StrongSwan user authentication failed on Android
-
@Alanesi said in StrongSwan user authentication failed on Android:
ignore candidate 'con-mobile' without matching IKE proposal
Check the phase-1 settings on both sides of the tunnel . If the Windows client is working perfectly , it is possible that an error occurred in the Android client settings.
P.S. I would recommend selecting the CA certificate manually in the client settings
-
I did the manual selection for the CA. I'll see what else I can change.
-
The user [user@domain.com] created ?
Aug 8 14:59:23 charon 16[CFG] <2431> looking for peer configs matching x.x.x.x[%any]...y.y.y.y[user@domain.com]
Aug 8 14:59:23 charon 16[CFG] <2431> ignore candidate 'con-mobile' without matching IKE proposal -
Yes, and its working on windows
-
@Alanesi
Then you need to check the settings of the Android client
There may be an error in the username/password field -
@Konstanti
Unfortunately still the same issue but with different log
This is from pfSense:Aug 8 17:01:25 charon 16[CFG] <2464> looking for IKEv2 configs for x.x.x.x...y.y.y.y
Aug 8 17:01:25 charon 16[CFG] <2464> candidate: %any...%any, prio 24
Aug 8 17:01:25 charon 16[CFG] <2464> candidate: x.x.x.x...%any, prio 1052
Aug 8 17:01:25 charon 16[IKE] <2464> no matching proposal found, trying alternative config
Aug 8 17:01:25 charon 16[CFG] <2464> selecting proposal:
Aug 8 17:01:25 charon 16[CFG] <2464> proposal matches
Aug 8 17:01:25 charon 16[CFG] <2464> received proposals: IKE:AES_CBC_128/AES_CBC_192/AES_CBC_256/3DES_CBC/HMAC_SHA2_256_128/HMAC_SHA2_384_192/HMAC_SHA2_512_256/HMAC_SHA1_96/AES_XCBC_96/PRF_HMAC_SHA2_256/PRF_HMAC_SHA2_384/PRF_HMAC_SHA2_512/PRF_AES128_XCBC/PRF_HMAC_SHA1/ECP_256/ECP_384/ECP_521/ECP_256_BP/ECP_384_BP/ECP_512_BP/CURVE_25519/MODP_3072/MODP_4096/MODP_6144/MODP_8192/MODP_2048, IKE:AES_GCM_16_128/AES_GCM_16_192/AES_GCM_16_256/CHACHA20_POLY1305/AES_GCM_12_128/AES_GCM_12_192/AES_GCM_12_256/AES_GCM_8_128/AES_GCM_8_192/AES_GCM_8_256/PRF_HMAC_SHA2_256/PRF_HMAC_SHA2_384/PRF_HMAC_SHA2_512/PRF_AES128_XCBC/PRF_HMAC_SHA1/ECP_256/ECP_384/ECP_521/ECP_256_BP/ECP_384_BP/ECP_512_BP/CURVE_25519/MODP_3072/MODP_4096/MODP_6144/MODP_8192/MODP_2048
Aug 8 17:01:25 charon 16[CFG] <2464> configured proposals: IKE:AES_CBC_128/AES_CBC_192/AES_CBC_256/CAMELLIA_CBC_128/CAMELLIA_CBC_192/CAMELLIA_CBC_256/3DES_CBC/HMAC_SHA2_256_128/HMAC_SHA2_384_192/HMAC_SHA2_512_256/HMAC_SHA1_96/AES_XCBC_96/AES_CMAC_96/PRF_HMAC_SHA2_256/PRF_HMAC_SHA2_384/PRF_HMAC_SHA2_512/PRF_AES128_XCBC/PRF_AES128_CMAC/PRF_HMAC_SHA1/ECP_256/ECP_384/ECP_521/ECP_256_BP/ECP_384_BP/ECP_512_BP/CURVE_25519/MODP_3072/MODP_4096/MODP_6144/MODP_8192/MODP_2048, IKE:AES_GCM_16_128/AES_GCM_16_192/AES_GCM_16_256/AES_GCM_12_128/AES_GCM_12_192/AES_GCM_12_256/AES_GCM_8_128/AES_GCM_8_192/AES_GCM_8_256/PRF_HMAC_SHA2_256/PRF_HMAC_SHA2_384/PRF_HMAC_SHA2_512/PRF_AES128_XCBC/PRF_AES128_CMAC/PRF_HMAC_SHA1/ECP_256/ECP_384/ECP_521/ECP_256_BP/ECP_384_BP/ECP_512_BP/CURVE_25519/MODP_3072/MODP_4096/MODP_6144/MODP_8192/MODP_2048
Aug 8 17:01:25 charon 16[CFG] <2464> selected proposal: IKE:AES_CBC_128/HMAC_SHA2_256_128/PRF_HMAC_SHA2_256/ECP_256
Aug 8 17:01:25 charon 16[CFG] <2464> received supported signature hash algorithms: sha256 sha384 sha512 identity
Aug 8 17:01:25 charon 16[IKE] <2464> remote host is behind NAT
Aug 8 17:01:25 charon 16[CFG] <2464> sending supported signature hash algorithms: sha256 sha384 sha512 identity
Aug 8 17:01:25 charon 16[IKE] <2464> sending cert request for "CN=internal-ca, C=SA, L=Riyadh, O=International"
Aug 8 17:01:25 charon 16[ENC] <2464> generating IKE_SA_INIT response 0 [ SA KE No N(NATD_S_IP) N(NATD_D_IP) CERTREQ N(FRAG_SUP) N(HASH_ALG) N(CHDLESS_SUP) N(MULT_AUTH) ]
Aug 8 17:01:25 charon 16[NET] <2464> sending packet: from x.x.x.x[500] to y.y.y.y[40538] (305 bytes)
Aug 8 17:01:25 charon 16[NET] <2464> received packet: from y.y.y.y[51903] to x.x.x.x[4500] (448 bytes)
Aug 8 17:01:25 charon 16[ENC] <2464> parsed IKE_AUTH request 1 [ IDi N(INIT_CONTACT) CPRQ(ADDR ADDR6 DNS DNS6) N(ESP_TFC_PAD_N) SA TSi TSr N(MOBIKE_SUP) N(NO_ADD_ADDR) N(MULT_AUTH) N(EAP_ONLY) N(MSG_ID_SYN_SUP) ]
Aug 8 17:01:25 charon 16[CFG] <2464> looking for peer configs matching x.x.x.x[%any]...y.y.y.y[user@domain.com]
Aug 8 17:01:25 charon 16[CFG] <2464> candidate "bypasslan", match: 1/1/24 (me/other/ike)
Aug 8 17:01:25 charon 16[CFG] <2464> candidate "con-mobile", match: 1/1/1052 (me/other/ike)
Aug 8 17:01:25 charon 16[CFG] <2464> ignore candidate 'con-mobile' without matching IKE proposal
Aug 8 17:01:25 charon 16[CFG] <bypasslan|2464> selected peer config 'bypasslan'
Aug 8 17:01:25 charon 16[IKE] <bypasslan|2464> peer requested EAP, config unacceptable
Aug 8 17:01:25 charon 16[CFG] <bypasslan|2464> no alternative config found
Aug 8 17:01:25 charon 16[IKE] <bypasslan|2464> processing INTERNAL_IP4_ADDRESS attribute
Aug 8 17:01:25 charon 16[IKE] <bypasslan|2464> processing INTERNAL_IP6_ADDRESS attribute
Aug 8 17:01:25 charon 16[IKE] <bypasslan|2464> processing INTERNAL_IP4_DNS attribute
Aug 8 17:01:25 charon 16[IKE] <bypasslan|2464> processing INTERNAL_IP6_DNS attribute
Aug 8 17:01:25 charon 16[IKE] <bypasslan|2464> received ESP_TFC_PADDING_NOT_SUPPORTED, not using ESPv3 TFC padding
Aug 8 17:01:25 charon 16[IKE] <bypasslan|2464> peer supports MOBIKE
Aug 8 17:01:25 charon 16[ENC] <bypasslan|2464> generating IKE_AUTH response 1 [ N(AUTH_FAILED) ]
Aug 8 17:01:25 charon 16[NET] <bypasslan|2464> sending packet: from x.x.x.x[4500] to y.y.y.y[51903] (80 bytes)
Aug 8 17:01:25 charon 16[IKE] <bypasslan|2464> IKE_SA bypasslan[2464] state change: CONNECTING => DESTROYING -
do you have set dns sec on your android?
-
No, but to wich server?
-
okay, did you set the user identity under advance settings on the strongswan app?
-
@Alitai
Yes its the same username. -
okay, on the android part there is not much more to todo.
Normally this is the easy part.Now, I think it's time for pictures from your pfsense and android. but don't forget to deleted the sensitive Infos.
-
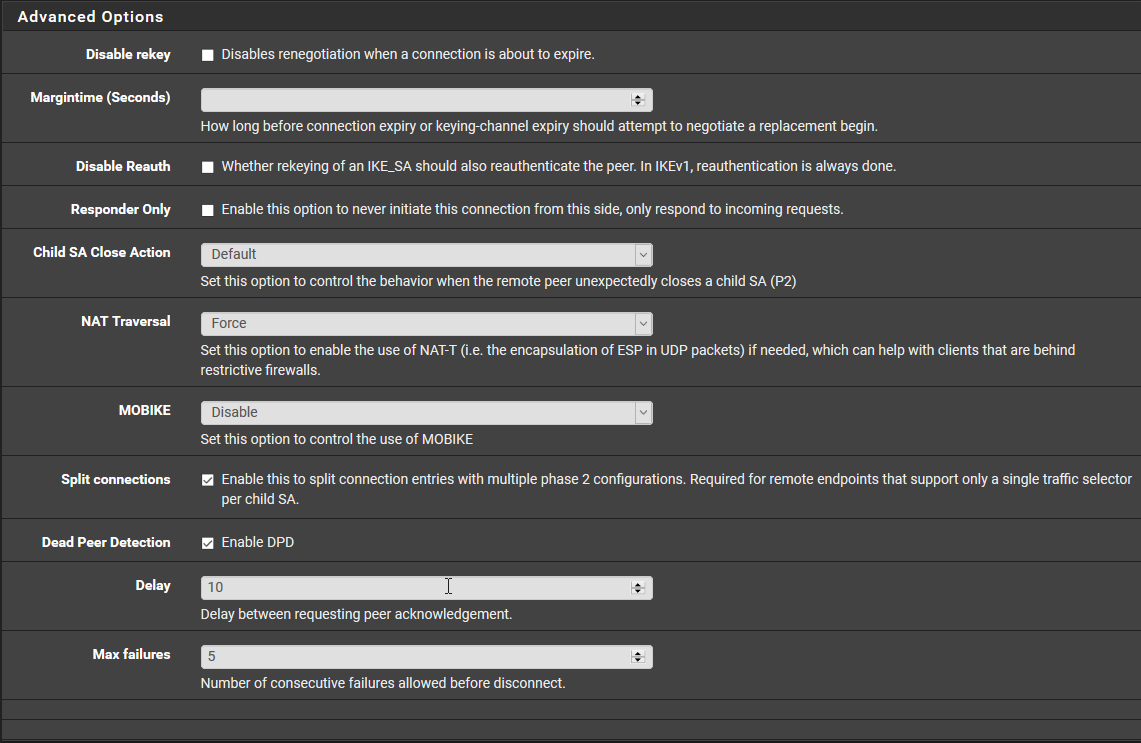
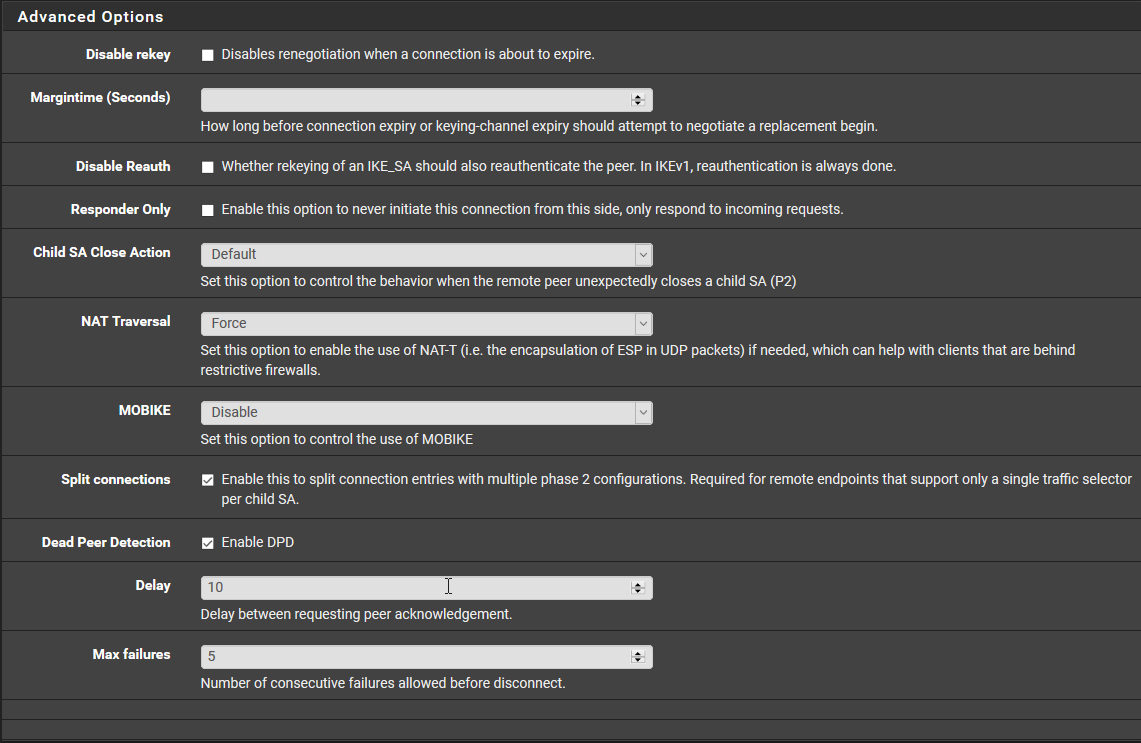
@Alitai
This the P1 on pfSense.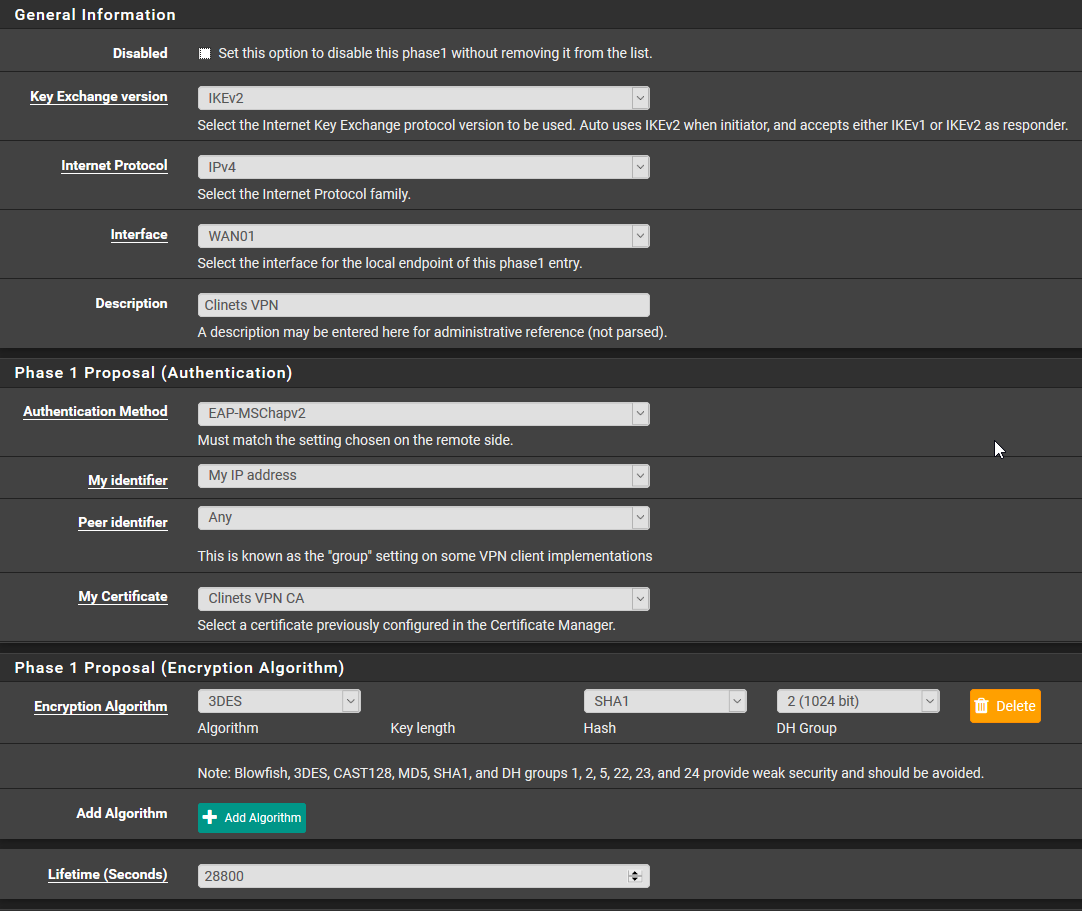
This Mobile Client
For the Pre-Shared Keys the secret type is EAP.
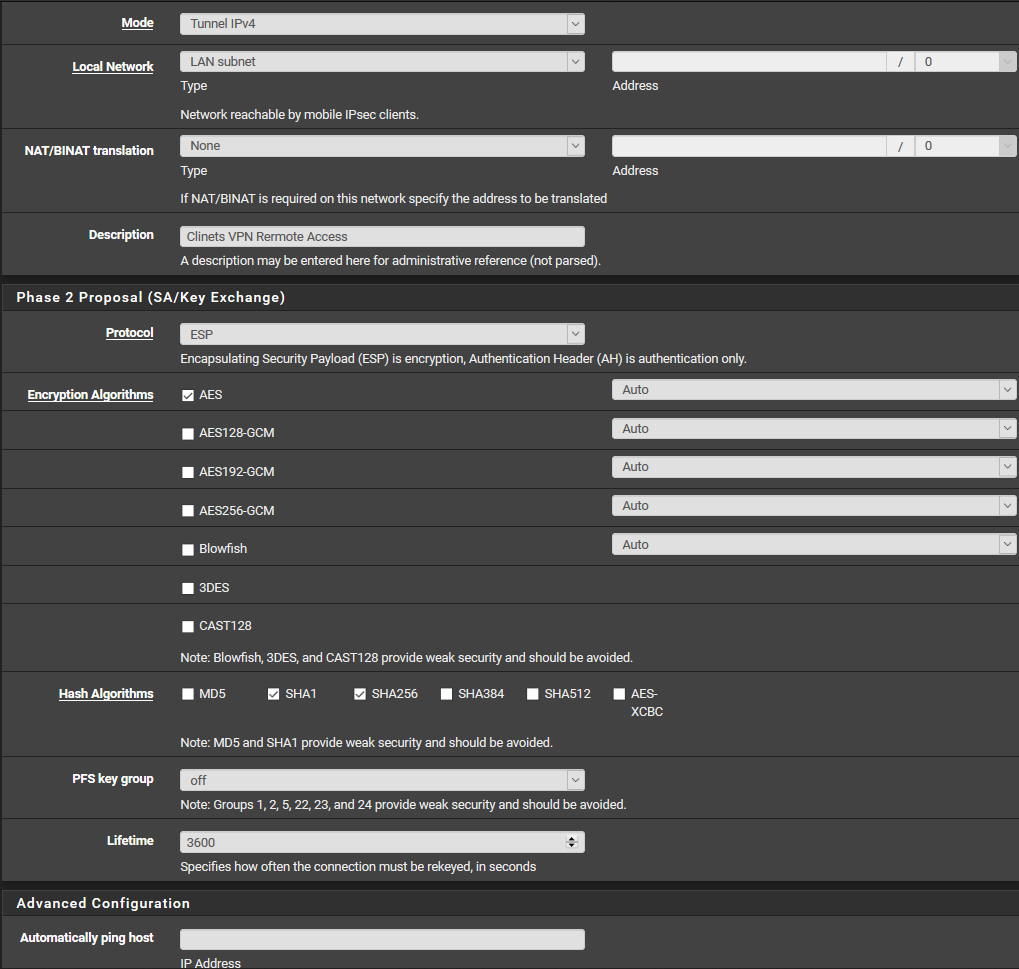
This P2
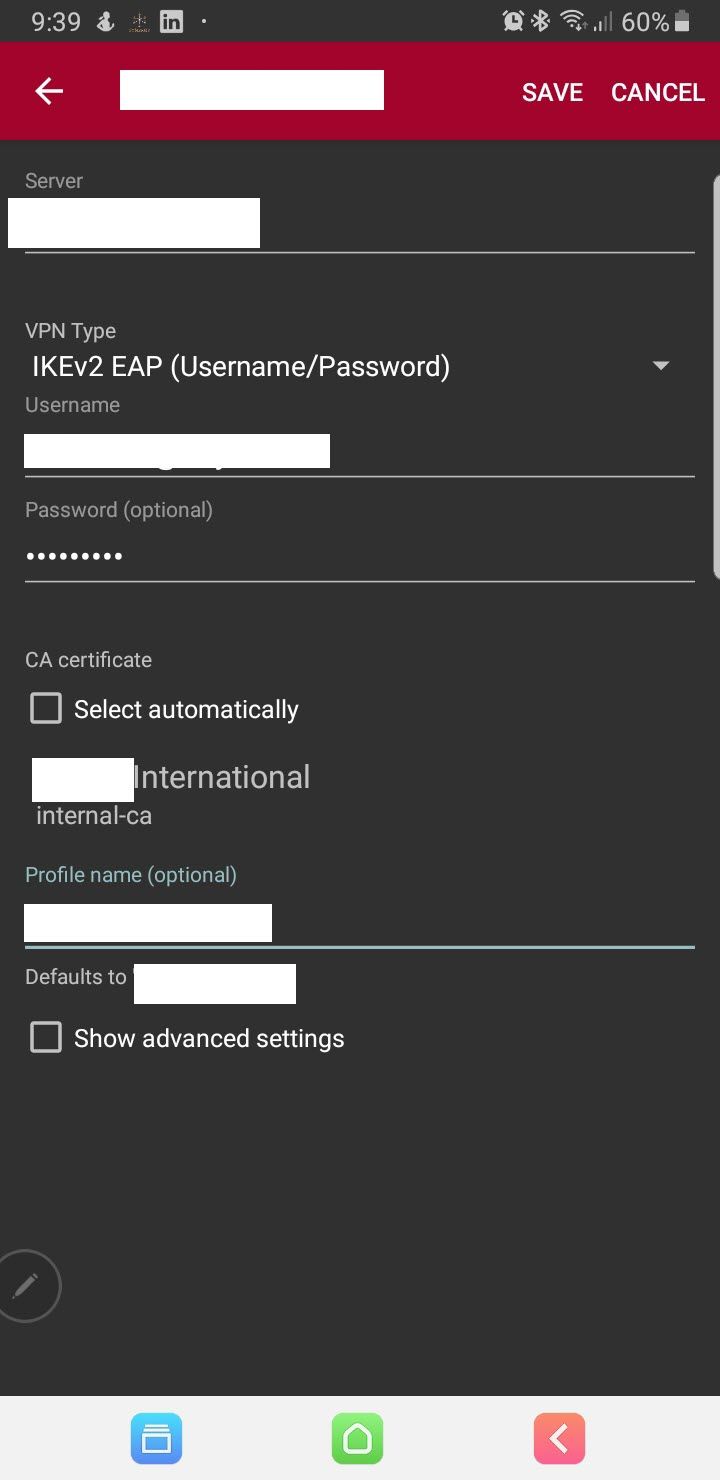
This on the Andriod
-
@Alanesi
Phase 1 - My identifier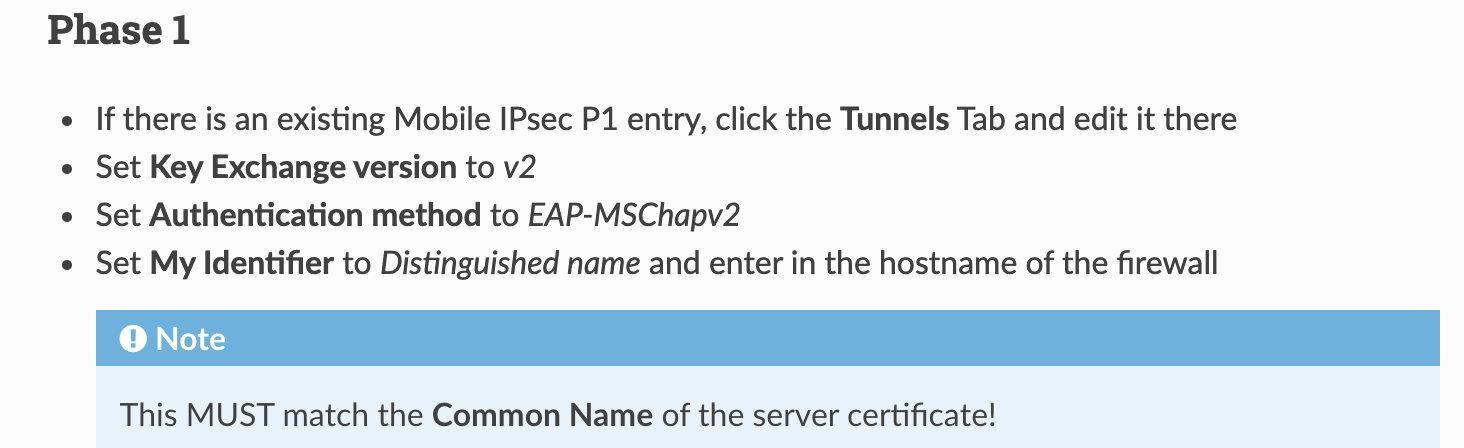
-
Thanks @Konstanti
I did that but it didnt make any diffreance still same error.
-
Phase 1:
Switch to:
AES / 256 bits / SHA256 / 14 (2048 bit)
and
Enable MOBIKEAndroid:
Don't forget the advanced settings (see above). -
