No Internet from WIFI connection on Router from 2nd LAN subnet
-
Hi everyone,
I have 3 physical interfaces on my pfsense box.
WAN
LAN = 10.1.10.0/24 , interface ip4v = 10.1.10.1/24
DEVICES_LAN = 10.1.13.0/24, interface ipv4 = 10.1.13.1/24DEVICES_LAN just has an ASUS router with DHCP enabled connected to it (Connected to the non-WAN port on the router). This will just be for connecting cameras, smart devices, game consoles, etc.
When I connect to the wifi from the router on DEVICES_LAN using my smartphone, it never gets internet. It will get the correct LAN IP in the 10.1.13.0/24 subnet.
Below are the ASUS router details I configured and firewall/NAT rules. Do you guys see what the issue is? The only thing I can think of is maybe my DNS or default gateway is wrong but I just playing around with it to no success.
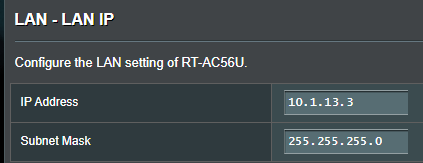
Router LAN IP:
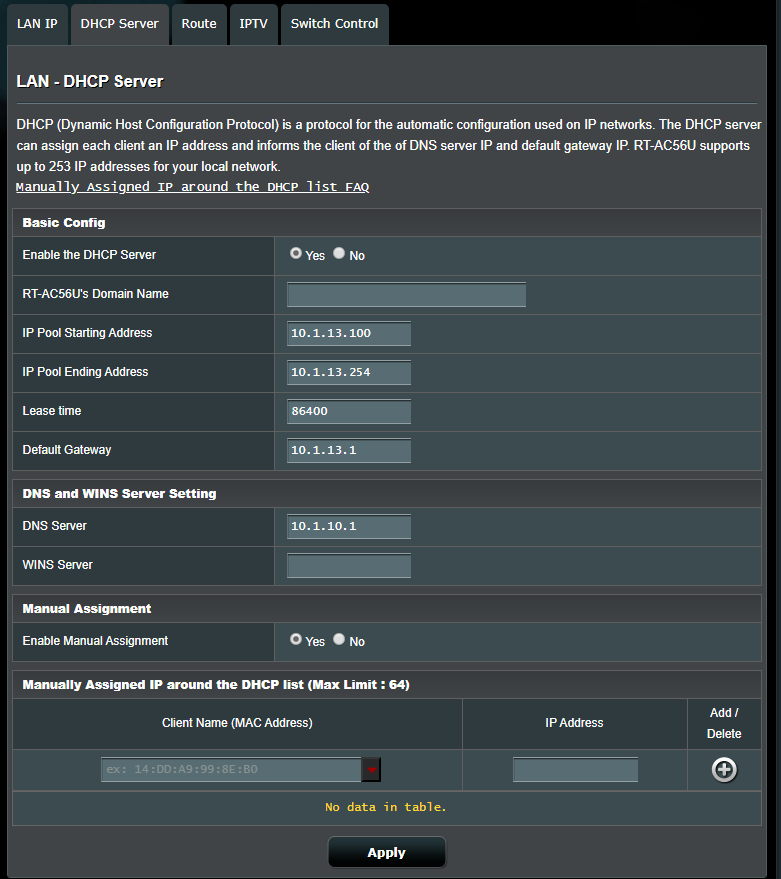
Router DHCP Server:
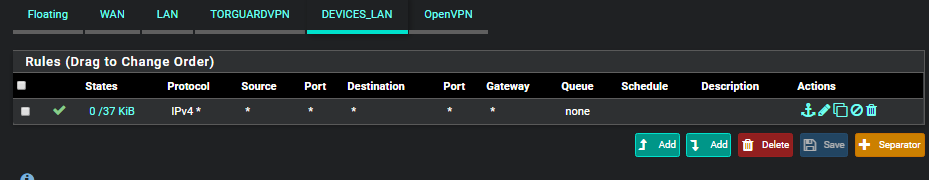
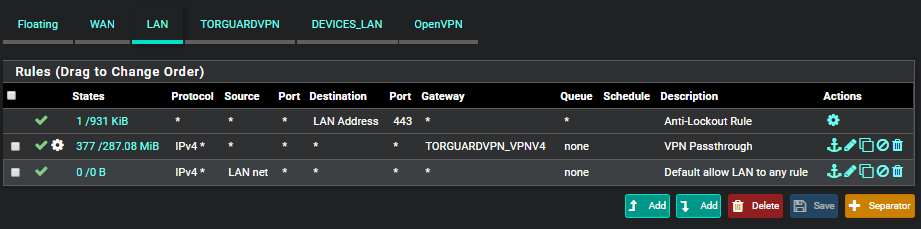
PFSENSE FIREWALL:
PFSENSE OUTBOUND NAT:

Thank you for your help and let me know if you need any other information. I'll continue playing around and update if I find the fix.
-
hmm, I changed the DNS server to an eternal one 8.8.8.8 and internet is working! (I'm pretty sure I tried this before and it didn't work but maybe I changed another setting inbetween that time).
Not sure if that is proper though.. Does this mean it is skipping over my security in the firewall like pfblockerng?
-
Assuming you're using the resolver, my guess is you need to add an ACL to allow queries from the 10.1.13.0/24 subnet. Also, you need to verify that the resolver is listening on the "DEVICES_LAN" interface.
And yes... using 8.8.8.8 will send your client's queries to google which will bypass any security settings, filtering, DNSBL, etc being leveraged by the resolver.
-
@marvosa Thank you, I will try that. I am indeed using DNS resolver. I believe it is listening to all interfaces/networks right now.
I'll report back on my results!
-
@marvosa That worked! I added the ACL for 10.1.13.0/24 and then I set the DNS server as 10.1.13.1 (the ip of my Device_LAN interface on pfsense. Thanks marvosa!
-
@marvosa Interesting, actually I don't think I needed the ACL. I deleted it and internet it still working. Maybe I just needed to change the DNS server to 10.1.13.1.
-
Yeah, I'm not sure why you set it to 10.1.10.1 initially? By default it would use the interface IP, 10.1.13.1 in this case.
I'm not sure that last time I tested something like that but it expects queries to come from IPs in the same subnet.Is there any reason you're not using pfSense as the dhcp server for that subnet?
Steve
-
@stephenw10 Hey Steve! I'm not sure why I did that either..lol.
In regards to using pfSense as my DHCP for the subnet - no reason really, I thought i'd just set the ASUS router to be the DHCP server and separate it from my pfSense box. Would you say that is more or less secure? (or better or worse).
I can change pfSense to my DHCP for that subnet, if you guys think its better/more secure. On my other subnet my windows server is the DHCP server for the 10.1.10.0/24 subnet.
Thanks!
-
@techgeek055 said in No Internet from WIFI connection on Router from 2nd LAN subnet:
I can change pfSense to my DHCP for that subnet, if you guys think its better/more secure. On my other subnet my windows server is the DHCP server for the 10.1.10.0/24 subnet.
Personally, I like to manage all my scopes in one place. So, if you already have Windows Server providing DHCP on another subnet, I would disable DHCP/DNS on your ASUS, create a new scope on your Windows server and then enable DHCP relay on the "DEVICES_LAN" interface and point it at your windows server. This way your Windows Server will provide DHCP for both segments of the network and both scopes will be centrally managed.
-
@marvosa I would love to do that! Althought the last time I tried, I failed. I will give it another try with your pointers. Hopefully it goes well :(
-
@marvosa I added the DHCP relay on my 10.1.13.1 interface and pointed it to my 10.1.10.8 dhcp server, disabled dhcp server option on my asus router but wifi just hangs on "Obtaining IP Address..."
Are there any other settings you can think of that I may need to configure?
-
A few things I can think of:
- Verify that the DHCP relay is bound to the correct interface
- Verify the LAN interface has firewall rules to allow communication to the DEVICES_LAN interface
- Verify the new scope is active on your Windows Server
After verifying the above, either reboot or do an ipconfig /release and ipconig /renew on all your clients or they will continue to contact the last DHCP server they previously connected to until 1/2 the lease expires.
-
Confirmed that:
-
DHCP relay is on my Devices_LAN
-
LAN Firewall is currently allowing everything
-
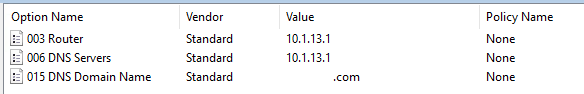
10.1.13.0 / 24 scope is active on the DHCP on windows server with below settings:
Still getting stuck on the "Obtaining IP address" stage" even after rebooting my smartphone.
Im beginning to think my DHCP server on the windows server is broken some how....I may consider/try re-installing the DHCP role..
-
-
@techgeek055
My apologies, one thing I made an assumption that you knew about and forgot to mention is, disabling those services on the ASUS is the manual way of turning your wireless router into an AP. After that, you have to move the patch cord that's currently plugged into the WAN port and move it to one of your LAN ports. ASUS on the other hand, has an AP mode, which disables the previously mentioned services automatically, however, you still have to move the patch cable into one of the LAN ports on the ASUS. Was this done?
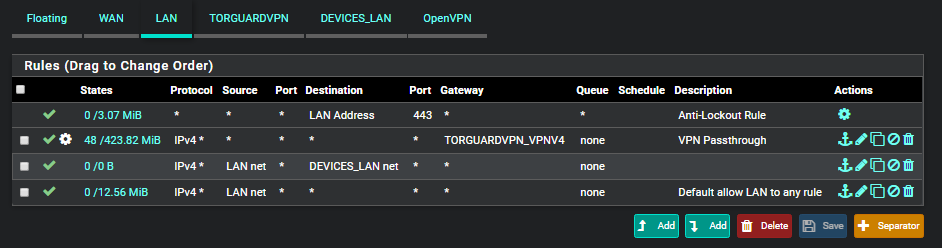
Also, notice that your LAN net/any rule does has no hits. The rules are parsed top-down so all of your traffic is being matched on the 2nd rule and being routed down the VPN, which I'm sure is also contributing to the issue. I would need to see the routing table, but you may need to add a LAN net/DEVICES_LAN rule that routes traffic using the routing table and place it above that 2nd rule. However, we need to make sure that dhcp traffic is making to PFsense first... hence moving the physical connections on the ASUS.
-
No worries, I appreciate your help to the fullest!
My ASUS router was already plugged into one of the LAN ports. I have now switched the router to AP mode.
I completely removed and re-installed my dhcp server but that didn't seem to fix anything :D
I made new LAN rule like this:
-
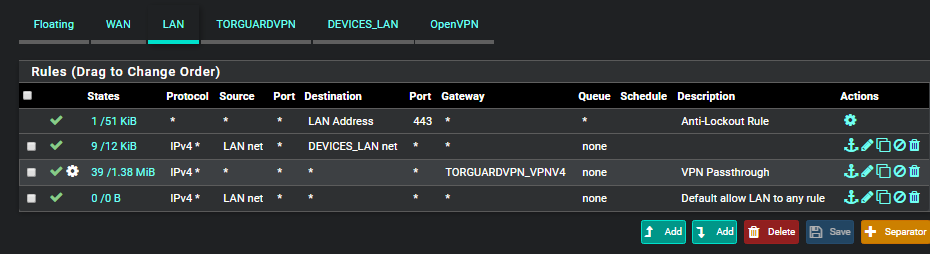
@techgeek055 Swap rules 2 and 3.
-
@marvosa My bad.
I have it like this now but smartphone still stuck trying to obtain in ip address:
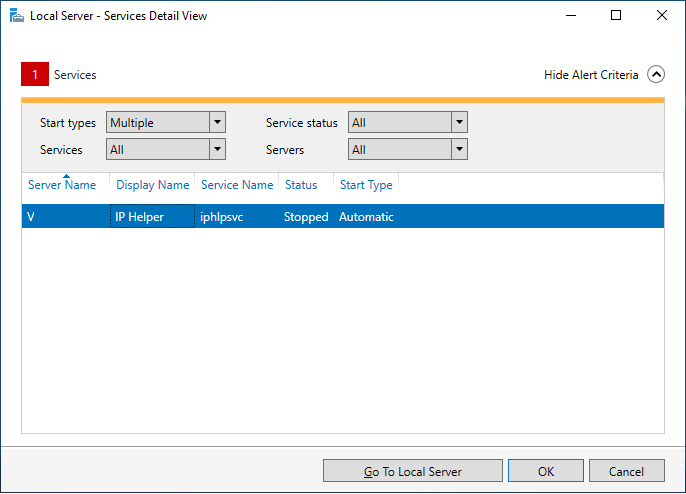
I noticed by DHCP server has the IP helper service not started. I don't think that is causing this issue by i'll try re-enabling it..
-
@marvosa doesn't look like starting the IP helper fixed it either :/
My DHCP server is connected to a switch, and the switch is connected to the 10.1.10.0 LAN interface on pfsense, don't think that makes a difference though..
-
Do you have a laptop you can troubleshoot with? I think we need a little more insight as to what's happening on the client.
Also, can you post a network map so we have a little more insight as to your network design? Since I haven't heard anything about VLANs, my assumption is you have 3 NIC's in your PFsense box... 1 for WAN, 2 for LAN... and two different switches... one connected to each LAN interface. That's my assumption, but I'd like to get a more accurate picture from you.
For grins and giggles, disable the windows firewall on your server and try a few clients. If things miraculously start working, you'll have to add some exceptions in the firewall or leave it disabled.
-
@techgeek055 After some research, it looks like what we need to do is go back into DHCP relay, hold ctrl and highlight the LAN interface so both LAN and DEVICES_LAN are highlighted and hit save.