SG-1100 Running Real VLANs
-
Ok, I have been reading through many threads and watching all the videos on vlan setups. I have tried just about everything and spent hours trying to get my vlans set up on my sg-1100. I can never get DHCP working on my unifi AC, if I try and set it up on extra vlans. Are you saying you got yours to work? This is driving me crazy.
-
Yes, they work. post your interface and switch configuration and describe what you are trying to do.
-
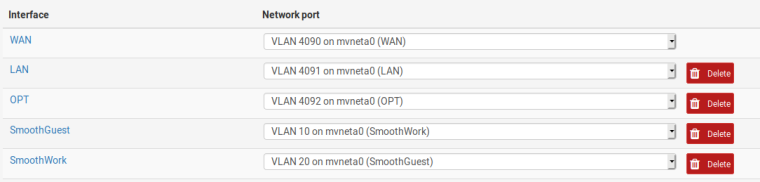
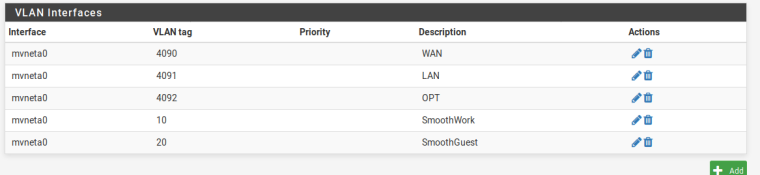
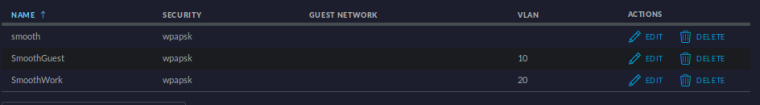
I also have the firewall rules for each vlan, as well as the DHCP set for each. However clients are never able to grab a DHCP address. I am hoping its just something simple I am missing.
-
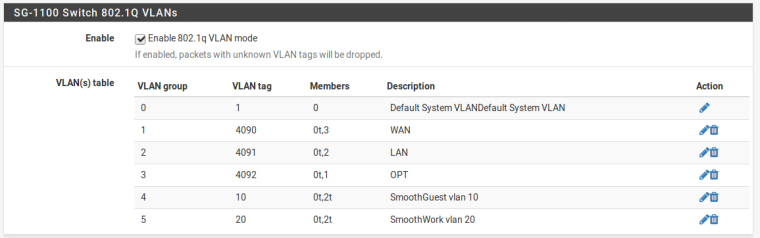
And the pfSense switch ports tab?
-
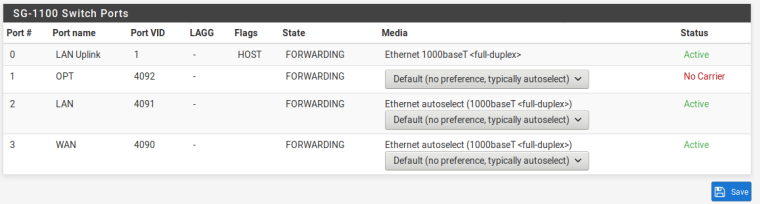
-
That all looks fine for managing that AP on a LAN address if it is connected to port 2.
Anything in the DHCP logs? DHCP has automatic rules for any interface with a DHCP server enabled.
Based on what you have posted I'd look at the DHCP logs and packet captures on UDP port 67.
Does the smooth network work?
-
Nothing showing up in the DHCP logs then I try to connect to the Work or Guest network. I can connect just fine to the regular Smooth network, clients connect and get a DHCP address. Port two is connected to a switch. I had a similar setup working with untangle, just want to make the jump to pfsense.
-
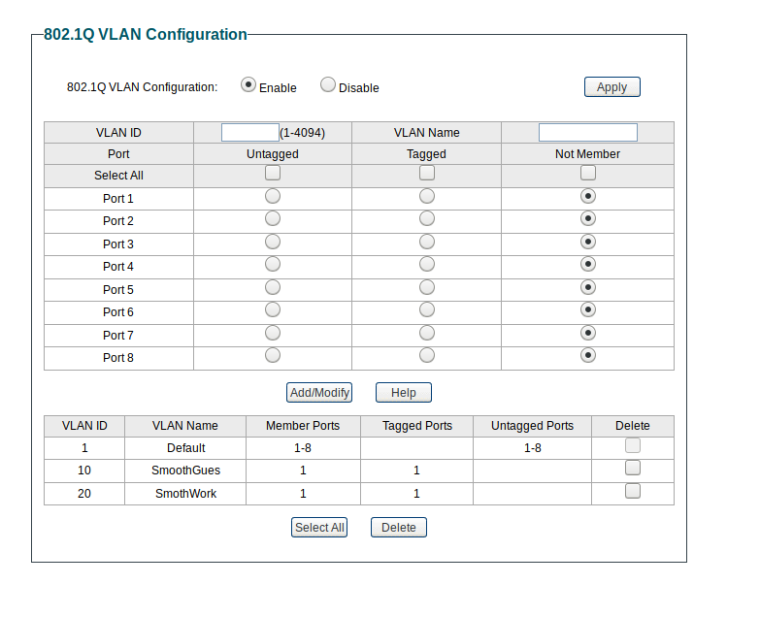
Well, you have to tag VLANs 10 and 20 through to the AP on the switch on the ports connected to pfSense and the AP.
-
If the L2 is setup correctly check the L3. How are the networks configured, a common beginner mistake is to use the default /32 CIDR for example.
-
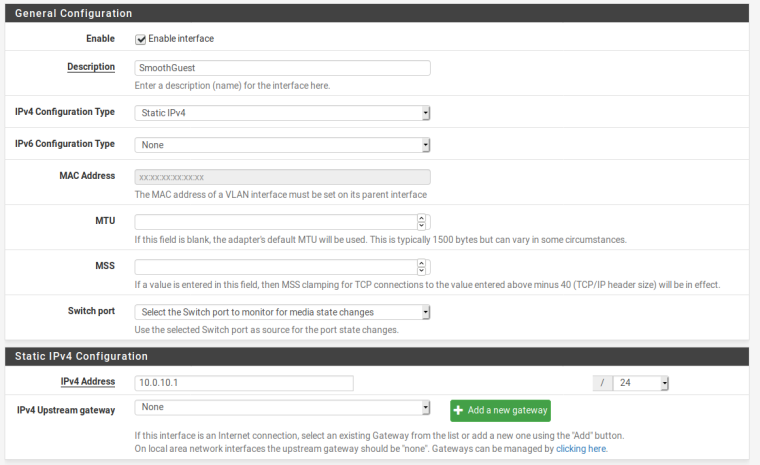 Yep, doublechecked /24
Yep, doublechecked /24and vlan set on the switch port
-
OK. On what switch port are 10 and 20 tagged to the AP?
-
All to port 1
-
OK, on what port are 10 and 20 tagged to pfSense port 2?
-
Not sure I follow, are you talking about the switch on the sg-1100?
-
No. What switch port on your switch is connected to pfSense port 2? That port needs 10 and 20 tagged as well.
-
Brilliant! Ok well that was easy. That worked. Thanks for all your help!
-
@pfsmooth Tag 10 and 20 on switch port 2 and I think you will be pleased with the results.
-
Well all was running smooth for a while, had it all set up and all of a sudden I get flooded with " Default deny rule IPv4 (1000000103) " and things like my plex server wont allow external connections. If I rebuild pfsense from scratch it is fine until i add the vlans. Then boom plex falls off. Any ideas?
-
From that description, no. Not enough information.
-
Not sure if I should start a new thread. But basically the port forwarding is not working directly to 32400. I have set the NAT rule and the FW rule with no luck. A search shows this pops up often but I haven't been able to pin down a solution.