Setting reversed proxy
-
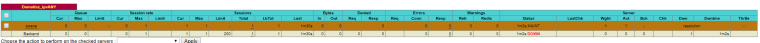
That is from the config file trying to find how to set it in the GUI :P
-
@piba When it's working it say Layer7 check passed: OK
-
@varazir
You already wrote 'Octoprint' in that same textfield you can put the other acl text..As for above maint line it looks like the 'zwave' servername might not resolve DNS easily to a IP? That shouldnt depend on the type of check used anyhow.. Perhaps give it a few seconds more to resolve? And the check again? A L7 check that passes would be good..
-
@piba Well I have to look at the openVPN tomorrow, getting late.
Thanks for your help
-
Where should I place in the GUI this again ? Front or back end ?
use_backend Octoprint_ipvANY if !{ req.ssl_hello_type 1 } !{ req.len 0 } -
@varazir
Where in the gui did you write 'Octoprint'?( For a Frontend - action ? )
--Edit--
Though i think i got your backends mixed up.
Should use the special acl for the 'openvpn' action acl name. -
Word of warning: Make extra sure that you do not expose OctoPrint to the Internet. It is not designed to do that. Keep it locked behind a VPN.
Personally, I run haproxy directly on my OctoPrint Pis (and acme.sh to do the certs). It only takes a very small/simple config. Much more secure that way.
-
@piba said in Setting reversed proxy:
@varazir
Where in the gui did you write 'Octoprint'?( For a Frontend - action ? )
Front end but it's OpenVPN that is the issue. It's on the same port on pfSense.
Octoprint back/frontend works fine
I changed to IP and now the health check works much better. -
@jimp said in Setting reversed proxy:
Word of warning: Make extra sure that you do not expose OctoPrint to the Internet. It is not designed to do that. Keep it locked behind a VPN.
Personally, I run haproxy directly on my OctoPrint Pis (and acme.sh to do the certs). It only takes a very small/simple config. Much more secure that way.
ya I read that.
Octopi comes with HAProxy, I have setup a extra authentication. Using acl / http-request auth not sure if it's enoufe or there are other things that is not designed.How can you open port 80/443 to several hosts that using certbot ?
-
If it's protected by at least some kind of auth it may be OK, but I still would prefer to keep it behind a VPN.
As for certbot, that would probably just get routed based on the requested hostname. Should work with plain http and some ACLs. I use acme.sh and DNS-01 challenges though, I do not want any inbound web requests hitting my Pis.
-
@varazir
Yes sorry i mixed up your backends/acls.. Where i wrote octoprint i ment openvpn at least for the last few posts..use_backend Openvpn_ipvANY if !{ req.ssl_hello_type 1 } !{ req.len 0 }Anyhow still location to put that is the frontend/action acl-name.
-
@piba said in Setting reversed proxy:
@varazir
Yes sorry i mixed up your backends/acls.. Where i wrote octoprint i ment openvpn at least for the last few posts..use_backend Openvpn_ipvANY if !{ req.ssl_hello_type 1 } !{ req.len 0 }Anyhow still location to put that is the frontend/action acl-name.
acl name :) thanks found the field thanks.
Now everything works.
-
@jimp said in Setting reversed proxy:
If it's protected by at least some kind of auth it may be OK, but I still would prefer to keep it behind a VPN.
As for certbot, that would probably just get routed based on the requested hostname. Should work with plain http and some ACLs. I use acme.sh and DNS-01 challenges though, I do not want any inbound web requests hitting my Pis.
I'm looking at the script I was using the command line that came with Let's Encrypt and this guide
https://www.digitalocean.com/community/tutorials/how-to-secure-haproxy-with-let-s-encrypt-on-ubuntu-14-04
This all started more or less with getting the Lets encrypt not needing to do a portforward each time.
-
If you are going to run all the haproxy bits on pfSense there is a script you can use to hook into the ACME package to handle all of that locally for any hostname.
https://forum.netgate.com/topic/90643/let-s-encypt-support/31
-
@jimp said in Setting reversed proxy:
If you are going to run all the haproxy bits on pfSense there is a script you can use to hook into the ACME package to handle all of that locally for any hostname.
https://forum.netgate.com/topic/90643/let-s-encypt-support/31
Hmm don't understand what it dose.
So I still run the rewnew/setup on the host on then LAN ?
-
The ACME package on pfSense would handle all of the certs, haproxy on pfSense would offload all SSL tasks from local devices. So for example you'd connect https to the firewall and it would hand off http to the octopi backend.
That may not be exactly what you're after but it would be an easy centralized solution.
-
@jimp Hmm sound much easier. Like the idea.
I guess I need to remake the backends on the current setup right ?I guess that will not work when I use https internal ?
-
@varazir
It is possible to keep the webservers the same as they are, HAProxy would need to be reconfigured though to decrypt traffic on a (second) frontend (but not for openvpn), and re-encrypt traffic send to the webserver. Or reconfigure the webservers to accept connections on :80 while 'understanding' that the actual connection from the client is really made over https (so they dont respond with a redirect to https or a absolute link to a http:// resource).. some web-applications are not easily configured to do so though.. -
-
@varazir
That 'message' is not a error, its just some 'unexpected' output as far as the haproxy package is considered.. You could remove that version output from the acme script if you like..If you want to use certificates on haproxy, then first step is to get the certificate to use into pfSense certificate manager, can use a combination of haproxy with acme package for that, as for the current configuration you need to 'offload' and configure a certificate on the frontend, and then check the ssl encyption checkbox on the backend servers. And configure the proper acl's based on host header instead of sni indication.
And because you also still want to pass along the openvpn traffic, the first frontend cannot do the ssl offloading, as openvpn does not use regular ssl. So need to make a second frontend and loopback the connection from a backend on the first one, to the second local frontend used for the https website connections.Basically back to post #2 : https://314es.pl/https-openvpn-and-ssh-on-one-port-thanks-to-haproxy