Using a GRE Tunnel to route VMs network and IP to external network.
-
Everything's done as you said. Now, to use the IPs on the Virtual Machines on Proxmox, I need to create a linux bridge that is associated to the local pfsense (a VLAN was created for that with the remote gateway)
and to get the VM to use the IP I need to put for instance: IP: 185.113.141.139 Netmask: 255.255.255.0 Gateway: 185.113.141.1 or I need to use my normal router gateway (192.168.1.254) and a local ip address like 192.168.1.139?Thanks in advance.
João Ferreira
-
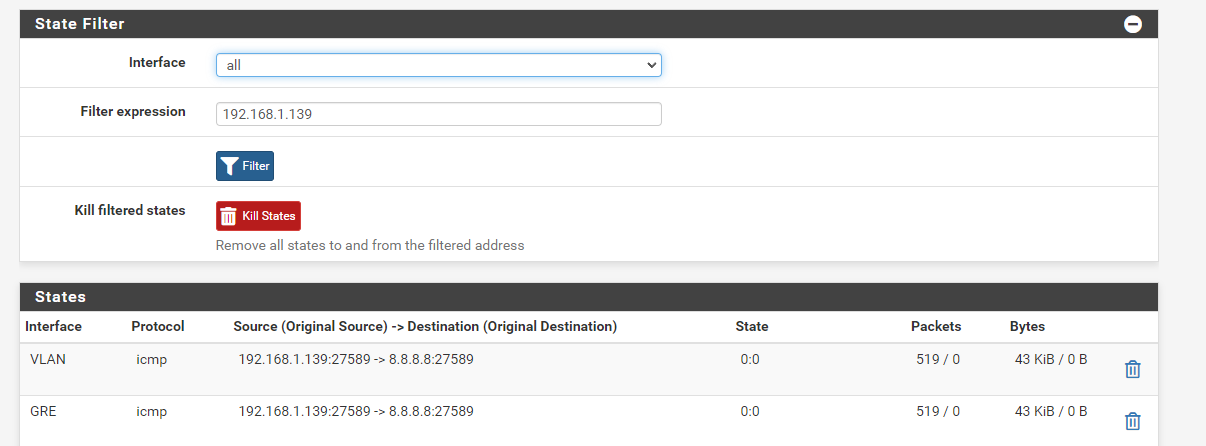
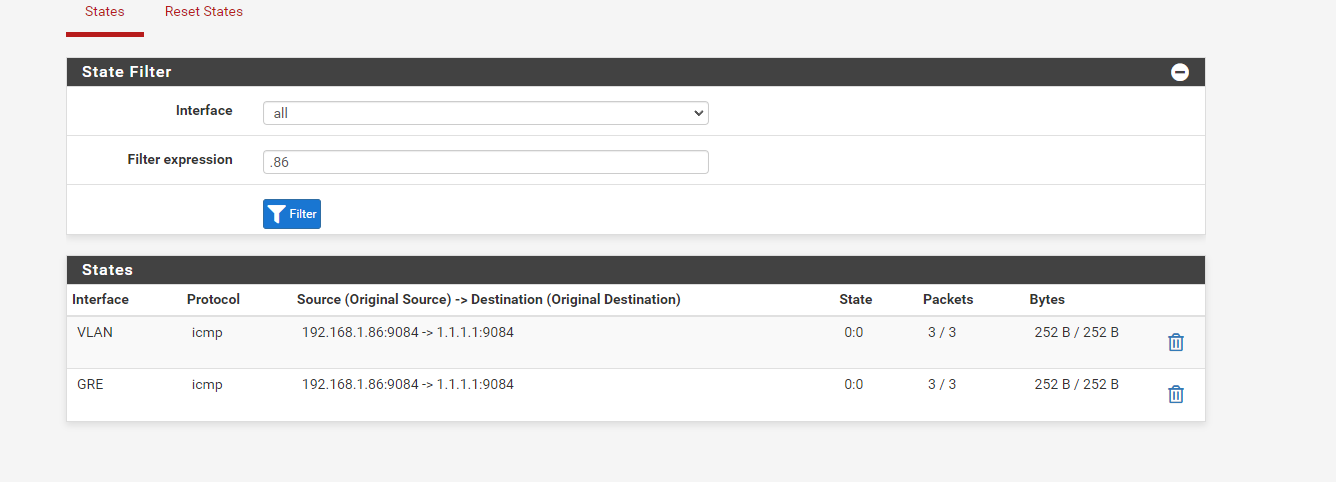
@xuap So, I used the gateway 185.113.141.1 on the VM and the IP 192.168.1.139, on the local pfsense I get this
and on the remote I get this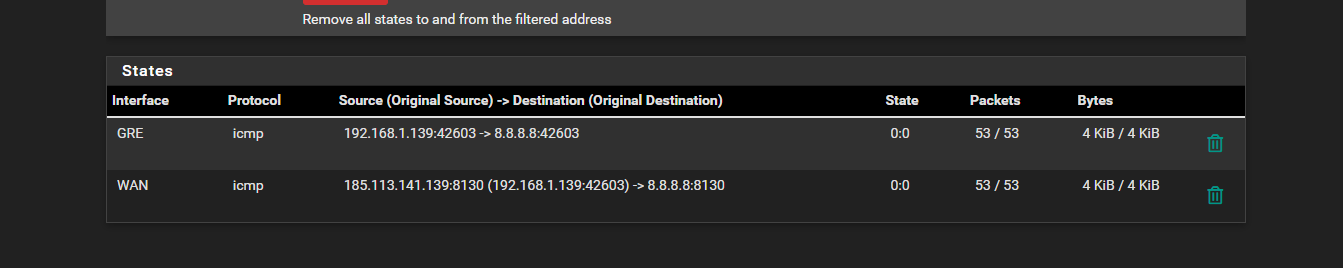
Also, I have this NAT rules

but I don't have internet access on the VM.
-
If you are 1:1 NATing, as you initially said, then you should not have any public IPs at the local site.
The only place the public IPs would be defined would be as VIPs at the remote site.
In the other thread they were given a routed subnet and so could use the public IPs directly on hosts at the local end. In that situation you don't need to NAT anything and instead can route the subnet across the tunnel at the remote site. Then use the subnet directly on an interface at the local end. The pfSense VLAN interface would still not be the .1 address though, that would imply they gave you the full /24 subnet which is very unlikely. It would be the first usable IP in the subnet they routed to you.
Steve
-
@stephenw10 Unfortunately, they didn't allow us to have a routed subnet, so I have to stick with the 1:1.
Virtual IPs on the remote site:

Virtual IPs on the local site:

I only have Virtual IPs on the remote which is one additional IP I got that the hosting provider gave me.
So, in my case do I need to change the gateway 185.113.141.1 to anything else or do I need to make some firewall rules to give the VM internet access or something? Because if I change to my router's gateway and the bridge to the main bridge of pfsense (WAN) the network starts working but I don't get any data on pfsense stats nor the public IP is correct..
-
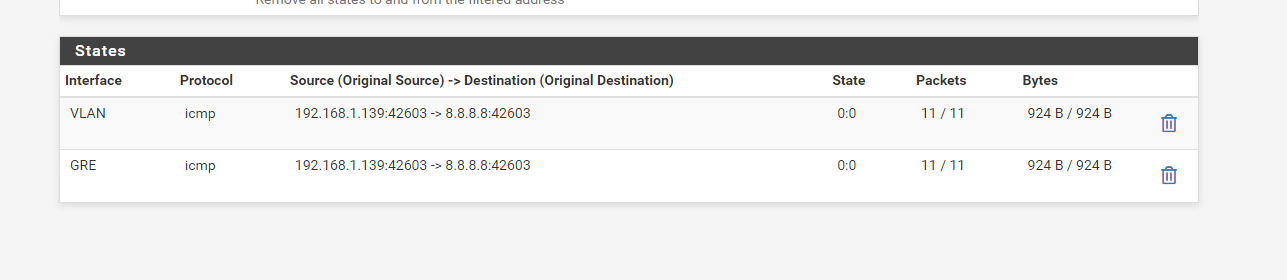
If I ping something like 1.1.1.1, on the console I get

without any output, but I do get the states on both ends
LOCAL:
REMOTE:
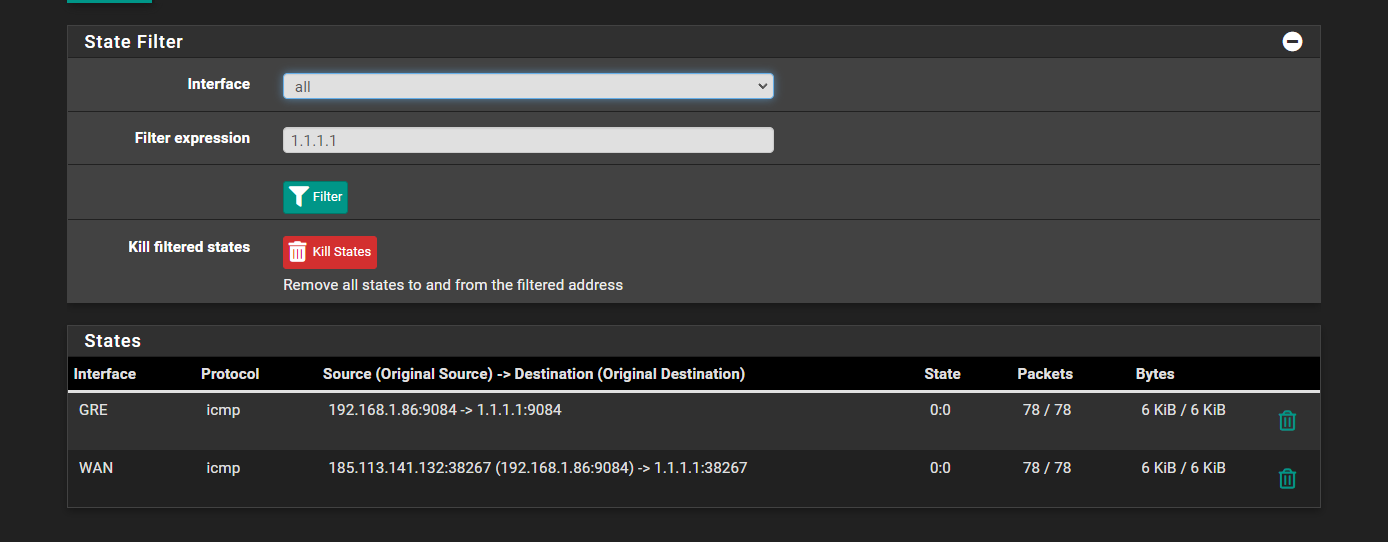
also referring that it's showing the ip 185.113.141.132 when the IP I want to use is the 185.113.141.139.
-
Ok, so what's the 1:1 NAT rule at the remote side? It looks like it's not catching the traffic there on the way out and it's using the auto outbound rule instead.
Also the 1:1 NAT rule would not change the source port (icmp ID here) like is shown there.However it does look to be working as expected apart from that. There is two way traffic shown on all 4 interfaces involved. But the ping fails?
Steve
-
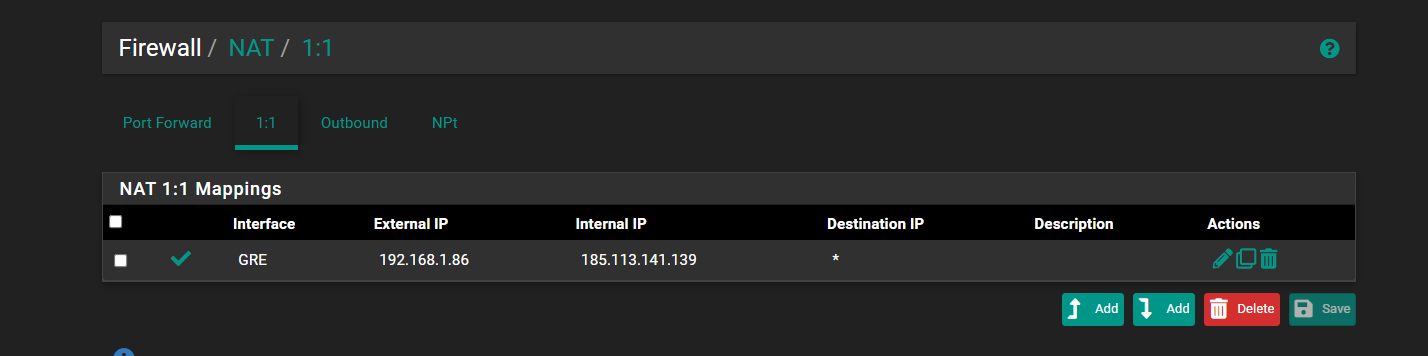
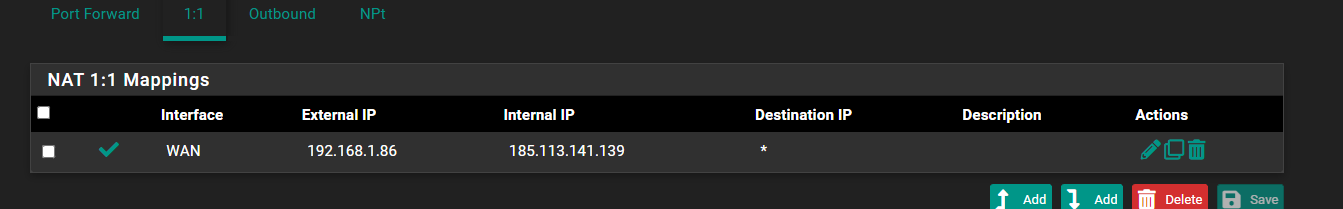
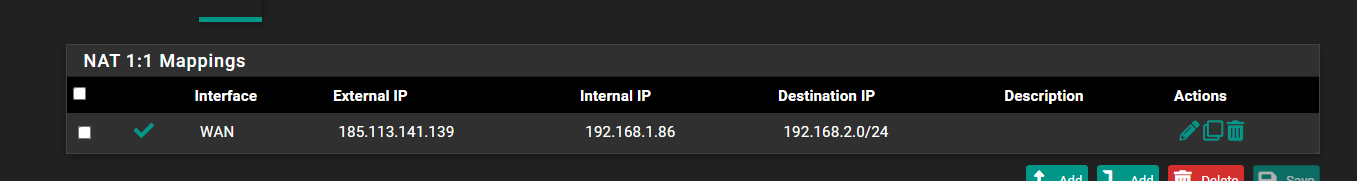
@stephenw10 The NAT rules on the remote site are like this:
1:1
Outbound

Yeah, basically it just doesn't have internet access, nor even access to the pfsense or tunnel ping.. I can't ping the tunnel through the VM even tho the ping arrives there.
-
Ok the 1:1 NAT rule should be on WAN with the external IP being the public IP VIP and the internal IP being the private IP of the server.
-
@stephenw10 So, like this?
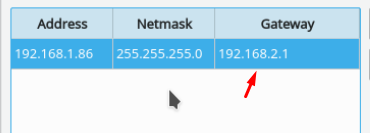
And on the VM, like this?

-
No the external IP should be the public IP. The internal IP should be the server IP in 192.168.1.0/24.
The VM gateway needs to be in the subnet so it should be the local pfSense VLAN interface IP. Probably 192.168.1.1
-
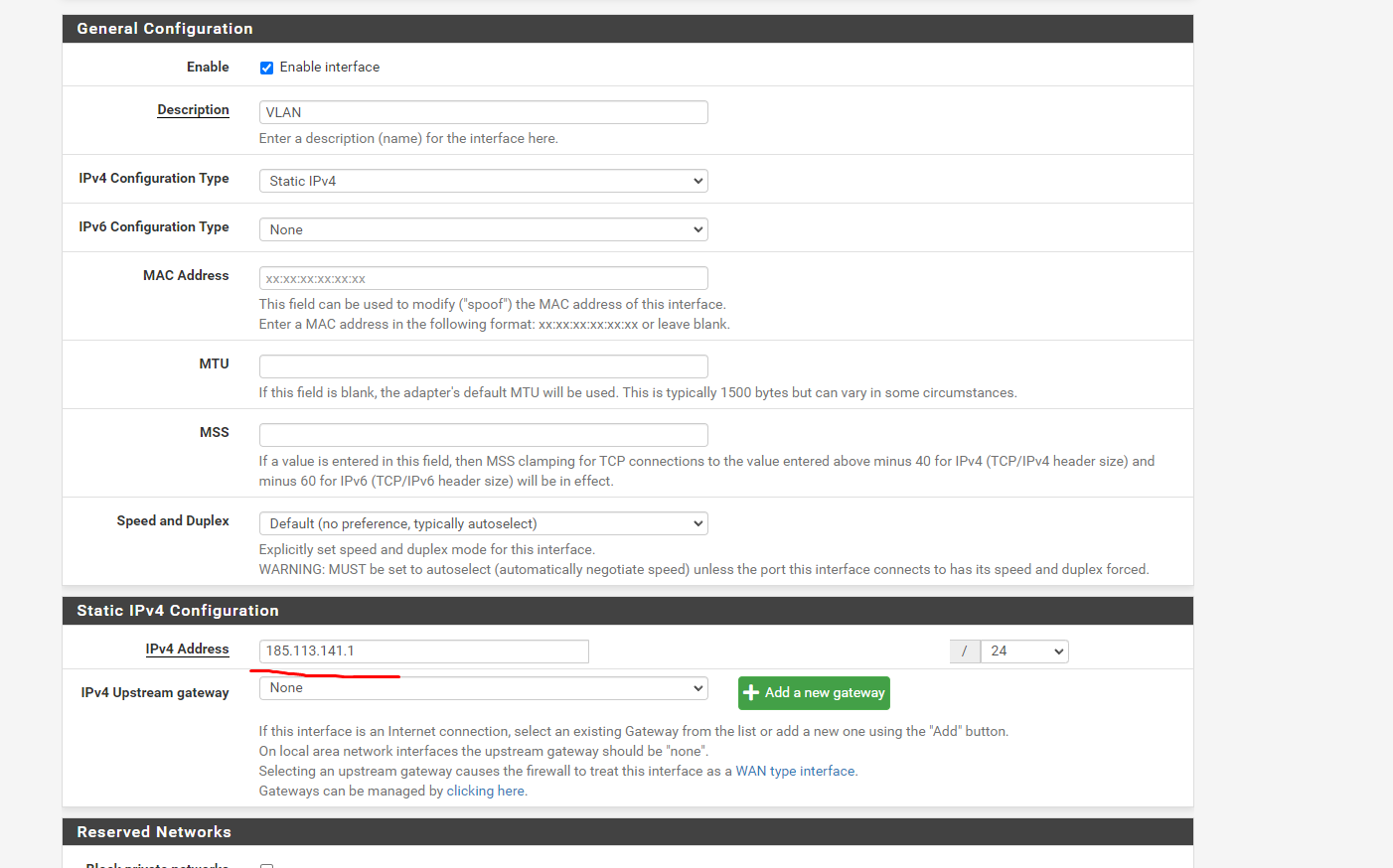
@stephenw10 So, my networks on local pfsense are like this:
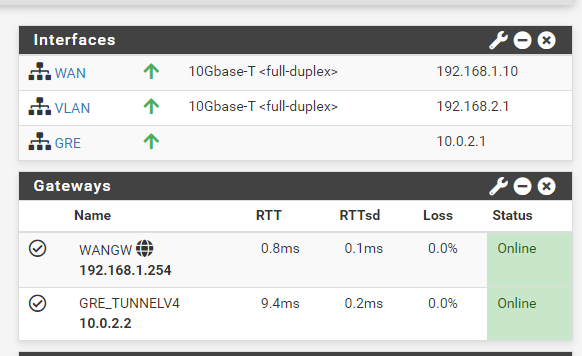
My WAN is the 192.168.1.10 which is on the main gateway of the router 192.168.1.254
I use the VLAN as a bridge for the VMs, but should I use something else both on pfsense or on the VMs?
-
Hmm, where is the VM at 192.168.1.86 then?
I expect all the VMs to be in the VLAN subnet and all the routing the NAT setup to be to and from the VLAN subnet.
Steve
-
I also did a pcap on both the GRE and VLAN of the local pfsense
GRE:

VLAN:

So, as I understood it is sending the ping to the 1.1.1.1 but it is not receiving any traffic..
-
Right, well it won't if traffic from 192.168.1.86 is coming in on the wrong interface!
If you run a pcap on WAN you will see all the replies going back that way because that's where the 192.168.1.0/24 subnet is.
How exactly is the VM connected?
-
@stephenw10 The VM is in the proxmox with the IP on 192.168.1.86 and gateway 192.168.2.1 like I showed above
The VM is with the bridge of the VLAN (192.168.2.1) which is the Linux Bridge 1 on proxmox (vmbr1) that will (supposedly) be attached to all VMs so it can tunnel the traffic to the remote pfsense
-
This is the only 1.1.1.1 ping I have on the WAN of the local pfsense
-
There is an ARP request for 192.168.1.86 though because it's trying to find it on the WAN. And failing.
The VMs should be in the VLAN subnet, 192.168.2.0/24.
The static route at the remote end should be for that subnet.
The 1:1 NAT rules at the remote side should also be for host in that subnet.
Steve
-
@stephenw10 So, like this?

-
Ok, so It looks like I was using a 192.168.1.86 on a .2 subnet, I changed it to 192.168.2.86 and it now pings 1.1.1.1 and 8.8.8.8 and the tunnel, but doesn't have internet access to like ifconfig.me or google.com. I'll do a bit more testing, but it's closer than never to work out.
-
Yeah you need to be using 192.168.2.X everywhere.
You are probably seeing pings work but no other traffic because there is some asymmetry somewhere. Once all the rules and routes are changed to the VLAN subnet it should work.