pfSense XML config file, can we decrypt it manually?
-
Hi,
I started encrypting the configuration export of my pfSense appliance. And I was wondering how should I proceed, if I wanted to manually decrypt the xml export. Obviously, I have the password. I am just really not to sure about how the file gets encrypted; I don't even know the cipher.
Anyone knows about this? I always review the .xml file before importing but once encrypted... It becomes a bit tedious (and unsafe!) to import blindly, and then export it in clear text again for review. I am sure there is no "secret sauce" about the file encryption either.
Thank you.
-
Hooray for open source software; everything is in clear somewhere.... Once I found /etc/inc/crypt.inc, I knew what had to be done.
As it turns out, I am able to decrypt a configuration backup with a one liner;
openssl enc -d -a -aes-256-cbc -in config.xml -out output.txtI can now encrypt my backups knowing they can be read/compared before I restore them. :)
-
Yes I use this if I need to decrypt it as the file is base64 encoded also.
You will need to extract that and then decrypt it. That can be done from a Linux box using the following command:
cat /tmp/config-enc.xml | sed -e '1d' -e '$d' | base64 -d | openssl enc -d -aes-256-cbc -out /tmp/config-dec.xml -k '12345'Or it can be done on the firewall itself if a Linux box is not available using the following command :
cat /tmp/config-enc.xml | sed -e '1d' -e '$d' | b64decode -r | openssl enc -d -aes-256-cbc -out /tmp/config-dec.xml -k '12345'Where 12345 is the password.
Steve
-
Fair warning, if you are running that command on a system with OpenSSL 1.1.1 and the file was encrypted on pfSense 2.4.x, you'll want to add
-md md5to the end of the command line parameters. -
Thanks for the tips, everyone!
I put together everyone's suggestions into this script:
https://gist.github.com/JonathonReinhart/d78e56586c6fd976d3bc52ee4614a083 -
Nice. I would probably output to a file though for all but the simplest configs. If you have a multi-megabyte config it can become...... challenging!
Steve
-
I am really regretting the long, randomly generated password full of special characters used to encrypt my configs right now. Can't seem to correctly escape the contained single quote (assuming that that's the only character that needs to be escaped when the rest is contained within single quotes). I keep getting 'bad decrypt'.
-
from : man enc (linux)
-k password The password to derive the key from. This is for compatibility with previous versions of OpenSSL. Superseded by the -pass argument. -kfile filename Read the password to derive the key from the first line of filename. This is for compatibility with previous versions of OpenSSL. Superseded by the -pass argument. -pass arg The password source. For more information about the format of arg see the PASS PHRASE ARGUMENTS section in openssl(1).You could try to paste the "ugly passwd" into a file (pass.txt) , on the first line.
Then instead of -k 'pass' , use -kfile pass.txt
Seems like -kfile <filename> is superseded by -pass file:<filename>
But both should still work.Edit:
Remember your pass is now saved in a file , cleanup appropriately/Bingo
-
@bingo600 Tried that and I still get the same result.
*** WARNING : deprecated key derivation used. Using -iter or -pbkdf2 would be better. bad decrypt 140140608259392:error:06065064:digital envelope routines:EVP_DecryptFinal_ex:bad decrypt:../crypto/evp/evp_enc.c:610:Thanks for the suggestion, though.
-
Did you try both variants ?
What version is the encryption made with
Re: @jimp post here
https://forum.netgate.com/post/884969/Bingo
-
I should have checked the docs before the forum. File I was trying first was from 2.5.0 which uses different encryption.
https://docs.netgate.com/pfsense/en/latest/backup/restore.html#encrypted-configuration-files
-
-
Encrypted Configuration files
The GUI can automatically determine the correct decryption method when restoring an encrypted configuration backup file, whether it’s from a current version or an older version. When restoring an encrypted configuration file, check Configuration file is encrypted then enter the password in the Password field, and restore as usual from there.Encrypted configuration files can be manually decrypted using the correct password for offline inspection.
The method used to encrypt configuration files changed in version 2.5.0, so use the method appropriate for the version which generated the encrypted configuration file. In either case, replace <PASSWORD> with the appropriate password string, and change the filenames as needed.
2.5.0 and later:
grep -v "config.xml" config-encrypted.xml | base64 -d | \ openssl enc -d -aes-256-cbc -out dencryptedfile.xml \ -pass pass:<PASSWORD> -salt -md sha256 -pbkdf2Older versions:
grep -v "config.xml" config-encrypted.xml | base64 -d | \ openssl enc -d -aes-256-cbc -out dencryptedfile.xml \ -pass pass:<PASSWORD> -salt -md md5
In my case, I changed
pass pass:<PASSWORD>topass file:<PASSFILE>. -
So...what is the password??? Same as admin?
-
@kevinrice No, the password is whatever you put in the password box that appears after ticking the 'Encryption' checkbox.
-
@seamonkey Oh, no. Not good. I'm using a Calix brand router running pfSense that is locked-down. So there's no way to decrypt its config file then.
-
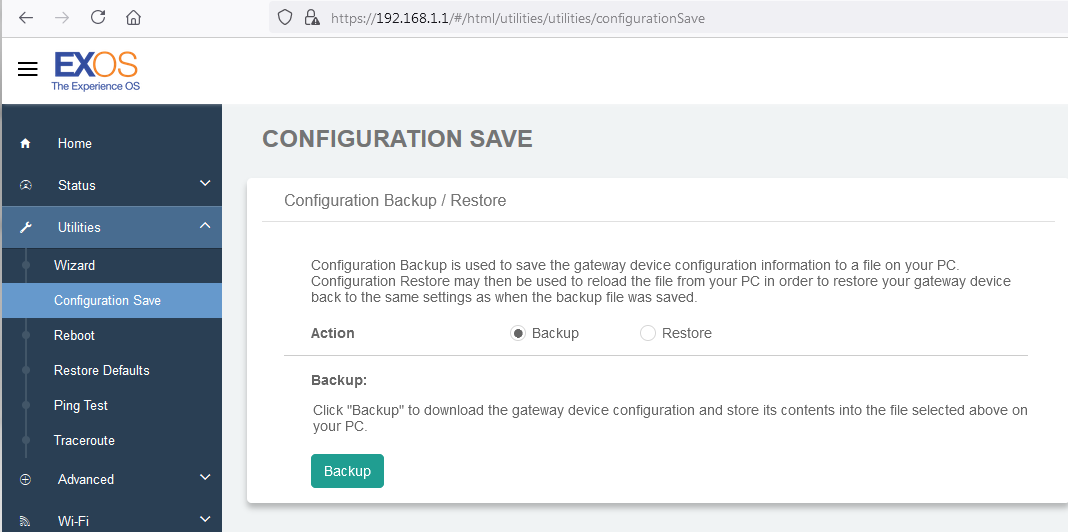
@kevinrice If you have the admin password and you're just trying to get an unencrypted copy of the current configuration, you can just login, go to Diagnostics | Backup & Restore, and download the configuration file.
-
@seamonkey I don't think that is possible. The Calix router is crippled. While there is a configuration backup page, the encryption is baked-in. I can't see any way of getting an unencrypted config file here.
-
Well that's..... um... interesting.
Reboot into single user mode, check the code?
Are you sure that's a pfSense rebrand and not just a cached favicon in your browser?
Edit: Yeah, almost certainly that ^
Steve
-
@stephenw10 Yeah, I suppose that's likely. Login screen sure looks familiar. And the config file begins:
<!--CalixVersion="0.0.0.0" crc32="03933f14" type="backup" product="17717" ConfigVersion="21.2.0.0.39" model="GS4220E" -->pfSense v.21.2 is very contemporary!
In any case, if I don't have access to the password, it would seem I'm chasing ghosts.