@pet1975 said in suricata fail to launch after update:
i just pm you regarding and email :-)
Imported your configuration into my test virtual machine and then installed the Suricata package. It failed to complete installation with the current package version posted in the pfSense packages repository (Suricata v5.0.2_3). It failed the same as it has with you previously. Nothing shows under the SERVICES menu for Suricata after the package installation.
However, installing the latest Suricata package version that I am currently testing was successful. That package version is 5.0.3, and it will be available soon for the pfSense-2.5 DEVEL branch and then a bit later for the pfSense-2.4.5 RELEASE branch.
Even better news is I found what the root problem is, and it is what I had suspected. If you have the option on the GLOBAL SETTINGS tab checked to enable download of the GeoLite2 database, but your MaxMind database license key is invalid, that download will fail. The current PHP script, when detecting that failure performs an exit() call instead of a return() call. Calling exit() in PHP terminates the currently running script. That is in turn prematurely terminating the Suricata package installation PHP script so that the remainder of the installation (putting the entry under the SERVICES menu) fails to complete. Here is the error from the system log -- (I changed the order to show the recent event first, so read the entries from the bottom up for the chronological sequence)
Jul 11 11:37:55 php 92290 [Suricata] ERROR: GeoLite2-Country IP database update check failed. The GeoIP database was not updated!
Jul 11 11:37:55 php 92290 [Suricata] ALERT: The Account ID or License Key for MaxMind GeoLite2 is invalid.
Jul 11 11:37:54 php 92290 [Suricata] Checking for updated MaxMind GeoLite2 IP database file...
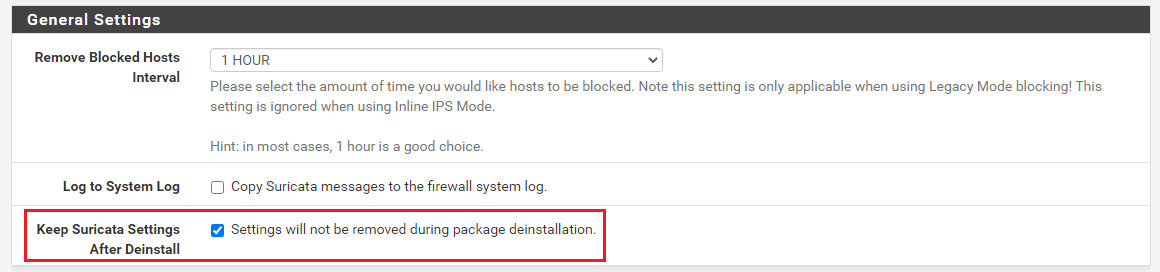
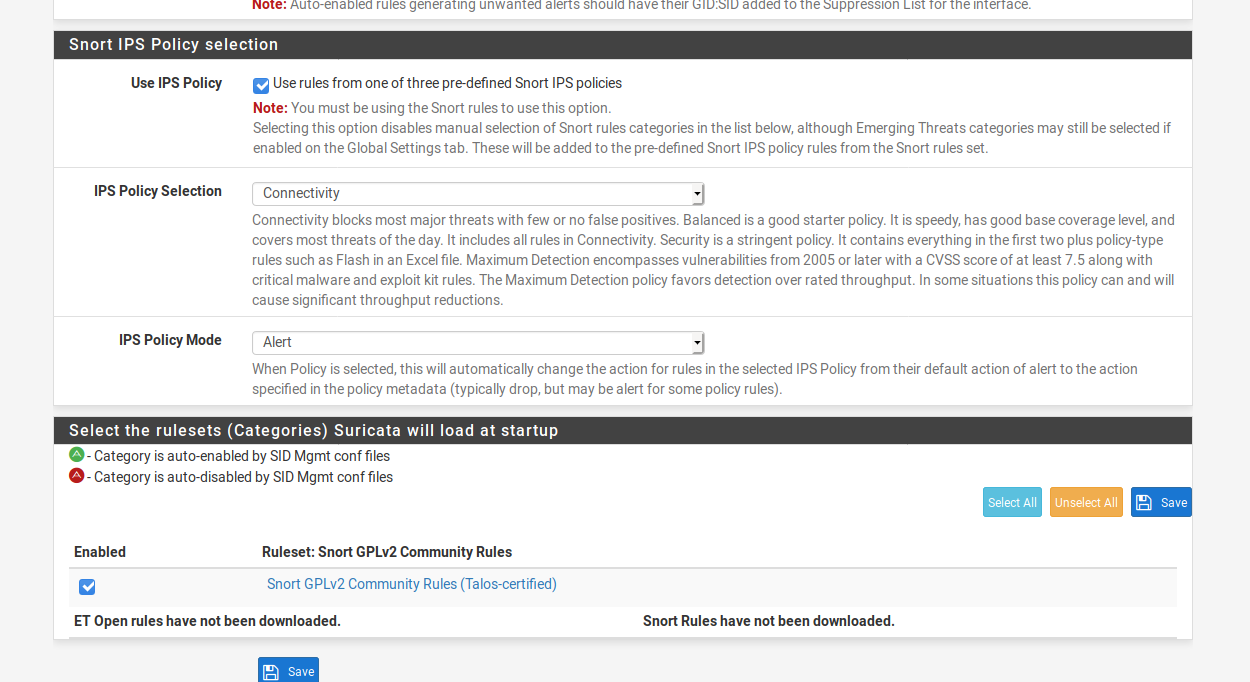
So the root cause of your issue is that your MaxMind GeoLite2 database download license key is invalid. If you fix this, then your Suricata installation will complete even with the current version. To fix this, go to this URL: https://myfirewall_ip/suricata/suricata_global.php. Replace "myfirewall_ip" with the correct value. Once on the tab, scroll down to this area --
[image: 1594482685703-suricata_geolite2_settings.png]
If you do not want to use GeoIP rules with Suricata, then uncheck the box for GeoLite2 DB Update. If you do want to use GeoIP rules, then you will need to enter a valid license key. The current key you will see listed is not valid. In the screenshot above, I deliberately obfuscated your key for privacy. Save the changes you make on this screen and then run the remove and reinstall Suricata sequence again. It should complete successfully and show up under the SERVICES menu.
In the upcoming 5.0.3 Suricata version I have changed the GeoLite2 database install code so that a failure to download the database does not terminate the rest of the installation script.