To 2.5.1 or not ? that is the question :)
-
On my side, as soon you try to do an install with a different ip or a different sub. it result into a 404 Not found -nginx error page. if leave and touch nothing and just put the psw.. look ok, but even after try to change the ip and it fail. Doing the exact same process as 2.4.5 or 2.5. So .. no 2.5 is the last working version.
-
@yanik Did you get your port forwarding working in 2.5.1?
I'm having the same issues on port forwarding to my Synology box and Plex Server (FreeNAS box). :-(
To roll back from pfSense 2.5.1 to 2.5.0 can I just restore my 2.5.0 backup config file, or would I have to do a clean install of pfSense 2.5.0 first and then restore the 2.5.0 backup?
-
@tac57
A roolback would always include a reinstall (format) , unless you are using ZFS w. snapshot. -
@docop2 de Winter is almost over, let's hope dev fix the bugs.
-
@tac57 said in To 2.5.1 or not ? that is the question :):
@yanik Did you get your port forwarding working in 2.5.1?
I'm having the same issues on port forwarding to my Synology box and Plex Server (FreeNAS box). :-(
To roll back from pfSense 2.5.1 to 2.5.0 can I just restore my 2.5.0 backup config file, or would I have to do a clean install of pfSense 2.5.0 first and then restore the 2.5.0 backup?
No, 2.5.1 port forwarding doesnt work.
I reinstalled pfsense v2.4.5_1 with zfs instead of ufs to able to have snapshots before upgrades. -
Upgrade from 2.5.0 to 2.5.1 went quickly and mostly fine on my netgate RCC-VE 2440. I have a pretty basic setup with a few vlans and pfblocker. The only issue I noticed was that DNS was not working. A subsequent reboot solved that.
-
My starting point was a working v2.5.0 install with no issues. Here is the sequence of events after upgrading to v2.5.1 this morning:
- PFsense unable to route traffic after boot up.
- Unable to ping google.com or 8.8.8.8 from PC
- Bounced the DNS forwarder service, no change
- Rebooted PFsense, no change
- Still unable to ping google.com or 8.8.8.8 from PC
- Verified PFsense itself can ping 8.8.8.8
- Verified correct default gateway was selected
- Rebooted PFsense a 2nd time, no change
- Verified I am able to ping my L3 switch and PFsense, but unable to ping my WAN_DHCP gateway IP (i.e. cable modem)
- Power cycled cable modem
- We have Internet!
I've never had to bounce my cable modem with any other upgrades (including 2.4.5-p1 to 2.5.0), so it's unclear why a power cycle was needed after this latest upgrade from 2.5.0 to 2.5.1.
I would be cautious about any remote upgrades to this version. This would've been a disaster if I performed the upgrade remotely and wasn't on-site to troubleshoot the outage.
-
@marvosa
Let me redo you list :1 PFsense unable to route traffic after boot up.
1a) does it have a WAN IP ? Is it a valid IP ? Does it have a gateway ? Are these addresses known / seen before.I'll be looking at the DHCP client log. Checking if there was a dialog that looks 'normal' between the pfSense DHCP client, and the upstream DHCP server, where ever that may be.
Step 2 to 11 : sending a ping to some remote network, knowing there is no 'route' only proves there is no route.
Restarting DNS doesn't has anything to do with routes. When using IP addresses as 8.8.8.8, DNS functionality isn't used anyway. Also, if there is no 'route', DNS wouldn't work anyway.Very true : Modem devices have most often nothing to set up, and should be transparent.
The reality is different : the most strange things are shown on this forum : modem that flap their NIX state several times during reboot or connection re negotiation. Or assign a RFC1918 while the connection isn't build yet.After pfSEnse has been undergoing a major update, a planned reboot is part of the 'validation process'. Just to be sure that, if it reboots in your absence, things land on their feeds.
It's hard to say what happened in your case, but it could be something like this :
Updating pfsense to 2.5.0 needs a kernel update. To do this, it needs to reboot to load the new kernel. The reboot will take you pfSense WAN NIC down for a moment. The mdoem sees this, and act upon that event, like : a upstream re negotiation.
pfSense boots fast, the modem is (to) slow to open a new connection to the ISP. The pfSense WAN DHCP client repeats over an over a DHCP DISCOVER. This request never reaches the upstream DHCP server : the question is why this dead lock situation exists - why it is created ?
Many modems (ISPs) have their own explanation. This forum has many examples about modems not being very cooperative.
To work out something that works for every situation, the pfSense DHCP client has some 'advanced' options could be very useful. -
I cannot access my local servers from the internet after the update to 2.5.1 while it was working before the update.
I have checked the firewall but nothing blocked. No changes on the port forwarding.
I can access Pfsense from the internet using HTTPS but not my local server which using HTTP. -
@alanesi said in To 2.5.1 or not ? that is the question :):
I can access Pfsense from the internet using HTTPS
To make that work, you need a firewall rule on the WAN interface.
@alanesi said in To 2.5.1 or not ? that is the question :):
but not my local server which using HTTP
To make that work, you need a NAT rule.
To make it work again, you need to do some step by step NAT troubleshooting.
Can't tell you nothing because you told us close to nothing.2 details :
Opening your https pfSense webserver to the Internet should be IP limited. Normally, its just is not done.
The IP you use to connect to the pfSense from the outside (you do connect from the outside, aren't you ?) indicates that you use the right IP.edit :
A real example :
I have a 'DiskSation' (Synology NAS) living on my LAN. It has IPv4 192.168.1.33
pfSense has 192.168.1.1/24.The HTTPS access of a DiskSation, by default, is 5001.
I added this NAT rule to pfSense :
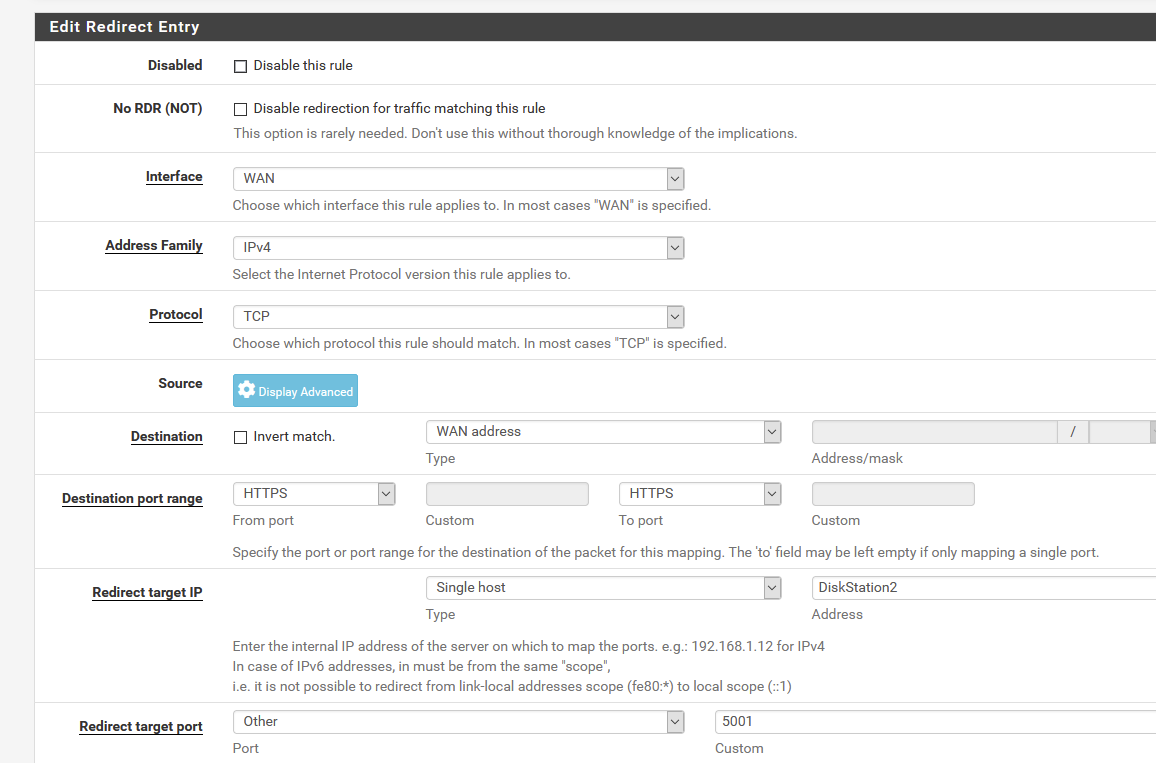
and now I can access - from anywhere from the Internet, my DiskSation using https://myip.tld
Because I'm PATting from 443 to 5001 in pfSense, I t all works right away **
** That is : I also had to NAT my upstream ISP router.
-
@gertjan I appreciate your prompt reply.
I have reviewed the configurations but still cannot find the issue.
-
@yanik Current status, according to https://redmine.pfsense.org/issues/11805:
-
The bug with NAT not working on non-default gateways exists, and has been fixed;
-
However, the patch involves an issue in the kernel, so it is not possible to patch it in-place.
-
It will be included in the next release, but no, they do not know when that will be.
-
From the amount of "I'm experiencing this too" posts there that have been periodically removed by jimp, it seems fairly widespread - I hope that this means that there'll be an interim release prior to 2.6.0, which is far in the future.
-
-
@cellobita said in To 2.5.1 or not ? that is the question :):
From the amount of "I'm experiencing this too" posts there that have been .....
Not enough as you can see.
-
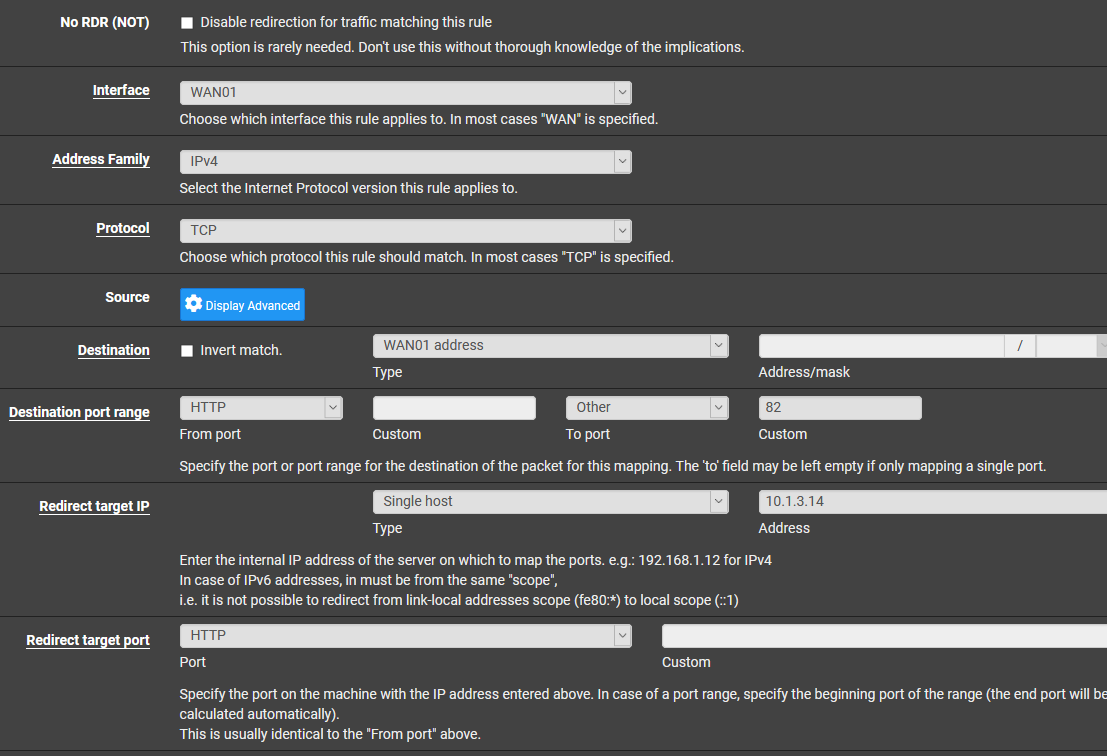
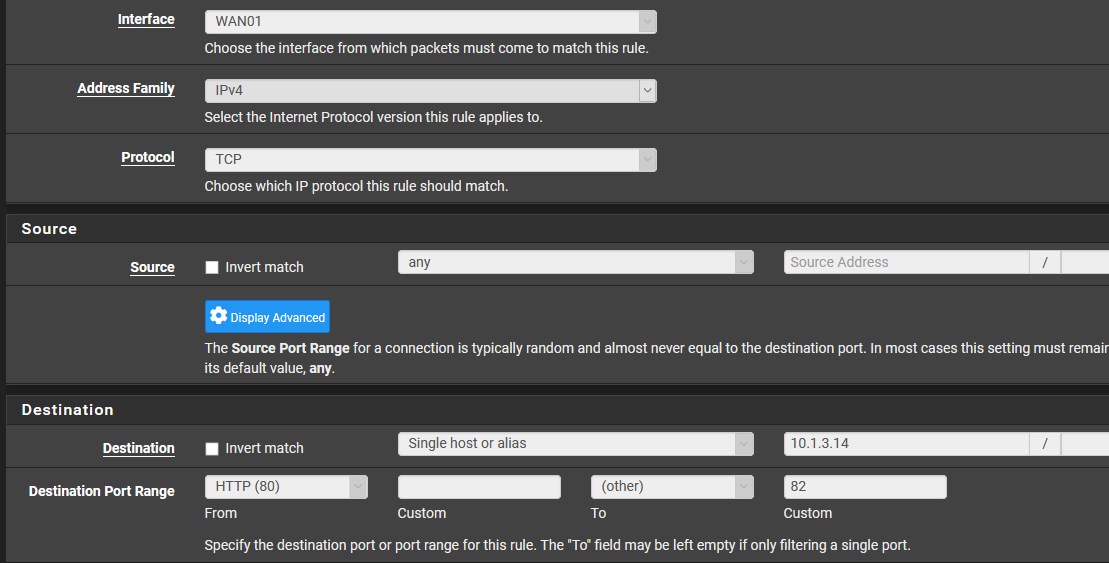
@alanesi Your doing it wrong.
http -> http on wan ports and forwarded to http redirect to internal server
-
Yeah, the port range, from 80 to 82 :
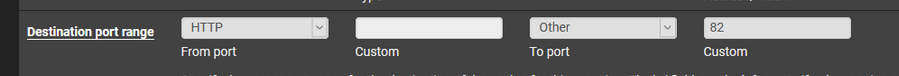
If the port range is needed he would be needing it, I guess.
-
@gertjan I suppose we've been relegated to second-class citizen status - this won't be the first time that an open source project leaves non-paying users behind. Can't say I'm surprised.
OTOH, this has made me look at alternatives to pfSense more closely, which is always a nice idea - one tends to default to familiar paths for new installations (I know I have done that, over the past 12 or so years deploying open source firewalls).
-
1a) does it have a WAN IP ? Is it a valid IP ? Does it have a gateway ? Are these addresses known / seen before.
Yes to all 4 questions.
Step 2 to 11 : sending a ping to some remote network, knowing there is no 'route' only proves there is no route.
It proves the router/firewall isn't routing traffic, which is different than not having a route. The default route was there... and the firewall itself was able to get to the internet... but for some reason, PFsense wasn't routing internal traffic to the internet.
Restarting DNS doesn't has anything to do with routes.
Never said it did. Once the ping to google.com failed, I bounced the DNS service just in case the issue was DNS related vs routing, which has happened before. After that, a failed ping to 8.8.8.8 proved I wasn't able to hit the internet and likely a routing issue of some kind.
It's hard to say what happened in your case, but it could be something like this :
Updating pfsense to 2.5.0 needs a kernel update. To do this, it needs to reboot to load the new kernel. The reboot will take you pfSense WAN NIC down for a moment. The mdoem sees this, and act upon that event, like : a upstream re negotiation.
Anything's possible I suppose. Although, the 2.4.5-p1 -> 2.5.0 upgrade went without issue... it was he 2.5.0 ->2.5.1 that gave me grief, but I get what you're saying. Considering my wife works from home and my son is doing distance learning... I'm just glad I was home to deal with the outage when it happened.
-
Can I restore the settings from version 2.5.1 on a 2.5.0 installation? NAT problems scratched my reputation with my users. I never imagined that something like this could happen with an official pfsense release
-
@bjunior Yes you can. And a lot has been scratched....
-
@cool_corona Thanks for information. I'll do it.