HA XMLRPC error
-
Nothing magical about XMLRPC sync. It's just a TCP/HTTPS connection to the webgui port on the secondary.
I suppose on the sending node that could happen if something has killed the state.
Do you have state killing on gateway failure enabled in System > Advanced, Miscellaneous?
-
But how/why would it be an outbound block?
-
Sorry I updated ^
-
But I still don't get how it could be an outbound block - that is what the little black arrow thing means.. I have to think there is some setting that are done that are not default..
I don't run HA setup, nor do I have it that setting set.. But seems odd that there could be outbound blocking even on a state kill?
-
If the primary has an open https connection to the secondary and is trying to send the config changes and something kills the state out from under it, it will continue to try to send the data until it times out and quits.
It will be out-of-state like anything else in that case.
# default deny rules block in log inet all tracker 1000000103 label "Default deny rule IPv4" block out log inet all tracker 1000000104 label "Default deny rule IPv4"1000000104 is the outbound default deny so that would log like that.
-
Yeah I get that it is out of state, but it would be logged as an outbound block?? This is what is confusing me..
-
Sorry. updated again lol
-
Ah that is why its block as outbound.. Then..
block out log inet all tracker 1000000104 label "Default deny rule IPv4"
Normally never see outbound blocks.. But if its pfsense itself doing the talking, and the state goes away then that rule would block it since the state is missing. Until the process on pfsense creates a new state by sending syn.
-
Yeah. Everything that was initially set up by the TCP handshake starting with a SYN going out has been blown away so...
-
Ok that makes sense then - thanks. Even though there is a rule that allows pfsense to talk out, it still needs a valid state.
-
So if they are seeing this block - how do they restart the sync process so there is a new state created? I really need to play more with the HA stuff.. Time to fire up some vms and play with the HA setup ;) My understanding of the inner works of that is very lacking - I just have not had need to play with it.
-
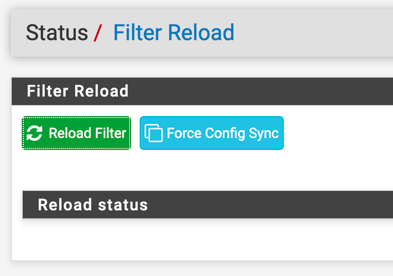
@johnpoz It will kick off another sync when another change is made or there's a button in Status > Filter Reload (of all places).
-
hehe - that image just got better, I was thinking man derelict must be blind if has fonts/resolution set like that ;) Now it looks normal.. Before it was HUGE ;)
-
@johnpoz It plays pretty nice in VMs. If you decide to lab it and have any questions just shout. Nothing special needed in proxmox.
-
But if the sync is having issues talking to the other side, wouldn't it auto send a new syn?
-
@johnpoz I made a folder action that automatically downsizes screencaps from the 4K when they are taken. I have gotten lazy with Cmd-Option-Shift-4 (instead of Cmd-Shift-4) because it automatically sends the capture to the clipboard instead of the disk.
-
@johnpoz said in HA XMLRPC error:
But if the sync is having issues talking to the other side, wouldn't it auto send a new syn?
A config sync is a one-time/as-needed event. If the connection fails it isn't retried - or maybe it is I don't know. Not really sure of why it is coded that way (if it is) and wouldn't understand it if I looked in there.
But that would not change those logged blocks or the logged XMLRPC message. It would just try again and succeed.
-
So you running 4k on your monitor? You Suck! ;) you have all the good toys!
-
@johnpoz 5K iMac with a 4K on each side

-
Yeah you suck! ;) heheheh.. I finally updated main tv to 4k.. But upgrading my pc to do 4k with new monitor is cost prohibitive currently.. Damn budget committee (wife) can be a problem ;)