Wireguard IPv6 & CGNAT Setup - starting at the basics
-
Hello everyone - can someone please help me get started setting up Wireguard. I am going in circles as step one - how to find my pfSense server on the internet.
My ISP (Deutsche Glasfaser) uses CGNAT so the IPv4 address shown in pfSense dashboard is 100.86.68.123 which I understand cannot be used for external routing to the firewall. The IPv6 address shows on the dashboard as 2a00:6020:1000:33::1234.
Using internet sites like whatismyipaddress.com and ifconfig.co/ip I get another IP - 2a00:6020:4726:abde::1356.
Which IP should be used in the Peer endpoint setting? I have tried both using the format [2a00:6020:4726:abde::1356]:51820 and I see no packets being captured on WAN on port 51820. AFAIK if WAN sees no packets then all other configuration settings are moot. For sure these are also wrong, but let's start at the beginning.
The Peer is an Android phone on Deutsche Telekom, showing an IP address of 2a01:599:a34:712a:28b8:51bb:66a3:cdfb. I am quite confident the public keys are set up correctly, other settings are all default. As my LAN runs on 10.0.0.0/24 the subnet for the VPN is 10.1.0.0/24 and the Peer address is set to 10.1.0.2/32.
Can anyone help me find my WAN on the internet??
-
@charry2014 said in Wireguard IPv6 & CGNAT Setup - starting at the basics:
The IPv6 address shows on the dashboard as 2a00:6020:1000:33::1234.
Use this address to connect to your pfSense.
-
@Bob-Dig Thank you - ping6 to this address results in a response, success there!
But there is absolutely nothing on WAN in the packet capture from Wireguard on port 51820. Is it correct that all VPN packets arrive first on WAN and are then routed as the firewall rules allow?
What is odd is the Android OS is showing Wireguard there is using 0B data up and down so perhaps there is a fault on the source. If I use the same Android as a hotspot the iOS client also doesn't produce any traffic on WAN on 51820.
-
@charry2014 Use DDNS. Log the Firewall rule you created on WAN. It should show something, even if WireGuard isn't working.
-
@Bob-Dig There is nothing happening, Android is reporting 0B used. Could this be caused by the Android phone using an IPv6 only connection, the ISP using IPv6, the endpoint in Wireguard on Android being IPv6 yet the setup is for IPv4 only? I am feeling I answered my own question.
In the Android phone Peer settings in pfSense the Allowed IPs is set to 10.1.0.2/32 only. Perhaps there must be an IPv6 equivalent? If so what should that be?
The instructions I followed are for remote access VPN connections here -
https://docs.netgate.com/pfsense/en/latest/recipes/wireguard-ra.htmlThank you for your help.
-
So finally I got Wireguard working in pfSense with a macOS and Android peer. It took quite some help from ChatGPT which explained the IPv6 addresses for the VPN, and helped get the various subnets right. The pfSense setup is fairly vanilla domestic setup, no special settings applied.
Here's the key details that pulled it over the line. The LAN is on 10.0.0.0/24 and the VPN subnet is 10.1.0.0/24.
The pfSense interface for Wireguard is set to have both static IPv4 and IPv6 addresses which are set to 10.1.0.1/24 and fd00:1:1:1::1/64 respectively. The MTU is set to 1420. Otherwise the settings in the pfSense Tunnel are straightforward.
The settings for the macOS peer in pfSense are dynamic peer is set, and the allowed IPs in the Peer configuration are 10.1.0.4/32 and fd00:1:1:1::4/128. The settings for the Android peer are similar, just replacing the 4 above with a 2. Again, the MTU is set to 1420.
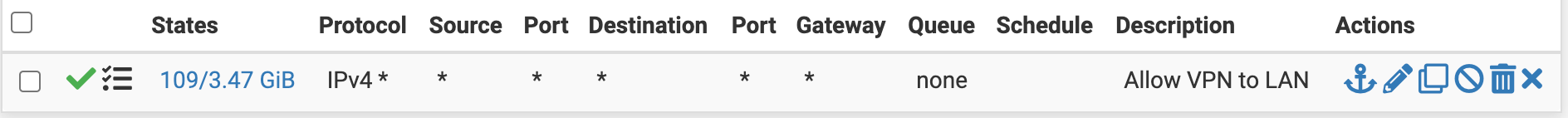
The only firewall rule that seems to pass any traffic is Firewall / Rules / WireGuard
There seems to be no need to put rules in the Wireguard interface firewall section. Similarly, there seems to be no need for any NAT settings, just leave on hybrid outbound NAT.Then to the peer settings on the devices that connect to the VPN. The key settings are adequately documented in many other places, no need to repeat that but the IPv6 addresses are harder to find.
Wireguard on the macOS peer has this configuration -
[Interface] PrivateKey = Ixxxyyyzzz2/GA3HDeE8GaoPZappqqqrrrEwrzLMHY= Address = 10.1.0.4/24, fd00:1:1:1::4/128 DNS = 8.8.8.8, 10.0.0.1 MTU = 1420 [Peer] PublicKey = vqverysecretkeylhiddenhereGQJHepd1zk= AllowedIPs = 0.0.0.0/0, ::/0 Endpoint = [2a00:6020:1000:33::1234]:51820The Android peer is similarly set up, notable are the DNS settings, Endpoint and Allowed IPs. Of course it is helpful to completely stop any other VPN you may have installed such as HMA, and in the VPN settings make sure that Always-on VPN is switched off, as this will block Wireguard.
Please let me know if any of this is incorrect, but otherwise This Works For Me (tm) and hope it helps someone.