DNS Resolver Timeouts
-
@kevindd992002 said in DNS Resolver Timeouts:
How do you propose I start with my analysis?
I don't know how far apart the endpoints are and how many ISPs are in this ...
but I would also take short- and longer-term measurements (on tunnel network):
short: iperf3
https://docs.netgate.com/pfsense/en/latest/packages/iperf.htmlfor long-term discipline I use this, free for 5 endpoints:
https://emcosoftware.com/ping-monitor
(I set it up and let it run for hours)although I still suspect it will be a different issue than the tunnel itself
DNS:
this pairing is best in your case
https://github.com/synackray/dns-load-generator
https://www.wireshark.org/ -
@daddygo said in DNS Resolver Timeouts:
@kevindd992002 said in DNS Resolver Timeouts:
How do you propose I start with my analysis?
I don't know how far apart the endpoints are and how many ISPs are in this ...
but I would also take short- and longer-term measurements (on tunnel network):
short: iperf3
https://docs.netgate.com/pfsense/en/latest/packages/iperf.htmlfor long-term discipline I use this, free for 5 endpoints:
https://emcosoftware.com/ping-monitor
(I set it up and let it run for hours)although I still suspect it will be a different issue than the tunnel itself
DNS:
this pairing is best in your case
https://github.com/synackray/dns-load-generator
https://www.wireshark.org/Yeah, I don't have issues with using iperf3 across the tunnel. Pfsense also has gateway monitoring for the IPsec tunnel (routed VTI) and long term ping monitoring seems stable.
Using the DNS server across the tunnel is just my last resort. My real goal here is for each site to use their own DNS resolvers. Do you have any ideas why I'm getting a lot of timeouts when DNS resolver is enabled in site B? Can an ISP block DNS requests to external DNS servers if it's a resolver (as opposed to a forwarder)?
-
@kevindd992002 said in DNS Resolver Timeouts:
Do you have any ideas why I'm getting a lot of timeouts when DNS resolver is enabled in site B?
So, honestly not, because there is little info - here Wiresark can help solve this
@kevindd992002 "Can an ISP block DNS requests to external DNS servers if it's a resolver (as opposed to a forwarder)?"
it would be very annoying and unfair (from ISP, but we have already seen a crow on a stick)
a packet capture also shows this
-
@daddygo said in DNS Resolver Timeouts:
@kevindd992002 said in DNS Resolver Timeouts:
Do you have any ideas why I'm getting a lot of timeouts when DNS resolver is enabled in site B?
So, honestly not, because there is little info - here Wiresark can help solve this
@kevindd992002 "Can an ISP block DNS requests to external DNS servers if it's a resolver (as opposed to a forwarder)?"
it would be very annoying and unfair (from ISP, but we have already seen a crow on a stick)
a packet capture also shows this
What can Wireshark provide that the packet capture (from pfsense's tcpdump) I already provided don't? If you check the OP again, you'll see that I have packet captures there.
-
Might not be related.
But when i had unbound "DNS issues".
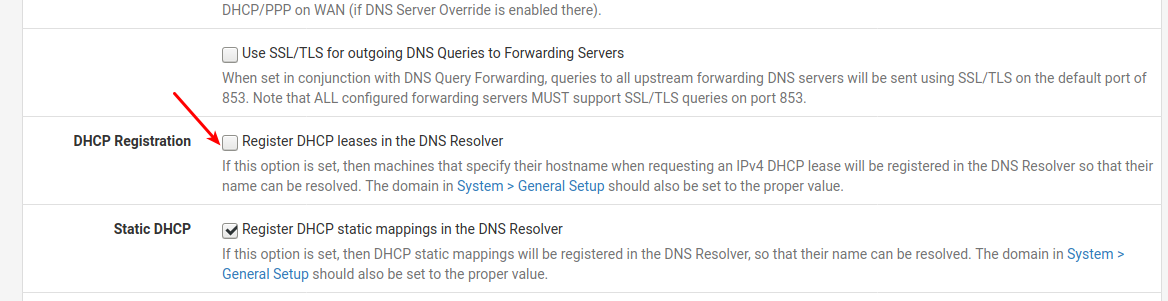
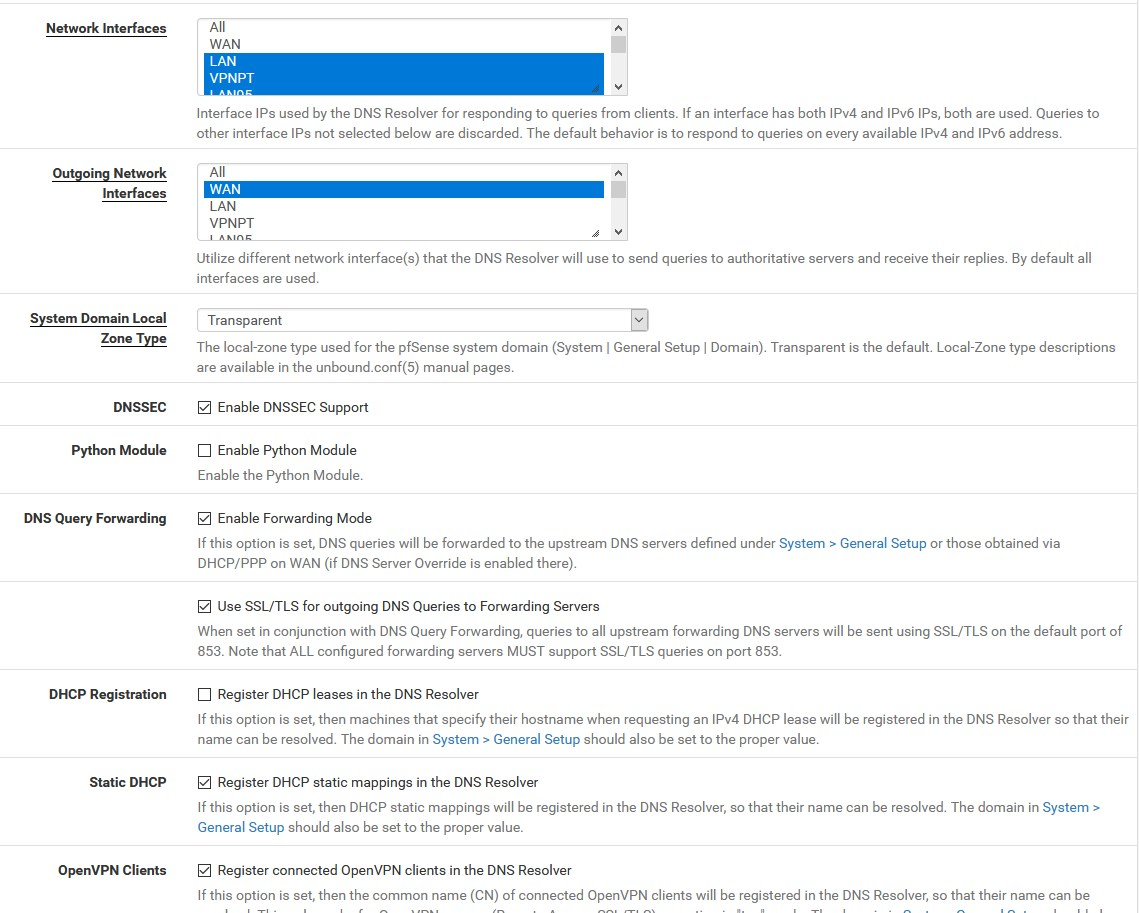
I had "ticked" register DHCP Leases in unbound
That made unbound restart every time a DHCP event happened, and made my system unusable.
Untick that DHCP Registration if set
/Bingo
-
@bingo600 Yeah, tried that already, didn't make a difference. In Site A where unbound is perfectly working, I have that checked and the DHCP service restart is very fast that it is barely noticeable. These are both for home sites and it's not like the lease of my few DHCP clients are always expiring.
-
@kevindd992002 said in DNS Resolver Timeouts:
What can Wireshark provide that the packet capture
you can see an online and / or real-time scan on the Wireshark screen - when you launch an action
do you pass this on site B?
(for this installation, for example, the DNS goes through a tunnel)translate this, of course, into your example (GW A site)
-
@daddygo said in DNS Resolver Timeouts:
@kevindd992002 said in DNS Resolver Timeouts:
What can Wireshark provide that the packet capture
you can see an online and / or real-time scan on the Wireshark screen - when you launch an action
do you pass this on page B?
(for this installation, for example, the DNS goes through a tunnel)translate this, of course, into your example (GW A site)
Sorry, what? What do you mean by "page B"?
Let's forget about the tunnel for now. Like I said, that is my last resort/workaround. Let's treat site B as an independent site without an S2S VPN. My goal here is to simply use unbound on site B as a resolver (not forwarder) without any issues.
-
@kevindd992002 said in DNS Resolver Timeouts:
Let's treat site B as an independent site without an S2S VPN
Okay then we misunderstand each other...
can you draw a quick diagram of what you want to achieve?
A site pfSense A
B site pfSense Bor exactly what
-
@daddygo said in DNS Resolver Timeouts:
@kevindd992002 said in DNS Resolver Timeouts:
Let's treat site B as an independent site without an S2S VPN
Okay then we misunderstand each other...
can you draw a quick diagram of what you want to achieve?
A site pfSense A
B site pfSense Bor exactly what
It looks like it, yes.
So I have two sites that are connected through IPsec VPN, yes, but I just gave that information here because it was one of the tests I had (using the DNS resolver on the far end of the tunnel).
Site A (main site)
- WAN interface has a public static IP
- no problems with being a DNS resolver (without forwarding)
Site B (remote site)
- WAN interface is assigned a private IP since it is behind a CGNAT
- when DNS resolver (without forwarding) is set, tons of timeouts are seen in Status -> DNS Resolver and the whole network is affected, browsing is very intermittent
- when DNS resolver (with forwarding to 1.1.1.1, or 8.8.8.8, or even to the ISP's own DNS servers) is set, same behavior, lots of timeouts. I must say though, that this was my workaround before like a few months ago and it worked. For some reason, it is also timing out these past few days I tested.
- when DNS Forwarder (dnsmasq) is enabled instead, everything is working properly. It's been almost two days without any issues.
- as soon as I go back to using DNS resolver (unbound), then the problem is immediately back
-
@kevindd992002 said in DNS Resolver Timeouts:
It looks like it, yes.
so I understand, so in terms of your question, it has nothing to do with A - B.
in summary:
- The pfSense installation which is used in point B, works with a timeout.... DNS, if UNBOUND is used
- in addition, it is behind CGNAT
Can you do a test with this for both conditions? (Unbound / Forwarder):
https://www.grc.com/dns/benchmark.htmFinaly, you can show UNBOUND settings such as:
-
You got it.
I have to get back to you after Christmas for that benchmark test (which I'm familiar with as I used it before). I'm physically at site A right now and while troubleshooting another issue with IPsec, I accidentally lost access to site B's pfsense and no one is physically there to undo what I did.
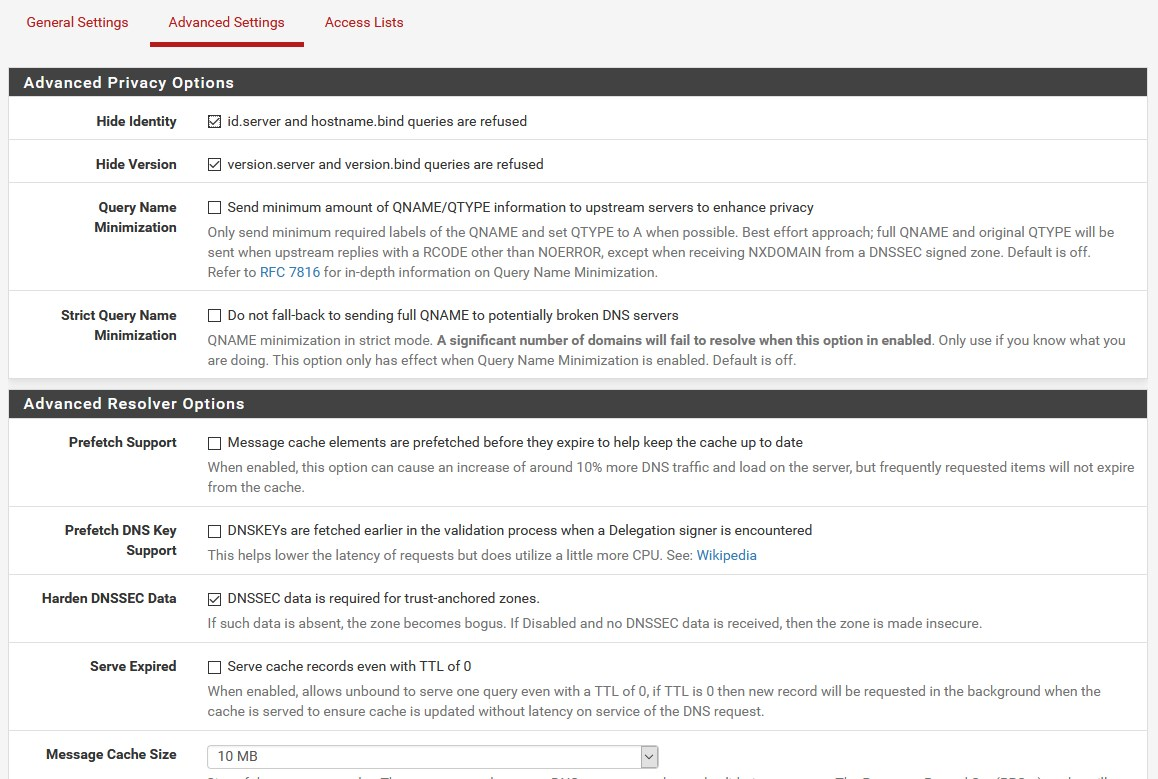
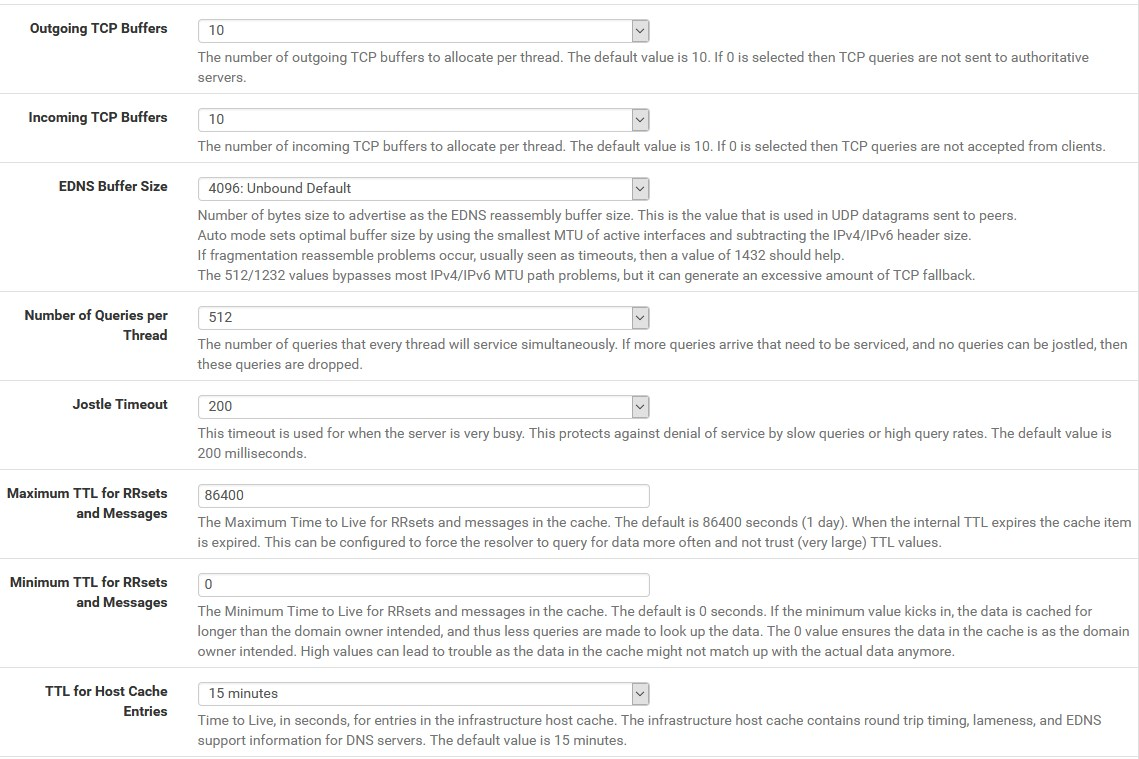
As for the settings, they are exactly the same with the unbound settings I have site A and here they are:
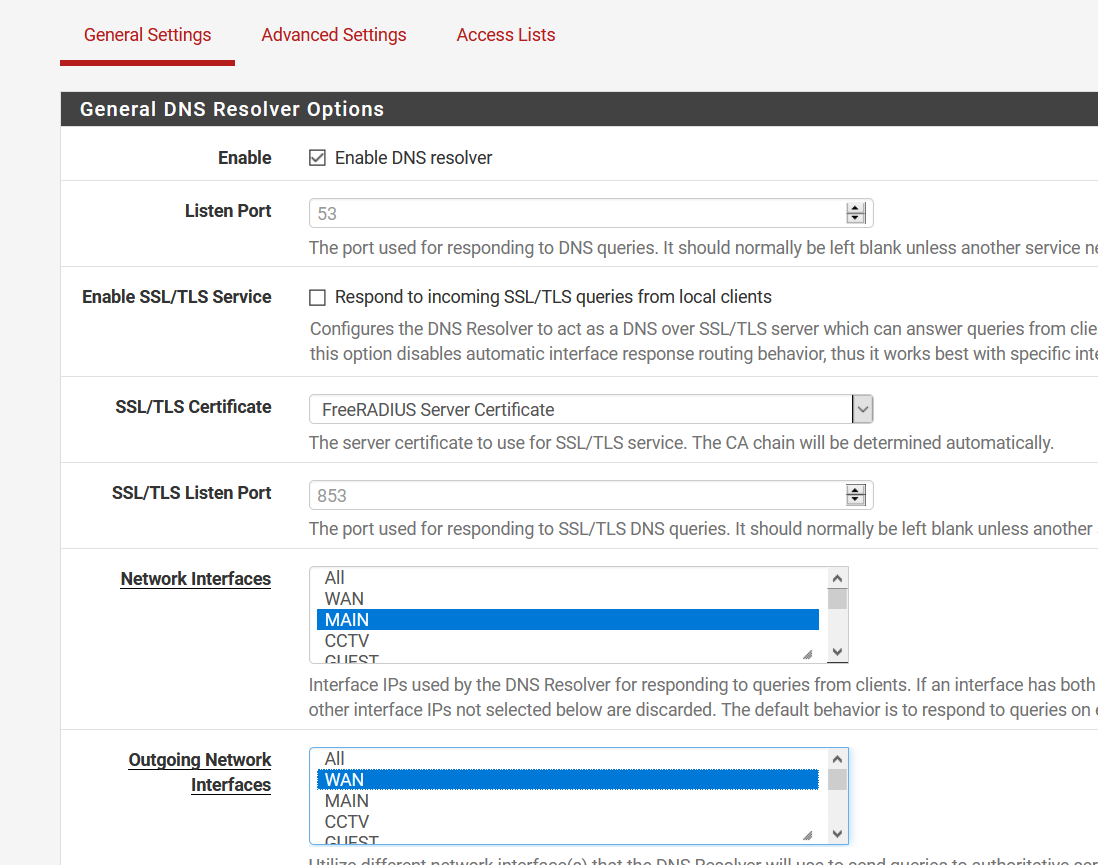
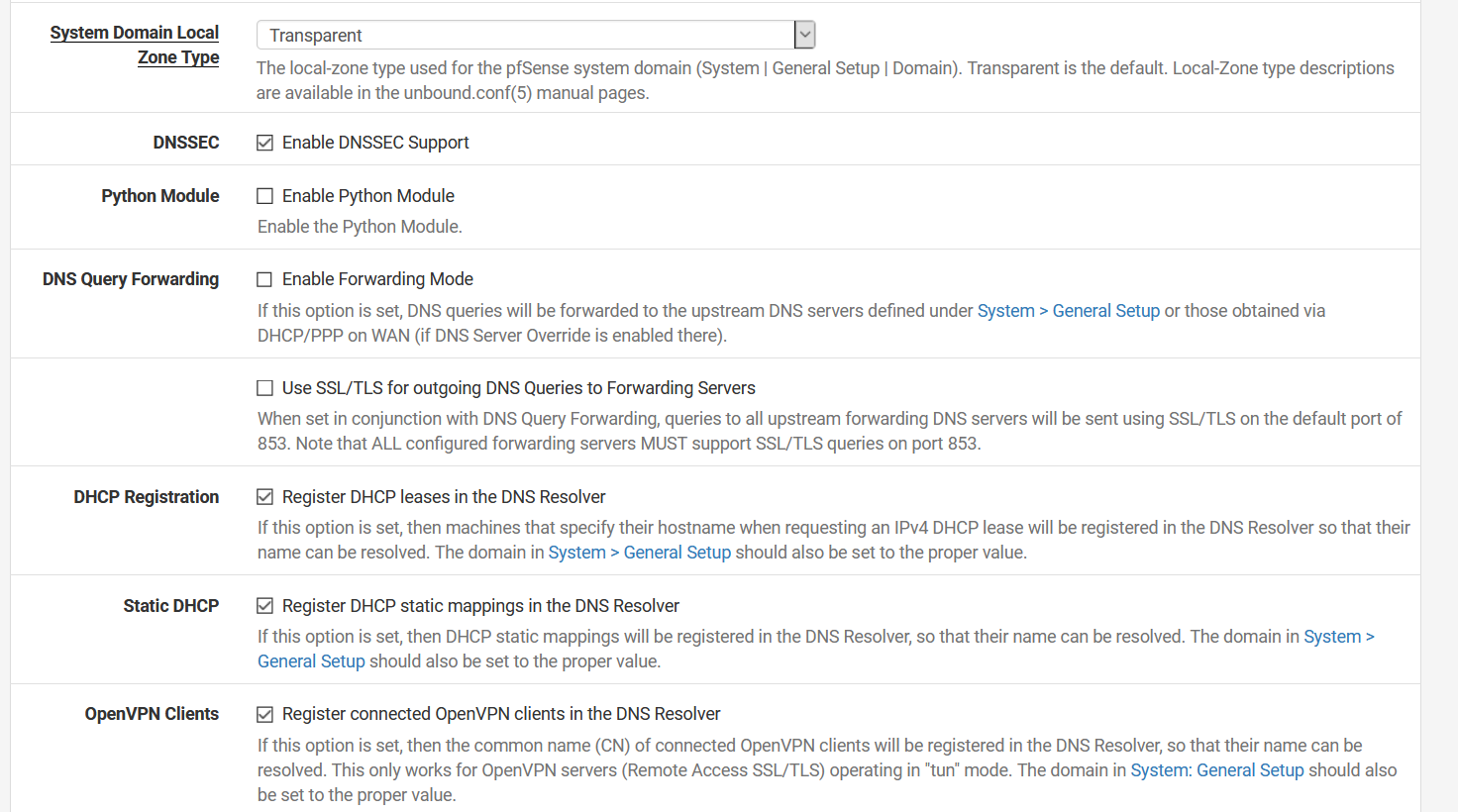
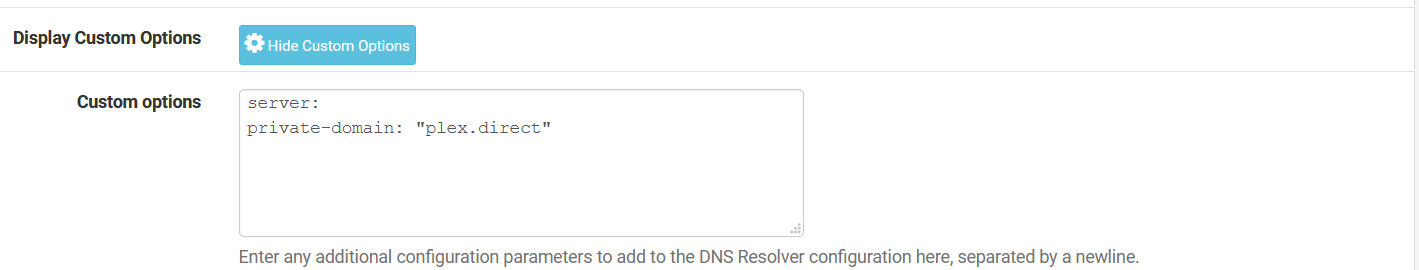
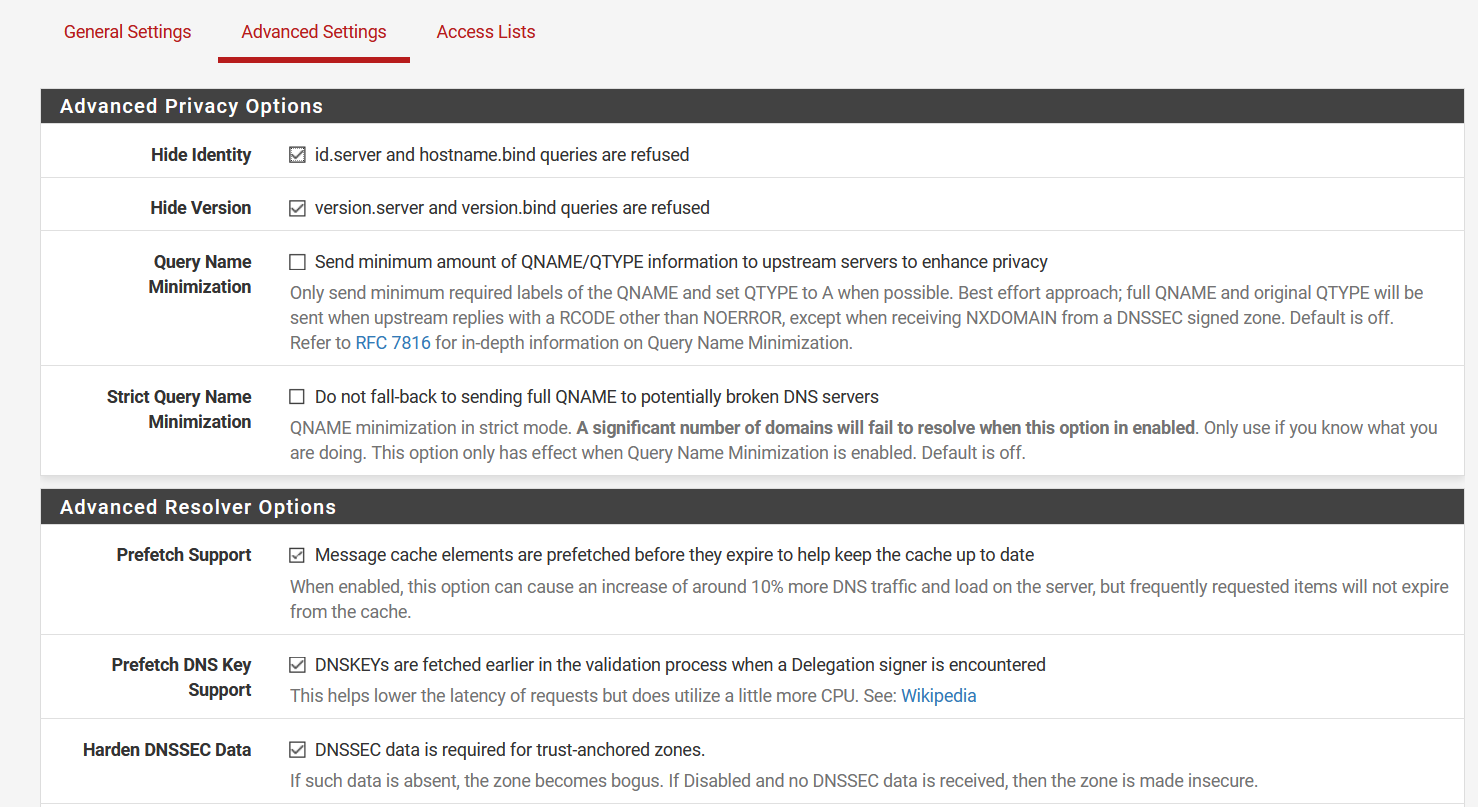
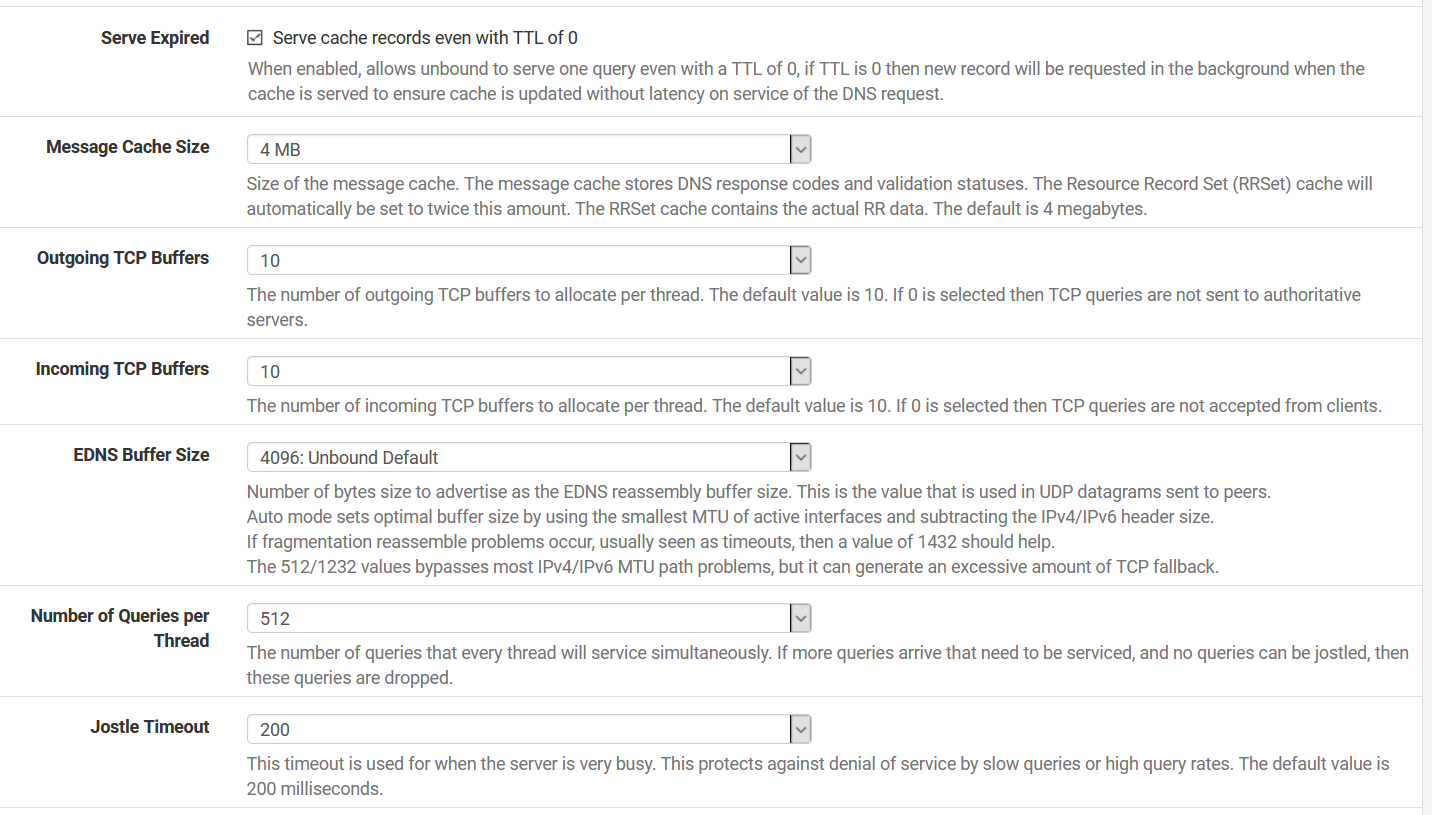
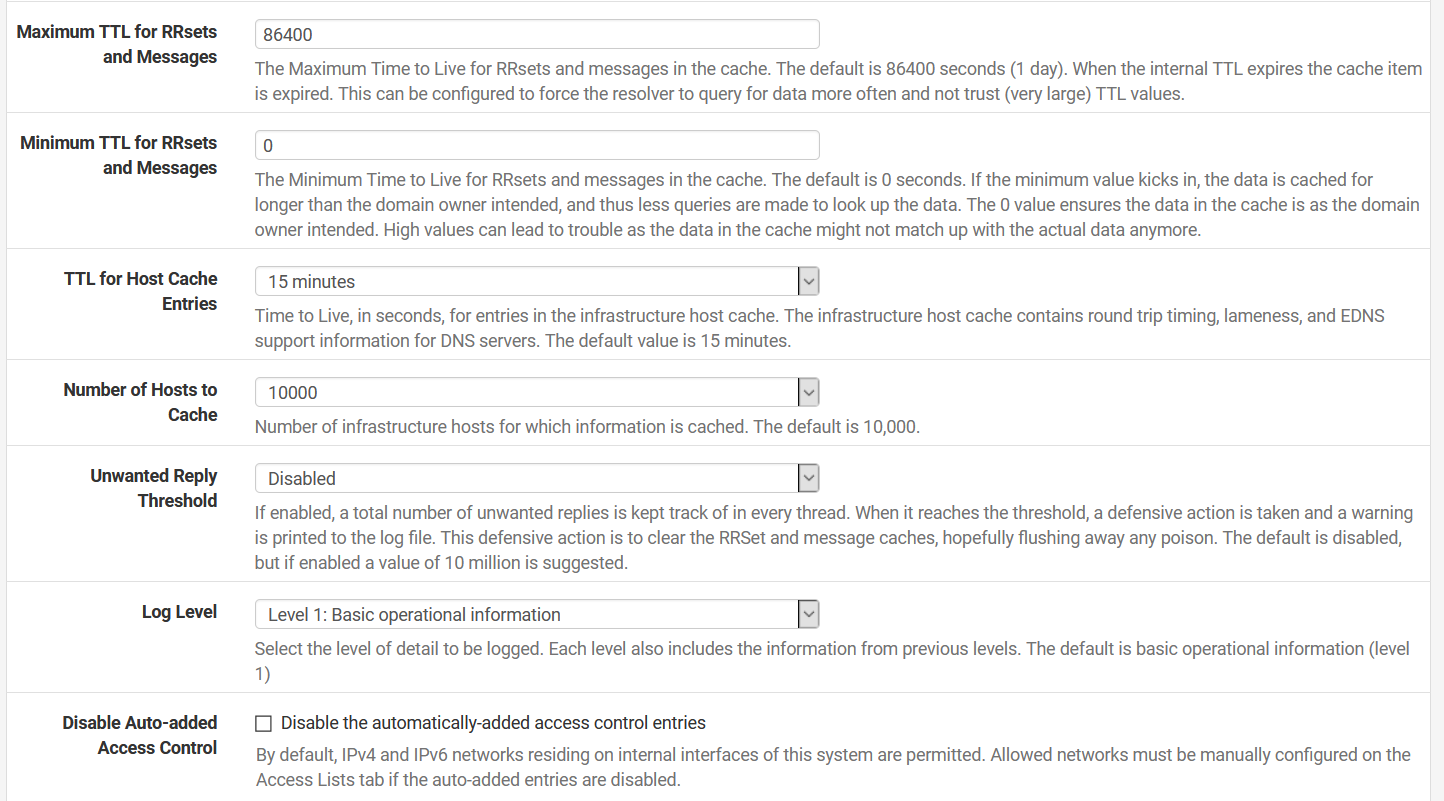
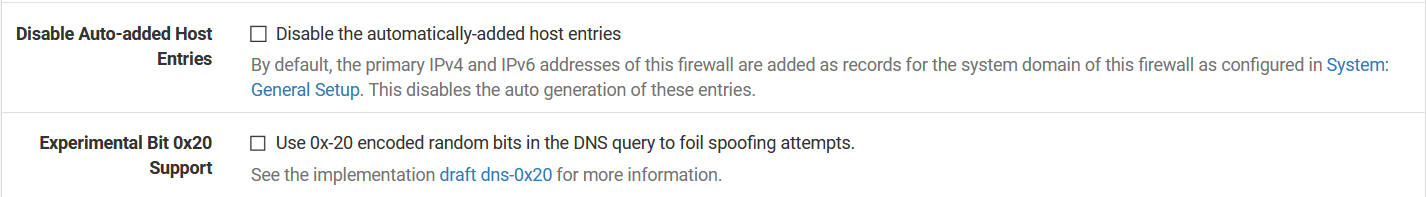
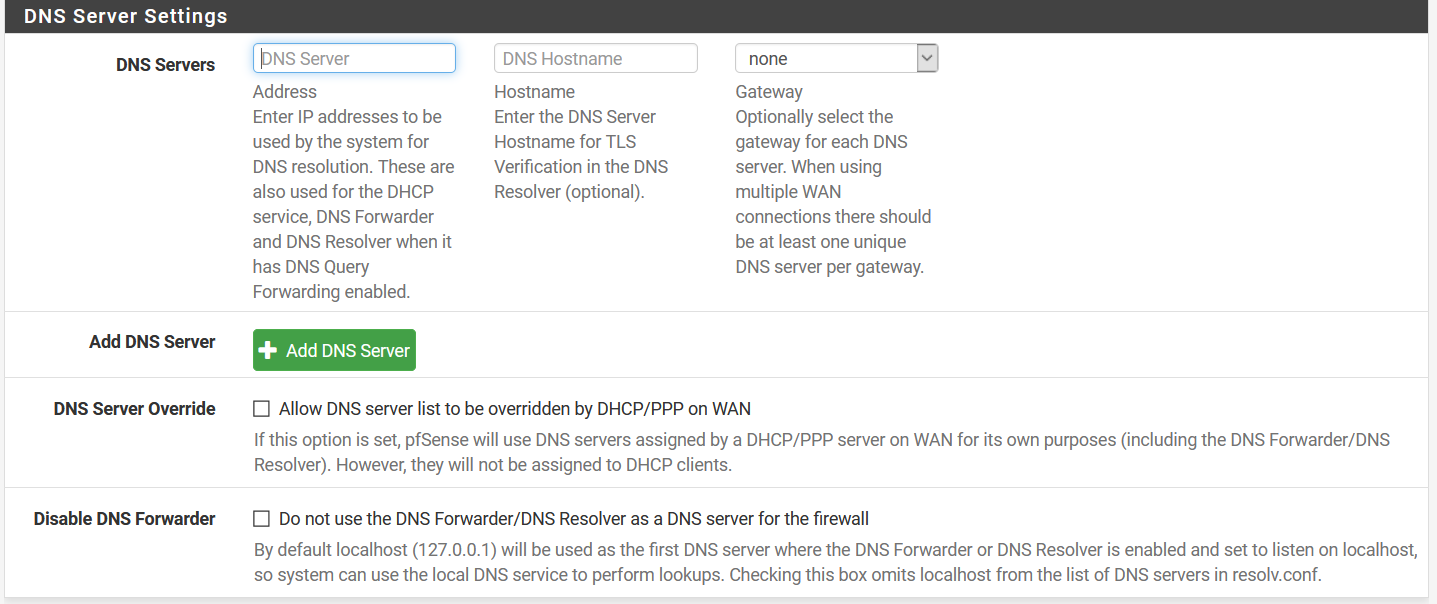
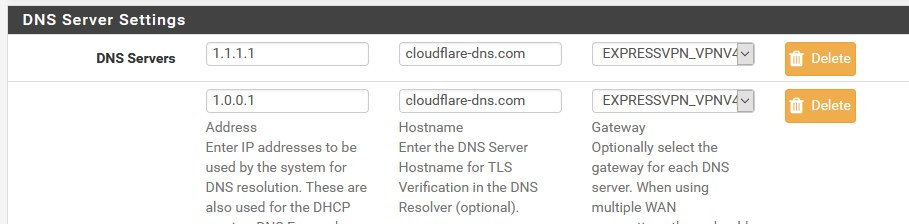
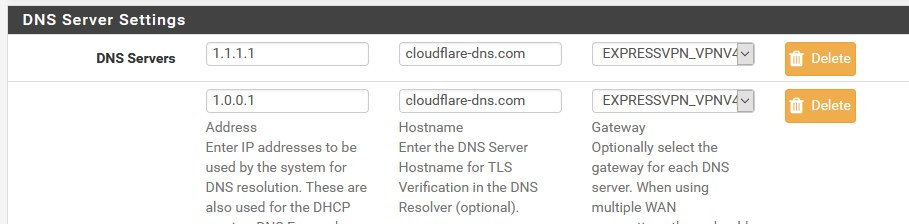
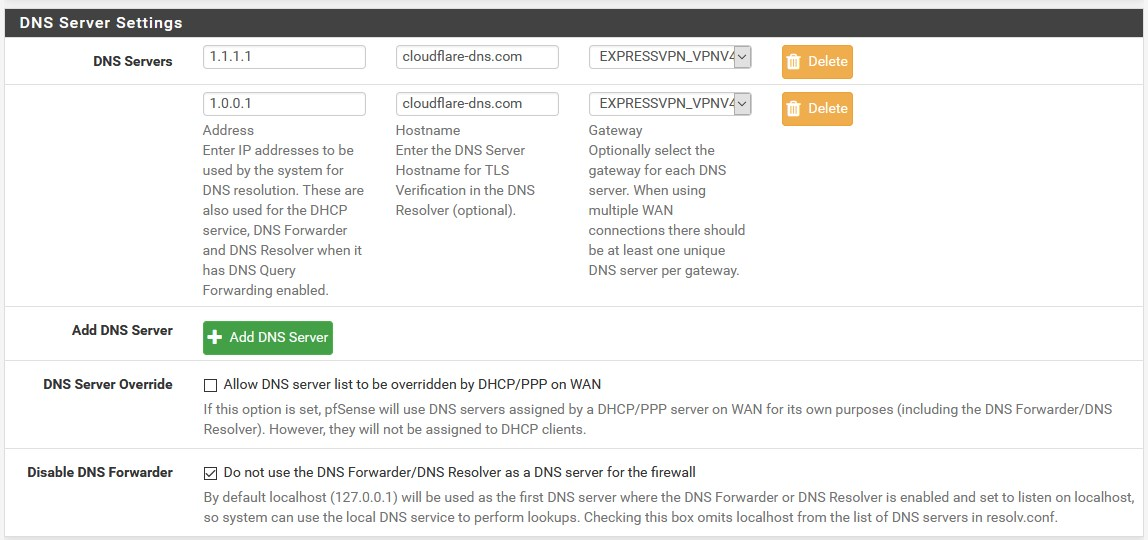
I don't have a DNS server in the DNS settings under General because I don't need one. I'm using unbound as a "resolver" so it queries the root hints directly. In the settings that you've shown, it looks like you're using unbound as a forwarder too, why?
-
How is this not the same exact problem you had before.. If you have a shit isp, then you have a shit isp..
Your previous thread showed loss on your isp.. If either of these sites its on that isp, or whatever isp they have is loosing packets.. Then yes you can have issue, be it dns or anything else.
Doesn't matter if you forward or tunnel or whatever.. If your isp sucks it sucks.. Nothing pfsense can do about that.
Previous you had sniffs showing traffic leaving your wan, with no answer.. There is nothing pfsense can do to fix that..
-
@kevindd992002 said in DNS Resolver Timeouts:
it looks like you're using unbound as a forwarder too, why?
Forwarding Mode to 1.1.1.1 = general tab
as I try to achieve more privacy and greater security

CloudFlare / 853 DoT
-
@daddygo said in DNS Resolver Timeouts:
as I try to achieve more privacy and greater security
Well that sure isn't doing anything about that..
-
@johnpoz said in DNS Resolver Timeouts:
Well that sure isn't doing anything about that..
I say I'm trying

at least I don't interrogate root servers through my own ISP, hihihihi
-
@johnpoz said in DNS Resolver Timeouts:
How is this not the same exact problem you had before.. If you have a shit isp, then you have a shit isp..
Your previous thread showed loss on your isp.. If either of these sites its on that isp, or whatever isp they have is loosing packets.. Then yes you can have issue, be it dns or anything else.
Doesn't matter if you forward or tunnel or whatever.. If your isp sucks it sucks.. Nothing pfsense can do about that.
Previous you had sniffs showing traffic leaving your wan, with no answer.. There is nothing pfsense can do to fix that..
Right, I just actually continued that old thread to this thread to make it "cleaner". The only new information I have now is that I tried with dnsmasq and it seems to have no timeouts. As to why, I don't know. But I was still having problems with unbound set as forwarder.
If you see my packet captures in the OP of this thread, it still does show traffic leaving the WAN and not getting any replies back. You're still right, I'm still pushing hard for my ISP to fix this shit, but what I don't understand is why dnsmasq seems to be working just fine?
-
@kevindd992002 said in DNS Resolver Timeouts:
I'm still pushing hard for my ISP to fix this shit
Indeed, if you have a shitty ISP, there’s nothing you can do, but my tests suggested above they are caught quickly
-
@daddygo said in DNS Resolver Timeouts:
I say I'm trying
But all you have accomplished is handing your info off to someone else on silver platter. With explicit trust of what they hand you back.. Your sure not hiding anything from your ISP that.. Since they still know every IP you go to, and simple if they wanted to to just sniff your sni for any https traffic to know what specific domain your going to.. Just like they could with your dns.
So what your trying to hide from the root servers?
Oh - the other thing you did accomplish is slowing down dns.. Guess you got that going for you ;)
-
@johnpoz said in DNS Resolver Timeouts:
@daddygo said in DNS Resolver Timeouts:
I say I'm trying
But all you have accomplished is handing your info off to someone else on silver platter. With explicit trust of what they hand you back.. Your sure not hiding anything from your ISP that.. Since they still know every IP you go to, and simple if they wanted to to just sniff your sni for any https traffic to know what specific domain your going to.. Just like they could with your dns.
So what your trying to hide from the root servers?
Oh - the other thing you did accomplish is slowing down dns.. Guess you got that going for you ;)
@DaddyGo sorry but I'm on @johnpoz on this one. He is completely right. If you're using unbound, then its primary purpose should be a "resolver" like what I've been telling you with my earlier posts. I guess you misunderstood again.