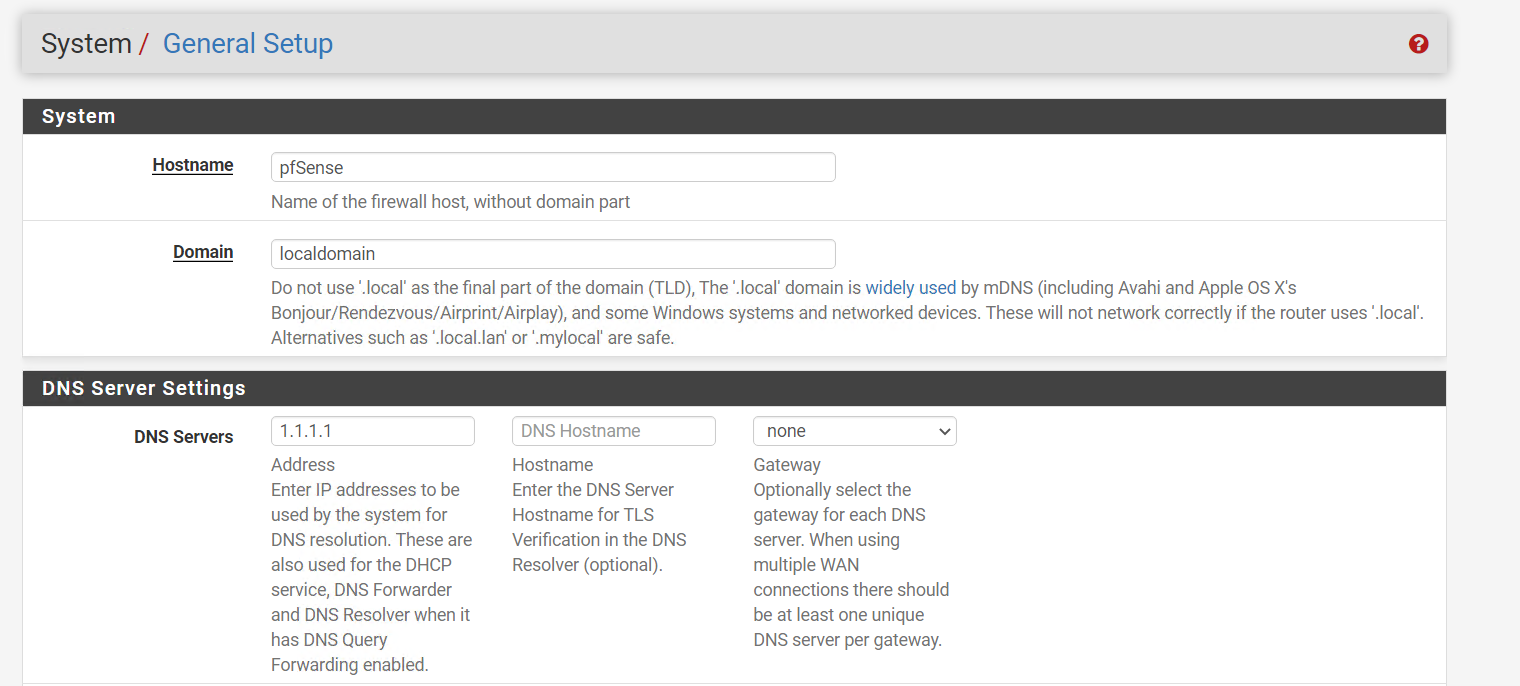
The first step is to make sure your DNS setup is reasonable. You want to be using Unbound as a resolver.
In general settings take note of the domain set. You’ll want this later.
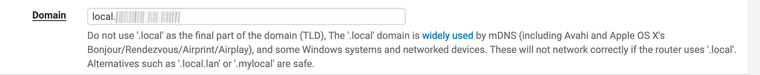
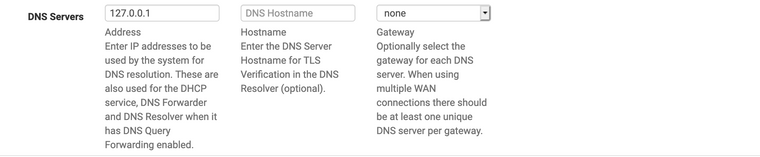
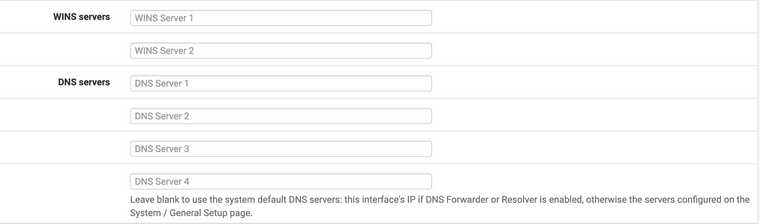
Make sure you haven’t set any external name servers. You want it to look like this.
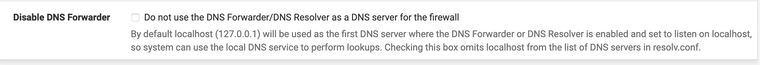
Make sure this isn’t set:
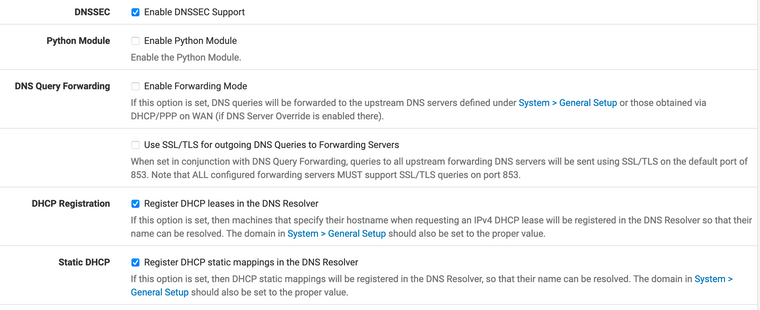
In Services -> DNS Resolver you want default values and then:
Now hop over into Services -> DHCP Server
Assuming you have ONE private network. If you have more you check this on each tab.
Blank is what you want.
I think it’s a good idea to setup static reservations for each known device on each private network.
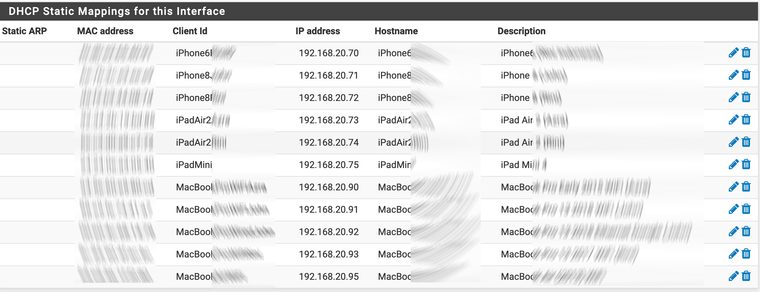
Looking at one of them.
Notice the DNS Servers are blank.
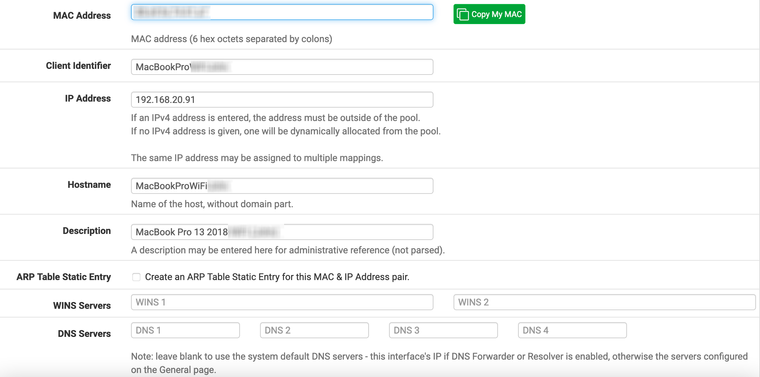
The hostname set is the hostname that will be registered with Unbound. That’s handy. You can then lookup devices by that hostname <hostname>.<local domain name>. The local domain name is set in general settings that you noted earlier. Some devices, Sonos, use crazy hostnames. Like ZSonos or something like that for every speaker. Setting a hostname in the DHCP reservation cleans that up.
At this point things should be working. It’s a nice simple default setup. You might be asking about redirecting DNS? It’s in the pfsense documentation so it must be something you want to do? Well… That depends.
If your clients are well behaved you don’t need to do that. If they use the DNS servers given to them by DHCP you’re good to go.
What if they don’t?
That’s a bit more complicated.
You could just block DNS for them with a firewall rule. The thinking is that you either play by the rules or you get no DNS resolution. OK. I guess. Maybe…
You can redirect them. Setup a NAT port forward and force all DNS traffic to the gateway (or pi-hole). Look at the pfsense documentation for how to do that. That sounds like a good idea until you have a valid reason to point a device to some other name server. It won’t work because it will be redirected. Not going to get into a shouting match about this. Do as you please.
At this point we have ticked a few boxes, setup DHCP reservations and started enjoying an out of the box setup. Still not blocking ads.
-
@agaitan026 And part 2
You need a pi-hole now. That is if you want to use a pi-hole. Pfblockerng works very well. You could just use that and be happy. Really happy. It will block ads and more. It just works with ipv6, no complications. If you want use a pi-hole you know why you want to use a pi-hole and don’t need me to sell you on the idea.
Once you have one get it connected. We’re going to talk about using it on a different private network than the one(s) your other devices are on. Different physical network or VLAN doesn’t make any difference.
OK, it’s now connected. In my case it’s on the 192.168.10.0/24 network. You will want to make sure it’s always at the same address. Static DHCP reservation or static IP setup on the pi-hole. I like doing it with a static IP on the pi-hole not DHCP reservation. Do it how you want. Mine’s at 192.168.10.40. I can ping it. I can ssh into it. I can open the GUI.
The way this works is like this:
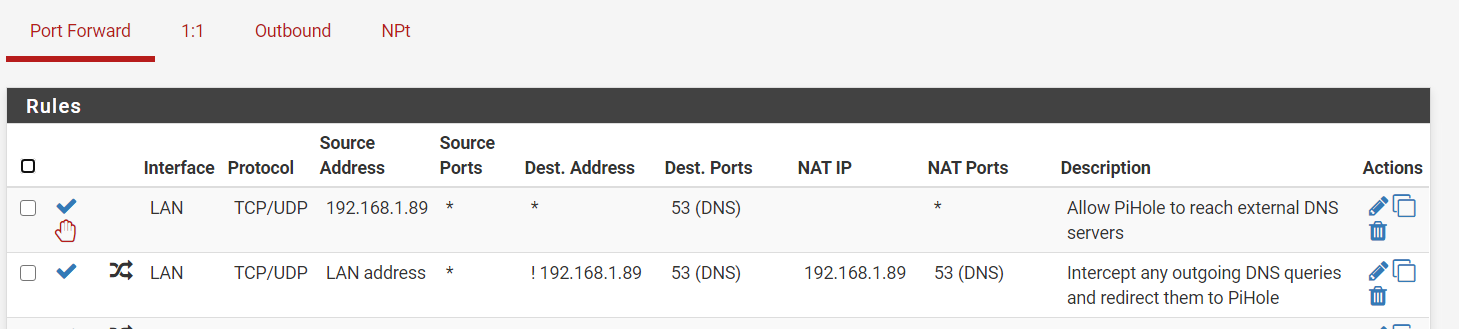
Device goes to the pi-hole for name resolution. It goes there because we told it to with DHCP. Those devices that don’t listen to DHCP go there because I redirect them with NAT. My choice. Again, handle this however you want.
The pi-hole forwards to the gateway (pfsense).
Device -> pi-hole -> Unbound
Notice there has been no mention of cloudflare or google or cloud9. I’ll rant about this for a moment.
<rant>
DNS privacy is a hot topic. Lots and lots of FUD. Who do you trust and why? Think you can hide from your ISP? Not unless you route EVERYTHING through a VPN. Yes, you can deny them the ease of logging your DNS traffic. They are still handling all your traffic. They will just scrape what they want out of your traffic. Do you trust cloudflare or google more than your ISP? Why? Do you trust some VPN service? If there is money to be made it will be made. Some VPN service in a sketchy Caribbean jurisdiction? They can say anything they want. It means nothing. VPN in a European or US jurisdiction? They will respond to legal requests. Do they say they’re not logging? Are they full of sh_t? What will they do when they get a secret court order to start logging based on some remnant of our post 9/11 insanity? Look at the business model. They appear to have a lot of infrastructure around the world. All for $40 a year? They’re full of sh_t.The people selling you on this crap are smart. Look, look at what I’m doing to keep your online life private, they say. Private DNS (ODoH, is the latest BS), I’m so great and we’re the good guys. At the same time they are tracking every click you make and logging every step you take with your smartphone.
It’s like organic food. What do you want? Do you want your carcinogens from the regular list or from the list of approved organic carcinogens? If I had a penny for every crunchy self-righteous statement made by the lemmings I’d be richer than Jeff Bezos. Anything produced on an industrial scale is managed by accountants. Money not only talks, it’s the only thing that talks.
By the way. If you want good food buy local. Visit the farm. Have a look around. The good ones will welcome you. The thing is you are going to have to pay. Good stuff done carefully costs. Treating employees right costs.
Just resolve using unbound. If you really care about your privacy, DNS is the least of your worries.
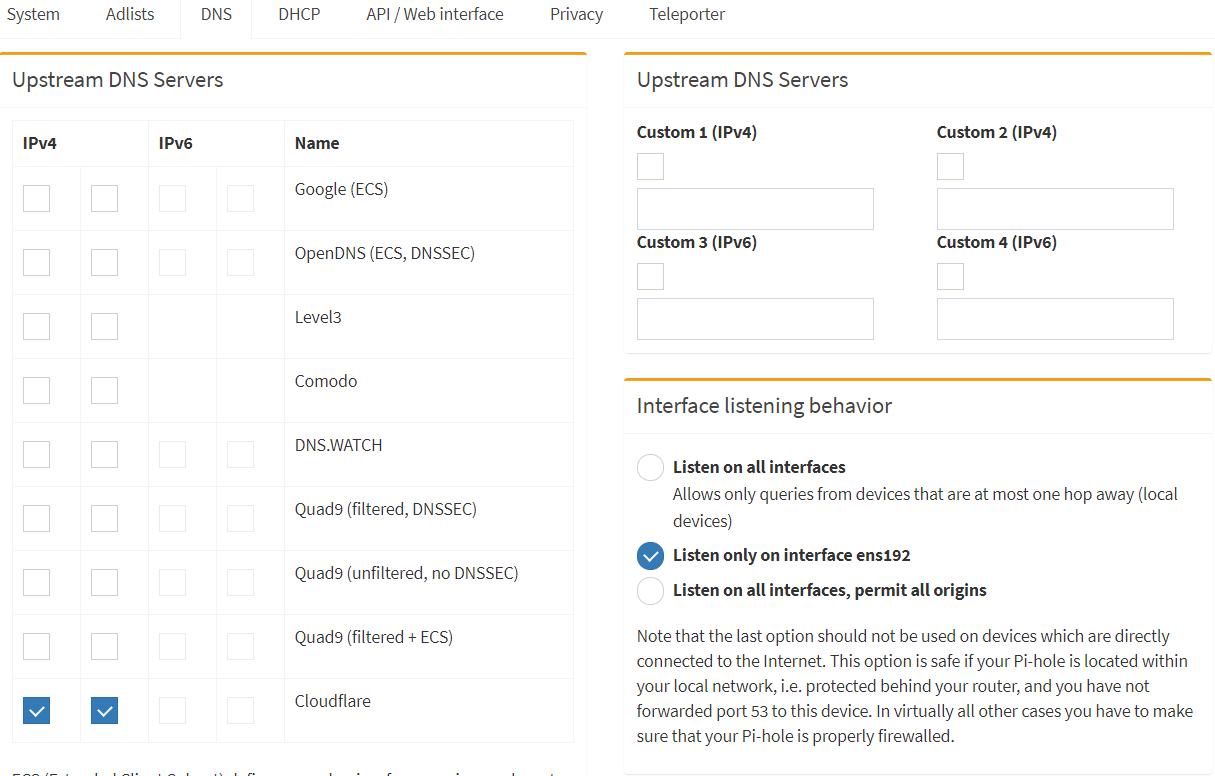
</rant>Once you’re up and running you want to see this in your pi-hole.
Remember, my pi-hole is on the 192.168.10.1/24 network so 192.168.10.1 is unbound. Also, there is no monkey business going on in this network. No redirection or rules blocking port 53.
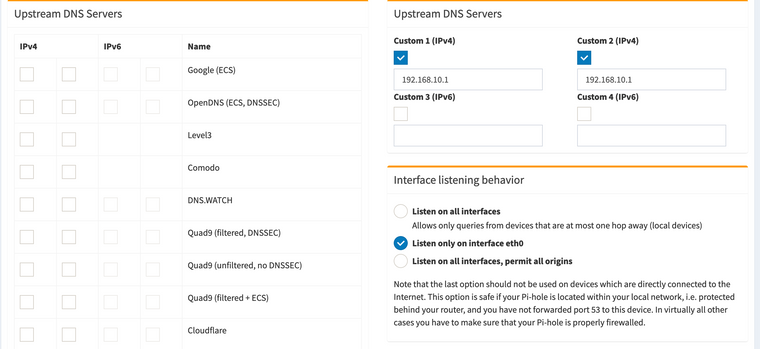
Now you can do this:
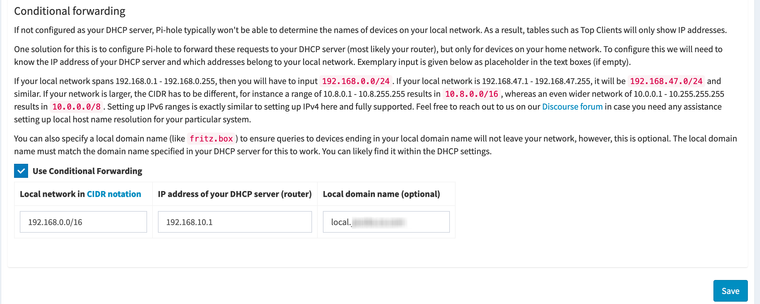
Adjust for your situation. I have a few networks so I just cover the entire 192.168.0.0/16 range.
Now I can see my hosts by the hostnames I setup in their DHCP static reservations. Otherwise it’s a hot mess in the pi-hole logs.
What’s left to do is to get your client devices pointed to the pi-hole. Simple really. Just have DHCP tell them were to go. In the DHCP server settings for each network (other than the one your pi-hole is on, sorry to be redundant but it is worth pointing out again) you do:
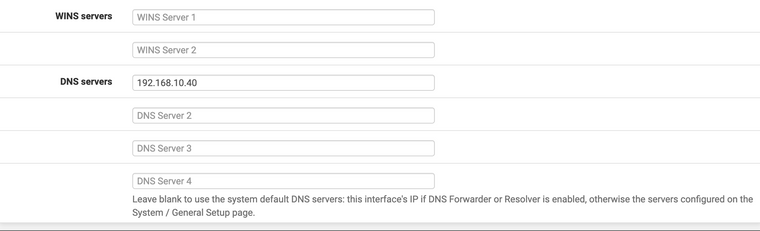
That points every device on that network to the pi-hole. Each individual static reservation should have nothing for DNS servers because we did that above for the generic baseline setup. You could do it device by device in their static reservations. Up to you. If you want to exempt some devices from filtering you can do it static reservation by static reservation or use pi-hole groups. Your choice.
Things should now be working good.
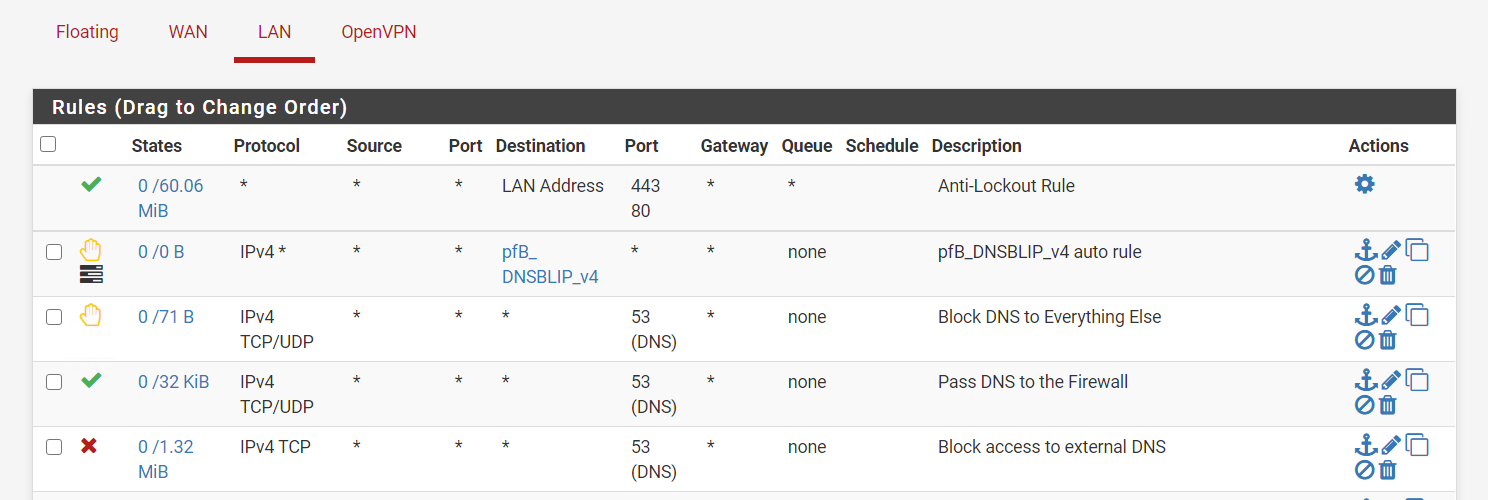
If you have locked down networks, like a guest network, you will need a rule to allow those clients to get to the pi-hole. Add a pass rule.If you want to do redirection on networks that contain devices that don’t play by the rules, add the NAT port forward and it will add the correct pass rule.
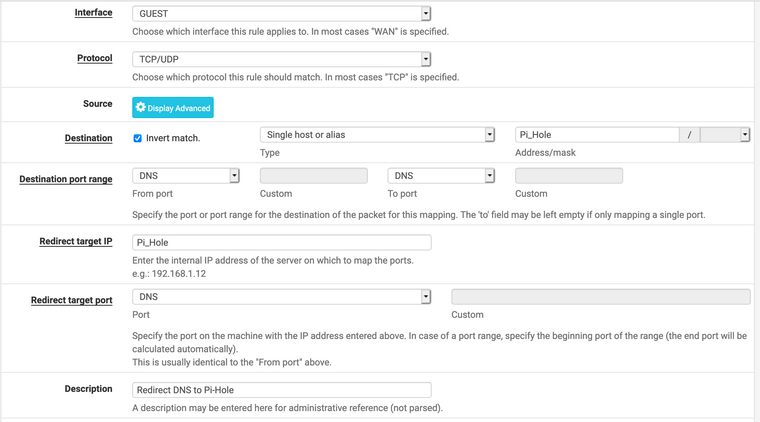
You should get a rule that looks like this on the corresponding network.

Creating an alias with the ip of your pi-hole will make the above rules clearer when you look at them later.
That's it for now. I hope that helps.
-
@jwj said in Pfsense with pihole correct configuration?:
ODoH, is the latest BS
But the company providing the proxy for that and then the dns provider - they would never collude ;) heheheh... They only have your privacy in mind ;)
Its like they are on a mission to F up dns beyond nonsense.. In the sake of privacy my ASS!!
If you are concerned about your isp easy sniffing your dns, then just resolve through a vpn tunnel.. But as stated - they still handling your traffic - so not like they can not find out where your going and when, etc.
The only way to hide where your going from your isp is full vpn.. But then your just handing all that info over to your vpn provider and giving them money to to boot..
If you really care about your privacy, DNS is the least of your worries.
QFT
Here is the thing - anything that centralizes dns, and lets devices or software just use what they want other than what you tell them for dns.. Is not in anyone's best interest that is for damn sure.
-
@johnpoz Yeah man. I just don't get the amount of attention this gets or the amount of emotional energy people put into it. Truly a not seeing the forest for the trees situation.
This guy should know better than give any attention to it:
https://www.schneier.com/blog/archives/2020/12/oblivious-dns-over-https.html
and, well, I guess this is an unsurprising bit of click bait:
https://arstechnica.com/information-technology/2020/12/cloudflare-apple-and-others-back-a-new-way-to-make-the-internet-more-private/
Was going to wade into the comments. Decided to not inflict that pain on myself.
-
@jwj thank you for your tips. I tried but not working. Im not sure if its because i have whm/cpanel on one of my VMs if i try to browse to a website from whm vm doesnt works but if i try google.com it works
What im doing wrong?
Thank you
-
@agaitan026 I have no clue. Sorry.

-
@agaitan026 said in Pfsense with pihole correct configuration?:
Im not sure if its because i have whm/cpanel on one of my VMs
Having a hard time coming up with how that would have anything to do with anything... Unless its trying to do something with dns on its own, and not paying attention to your settings in unbound, etc. And your trying to use it to figure out your dns working or not working?
Forget whatever it is your doing on some vm..
Do a simple query to pfsense IP.. Does dns work or not? Use your fav tool, dig, host, nslookup, etc..
Is pfsense running as a VM?
-
@johnpoz correct, pfsense is running on a vm, pihole is in another vm with another vlan
-
Ok so pfsense is a vm, which we have no idea if how you have setup and connected to the internet.
Does pfsense dns work or not - its 2 seconds to validate via simple queries to it via your fav tool.. Dig is mine..
-
@johnpoz working
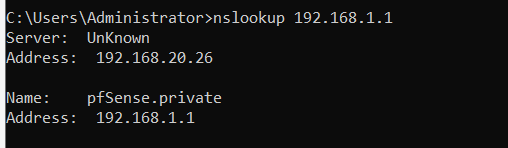
i have pfsense 192.168.1.1 and pihole 192.168.20.26 another vlan
i can browse any website except websites inside the cpanel vm
like this
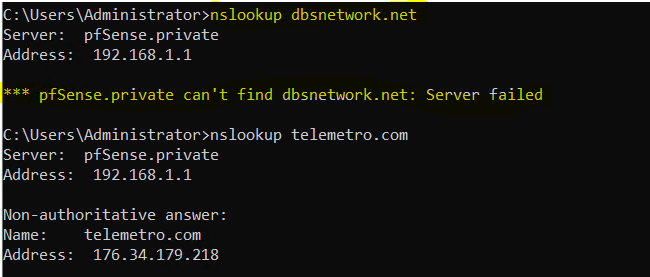
on yellow a domain from whm vm in the same machine as pfsense and pihole
strange by enabling this setting in Services / DNS Resolver / General settings
DNS Query Forwarding
Enable Forwarding ModeIf this option is set, DNS queries will be forwarded to the upstream DNS servers defined under System > General Setup or those obtained via DHCP/PPP on WAN (if DNS Server Override is enabled there).now i can browse whm websites without issues im not sure if thats the correct behavior and setting
-
Have already been over this multiple times..
There is not right or wrong setting be it you want to forward or not forward...
When you enable that - you forward, when its not enabled you resolve..
Where you resolving when you tried to lookup dbsnetwork.net?
Seems you point the NSs for that to yourself? Your hosting the NS for that domain it seems?
-
@johnpoz correct ns point to same ip
-
Well you have a problem there.. I see that they don't even answer via tcp as well.
So you have communication problem talking to yourself it seems then.. Hosting dns on the same device is not a good idea! The 2 NSs are on the same network.
-
@johnpoz yes thats true. I should use maybe amazon route 53 or another service. I got another vm that points to route 53 ns and doesnt have any issue.
So that's my big problem. A basic ns thing
You recommend another rather than amazon route 53?