Very Basic IPv6 security question.
-
@guardian said in Very Basic IPv6 security question.:
Are you telling me that I need to add firewall rules to the WAN?
The pfSense WAN firewall rule list is perfect as it was the day you installed pfSense.
And not only pfSense. Every router / firewall on planet earth, and probably in this solar system.
It's empty.
So : nothing gets in.@guardian said in Very Basic IPv6 security question.:
Can you please explain how ICMPv6 should be enabled?
Euh ... same way as ICMPv4 is 'enabled'.
Normally, the default LAN firewall rules (Netgate put them there - you saw them when you installed pfSense) will take care of things.
The role of ICMPv6 is more important as what ICMPv4 does.@guardian said in Very Basic IPv6 security question.:
Then there is the size of the tables for AD blocking etc. just the increased sizze of the address alone causes the tables to balloon, and than there is the sheer number of extra addresses.
Do you run an ad blocker or attempt to control the behavior of Applications or IoT devices/
True. In the future, it will be harder to keep a list with IPs or networks with 'known sources'.
Even the number of domain names is growing every day. Every domain name can point to many IPs.
Gradually, we, humans, will have to change.
If you don't want to see all the garbage, don't go looking for it.
That is : do not use tools/stuff/whatever (applications) that pulls in all this stuff.@guardian said in Very Basic IPv6 security question.:
the firewall block all uninitiated incoming by default
That's the principal role of a firewall.
initiated traffic on the trusted network(s) (LAN) passes, and replies for this that come back, is granted.
Traffic initiated on the non trusted network(s) (WAN) is blocked.@guardian said in Very Basic IPv6 security question.:
I still need to figure out how to create the necessary IPv6 paths in my managed switch
A switch is a dumb device that uses MAC addresses, which are a level lower.
A witch doesn't bother with TCP, UDP, ICMP or higher IPX, IPv4, IPv6 or even higher. A switch looks at the packet headers, uses MAC source and destination and doesn't care for the rest - extra packet info and payload.
A smart switch can blur this concept a bit, but in general : VLAN's are packets with a vlan tag ID. These can get grouped or separated out. VLAN exists because some one (the admin of course) was to lazy to pull more wires ( : or, to handle situations where more wires would introduce more weight : example : plains, etc )
: or, to handle situations where more wires would introduce more weight : example : plains, etc ) -
@Gertjan said in Very Basic IPv6 security question.:
@guardian said in Very Basic IPv6 security question.:
Are you telling me that I need to add firewall rules to the WAN?
The pfSense WAN firewall rule list is perfect as it was the day you installed pfSense.
And not only pfSense. Every router / firewall on planet earth, and probably in this solar system.
It's empty.
So : nothing gets in.@guardian said in Very Basic IPv6 security question.:
Can you please explain how ICMPv6 should be enabled?
Euh ... same way as ICMPv4 is 'enabled'.
Normally, the default LAN firewall rules (Netgate put them there - you saw them when you installed pfSense) will take care of things.
The role of ICMPv6 is more important as what ICMPv4 does.It has been so long since I set pfSense up, but I don't remember any ICMP rules. I don't think it adds any new rules because I enabled IPv6. Can someone tell me what rules I should have on the WAN for dual stack IPv4/6. Maybe that is why my pingers don't get set up correctly.
-
How can I control DNS leakage. I had a tightly controlled IPv4 network - no IPv6 on any interface, and all DNS traffic forced through unbound.
All I did was enable IPv6 on the WAN, and Diagnostics / Stages summary shows approximately 200 UDP states, which I have confirmed by PCAP are DNS calls. How can I lock this down?
-
@guardian Any particular port, say 5353 for example?
-
@guardian said in Very Basic IPv6 security question.:
Can someone ...
Default WAN firewall list : No RULES at all.
This stands as long as you do not have devices that you want to reach 'from the Internet'.
Example : If you have an internal web server, or mail server on your LAN, you need to add firewall rules to permit incoming traffic on the WAN interface (IPv4 : a NAT rule - IPv6 : just a firewall rule).
Another example : If you have a Openserver running on your pfSense, so you can admin it while on holiday, you need a firewall rule to permit incoming traffic to the OpenVPN server.
Another example : If you have a NAS that you want to make viosible on the Internet so you can share all your movies with your friends, you need a firewall rule (IPv4 : again a NAT rule).These are my WAN rules ;
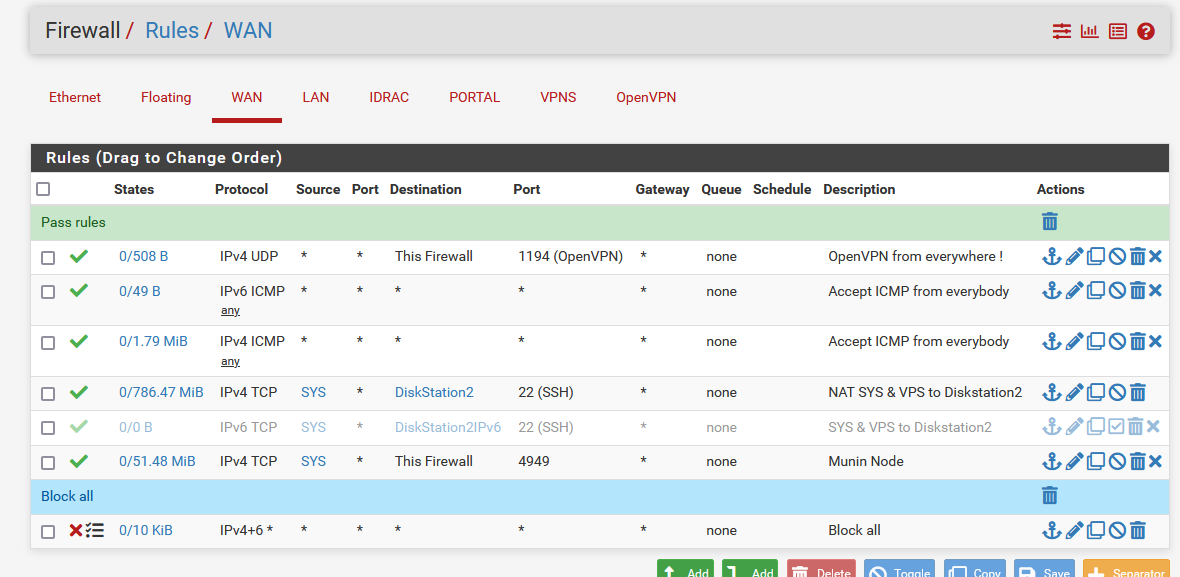
First rule : I like to admin pfSense 24h/24 (don't ask why).
Rule 2 : I accepts all incoming ICMPv6 traffic (don't ask why - this is probably for testing purposes).
Rule 3 : Same thing for ICMPv4.
Rule 4 : I have a group of dedicated bare bone servers somewhere in a data centre in paris. They are grouped up in an alias, and these have access to my Syno NAS for backup purposes.
Rule 5 : de activated. My ISP stills sucks when it comes to Ipv6 : my upstream router doesn't allow me allow incoming IPv6 traffic on it's prefixes, used by pfSense.
Rule 6 : Incoming Munin traffic as I have a Munin** node running on pfSense - which allows me to create this, because I do like reading log lines, but I've nothing against images.
Rule 7 and explicit "Block all" rule.Note : there is a last hidden Rule : implicit : Block all. This means that if you have no rules on an interface, all incoming traffic will be blocked. This is valid for every pfSense interface : WAN LAN whatever.
That's why the default LAN firewall rule list has one pass rule on it for all traffic.@guardian said in Very Basic IPv6 security question.:
Maybe that is why my pingers don't get set up correctly.
pingers == the pfSense dpinger procces ?
dpinger runs 'in' process so it can use any interface to send traffic OUT of any interface.
"OUT" is out of the box, going to any device elsewhere, outside of pfSense.
The pfSense firewall rules are operational on INCOMING == going into the box.There is this concept : use firewall rules here :
My advise : don't do that !!
If you have to, first : read the complete Netgate pfSense user manual.
Then : watch some video where they show examples.
Sign the dis-charger.
Go to a mirror and say out loud : "they told me not to do so - but I'm going to so any way".
Now you're ready to use floating rules. It was nice talking to you. -
@guardian said in Very Basic IPv6 security question.:
but why when I only enabled IPv6 on the WAN, and have it disabled on all other interfaces am I getting so much IPv6 DNS traffic?
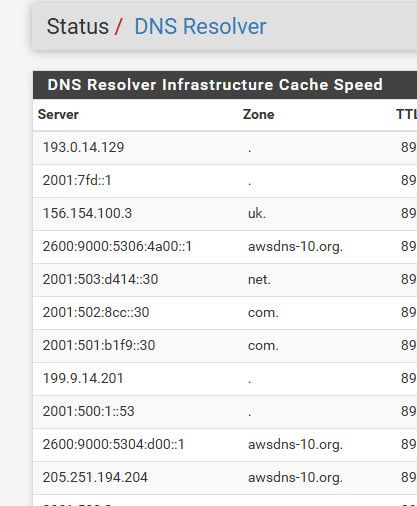
because unbound is using IPv6 to query the roots. and authoritative dns..
;1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.8.2.4.0.3.5.0.0.0.9.0.0.6.2.ip6.arpa. IN PTR ;; ANSWER SECTION: 1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.8.2.4.0.3.5.0.0.0.9.0.0.6.2.ip6.arpa. 86400 IN PTR ns-1064.awsdns-05.org.;; QUESTION SECTION: ;1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.8.7.5.0.3.5.0.0.0.9.0.0.6.2.ip6.arpa. IN PTR ;; ANSWER SECTION: 1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.8.7.5.0.3.5.0.0.0.9.0.0.6.2.ip6.arpa. 86400 IN PTR ns-1400.awsdns-47.org.this is gtld server
;; QUESTION SECTION: ;0.3.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.1.a.c.1.2.0.5.0.1.0.0.2.ip6.arpa. IN PTR ;; ANSWER SECTION: 0.3.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.1.a.c.1.2.0.5.0.1.0.0.2.ip6.arpa. 86400 IN PTR e.gtld-servers.net.The other 2 were dns on aws.. etc..
See the e.gtld - that is a NS for the .com tld
;; QUESTION SECTION: ;com. IN NS ;; ANSWER SECTION: com. 86400 IN NS h.gtld-servers.net. com. 86400 IN NS j.gtld-servers.net. com. 86400 IN NS e.gtld-servers.net. com. 86400 IN NS g.gtld-servers.net. com. 86400 IN NS k.gtld-servers.net. com. 86400 IN NS i.gtld-servers.net. com. 86400 IN NS c.gtld-servers.net. com. 86400 IN NS b.gtld-servers.net. com. 86400 IN NS m.gtld-servers.net. com. 86400 IN NS d.gtld-servers.net. com. 86400 IN NS l.gtld-servers.net. com. 86400 IN NS f.gtld-servers.net. com. 86400 IN NS a.gtld-servers.net.;; QUESTION SECTION: ;e.gtld-servers.net. IN AAAA ;; ANSWER SECTION: e.gtld-servers.net. 86400 IN AAAA 2001:502:1ca1::30You could check them all.. to see what they are..
Look in your dns resolver status
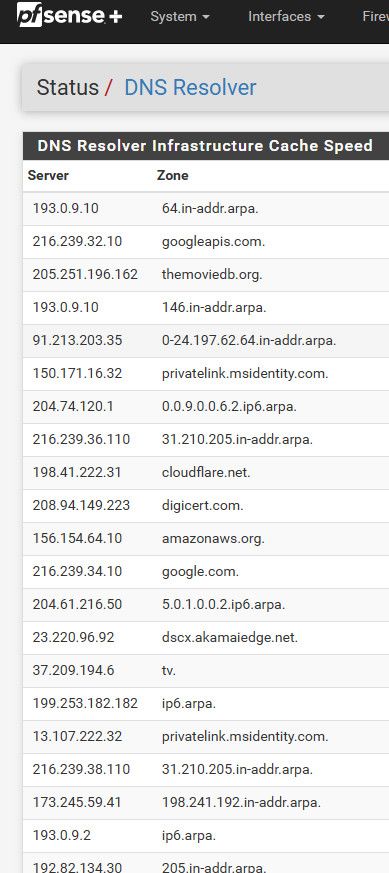
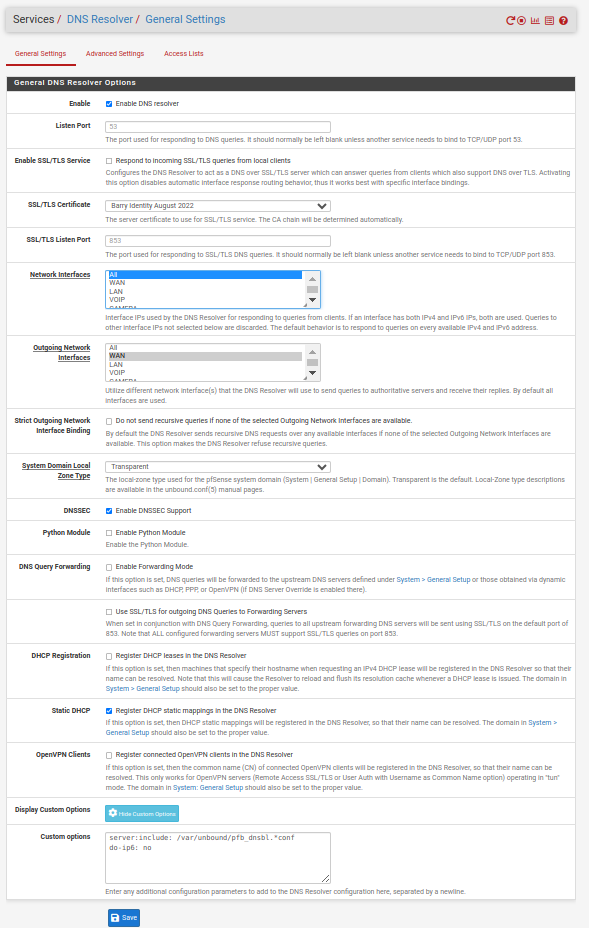
Notice mine only has IPv4 - because I told unbound not to use IPv6. I have IPv6 setup and working, but I don't see any point in having unbound use IPv6 through my HE tunnel. So I tell it not to use the IPv6 for dns.
do-ip6: <yes or no> Enable or disable whether ip6 queries are answered or issued. Default is yes. If disabled, queries are not answered on IPv6, and queries are not sent on IPv6 to the internet nameservers. With this option you can disable the IPv6 transport for sending DNS traffic, it does not impact the contents of the DNS traffic, which may have ip4 and ip6 addresses in it.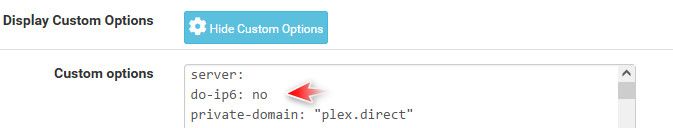
If I turn that off - look at that making queries to IPv6.
-
@guardian said in Very Basic IPv6 security question.:
If the firewall block all uninitiated incoming by default, that solves some of the problem, but with interfaces being able to create their own random accresses with SLAAC, it makes controlling outbound traffic much more difficult.
How often do you worry about outgoing traffic?
@guardian said in Very Basic IPv6 security question.:
I still need to figure out how to create the necessary IPv6 paths in my managed switch to get the IPv6 into the trunck, and then get it out agian in my new Tomato router.
http://groklawstatic.ibiblio.org/staticpages/index.php%3fpage=2005010107100653
Switches have nothing to do with IPv4 vs IPv6. They're for Ethernet frames. If you have a path for IPv4, you'll have one for IPv6 too.
-
@Gertjan said in Very Basic IPv6 security question.:
VLAN exists because some one (the admin of course) was to lazy to pull more wires ( : or, to handle situations where more wires would introduce more weight : example : plains, etc )
Or for things like VoIP phones, where the phone and a computer share a switch port. Same with access points with more than one SSID.
-
@JKnott said in Very Basic IPv6 security question.:
@guardian said in Very Basic IPv6 security question.:
If the firewall block all uninitiated incoming by default, that solves some of the problem, but with interfaces being able to create their own random accresses with SLAAC, it makes controlling outbound traffic much more difficult.
How often do you worry about outgoing traffic?
All the time.... I choke off IoT, most Microsoft traffic including updates (I open updates when I want to update, not when M$ wants to jam them down my throat), as well as ad blocking and known C&C/Malware networks. Once I go into IPv6 I end up with a lot of extra complexity and overhead.
@guardian said in Very Basic IPv6 security question.:
I still need to figure out how to create the necessary IPv6 paths in my managed switch to get the IPv6 into the trunck, and then get it out agian in my new Tomato router.
http://groklawstatic.ibiblio.org/staticpages/index.php%3fpage=2005010107100653
Switches have nothing to do with IPv4 vs IPv6. They're for Ethernet frames. If you have a path for IPv4, you'll have one for IPv6 too.
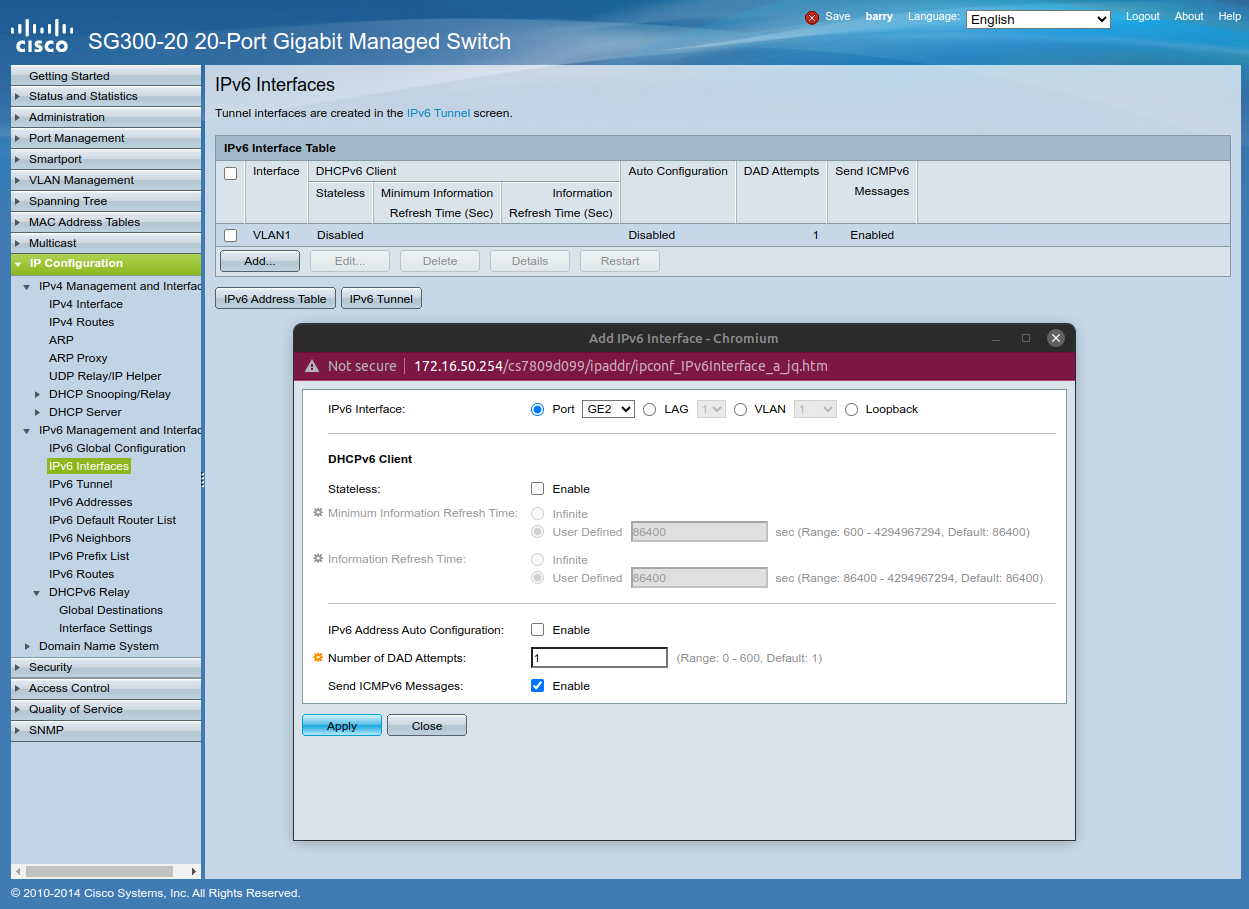
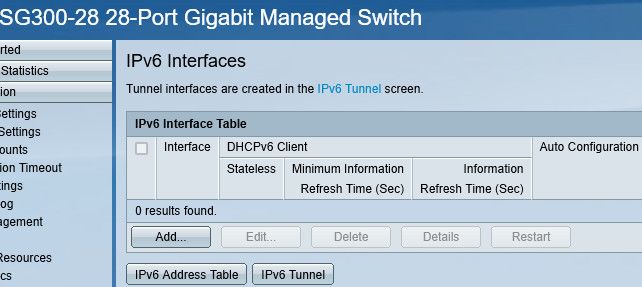
OK, maybe I don't understand, but it looks like on this L3 managed switch (SG300), IPv6 must be enabled or set up in some way.
It has been so long and infrequently that I have had to interact with the switch once I set it up (beyond using the monitor tap function)
-
@guardian said in Very Basic IPv6 security question.:
How often do you worry about outgoing traffic?
All the time.... I choke off IoT, most Microsoft traffic including updates (I open updates when I want to update, not when M$ wants to jam them down my throat), as well as ad blocking and known C&C/Malware networks. Once I go into IPv6 I end up with a lot of extra complexity and overhead.
Generally, you'd have IoT on it's own network. You can set up a network with only Unique Local Addresses for them.
OK, maybe I don't understand, but it looks like on this L3 managed switch (SG300), IPv6 must be enabled or set up in some way.
You didn't mention L3 switch before. You deal with them the same way as a router. However, is that actually a L3 switch? The Cisco spec doesn't seem to mention that.
BTW, I have a Cisco SG200 switch and while it has some IPv6 settings, it's not a L3 switch.
-
@JKnott said in Very Basic IPv6 security question.:
@guardian said in Very Basic IPv6 security question.:
How often do you worry about outgoing traffic?
All the time.... I choke off IoT, most Microsoft traffic including updates (I open updates when I want to update, not when M$ wants to jam them down my throat), as well as ad blocking and known C&C/Malware networks. Once I go into IPv6 I end up with a lot of extra complexity and overhead.
Generally, you'd have IoT on it's own network. You can set up a network with only Unique Local Addresses for them.
At the moment I only have cameras (which are only allowed to contact a server that I control for remote storage of motion capture), and an ATA which I restrict to only contacting the provider's servers. Both are old and don't support IPv6 AFAIK.
OK, maybe I don't understand, but it looks like on this L3 managed switch (SG300), IPv6 must be enabled or set up in some way.
You didn't mention L3 switch before. You deal with them the same way as a router. However, is that actually a L3 switch? The Cisco spec doesn't seem to mention that.
BTW, I have a Cisco SG200 switch and while it has some IPv6 settings, it's not a L3 switch.
I don't beleve I was explicit, I just said pfSense -> Managed Switch -> Ethernet of Powerline -> Fresh Tomato Router as Switch and Access Points.
I believe that the 2 in SG200 means Layer 2, and SG300 is Layer 3. Am I misinterpreting the info from the table below or is the SG300 a Layer 3 switch?
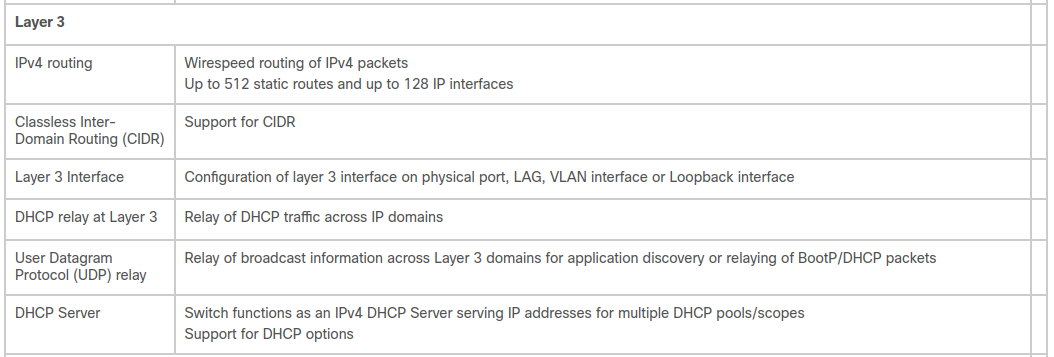
-
@guardian said in Very Basic IPv6 security question.:
is the SG300 a Layer 3 switch?
yes - if you put it layer 3 mode.. It can then be either just layer 2 or 3..
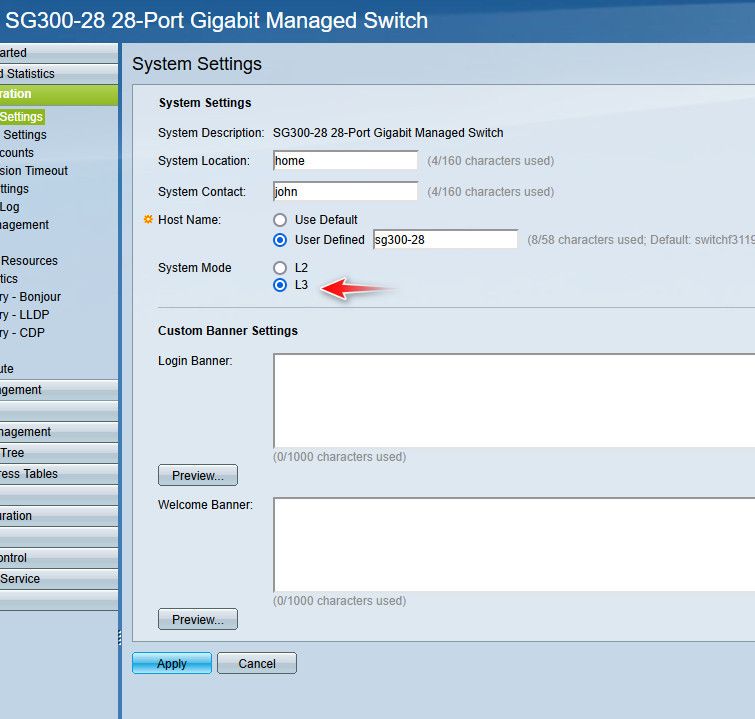
I have mine in 3 mode, but I am currently only doing layer 2 with it..
edit: and yes I gave it a very thoughtful and imaginative host name ;)
You do not need to setup any IPv6 on your switch if you don't want to - its pretty pointless unless you were going to actual route IPv6 with it, or if you wanted to access it for management over IPv6.
-
@johnpoz said in Very Basic IPv6 security question.:
@guardian said in Very Basic IPv6 security question.:
but why when I only enabled IPv6 on the WAN, and have it disabled on all other interfaces am I getting so much IPv6 DNS traffic?
because unbound is using IPv6 to query the roots. and authoritative dns..
[Snip]
@johnpoz thanks very much for taking so much time to put together such a detailed answer. As always you are right on!
Look in your dns resolver status. Notice mine only has IPv4 - because I told unbound not to use IPv6. I have IPv6 setup and working, but I don't see any point in having unbound use IPv6 through my HE tunnel. So I tell it not to use the IPv6 for dns.
do-ip6: <yes or no> Enable or disable whether ip6 queries are answered or issued. Default is yes. If disabled, queries are not answered on IPv6, and queries are not sent on IPv6 to the internet nameservers. With this option you can disable the IPv6 transport for sending DNS traffic, it does not impact the contents of the DNS traffic, which may have ip4 and ip6 addresses in it.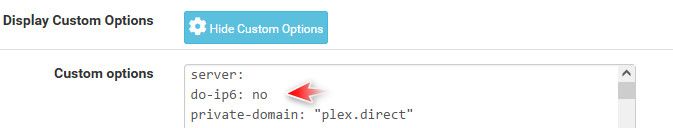
@johnpoz that's the magic spell - thanks so much.... Nasty IPv6 DNS Traffic all gone! :)
@johnpoz said in Very Basic IPv6 security question.:
@guardian said in Very Basic IPv6 security question.:
is the SG300 a Layer 3 switch?
yes - if you put it layer 3 mode.. It can then be either just layer 2 or 3..
[SNIP]
You do not need to setup any IPv6 on your switch if you don't want to - its pretty pointless unless you were going to actual route IPv6 with it, or if you wanted to access it for management over IPv6.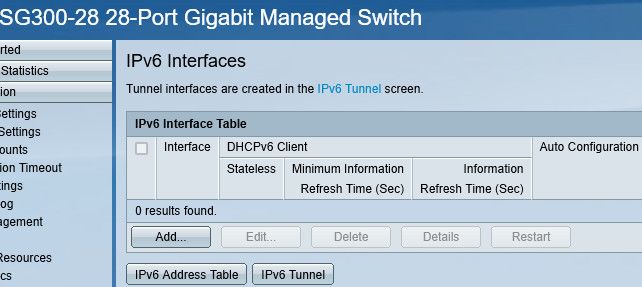
@johnpoz Thanks that helps!
-
Have I configured pfSense IPv6 Correctly? I am attempting to configure a VLAN6 which I am connecting over a trunk to an SG300 switch, and ultimately to an access port on GE2. The IPv4 is working fine, I get an IP assignment, and a DHCP server, but the IPv6 isn't working. I have a linux laptop connected to GE2 with DHCP configuration for both IPv4/v6. I have no IPv6 connectivity - a ping6 to 2607:f8b0:400b:804::2003 from the laptop results in Destination unreachable: Beyond scope of source address, but is successful if executed from the pfSense WebGUI.
The laptop has an fe80::/64, and the Default Route has an fe80:: address as well. There are no other entries, and if I attempt to run ping6 against the Defaut route, I get invalid argument. For some reason ping6 does not liek fe80 addresses--even when I fully expanded :: with the appropriate number of 0000 to make 8 complete hextets
I need to determine if the problem is with pfSense, the SG300, or the laptop, so any guidance would be much appreciated.
-
@guardian said in Very Basic IPv6 security question.:
The laptop has an fe80::/64, and the Default Route has an fe80:: address as well.
That is a link-local address, that is not gua.. So no you wouldn't be able to ping some gua address of 2607:f8b0:400b:804::2003
-
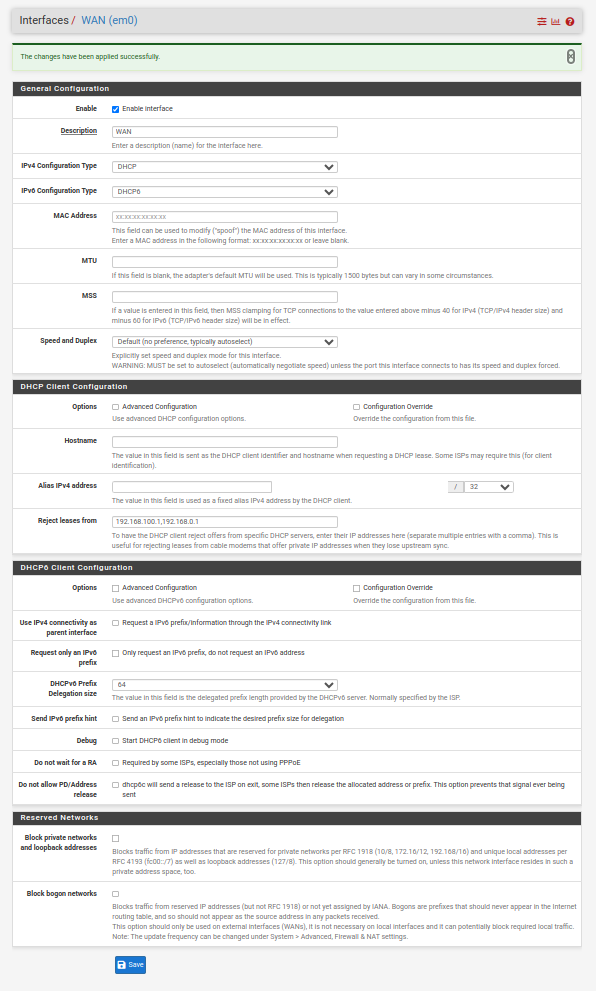
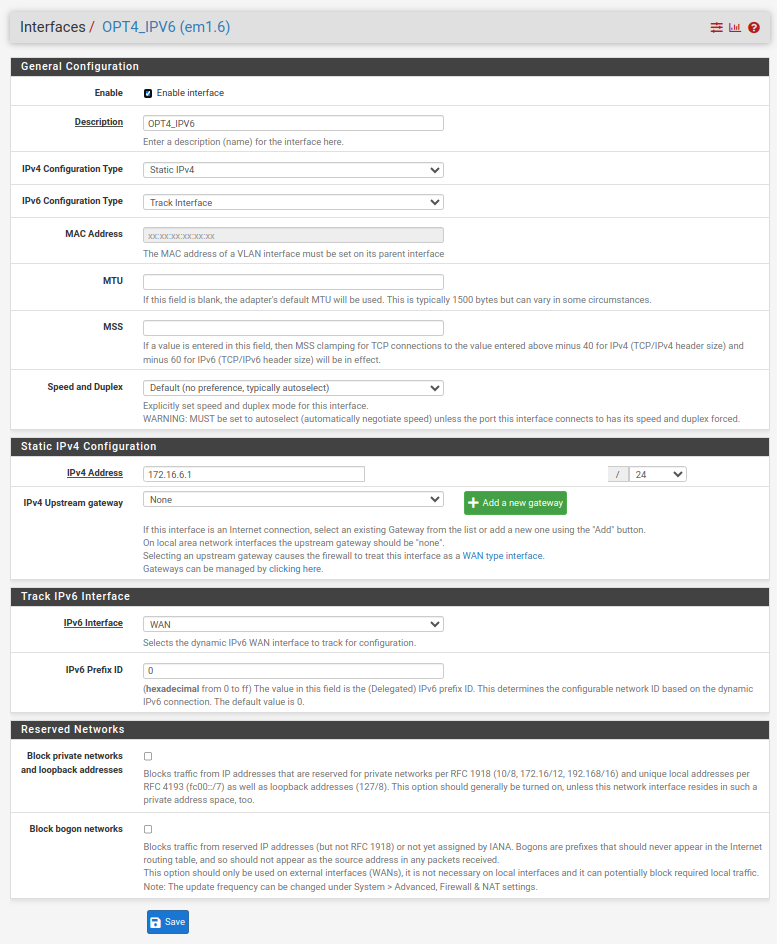
You are not configured for it to work just yet. For the Interfaces / WAN I would start by checking the boxes below and you will also have to determine what the prefix delegation size is from your ISP. A nice fat /48 is typical (as I have on the example below), with some ISPs trimming this down to a /56 (as it is still massive). Hopefully you don't just have a /64 but I understand that there are some ISPs that are that dumb/restrictive (particularly in the US it seems).
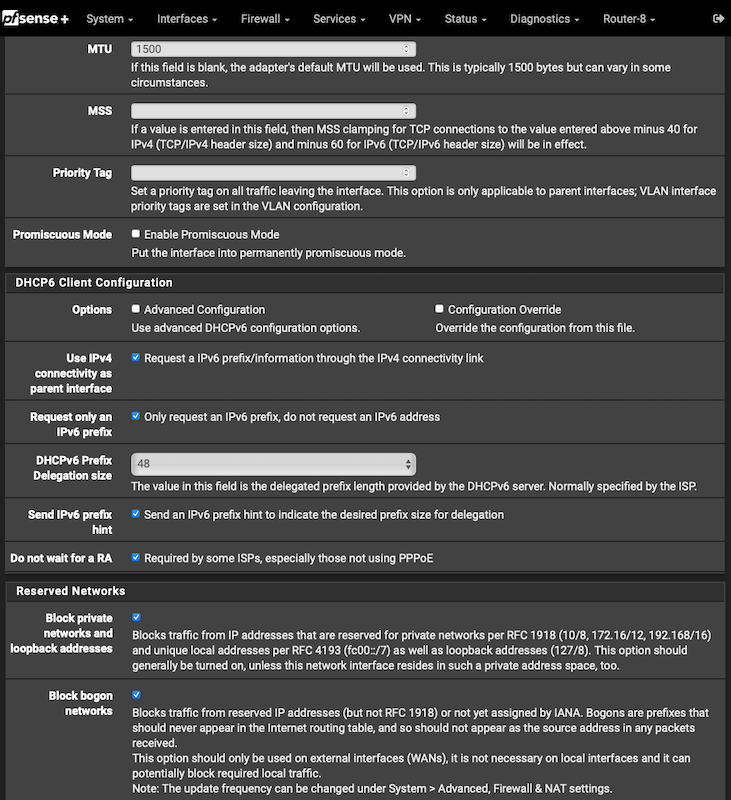
More to do after that on your LAN(s)/VLANs, DHCPv6 Server and Router Advertisements but the above is as good as any starting point. That and reading the section in the pfSense manual.
 ️
️ -
This page :
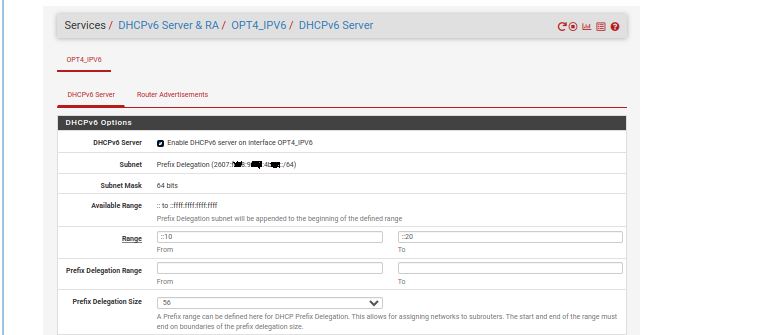
Normally, the /56 should be /64
Your OPT4_IPV6 is uses a prefix (carved out of the /56, so one of the 256 avaible upstream) /64
I advise you to look for more info.
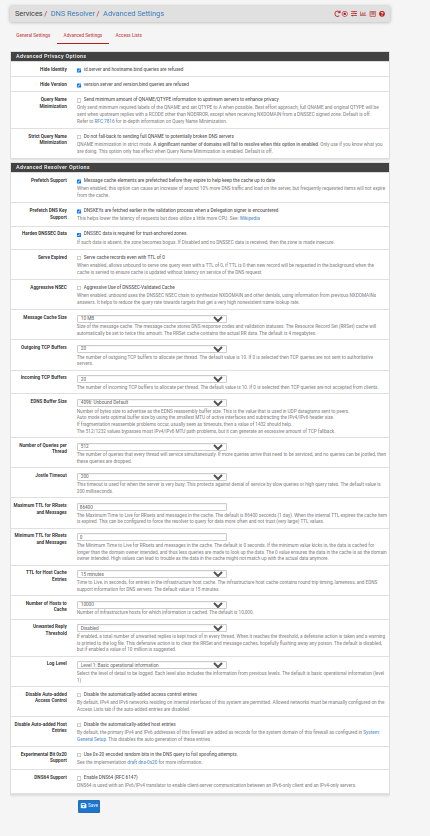
Here : System > Advanced > Networking and check "DHCP6 Debug". Save.
Disconnect the WAN, and reconnect;
Follow what happens here : Status > System Logs > DHCP. Important is, for now, what "dhcp6c" is telling you (the dhcp IPv6 CLIENT - the dhcp process on tha WAN side, doing IPv6 stuff).
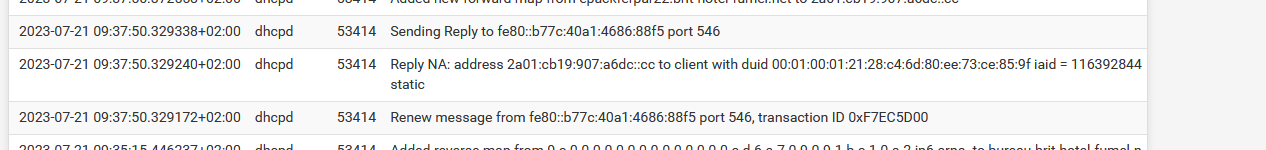
You want to see that it obtained a 'prefix' so it can be sued 'somewhere' :: your OPT4_IPV6 interface.You should see a line that says it received a IPv6 network (prefix) like this :

What you can do now, it hard code things. That's what I'm doing myself right now.
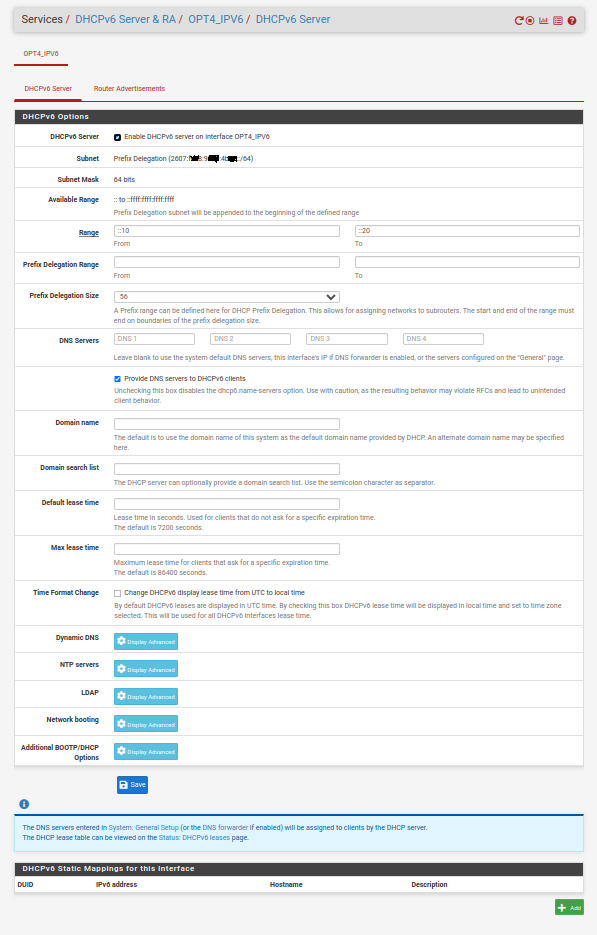
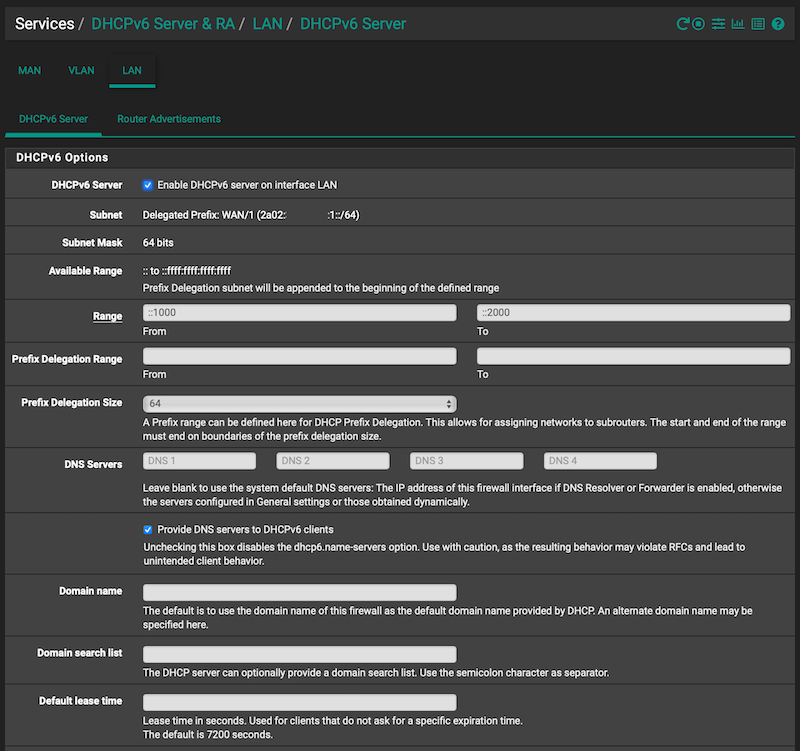
My LAN DHCPv6 server settings :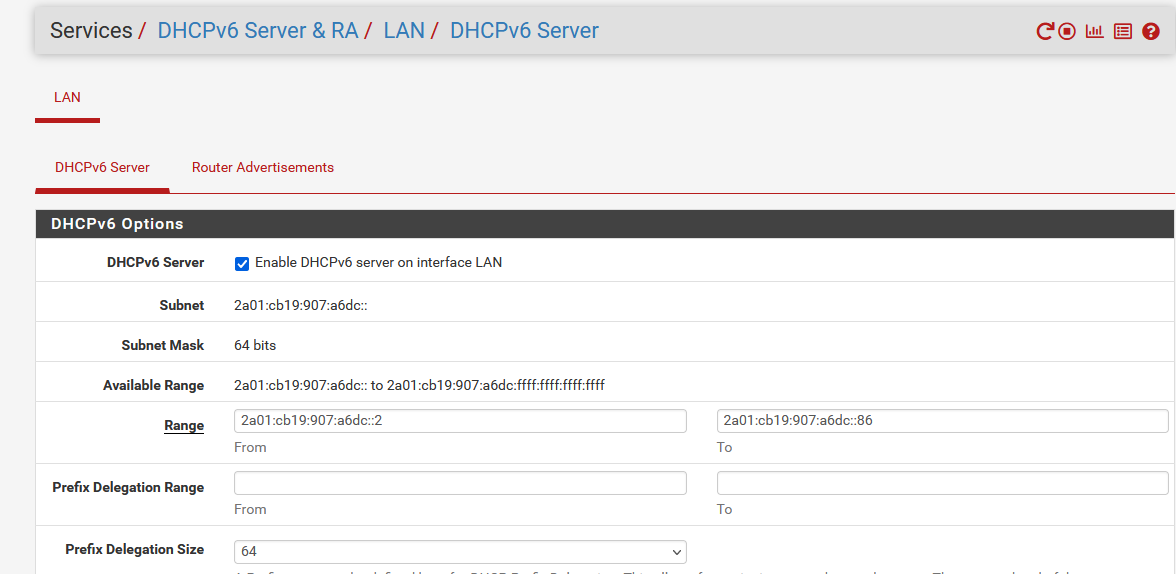
Because I know that I will receive "2a01:cb19:xO7:a6dc" as a prefix, I "hard coded" it.
When that part is done, back to the DHCP server - now set up :
Why : "because it works for me"


Or : This setting make DHCP IPV6 client behave how how IPv4 DHCP behave.Now you should see in the logs :
Btw : I also use DHCPv6 Static MAC .. sorry "DUID" mappings so my IPv6 devices always receive the same IPv6 under my control. Exactly like the v4 way.
I know, your - this setting :
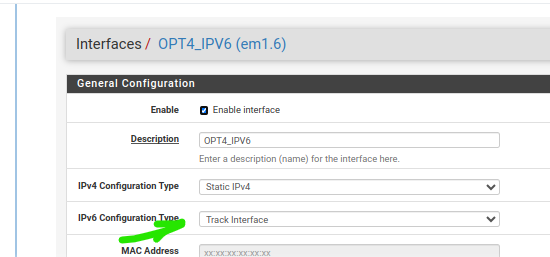
is better as you don't control what the prefix will me tomorrow : your upstream ISP router, or the ISP, can change that prefix. This is why is 'tracking' exists : When the prefix is known (obtained by the DHCPv6 client) it will be used by the DHCPv6 server.
And yes, there can be multiple LANs so multiple FHCPv6 servers, so multiple prefixes. In theory, pfSense could ask for 256 (/56) prefixes, as your ISP has them available for you. -
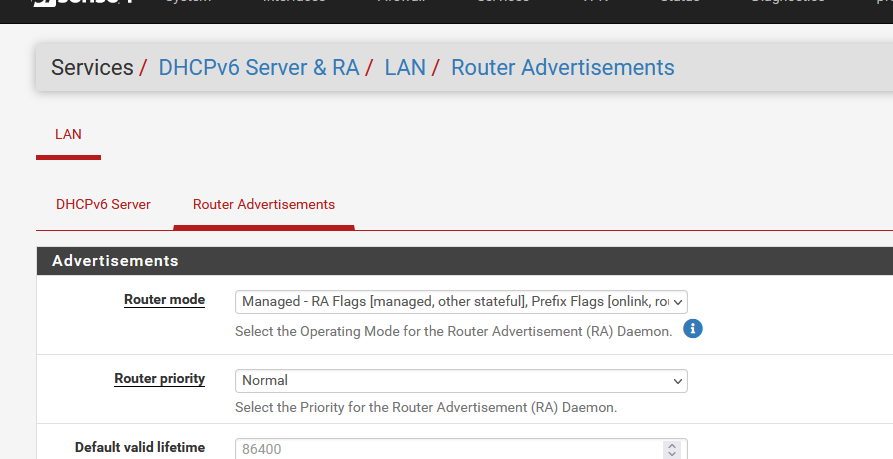
For simplicity I suggest the following, to keep your IPv6 prefix in line with what your ISP is offering you:
For the Router Advertisements / Router Mode I suggest either Assisted or Stateless (aka SLAAC). I use Assisted as it works better for my clients (especially for some Apple devices) but SLAAC is common too. I would not use the others listed unless you know what you are doing and why:
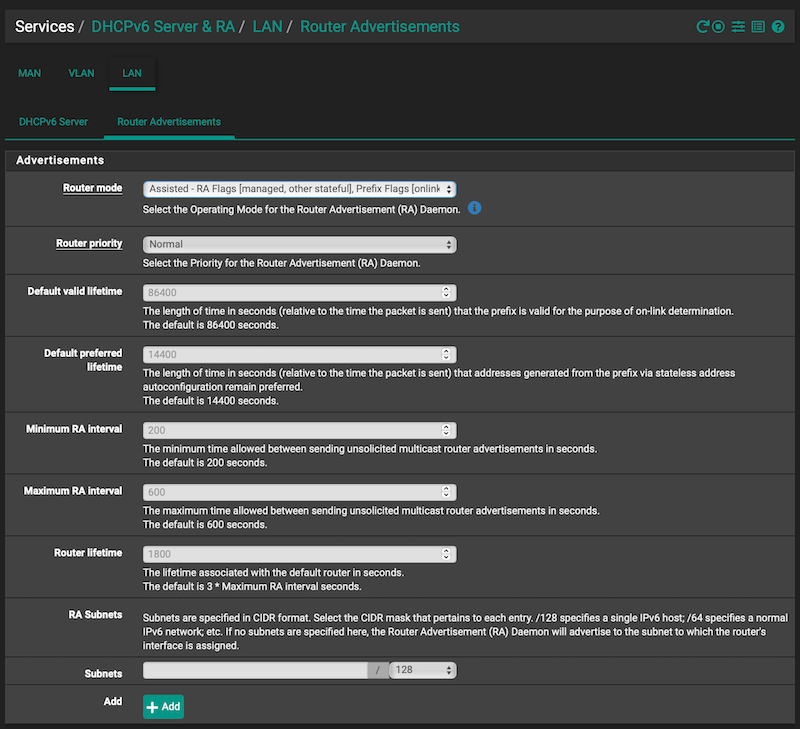
This is all in an effort to keep things simple and clear.
 ️
️ -
@RobbieTT said in Very Basic IPv6 security question.:
... keep things simple and clear.
Yes ... but .... This :
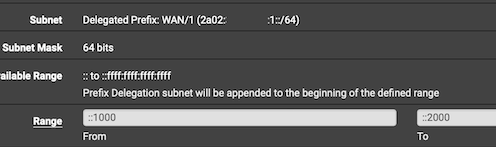
will assign IPv6 GUA's to clients like
2a0
 bsde:cdab:1234:5678:9abcd:[1000->2000]
bsde:cdab:1234:5678:9abcd:[1000->2000]I prefer the 2a0
 bsde:cdab::[1000->2000] ==> simple and clear
bsde:cdab::[1000->2000] ==> simple and clear
Again : I know, treating the prefix as a static value is plain wrong / can bite you back in the future (== break your IPv6 networking).
-
@Gertjan said in Very Basic IPv6 security question.:
will assign IPv6 GUA's to clients like
2a0
 bsde:cdab:1234:5678:9abcd:[1000->2000]
bsde:cdab:1234:5678:9abcd:[1000->2000]No, you are mistaken. When configured as stated the DHCPv6 leases look like:
2axx:xxx:xxxx:1::16be
With the ':1::' above being this particular LAN network prefix and the remaining 4 digits identifying the host.
You also get the full GUA, privacy addresses et al.
Example pfSense IPv6 leases, when configured as stated:
cat /var/dhcpd/var/db/dhcpd6.leases # The format of this file is documented in the dhcpd.leases(5) manual page. # This lease file was written by isc-dhcp-4.4.3-P1 # authoring-byte-order entry is generated, DO NOT DELETE authoring-byte-order little-endian; server-duid "\000\001\000\001+\240\234\326\220\redacted\251"; ia-na "\000\000\000\000\000\001\000\001*G\035m\redacted\303X" { cltt 5 2023/07/21 09:25:26; iaaddr 2a02:reda:cted:1::10d9 { binding state active; preferred-life 4500; max-life 7200; ends 5 2023/07/21 11:25:26; } } ia-na "f\263\3222\000\003\000\001\000\redacted\263f" { cltt 4 2023/07/20 03:01:42; } ia-na "\000\000\000\000\000\001\000\001)\232\244\230\330\276\redacted\254<" { cltt 5 2023/07/21 09:31:17; iaaddr 2a02:reda:cted:1::15de { binding state active; preferred-life 4500; max-life 7200; ends 5 2023/07/21 11:30:20; } } ia-na "\000\000\000\000\000\001\000\001)\232\242\017\304\221\014\redacted3\341" { cltt 5 2023/07/21 09:24:41; iaaddr 2a02:reda:cted:1::12b9 { binding state active; preferred-life 4500; max-life 7200; ends 5 2023/07/21 11:24:41; } } [snip…] ️
️